
Unlocking Password-Protected RAR/WinRAR Archives: Safe Methods for Legitimate Access
Few things are more frustrating than hitting a password prompt on a RAR or WinRAR archive you know is yours — only to realize you can’t remember the exact password, or the file refuses to open even when you’re sure you typed it correctly. Maybe it’s an old project backup, a legal archive, or a personal collection stored years ago on a now-retired machine. The data matters, but the door seems firmly shut.
In that situation, many users start searching for shortcuts or “miracle” tools. But modern RAR encryption is designed to resist unauthorized access, and there is no secret reset button. At the same time, if you are the rightful owner, you do have safe and legitimate ways to approach the problem — methods that respect cryptographic limits, protect your privacy, and keep you within legal boundaries while improving your chances of regaining access.
🧭 Navigation
Important
The information provided in this article applies exclusively to RAR / WinRAR archives for which you have full, demonstrable ownership or properly documented authorization. If you are not the rightful owner of the data, do not directly control it, or cannot clearly prove permission to access it, you must stop immediately. Attempting to access, recover, or modify data without explicit authorization may violate criminal law, civil statutes, corporate compliance requirements, and privacy regulations in many jurisdictions. You alone are responsible for ensuring that your actions are lawful and properly permitted before proceeding.
📌 TL;DR — What “Unlocking” Really Means for RAR Archives You Own
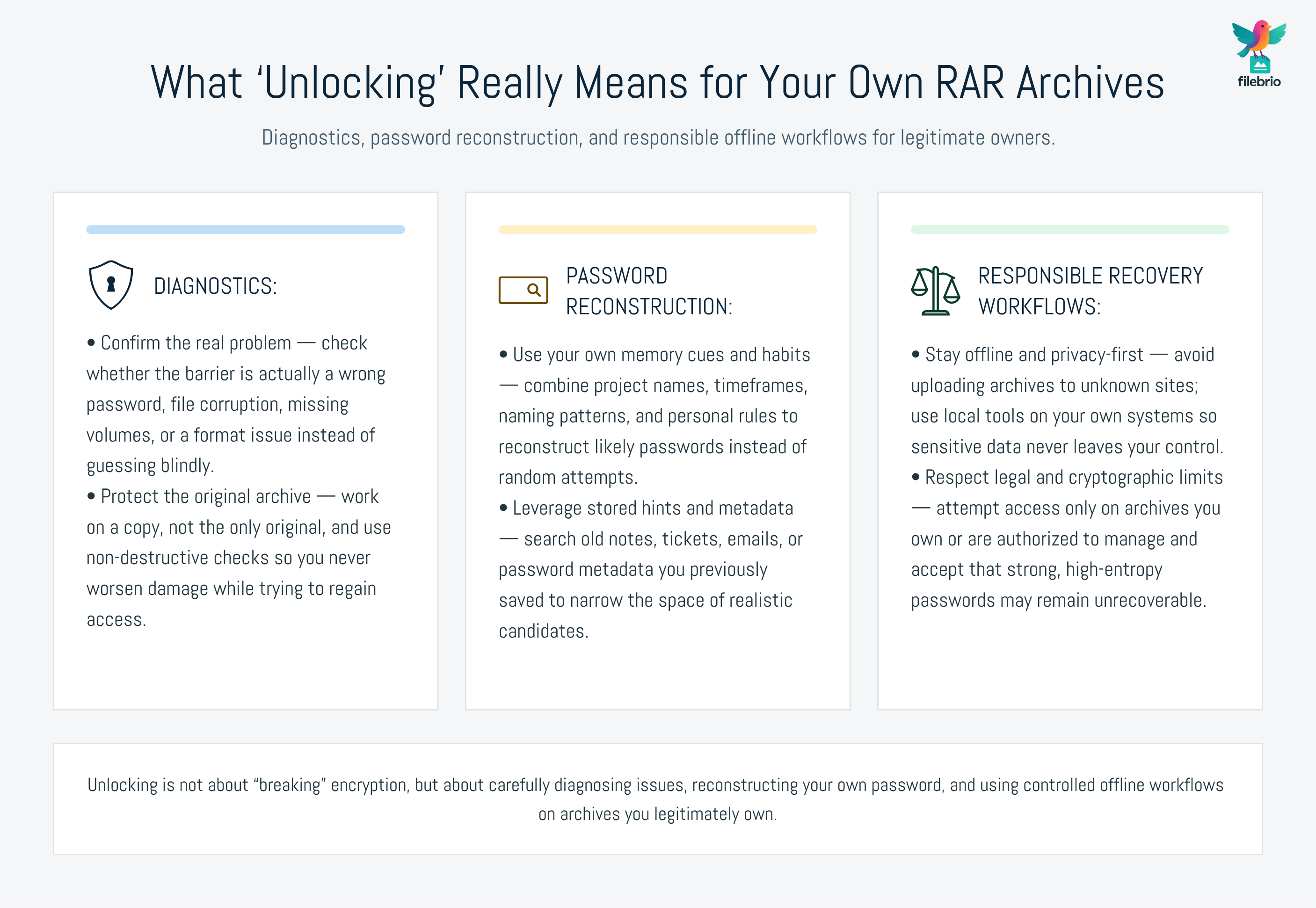
Short version: “Unlocking” a password-protected RAR archive is not about bypassing encryption; it is about regaining access to your own data in a way that respects cryptographic limits, legal requirements, and privacy. Modern RAR encryption (especially RAR5) offers strong protection, meaning there is no simple reset or universal backdoor. If you legitimately own the archive, your options center on three pillars: diagnostics (confirming whether the problem is really the password or file corruption), password reconstruction (using your own memory cues and habits), and responsible recovery workflows (using offline tools on local copies, with clear ownership and documented steps).
Before taking any action, you should: (1) verify that you are entitled to access the archive, (2) confirm that the file is intact and not simply corrupted, (3) use structured, non-destructive checks on a copy instead of experimenting on the only original, and (4) rely on privacy-first, offline tools rather than uploading sensitive material to the internet. If these steps confirm that recovery is appropriate and technically feasible, you can proceed with carefully controlled methods to attempt access, always accepting that extremely strong, high-entropy passwords may still be unrecoverable in practice.
🧠 Understanding RAR Password Protection and Realistic Limits
To talk about “unlocking” a RAR archive responsibly, you first need to understand what the password actually controls. In modern RAR formats, the password is not just a simple key you can “reset” — it is part of a cryptographic process that governs whether the contents can be decrypted at all.
A high-level overview like how encryption controls access to your protected RAR contents ↗️ explains that:
- The password is transformed through a key derivation function into a cryptographic key.
- That key is used to decrypt file data (and optionally headers, depending on settings).
- Without the correct key, the data remains mathematically unreadable, not just “hidden.”
For you as an archive owner, this has two important implications:
- No “reset” concept. Unlike an online account with an email-based reset, RAR archives have no built-in password reset mechanism. If you lose the password, the software has no alternative path to grant access.
- Strong passwords can be effectively unrecoverable. If your original password was long and random enough, no realistic amount of computing power will recover it within a useful timeframe.
Understanding these limits early helps you set realistic expectations and avoid unsafe tools that claim to “break” strong encryption instantly. It also reinforces why planning and safe storage of password metadata are so important.
⚖️ When You Can Unlock a RAR Archive — And When You Shouldn’t
Legitimate unlocking is not just a technical question; it’s also a question of rights and responsibilities. Even the safest method becomes problematic if used on archives you do not own or control.
Before doing anything, ask two fundamental questions:
- Do I own this archive or act on behalf of the lawful owner?
- Can I demonstrate that ownership or authorization if asked?
Resources like legal considerations when working with encrypted archives ↗️ and how to ensure you’re recovering only RAR files you own ↗️ provide practical guidance on staying within appropriate boundaries.
If the archive clearly belongs to you (personal files, business archives under your responsibility, or customer data you are contracted to manage), then carefully controlled access recovery is reasonable. If you cannot establish such ownership, the safest and most compliant option is not to attempt unlocking at all, and to refer the matter back to the rightful owner or appropriate authority.
💼 All-in-One Workspace for Unlocking Your Own RAR Archives Safely
In real life, password-protected archives rarely exist in isolation. A typical user or team might have:
- clean, healthy unlocked archives that just need safe extraction;
- locked archives with half-remembered passwords;
- archives that look “locked” but are actually corrupted;
- older RAR4 archives and newer RAR5 archives mixed together.
Trying to handle all of this with random tools — one for extraction, another for diagnostics, another for repair — quickly becomes hard to manage and even harder to audit. That’s where a unified, offline workspace helps.
FileBrio RAR Master is designed as a single environment focused on working with your own RAR and WinRAR archives. Instead of juggling multiple utilities, you can:
- inspect whether archives are locked, corrupted, or both;
- review structure and metadata before deciding how to proceed;
- handle extraction and diagnostics without sending data online;
- standardize your workflow across personal and team scenarios.
For a broader picture of how this fits into your daily work, the FileBrio RAR Master features overview ↗️ shows how diagnostics, repair options, and access workflows come together in one toolkit.
________________________
FileBrio RAR Master — part of the FileBrio Office Suite — is a privacy-first, offline Windows toolkit for diagnosing and safely regaining access to your own password-protected RAR / WinRAR archives.
- Local processing only — nothing leaves your PC.
- Smart diagnostics to separate password issues from corruption.
- Owner-verified recovery workflows designed strictly for legitimate use.
Reminder: FileBrio RAR Master may be used only with archives you own or are explicitly authorized to access. It performs all analysis and recovery operations locally on your device, without uploading data anywhere.
________________________
🧪 Safe Workflow Before Any Password Recovery Attempt
Before you attempt any form of access recovery, it’s critical to stabilize your situation and rule out misunderstandings. A structured workflow protects your data and saves time.
Step 1 — Verify ownership and context
Confirm that the archive is yours or under your professional responsibility. Recall when it was created, who created it, and why. A methodical checklist like how to assess your situation after losing a RAR password ↗️ helps you gather this context calmly.
Step 2 — Diagnose the technical issue
Don’t assume “wrong password” is the only explanation. RAR errors can indicate many things. A structured diagnosis, such as described in how to diagnose a locked RAR archive without risking data loss ↗️, walks you through:
- checking for incomplete downloads or missing multi-volume parts;
- observing specific error messages and their likely causes;
- distinguishing encryption issues from file corruption.
Step 3 — Work on a copy, not the original
Always duplicate the archive and run experiments on the copy. If a tool writes to the file or a repair attempt goes wrong, your original remains untouched.
Step 4 — Decide if recovery is realistically feasible
For example, a short password you roughly remember is very different from a long random string with no recollection at all. A high-level approach like how to evaluate safe options for regaining access to a RAR archive you own ↗️ helps you judge whether further attempts are reasonable or whether the archive should be treated as unrecoverable.

🔑 Legitimate Methods to Regain Access to Your Own RAR Archives
Once you’ve confirmed both ownership and feasibility, you can apply legitimate techniques that focus on your own memory, your own archives, and your own infrastructure.
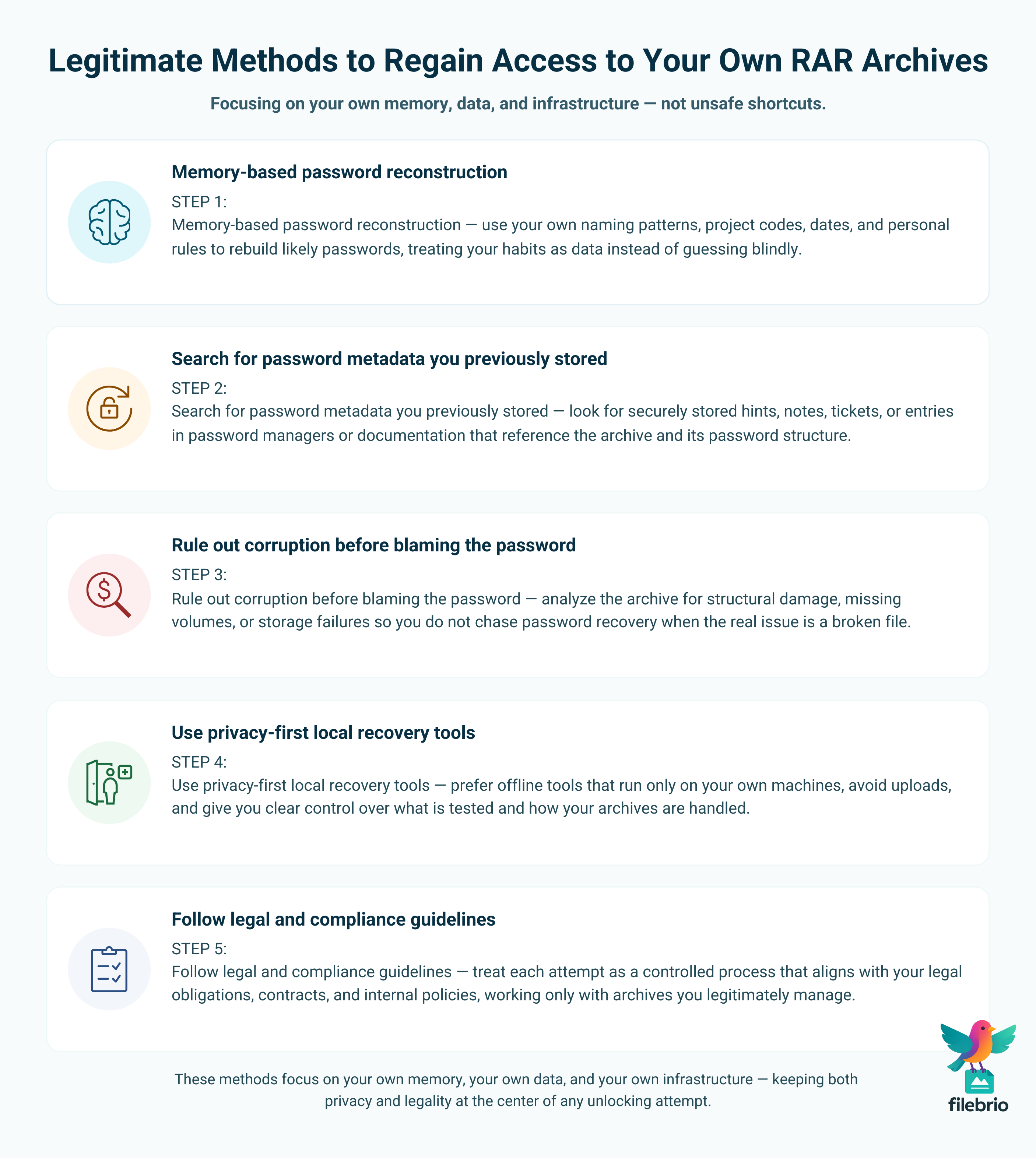
1. Memory-Based Password Reconstruction
Most archive passwords are derived from meaningful elements: project names, internal codes, personal patterns, or dates. Analyzing your own habits can pay off, especially when combined with notes, emails, or naming conventions that jog your memory.
For instance, if your organization uses consistent naming schemes for projects and archives, those conventions may be a strong clue. Articles about how naming and behavior patterns relate to password choices can guide your reflection and help you structure your own recall process instead of guessing randomly.
2. Searching for Password Metadata You Previously Stored
In well-organized environments, password metadata is stored separately in a secure form — not the full password, but hints, patterns, or references. Approaches described in long-term access guides emphasize keeping such metadata safe and accessible so that future you (or future team members) are not locked out.
3. Ruling Out Corruption Before Assuming Password Failure
Corruption can masquerade as “wrong password” symptoms. To avoid chasing the wrong problem, analyze your archive’s structure and health. If the file is partially damaged, repair options may be necessary before any password-related work makes sense. Clear workflows for understanding error messages and structural issues help ensure you don’t misinterpret symptoms.
4. Using Privacy-First Local Recovery Tools
When you decide to use specialized software to help regain access, keep everything offline. Guidance like why offline recovery tools are safer for privacy ↗️ explains how local-only operation avoids exposing your sensitive data to third parties.
Equally important is avoiding tools that make unrealistic promises. Resources such as why online RAR password tools often fail ↗️ highlight the limitations and risks of web-based “unlockers” that cannot realistically break strong encryption but may still collect or mishandle your files.
5. Following Legal and Compliance Guidelines
Especially in business settings, you should treat each access attempt as a controlled process. Align your actions with broader guidance like how to restore access to RAR archives using safe and legal methods ↗️, which emphasizes traceability, documented authorization, and working only with archives you own or manage legitimately.
For users who need to explore free tooling options while staying private and lawful, high-level overviews such as safe offline tools for accessing your locked RAR archive ↗️ can help you choose utilities that respect your data and your boundaries.
🛡️ Secure Offline Solution for Password-Protected RAR Archives
At the center of a safe unlocking strategy is your choice of tools. An offline, purpose-built toolkit provides the technical foundation for all the workflows described above, as long as it is used only on archives you own and in line with law and policy.
FileBrio RAR Master is specifically designed as a privacy-first environment for diagnostics, access recovery, and repair of RAR and WinRAR archives:
- It operates entirely on your local machine — no cloud uploads.
- It helps you distinguish between corrupted and properly encrypted archives.
- It supports workflows for opening archives once you have the right password.
- It integrates with broader organizational policies around secure handling.
For cases where you know the password but simply need a reliable way to open and work with protected archives, the FileBrio RAR Master: File Unlocker ↗️ is designed as a safe RAR file unlock utility for your own data, running entirely offline.
When the issue is a forgotten password and legitimate recovery is justified, the FileBrio RAR Master: Password Recovery ↗️ component provides a controlled way to work with your own encrypted archives inside a closed environment. And to ensure your practices stay aligned with responsible use, administrators can refer to the FileBrio RAR Master: Support & Legal (Responsible Use) ↗️ page when designing internal procedures.
For deployments across multiple machines or for users who simply need a trustworthy installer, the official FileBrio Office Suite: Download Page ↗️ serves as the central, verified source for obtaining and updating the toolkit.
________________________
FileBrio RAR Master — a secure, offline Windows toolkit for regaining access to your own password-protected RAR / WinRAR archives while keeping all data strictly on your device.
- Offline-only processing — never uploads your archives.
- Smart issue detection — password vs corruption.
- Fast recovery workflow optimized for legitimate ownership.
⬇️ Download FileBrio RAR Master
Reminder: FileBrio RAR Master is intended only for archives you own or are explicitly authorized to access. All operations run locally on your PC.
________________________
📈 How to Avoid Getting Locked Out Again in the Future
Once you’ve successfully unlocked a difficult archive, it’s the perfect time to upgrade your long-term habits so future access is easier and safer.
1. Design Passwords for Both Strength and Longevity
Aim for passwords that are hard for others to guess but easy enough for you to reconstruct later. That might mean using structured phrases, internal project concepts, or consistent rules that you can safely document as hints instead of full passwords.
2. Store Password Metadata and Ownership Records
Keep a secure, centralized record of who owns which archives, what they roughly contain, and how their protection is structured. This doesn’t require storing plain-text passwords, but it does mean leaving enough information that you or your colleagues can understand the archive years later. In organizations, formal policies for managing encrypted archives help ensure long-term continuity.
3. Maintain Healthy Storage and Backups
Many “unlocking” issues are actually storage issues. Use redundant, monitored storage for important archives, along with periodic checks and versioned backups, so that a single corrupt copy does not become a single point of failure.
4. Build a Standard Response Plan
Whether you’re an individual or part of a team, define a small playbook for what to do when an archive won’t open: verify ownership, duplicate the file, run basic diagnostics, and only then consider more advanced steps. Having a plan reduces panic, avoids risky shortcuts, and keeps you aligned with your own safety and compliance standards.
5. Educate Yourself and Your Team
Finally, treat safe access to encrypted archives as part of your broader digital hygiene. Understanding how passwords, encryption, storage, and behavior fit together makes it far less likely that you’ll face a truly unrecoverable situation in the future.
⚖️ Legal Reminder and Responsible Use
This article is provided for general informational and educational purposes only. Any examples, scenarios, or references to password recovery, archive security, or related tools (including FileBrio RAR Master or similar software) are intended solely to help you better understand how to protect and manage your own data.
You may only apply any techniques, workflows, or tools described here to files and archives that you fully own or are explicitly and verifiably authorized to access. Attempting to bypass, remove, or recover passwords for third-party data without clear permission may violate criminal law, civil law, or internal company policies in your jurisdiction.
Nothing in this article constitutes legal advice. Laws and regulations differ between countries and organizations, and you are solely responsible for ensuring that your actions comply with all applicable legislation, contracts, and internal policies. If you are unsure whether a particular action is lawful or permitted, consult a qualified legal professional before proceeding.
🔗 See Also: Related Guides on Safe RAR Access
- RAR/WinRAR File Passwords Explained: How Encrypted Archives Work and What Access Options You Have ↗️
- How to Evaluate Safe Options for Regaining Access to a RAR/WinRAR Archive You Own ↗️
- Open RAR Files Without a Password? What’s Possible, What Isn’t, and How to Access Your Data Safely ↗️
- Restoring Access to RAR/WinRAR Archives: Safe and Legal Methods for Handling Your Own Files ↗️
- Why Offline Recovery Tools Are Safer for Privacy ↗️
- Free RAR/WinRAR Password Recovery Tools: Safe, Offline Options for Accessing Your Own Files ↗️
- Why Online RAR Password Tools Fail — And What Legitimate Users Can Do Instead ↗️