Unzipping or Unrarring RAR Files (With or Without Password): Safe Extraction Practices
Maybe you received a RAR archive from a colleague, or you opened an old project folder and found a compressed backup you barely remember. You double-click the file expecting a quick “unzip,” but instead you see password prompts, error messages, or warnings about unexpected end of archive. In that moment, it’s tempting to just keep retrying extraction until something works — even if every attempt risks damaging your data further.
Safe extraction is not just about “getting the files out.” It’s about understanding what kind of RAR archive you’re dealing with, how to interpret the messages your software shows, and how to avoid shortcuts that accidentally corrupt your only copy or expose confidential data to risky tools. Whether you know the password, think you know it, or don’t have it at all, there are careful, structured steps that dramatically reduce the chance of making things worse.
This article walks through those steps. You’ll see how to prepare your system and storage before extraction, how to respond when errors appear, and how to handle both encrypted and unencrypted archives in a privacy-first way. You’ll also learn how an offline, policy-aligned toolkit can become your “safe default” for everyday unzipping and more complex cases — so you spend less time guessing and more time keeping your data healthy and under control.
🧭 Navigation
Important
The information provided in this article applies exclusively to RAR / WinRAR archives for which you have full, demonstrable ownership or properly documented authorization. If you are not the rightful owner of the data, do not directly control it, or cannot clearly prove permission to access it, you must stop immediately. Attempting to access, recover, or modify data without explicit authorization may violate criminal law, civil statutes, corporate compliance requirements, and privacy regulations in many jurisdictions. You alone are responsible for ensuring that your actions are lawful and properly permitted before proceeding.
📌 TL;DR — Safe Unzipping/Unrarring In Any Scenario
Safe extraction of RAR and WinRAR archives starts long before you press the “Extract” button. You should first confirm that you are working with a file you legitimately own, understand whether it’s encrypted or simply compressed, and check that your storage and destination folders are healthy. If you know the password, type it carefully and watch the error messages; if you don’t, it’s better to pause and evaluate your recovery options than to try random tools you found online.
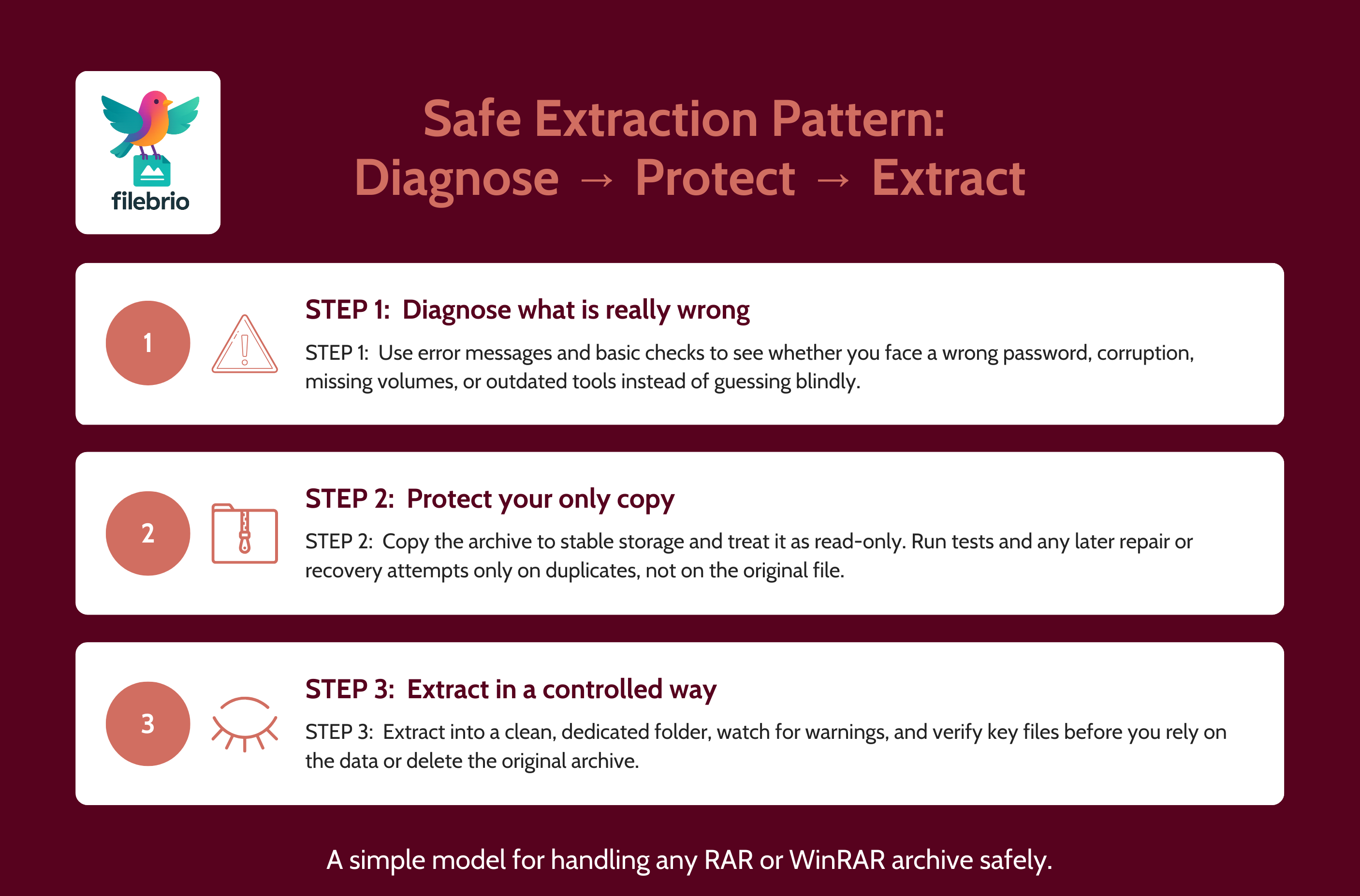
In every case, the basic pattern is the same: diagnose, protect, then extract. Diagnose whether your problem is a wrong password, corruption, or a partial download. Protect the original archive by copying it to reliable storage and avoiding repeated risky extraction attempts on the only copy. Then, extract to a separate, well-organized folder so that you can compare results and detect issues early. When errors appear, treat them as clues rather than annoyances: they often point to missing volumes, damaged data, or format mismatches that you can address calmly instead of with trial-and-error.
If you cannot open an archive even after careful checks, consider using a privacy-first offline toolkit designed for legitimate owners of encrypted RAR files. These tools help you inspect structure, repair damage, and — where technically and legally appropriate — attempt recovery, all without uploading sensitive data to unknown servers. In parallel, improve your long-term habits: better password retention, safer storage, and clear internal rules about which tools are allowed. That way, each future “unzipping” or “unrarring” task becomes routine, not a stressful guessing game.
🧠 Why Safe Extraction Of RAR Files Matters
RAR archives look simple on the surface — one file in, many files out — but in practice they sit at the intersection of encryption, compression, and storage. A rushed or careless extraction attempt can easily overwrite important data, spread partially corrupted files across your folders, or leak sensitive content to tools that were never designed for confidential material.
A more deliberate mindset treats every extraction as part of a broader access workflow. You are not just “unzipping” something; you are deciding where and how protected content will appear on your system. High-level guides like practical ways to access your locked RAR/WinRAR contents ↗️ emphasize that safe access is about context: who owns the data, what kind of archive you have, and what your long-term plans are for the extracted files.
Encryption adds another layer. Once you understand how encryption controls access to your protected RAR contents ↗️, it becomes clear why some archives are trivial to open and others are effectively unopenable without the correct password. That knowledge helps you avoid unrealistic expectations — and avoid risky “shortcuts” that promise to extract everything instantly but typically either do nothing useful or quietly expose your data.
⚙️ What Actually Happens When You Extract A RAR Archive
When you extract a RAR or WinRAR archive, your software reads headers, checks internal structures, and decompresses the stored data into new files and folders on your target drive. If the archive is encrypted, your password is used to derive keys to decrypt the compressed data before it can be unpacked. If filenames themselves are encrypted, even the list of contained files is inaccessible until a correct password is supplied.
Features like filename protection are explained in more detail in discussions of RAR filename encryption ↗️. For safe extraction, what matters is that you may see very different behavior depending on how the archive was created: sometimes you can view filenames but not contents; other times, everything is hidden until the password is accepted. Recognizing this helps you understand whether your software is behaving normally or whether something seems structurally wrong.
During extraction, the software may also verify checksums, track progress per file, and log errors. Paying attention to those logs — not just the final “failed” message — provides valuable clues. Combining them with the guidance from how to interpret error messages from your RAR file ↗️ lets you distinguish between wrong passwords, missing volumes, and genuine corruption, which in turn shapes your next steps.
🧺 How To Prepare Before You Click “Extract”
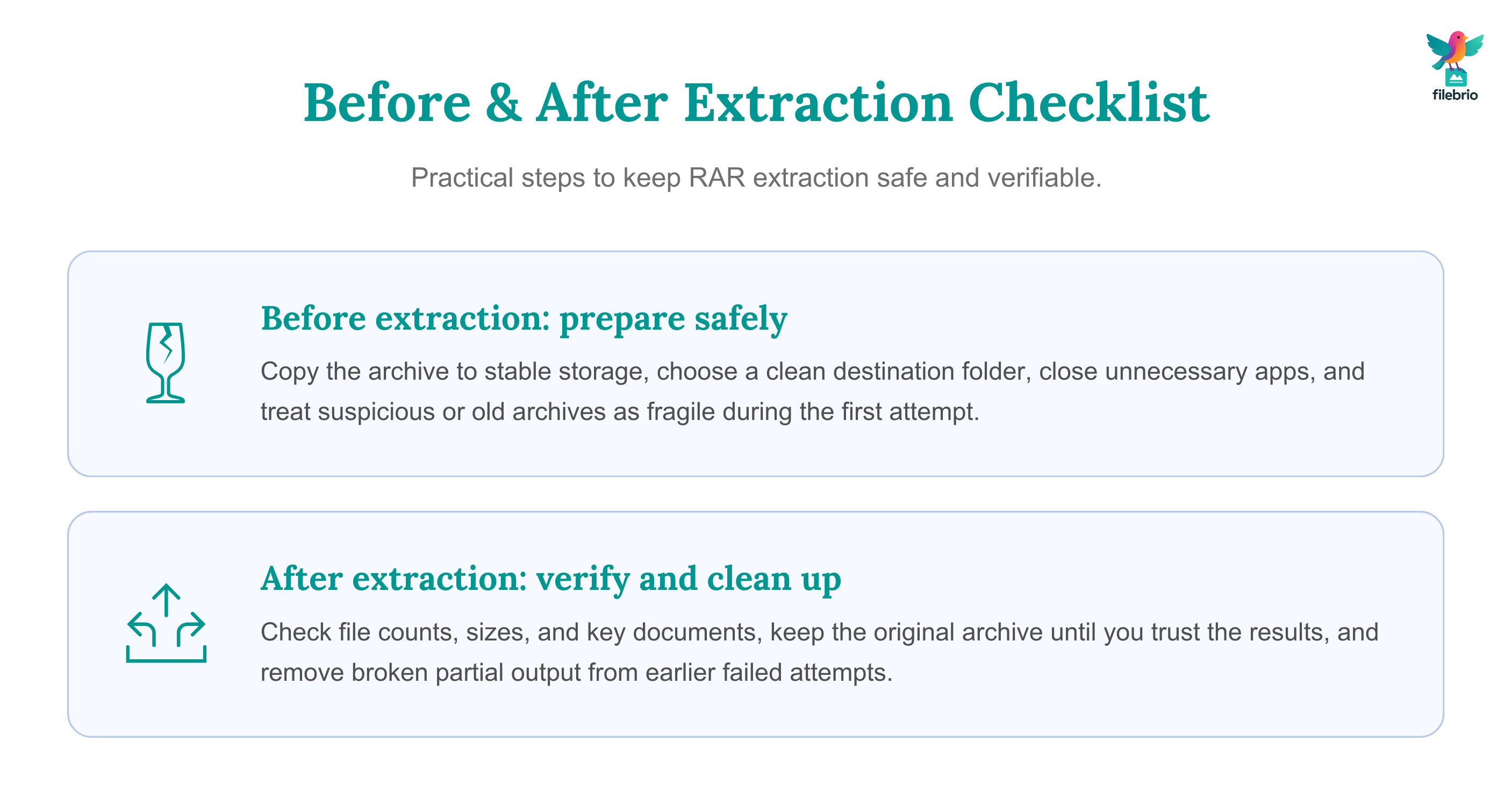
Safe extraction starts with preparation. Before you unzip or unrarr anything, especially if it contains sensitive or irreplaceable data, take a few minutes to stabilize your environment:
- Work from a known-good copy. If the archive is on an aging USB stick or a dubious network share, copy it to stable local storage first. Practices from ways to prevent losing your RAR data on storage devices ↗️ apply directly here.
- Choose a dedicated destination folder. Extracting into a clean, empty folder makes it easier to see exactly what appeared and to roll back if something goes wrong.
- Close unnecessary programs. This reduces the chance of conflicts, file locks, or unexpected interruptions during extraction.
If you already suspect that the archive might be damaged — for example, if it came from a flaky download or an old backup — treat it as fragile. Guidance like how to stabilize your partially corrupted RAR file ↗️ recommends taking extra care: avoid repeated extraction attempts that may leave half-written files everywhere, and consider running integrity tests or copying the archive to another drive before you try to open it.
🧰 All-In-One Toolkit For Safe RAR Extraction And Recovery
Juggling different apps for viewing, extracting, and diagnosing RAR files often leads to confusion — or to the risky habit of trying whatever random tool you find online. A more sustainable approach is to standardize on a single, offline toolkit that can handle everyday unzipping/unrarring and more advanced diagnostics inside your own security boundary.
A consolidated environment like all-in-one RAR recovery toolkit ↗️ can become your “home base” for working with RAR archives. Instead of guessing which program to use on each new file, you know that creation, extraction, repair, and — where appropriate — recovery tasks all live in one place, under the same privacy-first design. This consistency makes it easier to teach colleagues safe routines and to write internal procedures that people actually follow.
For deployment, your IT or support team can rely on the official distribution channel rather than ad-hoc downloads. Installing the toolkit from the trusted FileBrio tools download page ↗️ ensures everyone is using vetted binaries with predictable behavior — a crucial piece of any secure extraction and recovery workflow.
________________________
FileBrio RAR Master — part of the FileBrio Office Suite — is a privacy-first, offline Windows toolkit for diagnosing and safely regaining access to your own password-protected RAR / WinRAR archives.
- Local processing only — nothing leaves your PC.
- Smart diagnostics to separate password issues from corruption.
- Owner-verified recovery workflows designed strictly for legitimate use.
Reminder: FileBrio RAR Master may be used only with archives you own or are explicitly authorized to access. It performs all analysis and recovery operations locally on your device, without uploading data anywhere.
________________________
🧪 Diagnosing Errors Before And After Extraction
Even with careful preparation, extraction may still show warnings or fail outright. Treat every message as a diagnostic clue, not just as an obstacle. The wording and timing of the error often tells you whether you’re dealing with a password issue, a structural problem, or a missing piece of a multi-volume set.
If errors mention CRC failures, unexpected end of archive, or similar terms, it’s a sign you may be dealing with damage rather than a simple password mismatch. In that case, it’s worth revisiting the stabilizing strategies from safe steps to protect your damaged RAR contents ↗️, and cross-checking the messages using the explanations in how to decode alerts shown by your WinRAR archive ↗️. Sometimes, the safest move is to stop further extraction attempts, make a fresh backup of the archive, and consider repair options before trying again.
Good diagnostic practice also includes keeping track of what changed between attempts: did you move the archive, switch tools, or change the destination folder? Documenting those changes makes it easier to pinpoint the real cause and to avoid repeating the same failing steps in a loop.
🔑 When You Know The Password: Safe Encrypted Extraction
If you know (or strongly believe you know) the password, safe extraction is mostly about precision and patience. Typing errors, keyboard layout changes, and hidden whitespace can all make a correct password look wrong. Before assuming your password has failed, check simple factors: Caps Lock, language settings, and whether any password manager is auto-filling an outdated value.
Beyond typing, you should think about how the archive was created. Some encrypted archives only protect the file contents, while others also encrypt filenames and metadata. Safe techniques outlined in ways to inspect your protected archive without harming data ↗️ highlight the importance of using tools that respect these settings instead of trying to “peek inside” with untrusted utilities.
If extraction works but shows warnings, don’t immediately delete the original archive. Keep it as a reference until you have verified that the extracted files are complete and healthy. That way, if you discover later that a critical file is missing or corrupted, you can revisit the archive with updated tools or more conservative extraction options.
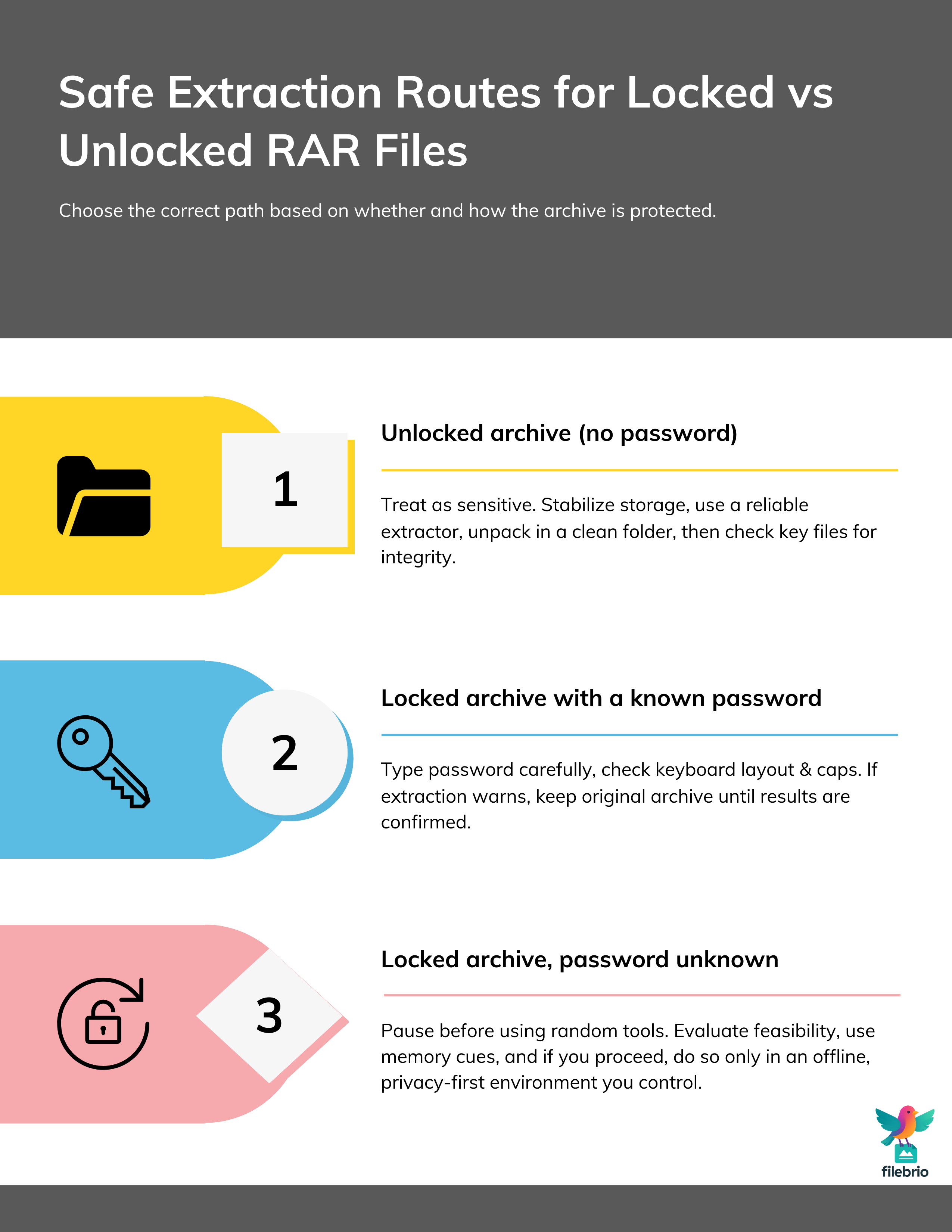
🧩 When You Don’t Know The Password: Limits And Safe Paths
Things become more complicated when you don’t know the password but still need to access the archive. Here, the temptation to search for “instant unlock” tools is strongest — and also where you can cause the most damage to your privacy or compliance obligations. Before doing anything, pause and recognize that some combinations of format and password strength may be effectively unopenable in practice.
High-level guidance such as ways to improve RAR protection with safe retention ↗️ exists partly because strong, well-managed passwords are meant to resist guessing. If an archive was protected using modern encryption and a long, unpredictable password, no tool — online or offline — can guarantee access. In those cases, your energy is better spent on password reconstruction (using your own memory cues and metadata) and on preventing similar situations in the future.
If you decide that a recovery attempt is warranted, it should happen within a structured, offline environment that respects ownership and legal boundaries. Educational utilities such as a RAR password strength estimator ↗️ can help you understand the scale of any realistic attempt before you invest time or resources. They do not reveal secrets or accept uploads of your archive; instead, they show conceptually how length and complexity affect feasibility, which is critical input when deciding whether to proceed at all.
🛡️ Secure Offline Solution For Sensitive Or Fragile Archives
For archives containing confidential personal data, business secrets, or regulated information, uploading to public “unrar” or “online extractor” sites is rarely acceptable. Even if those services are honest, you have no meaningful visibility into how long they keep your files, where they store them, or whether any secondary analysis is performed. The risk is especially high when you are dealing with key backups or one-of-a-kind historical archives.
Privacy-first guidance like why opening RAR files online risks your protected data ↗️ underscores the importance of keeping encrypted archives within systems you control. A dedicated offline toolkit can offer structured workflows for diagnostics, repair, and lawful recovery without ever sending data to third parties. It also makes it easier to implement and enforce policies: only one class of tool is approved, and it always runs on your own devices or servers.
Within such an environment, you can combine safe extraction practices with responsible escalation paths. For example, if routine diagnostics show that an archive is badly corrupted, you might involve specialists or higher-level support — but still within your offline framework, never via anonymous uploads — ensuring that both technical and legal risks are managed consistently.
________________________
FileBrio RAR Master — a secure, offline Windows toolkit for regaining access to your own password-protected RAR / WinRAR archives while keeping all data strictly on your device.
- Offline-only processing — never uploads your archives.
- Smart issue detection — password vs corruption.
- Fast recovery workflow optimized for legitimate ownership.
⬇️ Download FileBrio RAR Master
Reminder: FileBrio RAR Master is intended only for archives you own or are explicitly authorized to access. All operations run locally on your PC.
________________________
📋 After Extraction: Verifying Results And Cleaning Up
Safe extraction does not end when the progress bar reaches 100%. You still need to confirm that what came out of the archive is complete, consistent, and stored appropriately. This is especially important for long-term backups, legal evidence, or any content that might be used in audits or investigations.
Good practice includes running through a simple verification checklist: do the number of files and folders match expectations? Do file sizes and modification dates look plausible? Can key documents be opened without errors? Concepts from how to confirm integrity of your extracted RAR contents ↗️ can guide you here, emphasizing checks that are easy to automate or document for future reference.
Once you are satisfied, consider whether it’s appropriate to keep the extracted copies as-is, re-archive them in a modern format, or move them to more controlled storage. At the same time, you may want to tidy up any partial output from earlier failed attempts, clearly separating “known good” data from incomplete or suspicious files so that nobody mistakes a broken export for a verified one later.
📦 Long-Term Practices For Safer RAR Use
The most reliable way to avoid stressful extraction scenarios is to build safer habits from the moment you create an archive. That means choosing strong, well-documented passwords, labeling archives clearly, storing them on dependable media, and defining internal rules for which tools are used to open them. It also means educating users about what not to do, especially when they are under pressure and tempted by “instant fix” websites.
Online services that promise to “extract RAR files in the browser” may look convenient, but as highlighted in resources like safer local alternatives to open your locked RAR archives ↗️, they often trade privacy for simplicity. Building a culture of offline, policy-aligned handling — backed by clear documentation and a standard toolkit — keeps your data where it belongs and makes safe extraction the default, not an exception.
Over time, these practices turn RAR archives from risky black boxes into manageable, well-understood assets. When everyone knows how to create, store, and extract them safely, the phrase “unzipping or unrarring” goes back to being what it should have been all along: a routine task, not a crisis.
⚖️ Legal Reminder
This article is provided for general informational and educational purposes only. Any examples, scenarios, or references to password recovery, archive security, or related tools (including FileBrio RAR Master or similar software) are intended solely to help you better understand how to protect and manage your own data.
You may only apply any techniques, workflows, or tools described here to files and archives that you fully own or are explicitly and verifiably authorized to access. Attempting to bypass, remove, or recover passwords for third-party data without clear permission may violate criminal law, civil law, or internal company policies in your jurisdiction.
Nothing in this article constitutes legal advice. Laws and regulations differ between countries and organizations, and you are solely responsible for ensuring that your actions comply with all applicable legislation, contracts, and internal policies. If you are unsure whether a particular action is lawful or permitted, consult a qualified legal professional before proceeding.
📚 See Also
- Extract RAR Files Online Without A Password: Why Online Tools Are Risky And Safer Offline Methods ↗️
- What To Do When You Can’t Open Your Own RAR File (Even If The Reason Is Unknown) ↗️
- How To Diagnose A Locked RAR Archive Without Risking Data Loss ↗️
- How To Repair Damaged RAR Files Safely (What You Should And Shouldn’t Do First) ↗️
- What To Do When WinRAR Shows “Unexpected End Of Archive” ↗️
- RAR Recovery Records And .rev Volumes: How They Help Protect And Restore Data ↗️