
How Teams Should Store RAR Password Metadata Safely Across Devices and Roles
In many organizations, the problem is not just “we forgot a RAR password” — it is “nobody knows where the password hint, policy, or recovery notes were stored, or who should have access to them.” RAR archives move between laptops, cloud storage, and departments, while the critical metadata that describes how to unlock them gets scattered in emails, spreadsheets, or personal notes.
This article explains how teams can design a safe, auditable way to store RAR password metadata across devices and roles. We focus on archives that your organization owns, with practices that respect privacy, legal obligations, and long-term access — not on any form of offensive activity.
🧭 Navigation
Important
The information provided in this article applies exclusively to RAR / WinRAR archives for which you have full, demonstrable ownership or properly documented authorization. If you are not the rightful owner of the data, do not directly control it, or cannot clearly prove permission to access it, you must stop immediately. Attempting to access, recover, or modify data without explicit authorization may violate criminal law, civil statutes, corporate compliance requirements, and privacy regulations in many jurisdictions. You alone are responsible for ensuring that your actions are lawful and properly permitted before proceeding.
🧾 TL;DR — Team RAR Password Metadata in One View
Teams should treat RAR password metadata as sensitive business information: it must be accessible to the right people, and unavailable to everyone else. That means designing a central model that defines what metadata is kept, who can see it, where it lives, and how it is backed up.
A good approach includes:
- A clear metadata schema (what you store about each archive, not the password itself).
- Storage in hardened systems (team password managers or secure documentation tools, not ad hoc sheets).
- Role-based access control so only relevant roles can view or edit specific entries.
- Auditing and ownership documentation for regulated or sensitive archives.
- Offline, privacy-first tooling when you need to diagnose or recover access.
The rest of this article walks through how to design that system across devices, roles, and departments while staying within legal and ethical boundaries.
👥 Why Teams Need Shared RAR Password Metadata
In a personal scenario, you can often rely on your own memory and a private note system. In a team environment, that breaks down quickly. People change roles, devices are replaced, and archives may outlive the original creators by many years. Relying on one engineer’s or one manager’s memory is fragile.
To understand individual habits versus team practices, it can help to first look at guidance on personal metadata storage such as how to maintain continuity over time, and then adapt those ideas to organizations. At the team level, however, you must add governance: approval, auditing, and shared processes that survive staff changes and mergers.
| Context | Primary Risk | Why Metadata Matters |
|---|---|---|
| Project archives shared across departments | Key people leave, and nobody remembers how access was set up | Metadata records where passwords are kept, who owns them, and how to rotate them safely |
| Client or customer deliverables | Access is lost just when the client needs historical data | Metadata links archives to contracts, contacts, and retention periods |
| Regulated or legal matters | Failure to prove who had access or why | Metadata supports evidentiary trails and internal policy enforcement |
For high-level guidance on keeping encrypted archives available across longer time frames in organizations, resources such as how teams can preserve long-term access to encrypted RAR files ↗️ can help frame the lifecycle perspective you’ll need.
🧱 Designing a Team-Safe Metadata Model
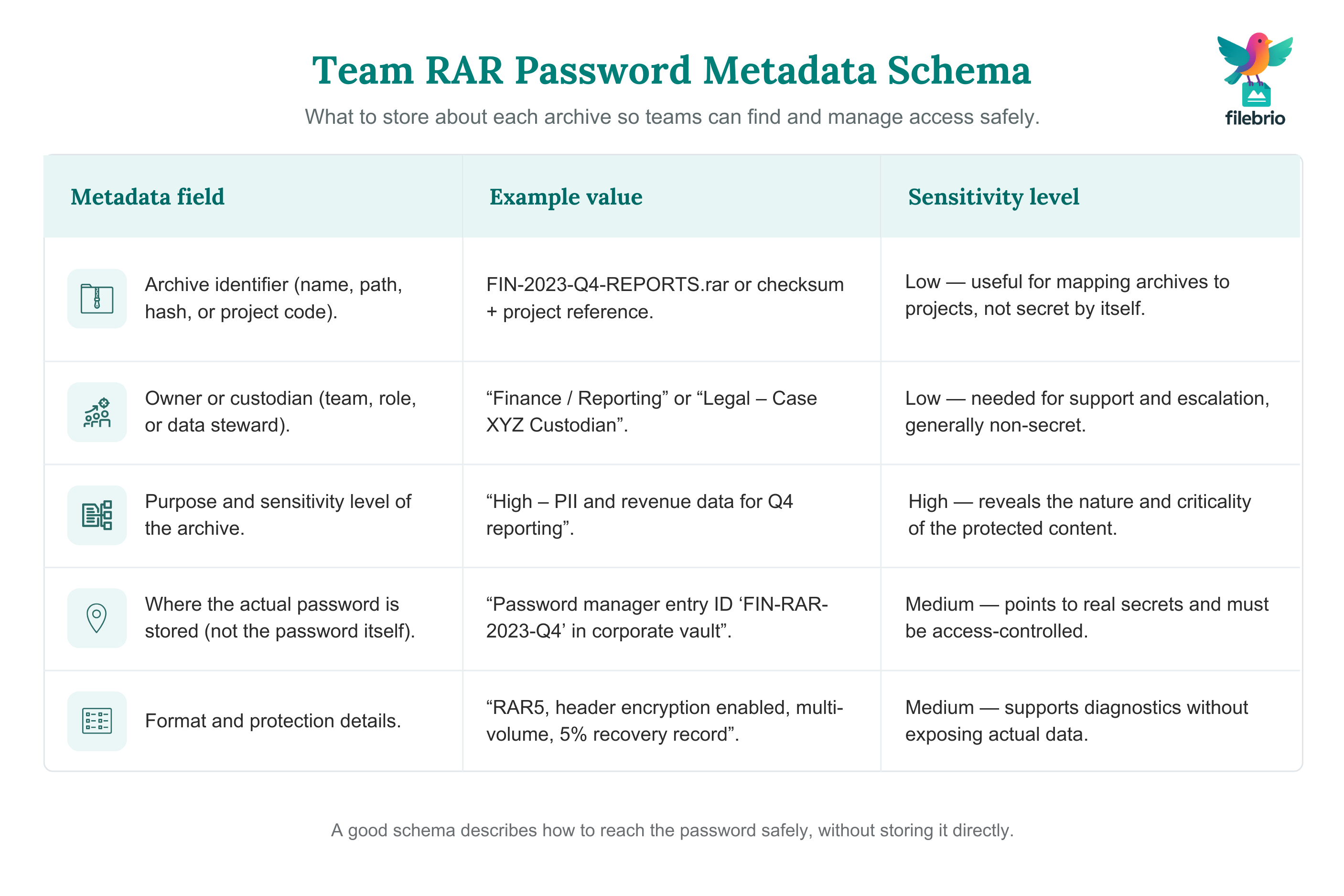
Before choosing tools, define the structure of the metadata you want to keep. The goal is to help future colleagues understand how an archive was protected without leaking the password itself.
A typical metadata model might include:
- Archive identifier (path, hash, project code).
- Owner or custodian (person or team).
- Purpose and sensitivity level.
- Approximate creation date and expected retention period.
- Password location (e.g., specific safe, password manager entry ID).
- Technical notes (RAR4/RAR5, header encryption, multi-volume, recovery records).
| Metadata Field | Example Value | Sensitivity |
|---|---|---|
| Archive ID | FIN-2023-Q4-REPORTS.rar | Low |
| Owner Team | Finance / Reporting | Low |
| Password Location | Password manager entry “FIN-RAR-2023-Q4” | Medium |
| Sensitivity Level | High (PII and revenue data) | High |
| Technical Notes | RAR5, header encryption enabled, recovery record 5% | Medium |
Team password policies and archive policies should be aligned with this structure. High-level guidelines on corporate rules for encrypted archives, such as those in how to design secure password rules for your business RAR files ↗️, can help you make sure the metadata supports your policy, instead of contradicting it.
🧩 All-In-One Workspace for Team RAR Metadata
When metadata is scattered between email threads, chat messages, and personal notes, teams struggle to answer basic questions like “Who is allowed to open this?” or “Where is the current password stored?”. Consolidation is key: you want one controlled workspace that ties RAR archives, their metadata, and your internal policies together.
A central, offline-friendly toolkit can help you:
- Map archives to owners and projects in a centralized view.
- Attach technical diagnostics (RAR version, header encryption, multi-volume layout).
- Record password locations and rotation events without writing the password in clear text.
- Export documentation for risk reviews, audits, and handovers.
| Need | What a Central Workspace Provides |
|---|---|
| Project onboarding | Single view of archives per project, with who owns them and where credentials are stored |
| Incident investigation | Structured technical notes about archive format, header encryption, and integrity |
| Compliance checks | Exportable reports showing who is allowed to access which protected archives |
An offline, diagnostics-first suite like FileBrio RAR Master features ↗️ can complement your documentation system by giving security or operations teams a consistent place to analyze archives locally before updating metadata or policies. This reduces ad hoc tool usage and keeps sensitive data within your own environment.
________________________
FileBrio RAR Master — part of the FileBrio Office Suite — is a privacy-first, offline Windows toolkit for diagnosing and safely regaining access to your own password-protected RAR / WinRAR archives.
- Local processing only — nothing leaves your PC.
- Smart diagnostics to separate password issues from corruption.
- Owner-verified recovery workflows designed strictly for legitimate use.
Reminder: FileBrio RAR Master may be used only with archives you own or are explicitly authorized to access. It performs all analysis and recovery operations locally on your device, without uploading data anywhere.
________________________
💻 Structuring Metadata Across Devices and Platforms
Teams rarely live on a single device. Laptops, desktops, virtual machines, and cloud drives all appear in the same workflow. Metadata needs to be usable wherever work happens, but not copied casually into every place where files exist.
A practical pattern is to separate working storage from metadata storage:
| Location | Recommended Use | Not Recommended For |
|---|---|---|
| Cloud file shares | Storing the RAR archives themselves | Storing passwords or detailed password hints |
| Local laptops/desktops | Temporary work with encrypted archives | Long-term storage of raw password notes |
| Team password manager | Primary store for credentials and high-level hints | Non-essential commentary or project notes |
| Secure documentation system | Metadata tables, rotation logs, ownership records | Direct passwords or low-level secrets |
Finding the right mix may also involve practicing with non-sensitive data. For example, guidance on how to test RAR protection with your dummy files ↗️ can help teams experiment with formats, metadata fields, and storage layouts before applying them to live archives.
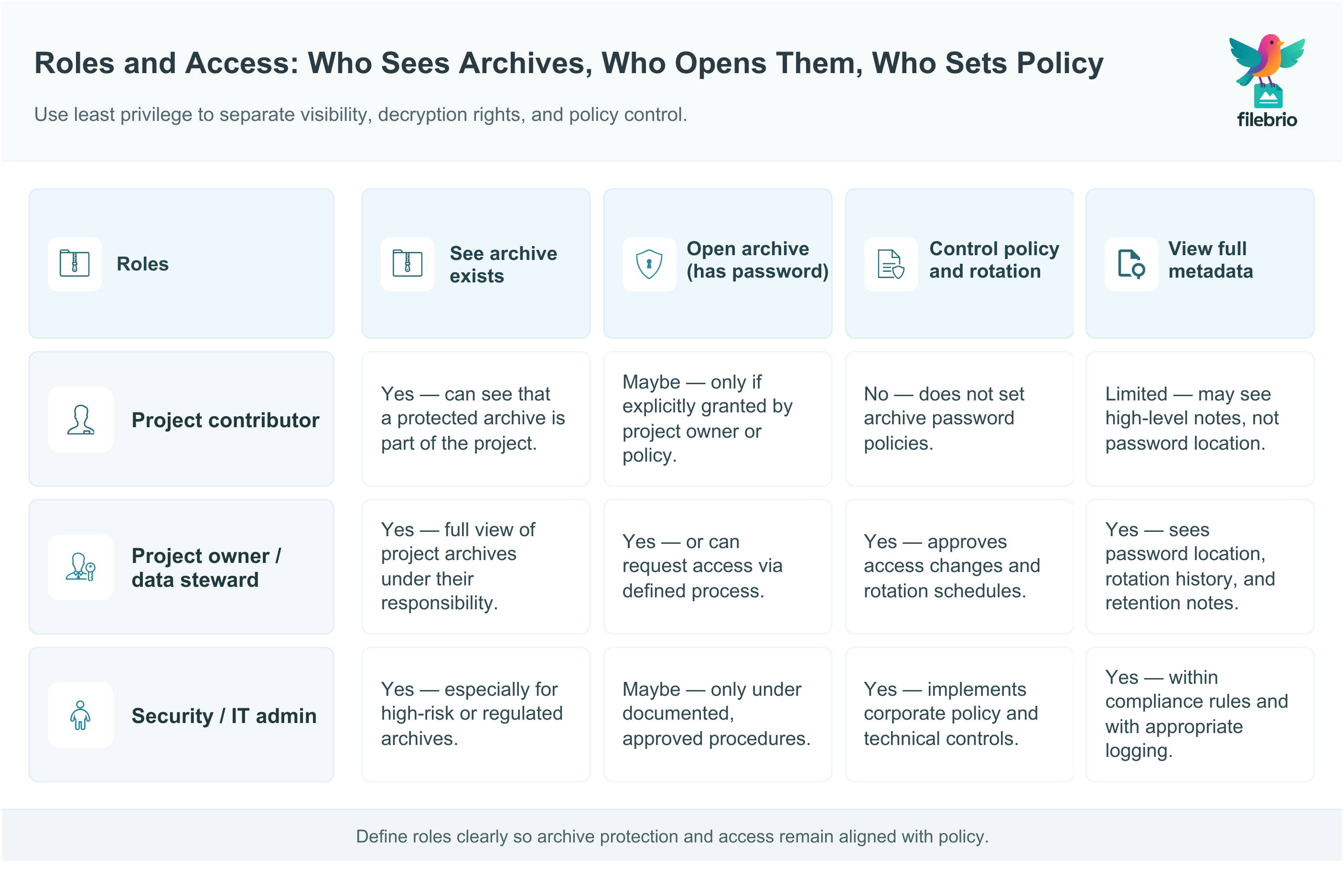
🛂 Access Control, Roles, and Least Privilege
In a team setting, “who can see what” is as important as “where is it stored.” Strong encryption on the archive can be undermined if metadata or passwords are freely accessible to people who do not need them.
At minimum, define three distinct dimensions of access:
- Who can see the archive file (for example, all members of a project space).
- Who can open the archive (those with password or decryption rights).
- Who controls policy and rotation (owners or information security roles).
| Role | Typical Rights | Metadata Access |
|---|---|---|
| Project contributor | Read/write project files | May see that an archive exists, not necessarily how to open it |
| Project owner | Approve access requests, manage archive lifecycle | Can see password location and rotation history |
| Security / IT admin | Enforce policy, support recovery in emergencies | Can review metadata across projects, subject to compliance rules |
Aligning these roles with centralized policies is essential. Articles such as how to protect sensitive files while allowing authorized recovery ↗️ provide conceptual frameworks for balancing strict protection with the need for legitimate access.
📜 Audit Trails, Ownership Proof, and Compliance
Many organizations must prove not only that they protected sensitive data, but also that access to encrypted archives was controlled and justified. RAR password metadata becomes part of that story: it can show who owned a given archive, who could open it, and when that changed.
Consider adding the following elements to your metadata program:
- Ownership records connecting each archive to a team, role, or data steward.
- Change logs for password location, rotation events, and revocation of access.
- Links to legal or compliance basis for retaining or deleting an archive.
For sensitive archives, look at frameworks for documenting custody and evidentiary chains, such as those discussed in how to document control of your sensitive encrypted files ↗️. High-level legal and ethical guidance like ethical ways to handle your encrypted RAR files ↗️ and legal factors when accessing your encrypted RAR files ↗️ can help teams align practices with regulations and internal policies.
🏢 Secure Offline Suite for Cross-Device Team Access
When a team needs to diagnose an archive or assess whether recovery is still realistic, it is tempting to send “just this one file” to an online service. That decision can conflict with everything your metadata and policies are trying to enforce, especially for regulated or confidential content.
A better strategy is to standardize on an offline, auditable toolkit that runs within your environment, where access is logged and controlled:
- Local-only processing ensures archives never leave your infrastructure.
- Consistent diagnostics give comparable results across teams and devices.
- Integration with documentation lets you tie technical findings back into metadata.
- Clear support and legal framework reduce ambiguity about acceptable use.
| Aspect | What a Secure Suite Provides |
|---|---|
| Diagnostics | Structured views of RAR format, header flags, and recovery records |
| Team support | Shared FAQ and usage patterns, similar to the guidance in RAR recovery questions ↗️ |
| Governance | Centralized support and legal resources such as legal and responsible use policy ↗️ |
A suite like FileBrio RAR Master within the FileBrio Office ecosystem can be aligned with your licensing and deployment rules, as described on software cost and editions ↗️. Teams can then distribute access in a controlled way and keep all work with encrypted archives local, avoiding unnecessary exposure to third-party cloud services.
When you are ready to equip your team with an offline, diagnostics-focused environment instead of relying on ad hoc tools, you can obtain the official installer from the FileBrio Office distribution page at FileBrio Office Suite download ↗️. This keeps your encrypted archives and their metadata under your own operational and legal umbrella.
________________________
FileBrio RAR Master — a secure, offline Windows toolkit for regaining access to your own password-protected RAR / WinRAR archives while keeping all data strictly on your device.
- Offline-only processing — never uploads your archives.
- Smart issue detection — password vs corruption.
- Fast recovery workflow optimized for legitimate ownership.
⬇️ Download FileBrio RAR Master
Reminder: FileBrio RAR Master is intended only for archives you own or are explicitly authorized to access. All operations run locally on your PC.
________________________
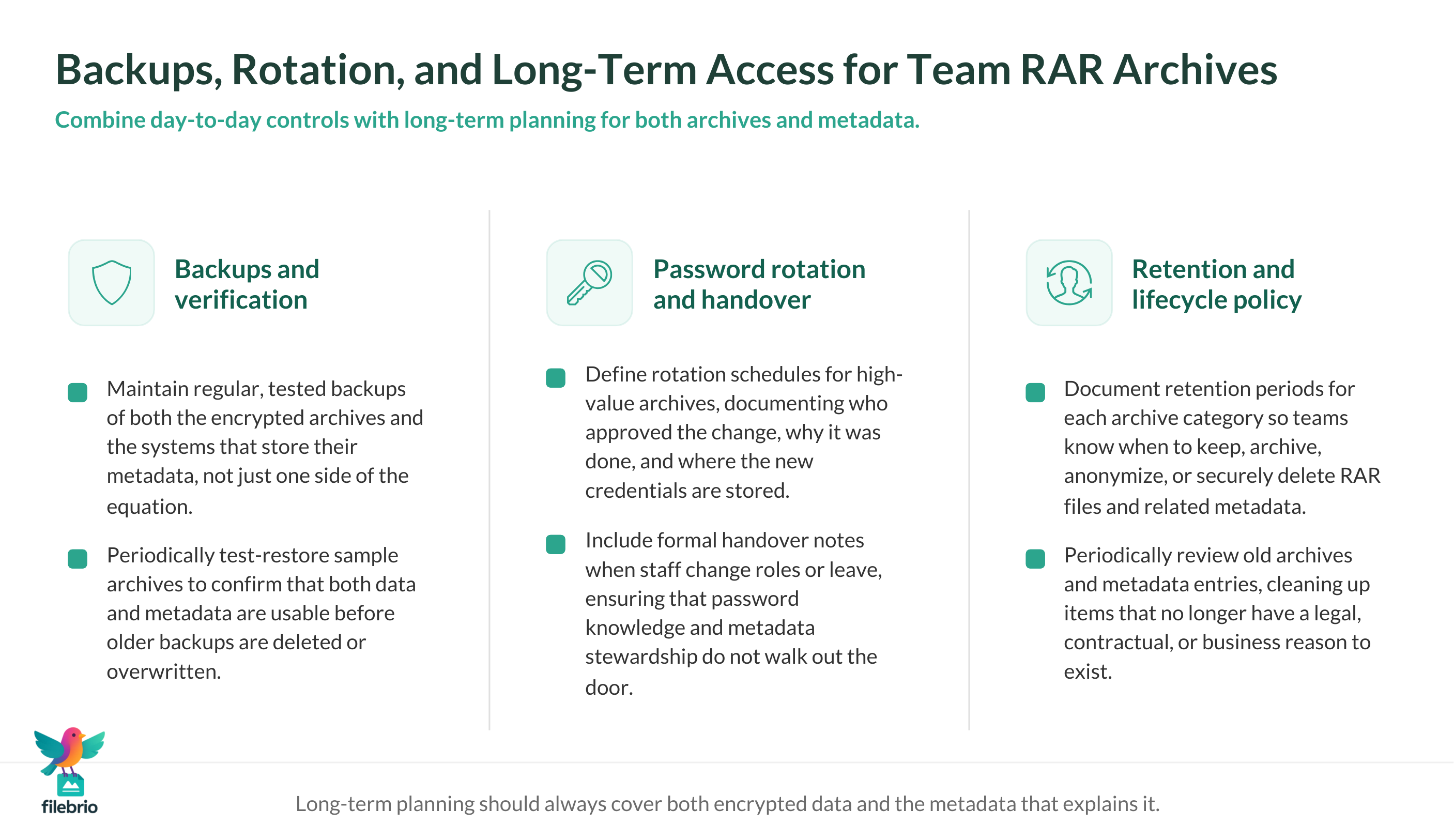
🔁 Backups, Rotation, and Long-Term Access Planning
Even with good metadata design, your plan can fail if backups are incomplete or password rotation is handled informally. Protecting yourself means pairing strong day-to-day controls with robust long-term strategy.
Key practices include:
- Regular, tested backups of both archives and metadata stores.
- Documented rotation schedules for high-value archives, with clear handover notes.
- Retention policies describing when archives should be archived, anonymized, or deleted.
Storage hygiene matters: guidance such as ways to prevent losing your RAR data on storage devices ↗️ can help you reduce physical and logical risks to both the archives and the systems that store their metadata. Combine those insights with enterprise-level planning from resources like how teams can preserve long-term access to encrypted RAR files ↗️ to design a strategy that survives hardware refreshes and organizational changes.
🚨 How to React When Something Goes Wrong
Despite best efforts, teams sometimes discover that a password note is missing, an owner has left the company, or a key archive is no longer accessible. How you respond in those first hours matters — both for data protection and for legal posture.
A structured response might include:
- Immediate containment: prevent uncontrolled copying or sharing of suspicious files or partial metadata.
- Metadata review: check your centralized records for ownership, location of legitimate credentials, and any previous incidents.
- Escalation to the right roles: involve security, legal, and data owners where appropriate.
- Use of vetted tools only: rely on your approved offline suite for diagnostics, not unverified downloads or online services.
Incident playbooks should cross-reference your internal legal and ethical guidance, similar to the high-level advice in guidelines for responsible access to your protected data ↗️. The goal is to ensure that any attempt to regain access remains within lawful boundaries and respects contractual and regulatory constraints.
📚 Legal Reminder
This article is provided for general informational and educational purposes only. Any examples, scenarios, or references to password recovery, archive security, or related tools (including FileBrio RAR Master or similar software) are intended solely to help you better understand how to protect and manage your own data.
You may only apply any techniques, workflows, or tools described here to files and archives that you fully own or are explicitly and verifiably authorized to access. Attempting to bypass, remove, or recover passwords for third-party data without clear permission may violate criminal law, civil law, or internal company policies in your jurisdiction.
Nothing in this article constitutes legal advice. Laws and regulations differ between countries and organizations, and you are solely responsible for ensuring that your actions comply with all applicable legislation, contracts, and internal policies. If you are unsure whether a particular action is lawful or permitted, consult a qualified legal professional before proceeding.
🔗 See Also: More on Metadata and Team Access
- Building Consistent Password Policies for RAR Archives in Team Environments ↗️
- How to Document and Prove Ownership of Encrypted Archives ↗️
- Best Practices for Sharing Encrypted RAR Files Within Teams ↗️
- How Password Encodings Affect Access Across Different Devices ↗️
- How to Update or Change RAR Passwords Safely When You Control the Archive ↗️
- Ensuring Long-Term Access to Older RAR Archives in Multi-User Settings ↗️
- How RAR5’s Security Model Improves Multi-Device and Multi-Role Access ↗️