
Why Online RAR Password Tools Fail — and What Legitimate Users Can Do Instead
You type a password into WinRAR, hit Enter… and nothing opens. Under deadline pressure, the next instinct is obvious: search for a quick online “RAR password tool” that promises instant access. The problem is that most of these sites either cannot actually help with real-world encrypted archives — or they quietly take possession of your sensitive data along the way. What looks like a shortcut often becomes the riskiest step in the entire process.
If the archive in question contains payroll data, legal documents, source code, or client files, that risk is not just technical. It can affect contracts, regulations, and long-term trust. This article explains why online RAR password tools frequently fail, what is technically going on under the hood, and how you can move away from risky uploads toward offline, policy-aligned workflows that still give legitimate users a fair chance to regain access to their own data.
We’ll look at the limits of what any tool can do, the privacy and compliance issues behind “just upload your file” services, and practical alternatives. Instead of chasing magical “password breakers,” you’ll learn how to diagnose your situation, understand your realistic options, and use an offline toolset that respects both encryption design and your legal responsibilities.
🧭 Navigation
Important
The information provided in this article applies exclusively to RAR / WinRAR archives for which you have full, demonstrable ownership or properly documented authorization. If you are not the rightful owner of the data, do not directly control it, or cannot clearly prove permission to access it, you must stop immediately. Attempting to access, recover, or modify data without explicit authorization may violate criminal law, civil statutes, corporate compliance requirements, and privacy regulations in many jurisdictions. You alone are responsible for ensuring that your actions are lawful and properly permitted before proceeding.
📌 TL;DR — Why Online Tools Fail And What To Do Instead
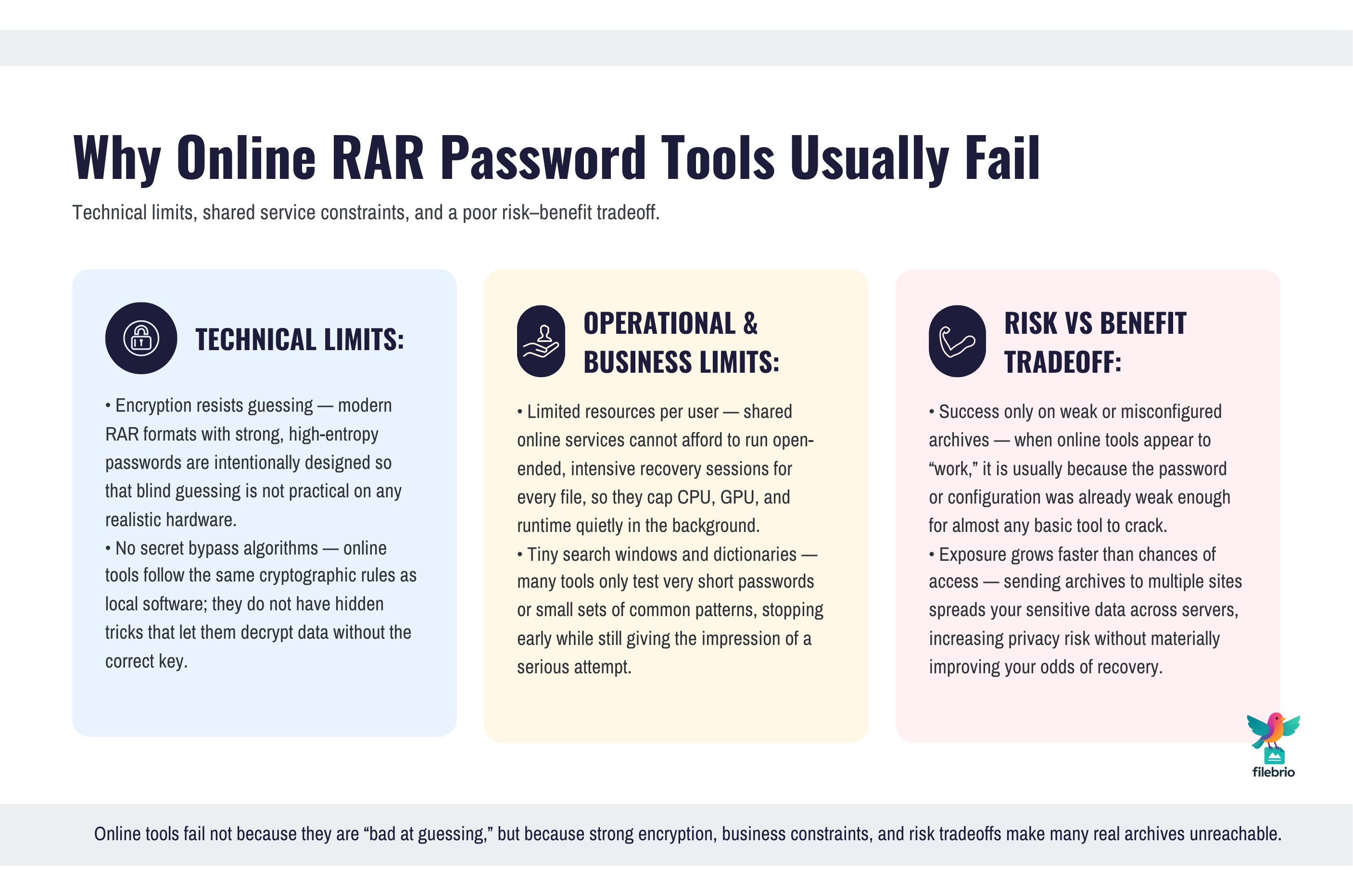
Online RAR password tools usually promise more than they can deliver. Real, strongly encrypted RAR/WinRAR archives — especially those using modern formats and robust passwords — cannot be opened by simple, generic “unlock in the browser” sites. When these services appear to “work,” it’s often because the password was extremely weak, the archive wasn’t fully encrypted, or the site performed only superficial checks. When they fail, you rarely get an honest explanation of why, and you may never know how your uploaded data is stored, analyzed, or reused.
The deeper problem is that uploading sensitive archives to unknown servers introduces serious privacy and compliance risks. Even if a tool is honest, it may keep copies of your files for troubleshooting, “research,” or future feature development. For personal backups this is bad enough; for company documents it can conflict with internal policies, regulations, or contractual obligations. In other words: you might stay locked out and still lose control of your data.
Instead of betting on online shortcuts, legitimate users should focus on three steps: diagnose what blocks access (password vs corruption vs format), evaluate safe options for archives they truly own, and use offline, audited tools that operate under their own security policies. That includes understanding ethical boundaries, realistic technical limits, and when recovery is simply not feasible. The goal is not to “beat” encryption at any cost, but to make sure you handle your own protected data safely, legally, and with your privacy intact.
🧠 Why People Turn To Online RAR Password Tools
Most people land on online RAR password sites in a moment of stress. A project deadline is close, an old archive suddenly matters again, or a colleague who knew the password is unavailable. The search query is emotional: “just open this file for me.” It’s easy to forget that encrypted archives are designed specifically not to have quick back doors.
That’s why ethical guidance like ethical ways to handle your encrypted RAR files ↗️ is so important. It reminds you that encryption is there to protect sensitive content, not to be bypassed whenever access becomes inconvenient. Online tools capitalize on urgency by promising simple fixes, but they rarely explain that upload-based “solutions” shift risk away from you understanding your situation and toward trusting an unknown server with your confidential data.
Understanding your own motivations helps reset expectations. If you realize you’re searching for relief from pressure rather than a technically sound method, you’re more likely to slow down, protect your data, and choose safer offline options instead of blind uploads.
🔎 How Online RAR Password Tools Actually Work (At A High Level)
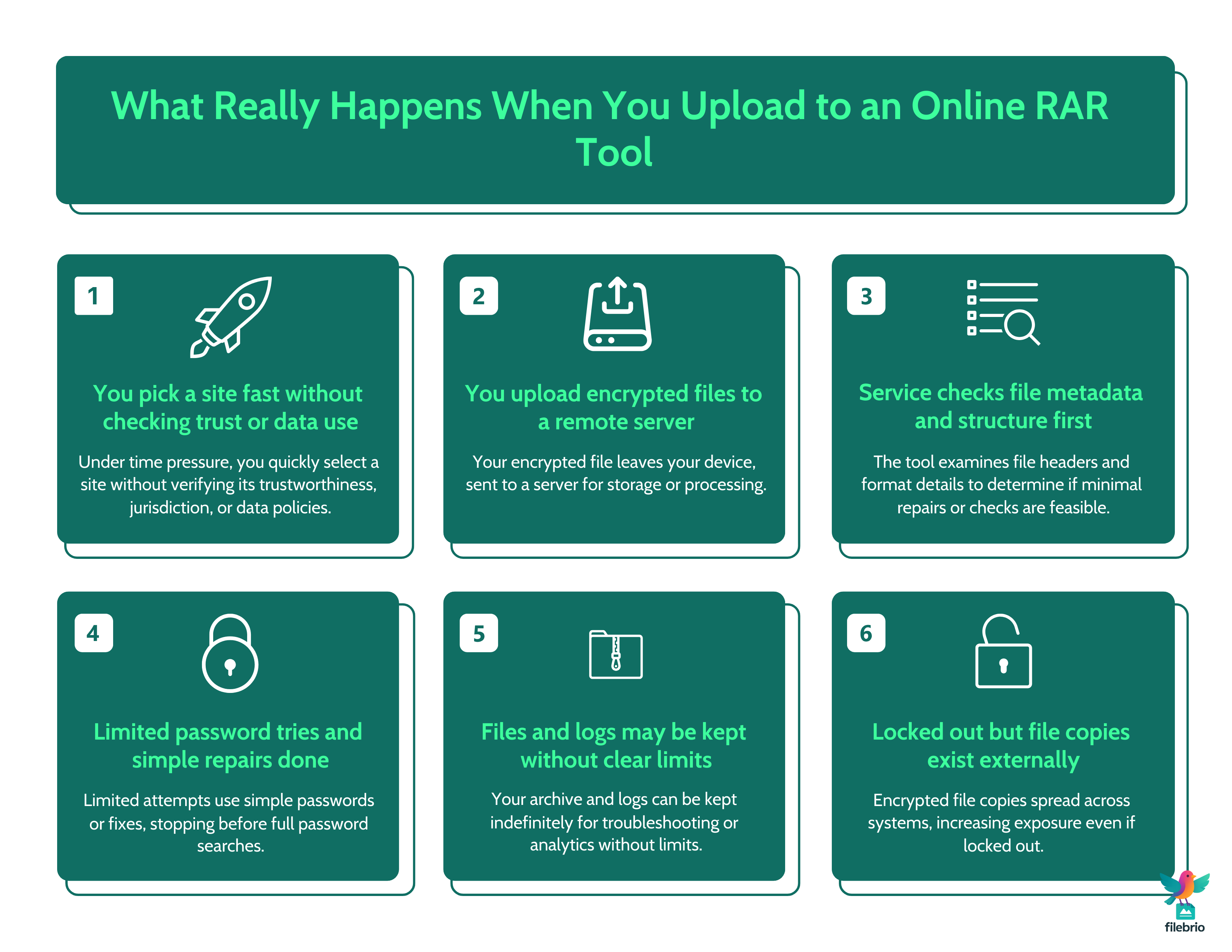
Most online tools follow a similar pattern: you upload your encrypted RAR file, sometimes choose basic options, and then wait for the service to “process” it. Behind the scenes, several different things can be happening — none of which change the fundamental rules of encryption.
Some services only inspect metadata: they look at headers, compression settings, and file structure to decide whether your archive is even a candidate for simple operations. Others may attempt limited guessing strategies against the password — usually something constrained, such as checking short passwords or trying a small set of common patterns. A few tools may even perform simple repairs if the archive is partially corrupted, but this is often superficial and undocumented.
From a practical standpoint, these tools face the same limits described in depth by high-level analyses such as why offline tools keep your encrypted RAR data private ↗️. They do not possess secret algorithms that bypass encryption. They are just software running on somebody else’s hardware. When the password is weak and the archive format is simple, they might succeed quickly; when it is strong and modern, they quietly run into the same mathematical walls that any local tool would face.
🧱 Technical Limits: Why Online Tools Often Cannot Deliver
To understand why online tools fail so often, you need a conceptual sense of how hard it is to guess a strong password and how RAR formats protect data. Modern archives with robust encryption and long, unpredictable passwords are designed so that blind guessing is not practically viable. It doesn’t matter whether guessing happens on your own machine or on a remote server; the underlying math does not change.
Educational discussions like why “breaking passwords online” risks your protected RAR data ↗️ and why online “decryption” risks your protected RAR contents ↗️ stress this point: online marketing language often hides the reality that many archives are effectively unopenable if the password is strong enough. Properly designed encryption doesn’t “fail” just because a website wants it to.
In fact, sending your file to multiple tools in a row does not meaningfully improve your chances if they all rely on the same basic ideas. What it does increase is the number of places where your confidential archive now exists. The more copies scattered across external servers, the higher your exposure if any of those systems are compromised or mismanaged.
🧰 All-In-One Offline Toolkit For Real RAR Password Problems
If guessing is hard and online tools are risky, you still need a practical environment to work with your own protected archives. That’s where a unified, offline toolkit becomes essential. Instead of juggling random utilities and web services, you can base your workflow around a single, policy-aligned application that understands modern RAR formats, respects your privacy, and stays entirely on your own systems.
For many users, this means standardizing on a suite that covers diagnostics, repair, and lawful recovery in one place. A comparison like offline vs online RAR recovery ↗️ helps frame the decision: working locally with a trusted toolkit gives you control over where archives are stored, how they are processed, and who can use the software. At the same time, you can rely on capabilities similar to those in a dedicated RAR password recovery tool ↗️ when recovery is technically and legally appropriate.
To support non-expert users, you might pair this toolkit with educational resources and internal documentation, such as a consolidated RAR user guide and FAQ ↗️. And when you are ready to roll the software out broadly, your IT team can obtain it safely via the official FileBrio Office Suite installer instead of letting users download unvetted utilities from random sites.
________________________
FileBrio RAR Master — part of the FileBrio Office Suite — is a privacy-first, offline Windows toolkit for diagnosing and safely regaining access to your own password-protected RAR / WinRAR archives.
- Local processing only — nothing leaves your PC.
- Smart diagnostics to separate password issues from corruption.
- Owner-verified recovery workflows designed strictly for legitimate use.
Reminder: FileBrio RAR Master may be used only with archives you own or are explicitly authorized to access. It performs all analysis and recovery operations locally on your device, without uploading data anywhere.
________________________
🚨 Privacy And Compliance Risks Of Uploading Encrypted Archives
Even when online tools are honest about their technical limits, their privacy model often clashes with real-world obligations. Uploading an encrypted archive does not mean it is safe by default. The file may still contain sensitive personal data, trade secrets, or confidential client material. Encryption protects the content from unauthorized decryption, but it does not prevent the service from storing or copying the ciphertext or associating it with your IP address or account.
This is why safety-focused explanations such as how to avoid exposing your encrypted RAR contents online ↗️ are so emphatic. They highlight that even if a site claims to delete files after processing, you usually have no way to verify whether temporary storage, backups, or logs retain data for longer. For corporate archives, this can conflict with internal policies, data protection laws, or contractual confidentiality clauses.
From a legal standpoint, you must also consider guidance like legal factors when accessing your encrypted RAR files ↗️. If the archive contains regulated information, uploading it to an unknown host may violate geographic restrictions, cross-border transfer rules, or sector-specific requirements. The practical takeaway is simple: do not use public online tools as a shortcut around governance, especially when there are offline alternatives under your direct control.
🧪 Diagnose Your Situation Before Choosing Any Tool
The safest way to avoid bad tools is to understand your problem before you search for solutions. Many people assume that any failure to open an archive means “wrong password,” when in fact the real issue might be file corruption, partial downloads, or mismatched formats. Uploading a damaged file to a dozen online tools will not suddenly fix a broken storage device.
Structured guidance like how to assess safe access paths for your locked RAR file ↗️ encourages you to treat diagnosis as a separate step. Ask yourself:
- Did the archive ever open successfully on this or another system?
- Are you seeing explicit “wrong password” messages or more generic error codes?
- Could the file have been truncated during transfer or backup?
Once you have a clearer picture, you can choose an appropriate path within the safe, legal methods outlined in restoring access to RAR/WinRAR archives with safe and legal methods ↗️. In some cases, your priority should be repairing corruption; in others, it might be reconstructing the password from your own habits and hints. Only after that should you consider whether a local recovery attempt is technically feasible and justified for a specific archive.
🛡️ Secure Offline Solution For Sensitive RAR Archives
Once you commit to staying offline, the next step is selecting a solution that aligns with both your technical needs and your policies. A good offline toolkit is not just a “password tool”; it is a controlled environment for working with encrypted archives over their full lifecycle — from creation and diagnostics to lawful recovery and retirement.
A responsible solution should help you operate within documented usage boundaries, such as those described in a formal legal and responsible use policy ↗️. It should support clear checks that you are only working with archives you legitimately own, echoing the principles in how to verify ownership before accessing your RAR file ↗️. Instead of anonymous uploads, you have a local audit trail: which user opened which archive, under which conditions, and with what level of success.
When you need to plan or explain how difficult recovery might be, a high-level utility such as a password speed benchmark ↗️ can illustrate the relationship between password length, complexity, and realistic testing time — without ever sending the archive itself anywhere. And for users who need tooling on more than one machine, you can deploy the same trusted suite via your internal distribution systems after obtaining it once from the official FileBrio tools download page ↗️.
________________________
FileBrio RAR Master — a secure, offline Windows toolkit for regaining access to your own password-protected RAR / WinRAR archives while keeping all data strictly on your device.
- Offline-only processing — never uploads your archives.
- Smart issue detection — password vs corruption.
- Fast recovery workflow optimized for legitimate ownership.
⬇️ Download FileBrio RAR Master
Reminder: FileBrio RAR Master is intended only for archives you own or are explicitly authorized to access. All operations run locally on your PC.
________________________
🛟 Safer Options For Legitimate Users (Without Online Shortcuts)
If you own the archive and still need access, what can you do instead of relying on online tools? The answer is a combination of behavioral, procedural, and technical steps that keep control in your hands. First, focus on your own behavior and memory. Many cases can be resolved by systematically revisiting your past patterns, which is precisely the kind of safe exploration discussed in higher-level resources about reconstructing or analyzing your password style.
Second, look at your broader situation through the lens of ways offline recovery preserves confidentiality of your files ↗️. If the archive contains highly sensitive data, your threshold for attempting any form of technical recovery should be higher than for personal, low-risk content. For some archives, after careful evaluation, the only responsible conclusion may be that the combination of encrypted format and password strength makes recovery unrealistic — and that is still better than exposing your data unnecessarily.
Finally, incorporate structured decision-making like that described in how to choose secure methods for accessing your protected files ↗️. You might decide to attempt local recovery with a managed toolkit, or to escalate to a specialist under contract, or to accept that specific archives remain inaccessible while ensuring that future ones are created with better retention and metadata practices.

⚙️ Policy And Habits That Keep You Away From Risky Sites
The best way to “win” against misleading online tools is not to outsmart them technically, but to design your policies and habits so you never need them. That starts with clear internal rules: encrypted archives belong to defined owners; only approved software may be used to handle them; and uploading to public password sites is explicitly forbidden. These rules should be grounded in frameworks like guidelines for legally managing your RAR-protected data ↗️, not just in ad-hoc advice.
Education is just as important. Users should know that online tools are risky not because they are “bad software,” but because they operate outside your governance. Point them to offline, policy-aligned workflows as the default path, and make sure those workflows are convenient enough to use under real-world pressure. Centralizing documentation in a place that references practical help — such as your own internal FAQ plus the official RAR Master help and answers ↗️ — gives people a safe starting point when problems arise.
Ultimately, the more you normalize careful diagnostics, ownership checks, and offline handling, the less appealing anonymous web tools become. When everyone knows there are safer, legitimate options for dealing with their own locked archives, the phrase “just upload it to a password site” fades out of your culture — and your encrypted data stays where it belongs.
⚖️ Legal Reminder
This article is provided for general informational and educational purposes only. Any examples, scenarios, or references to password recovery, archive security, or related tools (including FileBrio RAR Master or similar software) are intended solely to help you better understand how to protect and manage your own data.
You may only apply any techniques, workflows, or tools described here to files and archives that you fully own or are explicitly and verifiably authorized to access. Attempting to bypass, remove, or recover passwords for third-party data without clear permission may violate criminal law, civil law, or internal company policies in your jurisdiction.
Nothing in this article constitutes legal advice. Laws and regulations differ between countries and organizations, and you are solely responsible for ensuring that your actions comply with all applicable legislation, contracts, and internal policies. If you are unsure whether a particular action is lawful or permitted, consult a qualified legal professional before proceeding.
📚 See Also
- Extract RAR Files Online Without A Password: Why Online Tools Are Risky And Safer Offline Methods ↗️
- Free RAR/WinRAR Password Recovery Software: Safe Tools For Accessing Your Own Locked Archives ↗️
- Online RAR/WinRAR Unlockers: Hidden Risks And Why Local Tools Offer Better Security ↗️
- Free RAR Password Recovery Utilities: How To Choose Safe, Privacy-Focused Local Tools ↗️
- Unlocking A RAR Archive Without A Password: What’s Realistic And How To Evaluate Safe Access Options ↗️
- Unlocking Password-Protected RAR/WinRAR Archives: Safe Methods For Legitimate Access ↗️
- Opening RAR/WinRAR Archives With Or Without A Password: A Practical Guide To Safe Access Options ↗️