
When It Makes Sense to Attempt Password Recovery — and When the Archive Is Mathematically Unopenable
You open a RAR archive you absolutely own, expect your files to appear, and instead you hit a wall: repeated password prompts, error messages, or nothing at all. At that moment, one question quickly dominates everything else: is it worth attempting password recovery, or is this archive already beyond reach?
This article helps you distinguish between situations where a carefully planned, lawful recovery attempt is reasonable, and situations where cryptographic and structural limits make a locked RAR archive effectively inaccessible, no matter how determined you are. Instead of guessing blindly, you will learn how to read symptoms, understand how encryption and password complexity interact, and decide whether further effort makes technical sense.
🧭 Navigation
📌 TL;DR — Quick Decision Snapshot
In short, attempting password recovery makes sense when:
- You clearly own the archive and are authorized to access it.
- The archive is structurally healthy or only mildly damaged.
- The password comes from human patterns you can still reason about (old schemes, themes, or predictable variations).
- You have useful context: approximate length, typical style, or notes that meaningfully narrow the search space.
Attempts become unrealistic or mathematically unopenable when:
- The archive uses strong modern encryption, and the password was designed to be high-entropy and random with no remaining memory cues.
- The file is severely corrupted or truncated, with key structural parts missing.
- Multi-volume sets have lost critical volumes with no backups or recovery records.
- You cannot reliably prove or document ownership and would risk legal or policy violations by continuing.
The rest of this article explains how to move from gut feeling to a structured, technical decision about whether to proceed or stop.

🔓 Introduction: Effort vs Reality
Most users encounter this question after a moment of panic: the archive will not open, and the first instinct is to try every password they can remember. That is understandable, but not always rational. The more time and energy you invest, the more important it becomes to know whether the goal is even technically achievable.
A more disciplined workflow is to first confirm basic recoverability, then decide if password attempts are worthwhile. A separate article goes deeper into ways to validate recovery chances for your locked RAR file ↗️, but here we focus on one specific decision: should you try to recover the password at all, or is the archive effectively out of reach?
🧠 Mindset: Possible, Feasible, and Sensible
To reason clearly about this, it helps to separate three concepts that often get blended together:
- Theoretically possible: With enough time and computing power, almost any password could be discovered.
- Practically feasible: The time and resources required are within realistic limits for you or your organization.
- Personally sensible: The effort, cost, and risk are justified by the value of the data.
For example, an 8-character password made from common words may be both theoretically and practically manageable, especially if you remember rough structure. A 25-character random string generated by a password manager years ago, now forgotten, may be theoretically possible but practically unachievable in your lifetime.
RAR’s encryption model reinforces this distinction. Modern RAR formats use robust cryptography, not easily bypassed tricks. A high-level explanation of how RAR4 and RAR5 protect your data is covered in how RAR4 and RAR5 secure your protected data ↗️.
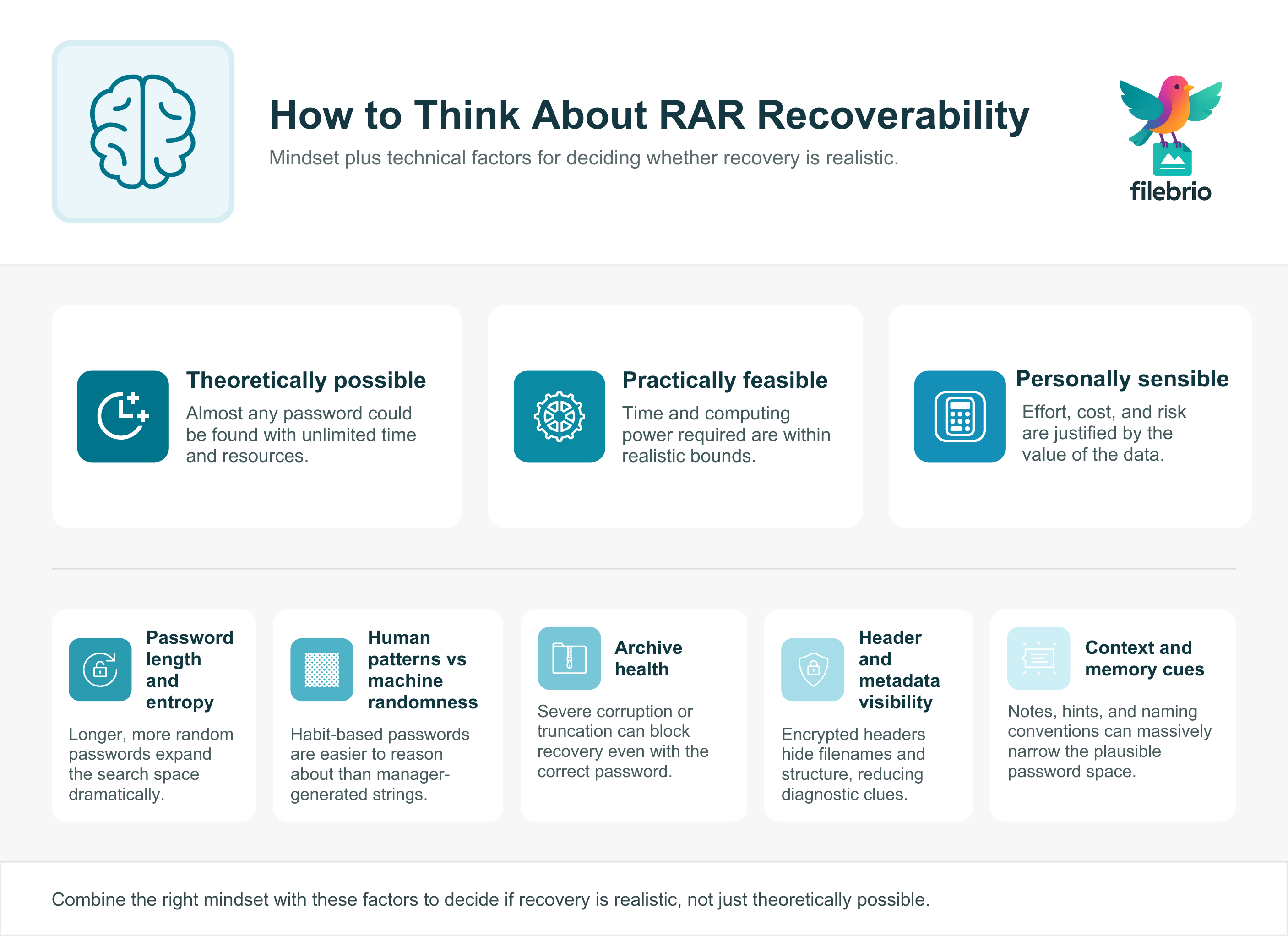
⚙️ Key Factors That Decide Recoverability
Several technical and human factors determine whether password recovery attempts make sense. At a high level, the most important are:
- Password length and entropy: Longer, more random passwords grow the search space dramatically. Conceptual background on this is explored in how length impacts protection of your RAR password ↗️.
- Human patterns vs machine randomness: Human-created passwords often follow themes, substitutions, or predictable tweaks, whereas password-manager-generated strings are closer to true randomness.
- Archive health: If the archive is badly corrupted or truncated, even the correct password might not yield usable data.
- Header and metadata visibility: Encrypted headers make diagnostic work harder, while visible metadata (filenames, sizes) can show whether the archive structure is intact.
- Context and memory cues: Notes, hints, naming conventions, and old habits can dramatically narrow the space of plausible passwords.
When several factors align in your favor — manageable length, human patterns, good archive health, and decent memory cues — password recovery can be a sensible next step. When they align in the opposite direction, you may be facing practical impossibility even before you start.
🧭 Before You Commit Time and Effort, Get a Clear Picture of Recoverability
When you’re deciding whether password recovery attempts make sense, the hardest part is knowing what kind of obstacle you’re truly facing. A wrong-password prompt, a missing file list, or repeated extraction failures can all look the same — but they come from very different causes. Before spending hours chasing possibilities, it’s worth confirming whether the archive is healthy, corrupted, encrypted at the header level, or already mathematically sealed.
FileBrio RAR Master helps you make that decision safely and privately:
- 🔍 Detects encrypted headers that hide filenames and mimic “wrong password” symptoms
- 📦 Evaluates archive structure to separate password issues from corruption
- 🧩 Identifies truncation, damaged volumes, and RAR4/RAR5 differences
- 🛡️ Runs 100% offline — your protected data never leaves your device
- 📊 Helps you judge whether password evaluation is realistic or a dead end
Before you decide whether recovery is sensible, get a safe diagnostic snapshot:
________________________
FileBrio RAR Master — part of the FileBrio Office Suite — is a privacy-first, offline Windows toolkit for diagnosing and safely regaining access to your own password-protected RAR / WinRAR archives.
- Local processing only — nothing leaves your PC.
- Smart diagnostics to separate password issues from corruption.
- Owner-verified recovery workflows designed strictly for legitimate use.
Reminder: FileBrio RAR Master may be used only with archives you own or are explicitly authorized to access. It performs all analysis and recovery operations locally on your device, without uploading data anywhere.
________________________
✅ Scenarios Where Password Recovery Attempts Make Sense
Let’s look at situations where it is technically and practically reasonable to consider password recovery, assuming you have clear ownership and stay within legal boundaries.
Passwords Based on Old Habits and Themes
If you know the password was built from personal patterns — favorite words, dates, predictable substitutions — and not from a hardware token or password manager, you often have more leverage than you think. Structured reflection can help you narrow down realistic candidates rather than guessing blindly.
For example, you might remember that you combined a nickname with a year and a symbol, or that you used a specific pattern at the time. A separate article describes ways to rediscover your forgotten RAR password safely ↗️ using context and associations rather than random trial-and-error.
Moderate Length and Non-Random Structure
Even if you cannot recall the exact string, passwords that are moderate in length and built from a limited alphabet (e.g., mostly lowercase letters with a few digits) are more realistic candidates for carefully planned attempts, especially when combined with strong memory cues.
If you roughly remember the length and type of characters, that information shrinks the conceptual search space. The article on how structural strength shapes your RAR password difficulty ↗️ provides a high-level look at why this matters.
Structurally Healthy Archive with High Data Value
If diagnostic checks show the archive is structurally sound — no serious corruption, all volumes present, headers intact — and the data inside is important enough, investing effort into password evaluation may be justified. In such cases, you face a pure encryption barrier rather than a mix of damage and lost credentials.
Before you commit, it is still wise to confirm that the archive is technically viable. Conceptual guidance on this is provided in checks to confirm your encrypted RAR file’s viability ↗️.
Useful Notes, Metadata, and Hints
Sometimes the deciding factor is not the password itself, but the metadata you kept about it. Notebook entries, password hint files, or internal documentation that describe “how” a password was constructed can transform a hopeless situation into a manageable one.
For individuals, this is closely tied to secure approaches to keeping your RAR password metadata ↗️, where you keep enough information to reconstruct your logic later without exposing the exact password in plain text.
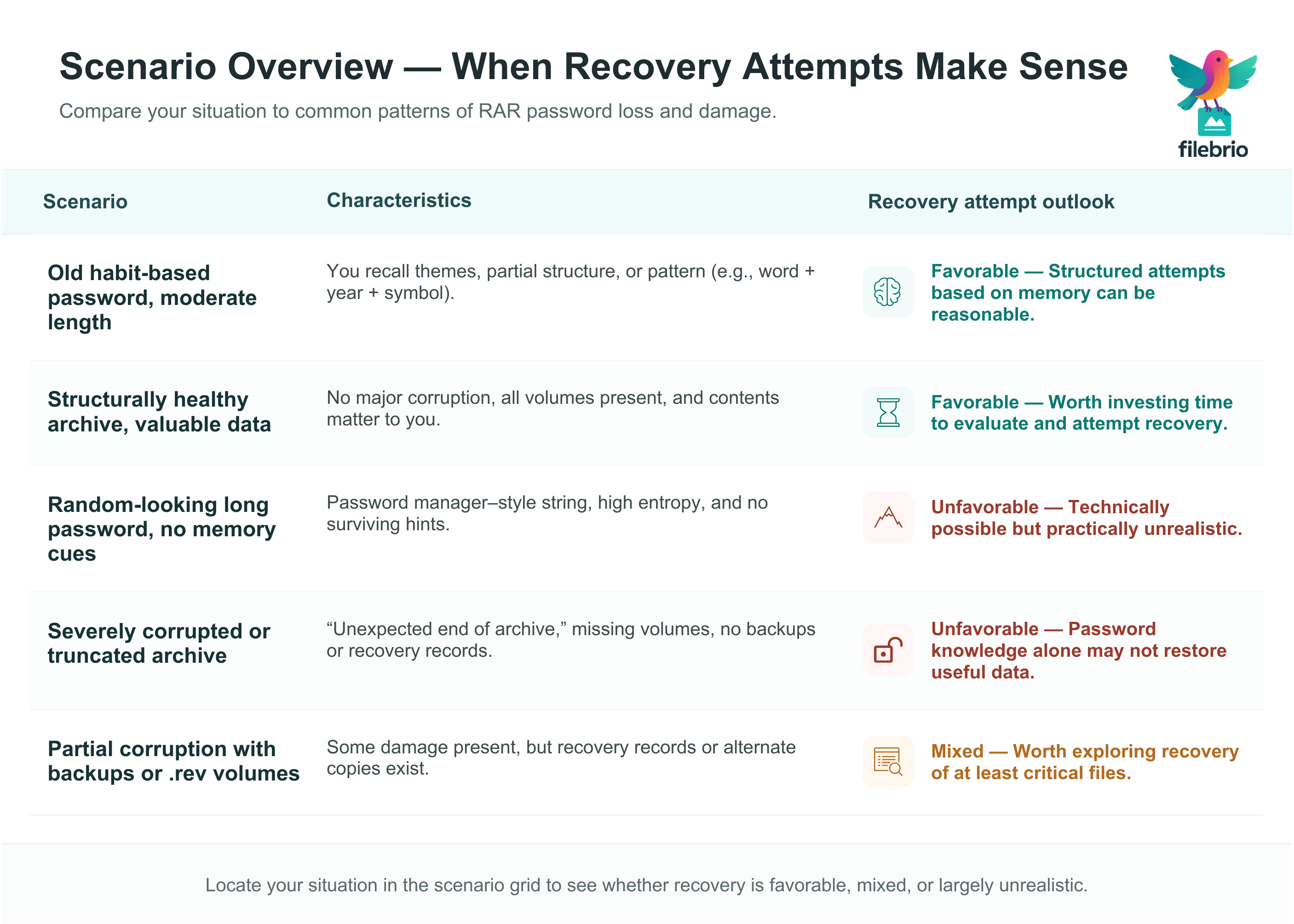
📊 Scenario Overview: Should You Attempt Recovery?
| Scenario | Characteristics | Recovery Attempt Outlook |
|---|---|---|
| Old habit-based password, moderate length | You recall themes, partial structure, or pattern (e.g., word + year + symbol) | Favorable: Structured attempts based on memory can be reasonable. |
| Structurally healthy archive, valuable data | No major corruption, all volumes present, and contents matter to you | Favorable: Worth investing time to evaluate and attempt recovery. |
| Random-looking long password, no memory cues | Password manager–style string, high entropy, and no surviving hints | Unfavorable: Technically possible but practically unrealistic. |
| Severely corrupted or truncated archive | “Unexpected end of archive,” missing volumes, no backups or recovery records | Unfavorable: Password knowledge alone may not restore useful data. |
| Partial corruption with backups or .rev volumes | Some damage present, but recovery records or alternate copies exist | Mixed: Worth exploring recovery of at least critical files. |
🚫 When a RAR Archive Becomes Mathematically Unopenable
On the other side, there are scenarios where continuing to “try things” is mostly an emotional response rather than a rational plan. In these cases, mathematics, cryptography, or physical damage are working against you in ways that human effort cannot overcome.
Truly Random, Long Password with No Surviving Clues
If the password was generated as a long, random string with no meaningful pattern — and you no longer have access to the manager or record that stored it — then you are effectively facing the full strength of modern encryption. High-level discussions of why some archives cross this line are given in why some archived RAR files become inaccessible ↗️.
In such cases, there is no realistic way to “narrow the search space” using human logic. The number of possibilities quickly exceeds what can be explored in any meaningful timeframe.
Severe Structural Damage or Truncation
Even with the correct password, a badly damaged archive may not be able to reconstruct its contents. If diagnostics show:
- Major truncation (only a fraction of the archive remains),
- Multiple volumes missing from a multi-volume set, or
- Consistent errors in core structural areas, not just in a few data blocks,
then much of the data may be mathematically lost. Knowing the password in this scenario is like knowing the key to a safe that has already been crushed: the lock may open, but the contents are no longer intact.
Unclear Ownership and Legal Barriers
There is also a non-technical version of “unopenable”: if you cannot demonstrate clear rights to the data, or if opening it would violate applicable law or policy, then responsible practice says you must not proceed. Even if access might be technically possible, it is not permissible.
Legal questions around working with encrypted material are explored conceptually in legal factors when accessing your encrypted RAR files ↗️. Respecting these boundaries is part of what it means to handle sensitive archives professionally.
🧪 Safe Preparation Before Any Password Attempts
Suppose your assessment lands in the “favorable” or “mixed” zone — it might be worth attempting recovery. Before you do anything, it is crucial to prepare in a way that protects your data and your time.
- Work on copies, not originals: Duplicate the archive to safe storage and perform any checks on the copy.
- Confirm basic integrity and recoverability: Check that the file is not severely truncated and that metadata looks sane. Helpful high-level guidance is found in what to review before guessing your RAR password ↗️.
- Collect all memory cues and notes: Spend time reconstructing your password creation habits, likely themes, and time period when you set it.
These preparatory steps do not guarantee success, but they ensure that any attempts you make are reasoned rather than random, and that you do not accidentally damage the last remaining copy of a critical archive.
🛠️ A Safe, Offline Way to Check If Recovery Attempts Are Even Worth Pursuing
Once you understand that some archives are feasible to recover while others are mathematically unopenable, the next step is using responsible, private diagnostics. Guessing randomly or relying on risky online tools can waste time — or compromise the last
remaining copy of your own data.
FileBrio RAR Master gives you a controlled environment built for this exact decision point:
- 🔐 Verifies whether your archive is intact enough to justify recovery attempts
- 🧠 Helps you interpret symptoms: wrong password vs corruption vs missing volumes
- 📁 Analyzes RAR4/RAR5 structure and header behavior with precision
- 🖥️ 100% offline diagnostics — essential for confidential or regulated archives
- 📌 Ideal before investing into memory-based reconstruction or further evaluation
| What You’re Seeing | What FileBrio Helps You Learn |
|---|---|
| No filenames, “empty” archive | Encrypted headers vs structural damage |
| Endless wrong-password prompts | Password error vs corrupted metadata block |
| Multi-volume errors | Missing segments vs misordered chain |
| Unsure if password recovery is worth it | Feasibility insights based on structure + context cues |
If you’re weighing whether recovery is realistic, start with a safe diagnostic step:
________________________
FileBrio RAR Master — a secure, offline Windows toolkit for regaining access to your own password-protected RAR / WinRAR archives while keeping all data strictly on your device.
- Offline-only processing — never uploads your archives.
- Smart issue detection — password vs corruption.
- Fast recovery workflow optimized for legitimate ownership.
⬇️ Download FileBrio RAR Master
Reminder: FileBrio RAR Master is intended only for archives you own or are explicitly authorized to access. All operations run locally on your PC.
________________________
⚖️ Legal and Ethical Boundaries You Must Respect
Even when a recovery attempt seems technically promising, you must ensure it is legally and ethically justified. That means you should:
- Verify that the archive belongs to you or an organization you are authorized to represent.
- Check that any steps you take align with local regulations, internal policies, and contractual obligations.
- Document your actions if the archive contains regulated or sensitive information.
High-level principles for working responsibly with protected archives are discussed in guidelines for legally managing your RAR-protected data ↗️. If you cannot show clear authorization, the correct decision is not to attempt recovery, regardless of technical feasibility.
🛡️ Future-Proofing: Avoiding Unrecoverable Situations
One of the most valuable outcomes of a difficult recovery decision is the lesson it teaches about future habits. Whether you eventually succeed or not, you can adjust how you protect your data so that you rarely face the same dilemma again.
Designing Strong Yet Memorable Passwords
The ideal password policy for personal archives balances strength with memory. Instead of extremely short or extremely random passwords you will forget, use structured, layered phrases that are hard to guess but meaningful enough for you to recall later.
Practical techniques for this are explored in how to design strong memorable RAR passwords ↗️, focusing on building patterns that are both resilient and realistic to maintain.
Storing Password Metadata Safely
In many “unopenable” cases, the core problem is not that the password is weak or strong, but that no metadata was preserved about your choices. You do not need to store raw passwords in plain text, but you should keep:
- Hints about structure (for example, “three words, year, symbol”),
- References to the system you used (“scheme from project X”), and
- High-level notes about where you stored the exact password (e.g., a secure manager).
For individuals, best practices are described in methods to preserve long-term access to your protected RAR files ↗️, where you retain enough information to recover your logic without undermining security.
Balancing Security and Future Access
Encryption that is too weak exposes you to unauthorized access; encryption that is too strong and undocumented can lock you out of your own information. The goal is to design a setup that protects your data today while preserving access for your future self.
Conceptual strategies for achieving this balance are discussed in ways to boost security without losing access to your data ↗️, combining sensible password design, metadata storage, and backup practices.
📂 When to Involve Professionals and How to Document Ownership
Some cases sit at the edge of what you can handle alone. The archive may still be technically viable, but the effort or risk of further attempts is high. In these situations, involving a professional service or internal security team can be reasonable — if your ownership and authorization are clear.
Before you consider external help, prepare:
- Evidence of ownership: Purchase records, email trails, project documentation, or corporate policies stating that you are responsible for the data.
- Chain-of-custody notes: Where the archive came from, which devices it has been on, and what tools you already used.
- Constraints and goals: What is the acceptable risk, budget, and timeframe?
Corporate environments in particular benefit from clear evidence trails and policies on who may authorize access, as explored in steps to meet compliance when working with your archives ↗️. If you share the archive with any third party, do so under well-defined agreements and only when doing so is fully compliant with your obligations.
📜 Legal Reminder
This article is provided for general informational and educational purposes only. Any examples, scenarios, or references to password recovery, archive security, or related tools (including FileBrio RAR Master or similar software) are intended solely to help you better understand how to protect and manage your own data.
You may only apply any techniques, workflows, or tools described here to files and archives that you fully own or are explicitly and verifiably authorized to access. Attempting to bypass, remove, or recover passwords for third-party data without clear permission may violate criminal law, civil law, or internal company policies in your jurisdiction.
Nothing in this article constitutes legal advice. Laws and regulations differ between countries and organizations, and you are solely responsible for ensuring that your actions comply with all applicable legislation, contracts, and internal policies. If you are unsure whether a particular action is lawful or permitted, consult a qualified legal professional before proceeding.
📚 See Also
- How to Check Whether Your RAR Archive Uses Header Encryption ↗️
- How to Interpret RAR Error Messages Before Taking Action ↗️
- What’s Actually Possible When You Don’t Have the Correct Password ↗️
- Why Ethical Wordlist Principles Matter When Evaluating Feasibility ↗️
- How to Choose Safe Offline Tools for Responsible Password Recovery ↗️
- Why Online “Decryption” Sites Are Unsafe for Encrypted RAR Files ↗️
- How Dummy Archives Help You Gauge Realistic Recovery Difficulty ↗️