
How to Strengthen RAR Archive Security While Preserving Future Access
You encrypt a RAR archive to keep your data safe — then years later, you discover that “safe” has quietly turned into “unopenable.” The password is fuzzy, team members have changed, devices have been replaced, and now that carefully protected archive is effectively gone. Strong security without a plan for future access can feel less like protection and more like self-inflicted data loss.
The good news: you don’t have to choose between “weak but convenient” and “strong but unusable.” With a bit of planning, you can design RAR archives that are genuinely hard to misuse or leak while still being realistically accessible to you (and your authorized team) in five or ten years. This article shows how to balance those two goals: tightening security without building an impenetrable wall between you and your own information.
We’ll stay strictly within legal, ethical boundaries. Everything here applies only to RAR archives that you own or are explicitly authorized to manage. The aim is to help you avoid accidental lockouts, data loss, and privacy mistakes — not to access data that doesn’t belong to you.
🧭 Navigation
Important
The information provided in this article applies exclusively to RAR / WinRAR archives for which you have full, demonstrable ownership or properly documented authorization. If you are not the rightful owner of the data, do not directly control it, or cannot clearly prove permission to access it, you must stop immediately. Attempting to access, recover, or modify data without explicit authorization may violate criminal law, civil statutes, corporate compliance requirements, and privacy regulations in many jurisdictions. You alone are responsible for ensuring that your actions are lawful and properly permitted before proceeding.
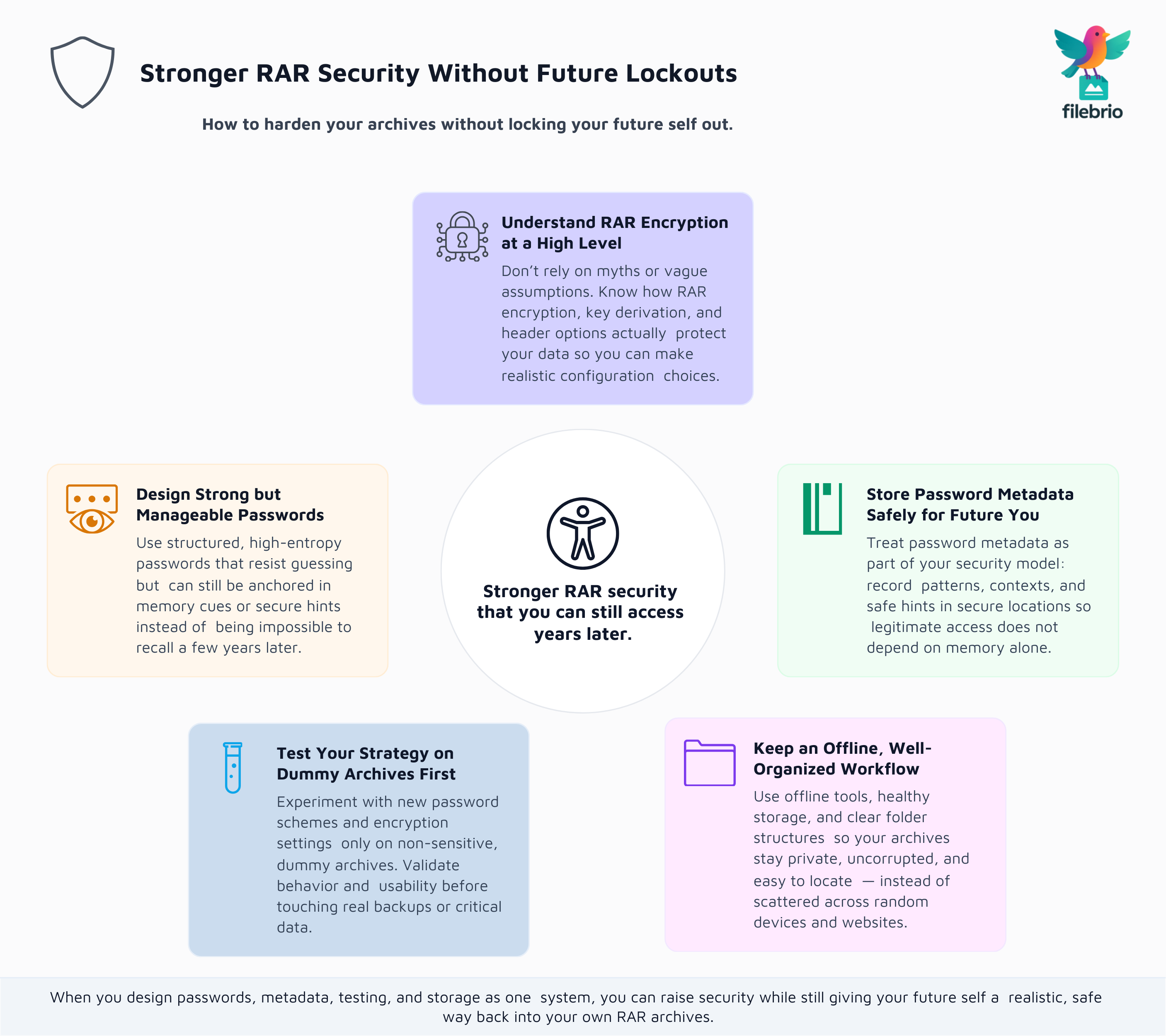
✨ TL;DR — Stronger Security Without Future Lockouts
Strengthening RAR archive security doesn’t just mean choosing a “stronger” password or flipping every advanced option you can find. In practice, real security is a trade-off between resistance to misuse and your own ability to regain access later. Overly complex passwords with no metadata, scattered storage, and undocumented team practices often lead to the same outcome as weak security: permanent loss of important information.
A safer model is to treat each RAR archive as part of a long-term security plan. That plan includes:
- Understanding RAR encryption at a high level so you don’t rely on myths or unrealistic expectations.
- Designing strong, structured passwords that resist guessing but are still manageable using secure memory cues and written hints.
- Storing password metadata safely so future you (or your authorized colleagues) can reconstruct access when memory inevitably fades.
- Testing your strategy on dummy archives so you never experiment directly on your only copy of a sensitive RAR file.
- Keeping everything offline and well-organized to avoid leaks, corruption, and confusion across devices and storage mediums.
If you adopt this mindset, you can raise the bar for attackers while keeping archives realistically accessible years from now. The key is to design your passwords, metadata, and workflows as a single system — one that assumes humans forget, organizations change, and hardware fails, but your future self still deserves a safe path back to the data.
🔐 Why Stronger RAR Security Can Backfire If You Ignore Future Access
Most security problems are obvious in hindsight: “We encrypted everything with a very strong passphrase… and then the only person who knew it left the company.” Or: “We followed best practices, used complex passwords, and encrypted headers — but nobody kept structured metadata, so now every backup looks like a black box.”
Problems like this rarely come from weak algorithms. They come from human and organizational factors:
- People forget even carefully chosen passwords under stress or after long gaps.
- Teams change; the person who understood the archive structure might be gone.
- Documentation lives in random files or personal notes that never make it into a shared, secure location.
To understand the cryptographic side of the equation, it helps to review how RAR4 and RAR5 secure your protected data ↗️. Once you see how strong modern RAR encryption really is, it becomes clear that “we’ll remember the password somehow” is not a backup strategy — it’s the single point of failure.
This is why strengthening security must always go hand-in-hand with future-access planning. A design that doesn’t account for memory, turnover, and device changes is incomplete, no matter how impressive the cipher or key length looks on paper.
🧠 High-Level View: How RAR Encryption Protects Your Data
Before you can decide how much to “strengthen” your RAR archives, you need a realistic view of what RAR encryption already does by default.
At a high level, RAR uses modern encryption and key-derivation functions to ensure that, without the correct password, your data is effectively unreadable. The details are explored more deeply in how encryption controls access to your protected RAR contents ↗️, but three concepts matter most for configuration decisions:
- Encryption mode: Modern RAR formats can protect both the contents and, when enabled, filenames and headers.
- Key derivation: The password is processed through many computation rounds to slow down large-scale guessing attempts.
- Entropy and length: The practical difficulty of guessing a password depends on how long it is and how unpredictable its structure is.
For a conceptual grasp of the last point, see how length impacts protection of your RAR password ↗️. The takeaway is that you often gain far more security by improving password quality and entropy than by enabling every advanced toggle you can find without a plan.
When you understand these basics, “strengthening security” stops being a vague idea and becomes a series of concrete choices: how strong should passwords be, what metadata is stored, whether headers are encrypted, and how you will later prove ownership and reconstruct access.
🧰 All-In-One RAR Security Toolkit for Safer Hardening
Once you start thinking in terms of long-term security and future access, it quickly becomes clear that you don’t just need “a tool” — you need a structured environment that supports diagnostics, planning, and safe testing without scattering your data across random utilities.
FileBrio RAR Master, part of the FileBrio Office Suite, is designed as an all-in-one RAR recovery and diagnostics toolkit that fits this mindset. Instead of juggling multiple apps, you can:
- Review archive formats, header options, and basic health checks inside one app capabilities overview ↗️.
- Evaluate how different protection settings behave on test archives before you touch production data.
- Keep all operations local, integrating the tool into an offline-first workflow that respects privacy and compliance.
Because configuration and diagnostics happen in a single environment, it’s easier to build a policy: which encryption options your organization uses, how passwords are structured, how metadata is recorded, and what steps must be followed before anyone changes an archive’s protection level. When you’re ready to deploy this approach in practice, you can obtain the suite from the official FileBrio Office Suite installer hub ↗️ and standardize it across your systems.
________________________
FileBrio RAR Master — part of the FileBrio Office Suite — is a privacy-first, offline Windows toolkit for diagnosing and safely regaining access to your own password-protected RAR / WinRAR archives.
- Local processing only — nothing leaves your PC.
- Smart diagnostics to separate password issues from corruption.
- Owner-verified recovery workflows designed strictly for legitimate use.
Reminder: FileBrio RAR Master may be used only with archives you own or are explicitly authorized to access. It performs all analysis and recovery operations locally on your device, without uploading data anywhere.
________________________
🧩 Designing Strong Yet Manageable RAR Passwords
Human memory has limits. If you only focus on maximum complexity, you will eventually create a password that is both cryptographically strong and practically unusable. The goal is to design structured passwords that offer high entropy but can still be anchored in controlled memory cues or secure written hints.
Helpful perspectives include:
- Balancing strength and recall: how to design strong memorable RAR passwords ↗️ explains how length, structure, and personal relevance can coexist without collapsing into something obvious.
- Avoiding fragile habits: Many users repeat small patterns or reuse parts of passwords in ways that feel safe but actually make guessing easier.
- Planning for forgetting: Even a carefully designed password will fade over time, which is why password design must be paired with metadata and storage strategies.
From a “protect yourself” point of view, it’s often better to have a slightly less complex password with excellent metadata and retention practices than a theoretically perfect password that nobody can reconstruct later. The right balance depends on the sensitivity of your data and your threat model, but in all cases, design and documentation must be considered together.
To reduce the risk of self-inflicted data loss, it’s also worth studying mistakes that endanger your protected RAR files ↗️. Many of those mistakes stem from overconfidence (“I’ll never forget this”) or oversimplification (“I’ll just add a few symbols”). Treat those patterns as cautionary tales when designing your next archive.
🗂️ Storing RAR Password Metadata for Future You
Once you accept that even the best-designed passwords can be forgotten, the obvious next step is to create a metadata layer that helps you reconstruct access without exposing the password itself. Done correctly, this becomes your safety net: future you doesn’t have to guess blindly, because there is a structured record of how the password was chosen, where it is expected to be stored, and how to confirm ownership.
For personal archives, this is covered in depth in how to organize metadata for your RAR passwords safely ↗️. The core ideas include:
- Separating exact passwords from carefully worded hints stored in encrypted notes or vaults.
- Documenting which naming conventions, themes, or structures you tend to use for each category of archive.
- Recording dates, purposes, and storage locations so future you can quickly determine whether an archive is still relevant.
For team or shared archives, you need additional structure, as outlined in how teams can organize shared RAR password metadata ↗️. In that context, good metadata also answers questions like:
- Who is responsible for maintaining access?
- Where are primary and backup records stored?
- How are departures, role changes, and handovers handled?
When metadata is treated as an integral part of security, archives become both safer and more usable. Passwords can be strong because you no longer rely on memory alone; future access is preserved because hints, roles, and locations are documented in a secure, structured way.

👥 Coordinating Team and Enterprise Access Policies
In organizations, archive security is rarely a purely technical problem. It’s also a matter of policy and coordination. A single locked RAR archive might represent years of project data, compliance evidence, or legally significant records — losing access can be far more damaging than a single lost file on a personal machine.
That’s why it’s important to build a standard, documented process for how teams create, protect, and share encrypted RAR archives. how teams can preserve long-term access to encrypted RAR files ↗️ highlights good practices like:
- Defining roles for who can create and who can open certain categories of archives.
- Ensuring that password metadata is stored in shared, secure systems rather than personal notes.
- Planning for audits and incident reviews so that you can prove ownership and access history if needed.
These policies should be aligned with your broader security and compliance framework. For example, if your organization has retention rules or legal obligations, your RAR archive practices should reflect how long data must remain accessible, under what conditions, and who is allowed to change passwords or protection levels.
Getting this right dramatically reduces the likelihood of “mystery archives” appearing years later with no one able to explain what they contain or who can open them.
🧪 Using Dummy Archives to Test Your Security Strategy
Any change to your security approach — stronger passwords, new encryption options, stricter metadata rules — should be tested before you apply it to real data. The safest way to do that is through dummy archives: RAR files containing only non-sensitive content that you create specifically for experimentation.
As described in how to test RAR protection with your dummy files ↗️, this gives you a sandbox where you can:
- Validate that your password patterns are usable across different devices and platforms.
- Confirm that your chosen encryption settings (including header protection) behave as expected.
- Rehearse recovery and diagnostic steps without risking actual business or personal data.
Once you’ve run through your process on dummy archives multiple times, you can be far more confident when applying the same design to production backups. If new policies make access confusing or fragile even in testing, you can adjust them early — long before any irreplaceable data is put at risk.
This kind of practice is especially useful if you’re introducing new team members to your RAR security standards. It allows them to learn and make mistakes in a controlled environment rather than on live archives.
🛡️ Secure Offline Hardening and Storage Practices
Even the best password and metadata strategy can be undermined by poor storage habits. Corrupted drives, inconsistent backups, and risky online tools have caused far more real-world damage than theoretical cryptographic attacks. Strengthening RAR archive security must therefore include where and how the archives are stored and handled.
An offline-first mindset is a good foundation. why offline tools keep your encrypted RAR data private ↗️ outlines the privacy advantages of keeping archives and diagnostics on systems you control instead of uploading them to unknown services. On top of that, you should pay attention to physical and logical storage factors, like:
- Using multiple, verified storage locations (e.g., internal drives plus encrypted external backups).
- Checking media health periodically to catch early signs of failure.
- Avoiding untrusted cloud-based “unlock” or “viewer” tools that may archive and inspect your data.
For practical guidance, see ways to prevent losing your RAR data on storage devices ↗️. It’s easier to maintain long-term access when your archives are not silently degrading in forgotten folders or on aging drives.
Finally, tools like FileBrio RAR Master can be part of a hardened offline environment: a local application you trust, combined with documented policies, structured backups, and clear contact points. If you need to align your setup with licensing and responsible-use guidelines, the software cost and editions overview ↗️ and responsible recovery guidelines ↗️ provide the licensing, support, and legal framing to integrate the toolkit into formal processes.
________________________
FileBrio RAR Master — a secure, offline Windows toolkit for regaining access to your own password-protected RAR / WinRAR archives while keeping all data strictly on your device.
- Offline-only processing — never uploads your archives.
- Smart issue detection — password vs corruption.
- Fast recovery workflow optimized for legitimate ownership.
⬇️ Download FileBrio RAR Master
Reminder: FileBrio RAR Master is intended only for archives you own or are explicitly authorized to access. All operations run locally on your PC.
________________________
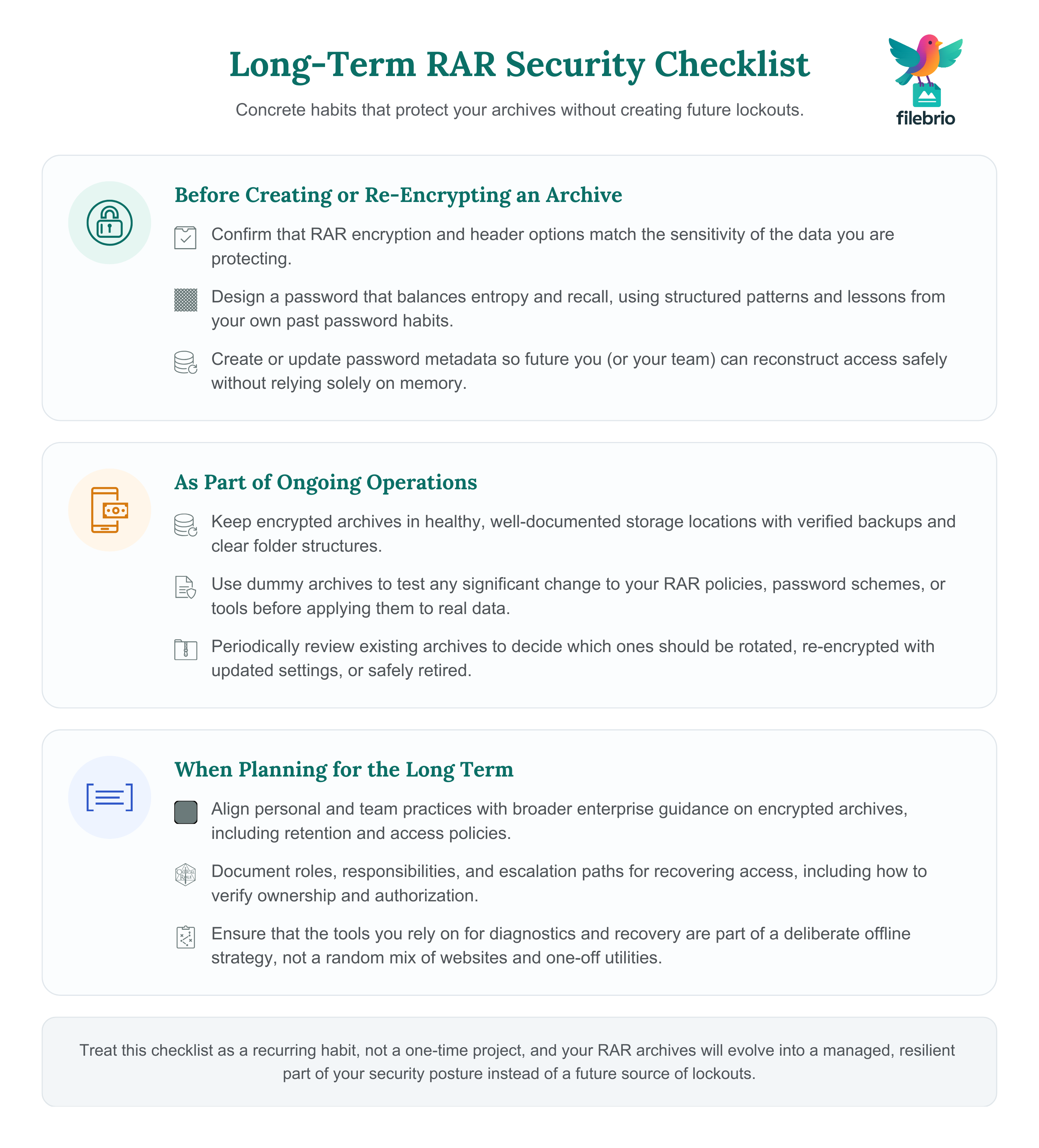
📋 Long-Term Security Checklist: Protect Yourself Without Lockouts
To turn all of this into a concrete “protect yourself” plan, it helps to compress the ideas into a checklist you can revisit whenever you create or revise a RAR archive.
Before creating or re-encrypting an archive:
- Confirm that RAR encryption and header options match the sensitivity of the data.
- Design a password that balances entropy and recall, following lessons from ways to retain long-term memory of your RAR passwords ↗️.
- Create or update password metadata so future you (or your team) can reconstruct access safely.
As part of ongoing operations:
- Keep archives in healthy, well-documented storage locations with verified backups.
- Use dummy archives to test any significant policy or workflow change.
- Periodically review whether certain archives can be rotated, re-encrypted with updated settings, or safely retired.
When planning for the long term:
- Align personal and team practices with broader enterprise guidance, such as in how teams can preserve long-term access to encrypted RAR files ↗️.
- Document roles, responsibilities, and escalation paths for recovering access, including how to verify ownership and authorization.
- Ensure that any tooling you rely on is part of a deliberate offline strategy, not an ad-hoc collection of websites and utilities.
If you treat this checklist as a regular habit rather than a one-time project, your RAR archives will gradually shift from “sealed boxes that might be trouble later” to well-managed, resilient components of your broader security posture.
⚠️ Legal Reminder
This article is provided for general informational and educational purposes only. Any examples, scenarios, or references to password recovery, archive security, or related tools (including FileBrio RAR Master or similar software) are intended solely to help you better understand how to protect and manage your own data.
You may only apply any techniques, workflows, or tools described here to files and archives that you fully own or are explicitly and verifiably authorized to access. Attempting to bypass, remove, or recover passwords for third-party data without clear permission may violate criminal law, civil law, or internal company policies in your jurisdiction.
Nothing in this article constitutes legal advice. Laws and regulations differ between countries and organizations, and you are solely responsible for ensuring that your actions comply with all applicable legislation, contracts, and internal policies. If you are unsure whether a particular action is lawful or permitted, consult a qualified legal professional before proceeding.
📚 See Also: Further Reading on Long-Term RAR Security
- Why RAR5 is More Secure — and What That Means for File Access ↗️
- How to Create Password Policies for RAR Archives in Business Settings ↗️
- Why Old RAR4 Archives Still Matter — and When to Convert Them ↗️
- Understanding Password Encodings in RAR Archives (Unicode, Cyrillic, etc.) ↗️
- How to Avoid Losing Access to Decade-Old RAR Archives ↗️
- Removing or Changing a RAR/WinRAR Password: What’s Possible When You Own the Archive ↗️
- How to Document Ownership of Sensitive Encrypted Archives ↗️