
How to Store RAR Password Metadata Securely for Future You
You finally manage to protect a sensitive RAR archive with a strong password — and then time passes. Months or years later, you no longer remember exactly how that password was built. Was it your usual pattern? A special phrase? A one-off experiment? At that moment, the difference between complete lockout and smooth access often depends on how well you stored your password metadata, not the password itself.
This article explains what “password metadata” really means in the context of RAR and WinRAR archives, how to separate helpful notes from sensitive secrets, and how to store those notes safely so future you can still access your own data. We will focus on personal workflows for individuals, keeping everything strictly lawful, privacy-first, and offline-friendly.
🧭 Navigation
Important
The information provided in this article applies exclusively to RAR / WinRAR archives for which you have full, demonstrable ownership or properly documented authorization. If you are not the rightful owner of the data, do not directly control it, or cannot clearly prove permission to access it, you must stop immediately. Attempting to access, recover, or modify data without explicit authorization may violate criminal law, civil statutes, corporate compliance requirements, and privacy regulations in many jurisdictions. You alone are responsible for ensuring that your actions are lawful and properly permitted before proceeding.
⚡ TL;DR — Why Password Metadata Matters to Future You
Password metadata is carefully chosen information about your RAR password — patterns, hints, rules, and context — that helps you reconstruct or recall the password later, without writing the password itself in plain text. When done well, it:
- Makes it much easier for future you to remember how you built the password.
- Reduces the temptation to use weak, easily remembered phrases.
- Supports safe diagnostics if you are unsure which archive is which.
- Keeps sensitive data local and under your control.
Good metadata balances three goals: it should be understandable to you, useless to outsiders, and durable over many years. The rest of this article walks through what to store, how to structure it, and where to keep it so that you preserve long-term access to your own RAR archives.
🧠 What “Password Metadata” Actually Is (and Why It’s Not the Password Itself)
“Password metadata” often sounds abstract, but in practice it is just structured notes that describe how you designed a password, not the password itself. For RAR archives, this might include:
- The general pattern you used (for example, “phrase + year + symbol”).
- A reminder of which language or alphabet you chose.
- Whether the password follows your usual style or a one-off experiment.
- Which part of your life it relates to (project name, trip, event).
This kind of information is extremely powerful when combined with your own memory. It complements the guidance in resources about how to design strong memorable RAR passwords ↗️ by adding a second layer: not only do you create good passwords now, you also give future you a map to remember them.
| Concept | Example | Sensitive? |
|---|---|---|
| Password itself | MySummerTrip2024! |
Highly sensitive — do not store in plain text. |
| Metadata (pattern) | “Travel phrase + year + symbol” | Lower sensitivity, can be stored with care. |
| Metadata (context) | “Personal travel photos, early 2020s” | Contextual, but still should remain private. |
The goal is not to make recovery trivial for strangers, but to ensure that in five or ten years your own memory has enough structured support. Articles on how to avoid forgetting RAR passwords in the future ↗️ emphasize behavior and habits; password metadata is the written expression of those habits.
📂 Typical RAR Password Metadata You May Want to Keep
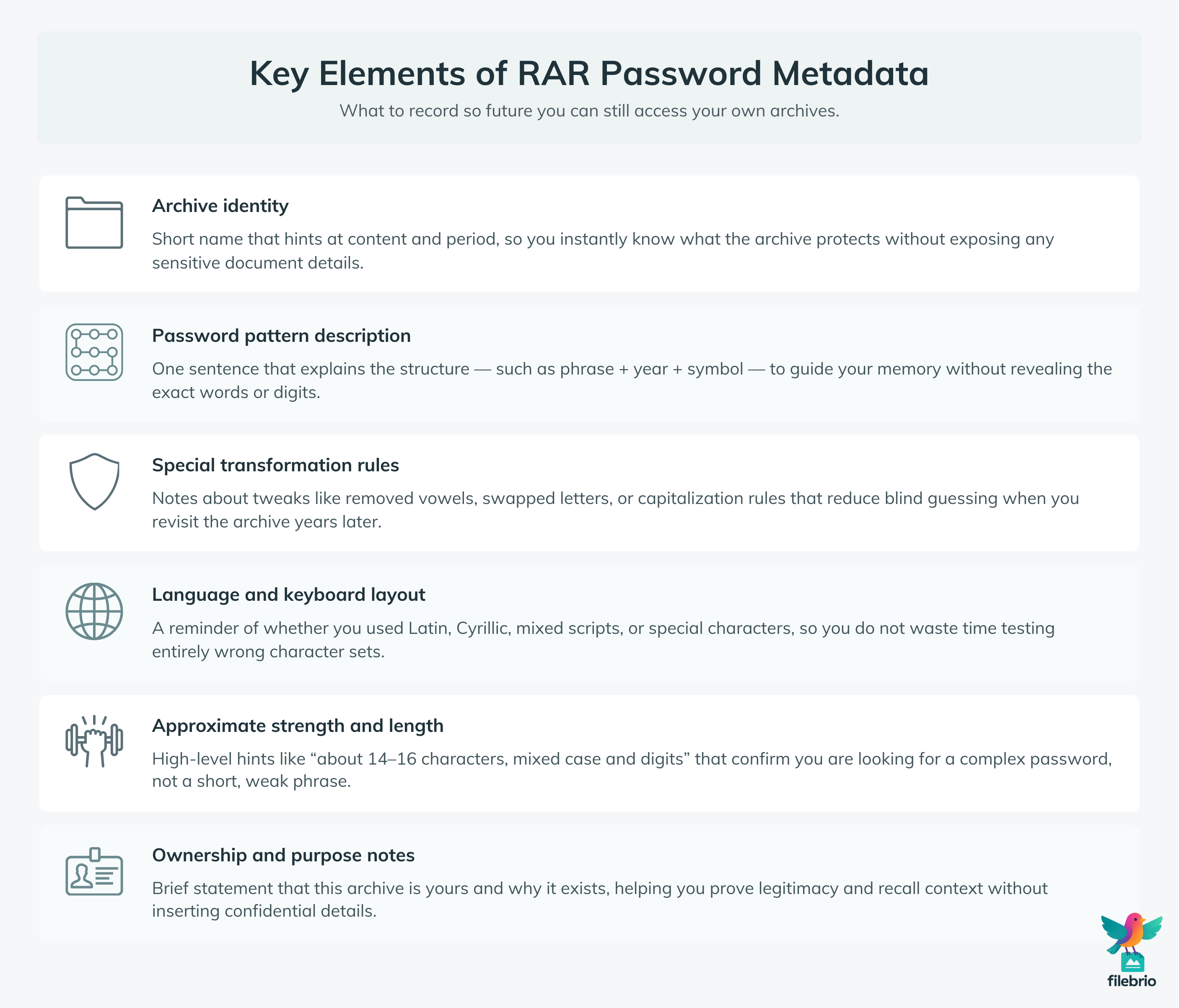
Before deciding where to store metadata, it helps to know what you want to retain. For individual users dealing with their own RAR archives, typical metadata fields include:
- Archive identity: what this archive represents (project name, time period, topic).
- Password pattern description: short statement of structure, not the password.
- Special rules: e.g., “replace spaces with underscores”, “year in two digits”.
- Language/keyboard: Latin vs Cyrillic, mixed scripts, special characters.
- Strength cues: approximate length, mix of character types, but no exact values.
- Ownership and purpose: a short note showing that the archive is yours and why it exists.
| Metadata Element | Example Entry | Why It Helps Future You |
|---|---|---|
| Archive identity | “Personal-tax-documents-2019-2021.rar” | Reminds you what kind of data is inside and why you protected it. |
| Password pattern | “Tax keyword + random word + 4 digits” | Guides your memory toward the right structure. |
| Special rules | “All vowels removed, first letter capitalized” | Reduces trial-and-error with small variations. |
| Encoding / keyboard | “Uses Cyrillic characters, no Latin” | Prevents you from searching in the wrong character set. |
Structured metadata like this works best when combined with secure storage habits and strong RAR protection. For a more general view on balancing strength and usability, see the broader recommendations in how to strengthen RAR archive security while preserving future access ↗️.
💼 All-In-One Solution to Keep Archives, Metadata, and Access in One Place
Even well-designed metadata can become hard to manage when your digital life expands. Common pain points include:
- Scattered notes across devices, notebooks, and apps.
- Multiple RAR archives with similar names and overlapping content.
- No single place where you can see which archives are critical and how they are protected.
- Uncertainty about which password patterns you used in which period of your life.
FileBrio Office Suite is built to reduce that fragmentation. RAR-focused modules like FileBrio RAR Master can help you:
- Group related RAR archives and review key technical parameters locally.
- Combine header-level diagnostics with your own metadata notes for each archive.
- Align your password metadata with realistic recovery expectations based on archive format and strength.
- Keep all operations strictly offline so private archives never leave your machine.
For a high-level view of what the toolkit offers — from diagnostics to lawful recovery workflows — you can review the FileBrio RAR Master features ↗️ summary, which shows how archive structure, security, and recoverability fit together.
________________________
FileBrio RAR Master — part of the FileBrio Office Suite — is a privacy-first, offline Windows toolkit for diagnosing and safely regaining access to your own password-protected RAR / WinRAR archives.
- Local processing only — nothing leaves your PC.
- Smart diagnostics to separate password issues from corruption.
- Owner-verified recovery workflows designed strictly for legitimate use.
Reminder: FileBrio RAR Master may be used only with archives you own or are explicitly authorized to access. It performs all analysis and recovery operations locally on your device, without uploading data anywhere.
________________________
📊 Comparing Common Ways to Store RAR Password Metadata
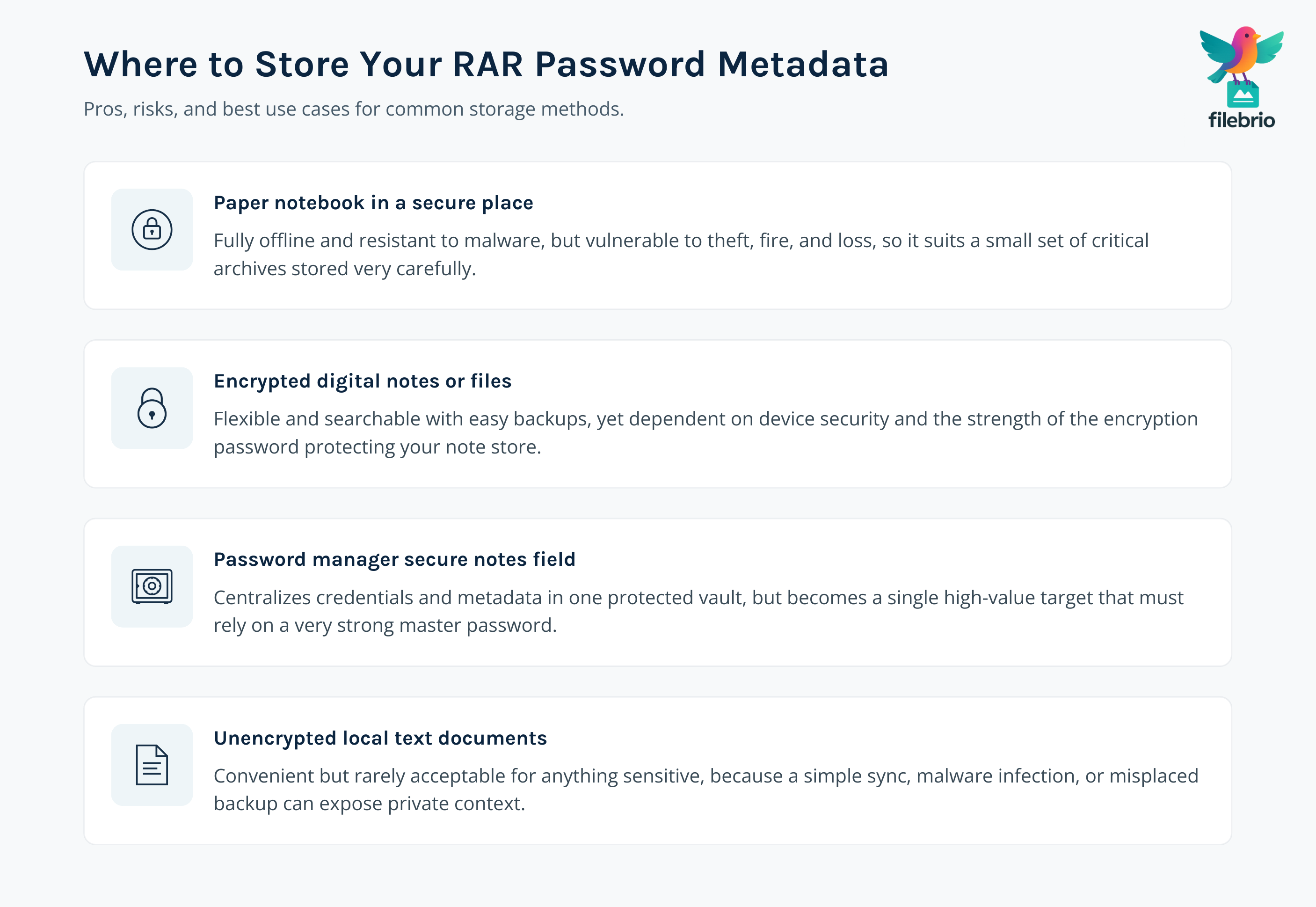
There is no single “right” place to store password metadata, but some options are safer and more durable than others. The crucial idea is to use methods that keep your notes private, under your control, and available years later.
| Method | Pros | Cons / Risks | Best For |
|---|---|---|---|
| Paper notebook in secure place | Offline, immune to malware, easy to understand. | Can be lost, stolen, or damaged; needs clear but private wording. | Small number of critical archives. |
| Encrypted digital note (e.g., encrypted file) | Searchable, easy to back up, can include structured tables. | Relies on device security and the encryption password for that note. | Users comfortable with basic encryption tools. |
| Password manager “notes” field | Secure storage, sync across devices, can link archive identity and metadata. | Still a central point of failure; must be protected with a very strong master password. | Users already managing credentials in a trusted manager. |
| Unencrypted text files | Simple and flexible. | Too easy to leak; usually not recommended for metadata containing personal context. | Only safe in very restricted environments. |
Whatever storage medium you choose, treat metadata with the same respect you give to the archives themselves. Good storage habits, combined with archive-level precautions such as those in how to prevent RAR data loss on USB drives, HDDs, and cloud storage ↗️, give you both durability and privacy.
🔐 Designing Secure, Memorable Metadata for Future You
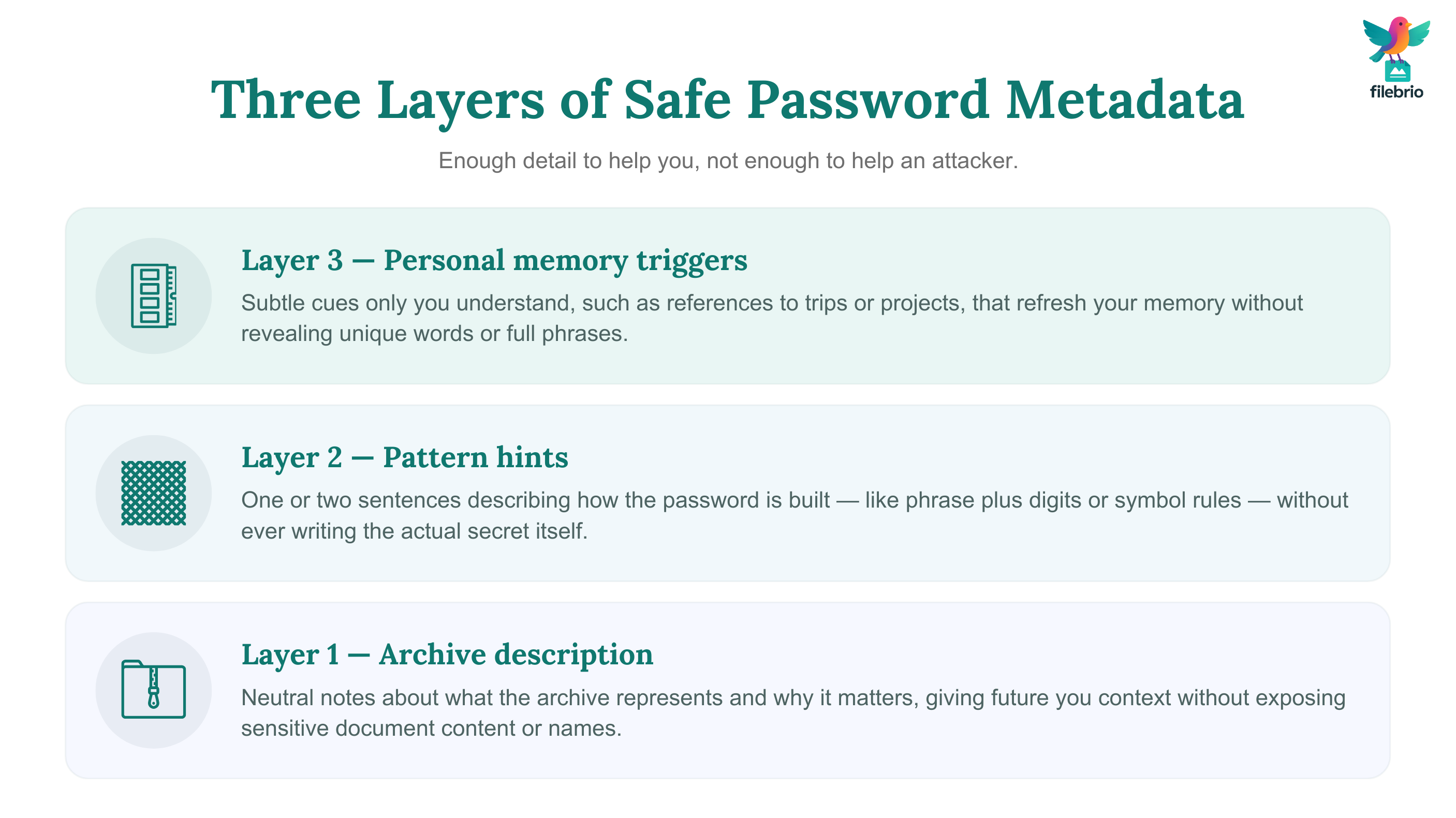
Metadata should be specific enough to jog your memory, but vague enough that someone else cannot reconstruct the password without already knowing your personal patterns. A useful approach is to think in layers:
- Layer 1 — Archive description: what this archive represents and why it matters.
- Layer 2 — Pattern hints: a sentence describing the structure, not the exact content.
- Layer 3 — Memory triggers: internal references that only you or trusted future you would understand.
| Layer | Bad Example | Better Example |
|---|---|---|
| Pattern hint | “Password is: MySummerTrip2024!” | “Travel phrase + year + symbol (same style as other travel archives)” |
| Memory trigger | “Uses the word Venice in English.” | “City from that spring holiday, written in the same language as the photo folder names.” |
The techniques described in how to create strong yet memorable RAR passwords ↗️ pair well with this layered metadata approach: first design solid passwords, then decide what high-level information about them is safe to record.
It is also wise to note when you intentionally changed your style (for example, when you increased password length or switched to a new pattern). In a decade, knowing “this archive uses my old style; this one uses my new 16+ character style” can be the difference between fast recall and endless guessing.
📝 Practical Workflows for Personal Password Notes (Without Over-Sharing)
Translating these ideas into everyday life requires simple, repeatable steps. Here are some patterns individuals often find practical:
- Archive log: maintain a single, encrypted note or notebook where each entry corresponds to a critical RAR archive.
- Consistent fields: for each archive, write archive name, purpose, pattern hint, special rules, and the approximate period when you created it.
- Cross-reference: when multiple archives reuse a similar pattern, add a short reference like “same style as ‘photos-2018’ archive.”
- Review moments: once a year, skim your metadata to ensure it still makes sense and reflects your current habits.
These workflows are about protecting your own data, not accessing anything that belongs to someone else. Following the principles from how to ensure you’re recovering only RAR files you own ↗️ keeps your practice aligned with lawful use and personal responsibility.
When the stakes are particularly high — for example, archives containing important documents — it can be worth adding a short note describing why you encrypted the archive and what proof of ownership you have. Guidance from how to document ownership of sensitive encrypted archives ↗️ can help you formalize this, especially if you might need to demonstrate legitimacy later.
🛡️ Secure Offline Environment for Your Notes and Recovery Attempts
Storing metadata is only half of the story; you also need a trustworthy environment for diagnostics and lawful recovery attempts. Common concerns include:
- Not wanting to upload sensitive archives to unknown online services.
- Needing tools that can interpret RAR4 vs RAR5 structures and confirm whether an archive is still technically recoverable.
- Wanting consistent behavior across metadata notes, recovery attempts, and integrity checks.
FileBrio RAR Master, as part of the FileBrio Office Suite, is designed to support these needs in a privacy-first way:
- All operations happen locally; your RAR archives and metadata stay on your own systems.
- Diagnostics modules help you understand if an archive is intact, damaged, or mathematically unrealistic to recover.
- Recovery-related components are aligned with safe, documented use for archives you legitimately own.
For more detailed insight into how the suite handles lawful password recovery tasks, you can explore the RAR password recovery tool ↗️ overview. If you want to understand how long certain patterns might take to process at a high level, the password strength estimator and time-to-crack calculator ↗️ provides conceptual, non-instructional timing estimates.
When you are ready to integrate FileBrio into your local workflow, you can obtain it from the official FileBrio tools download page ↗️, ensuring you install from a trusted source.
________________________
FileBrio RAR Master — a secure, offline Windows toolkit for regaining access to your own password-protected RAR / WinRAR archives while keeping all data strictly on your device.
- Offline-only processing — never uploads your archives.
- Smart issue detection — password vs corruption.
- Fast recovery workflow optimized for legitimate ownership.
⬇️ Download FileBrio RAR Master
Reminder: FileBrio RAR Master is intended only for archives you own or are explicitly authorized to access. All operations run locally on your PC.
________________________
📁 Backups, Redundancy, and Avoiding Single Points of Failure
Metadata that exists in only one place is fragile. If that place is lost, damaged, or compromised, future you may find it impossible to reconstruct the password pattern, even if the archive is otherwise healthy.
To avoid this, treat your metadata as part of your backup plan:
- Keep at least two copies of your encrypted notes or paper records, stored in different places.
- Periodically verify that you can still open and read the metadata (no corrupted files or unreadable handwriting).
- Ensure that your backup devices are themselves stored safely and do not travel unnecessarily.
These ideas mirror the general storage and protection advice found in how to prevent RAR data loss on USB drives, HDDs, and cloud storage ↗️. The same mindset that preserves your data also preserves your ability to interpret your own passwords.
If you upgrade your RAR security over time — for example, moving from older RAR4 archives to newer RAR5 ones — align your metadata strategy with those changes, as discussed in how to strengthen RAR archive security while preserving future access ↗️. Make a note when an archive is migrated, which format it now uses, and whether the password pattern changed.
👀 Privacy Boundaries: What Not to Put in Metadata
While metadata is safer than writing passwords in plain text, it can still leak sensitive information if you are careless. A few boundaries help maintain a healthy balance between usefulness and discretion:
- No full passwords: avoid ever writing the complete password, even “just this once.”
- Limit highly personal details: avoid explicit references to medical information, financial account numbers, or other sensitive topics.
- Be careful with unique phrases: if a phrase is so unique that it practically is the password, consider using more abstract wording.
- Protect third-party data: if archives contain data about other people, keep notes respectful and minimal.
Metadata should help you recall the password, not give strangers critical clues. If you later choose to work with external specialists, having well-designed metadata can also make it easier to demonstrate that you are the legitimate owner and that your actions follow guidance like how to ensure you’re recovering only RAR files you own ↗️.
📚 Planning for Long-Term Access and Life Changes
Finally, think about how your RAR archives and their metadata fit into your long-term digital life. Over years, people change devices, move countries, change names, and reorganize their storage. Metadata that made perfect sense in your twenties may be confusing in your forties unless you plan ahead.
For individuals, a simple long-term plan might include:
- Defining which archives are “long-term critical” (for example, legal, financial, or family history).
- Reviewing those archives and their metadata every few years to ensure they still make sense.
- Documenting, in a sealed or legally appropriate way, how trusted people could eventually access important archives if needed.
The same questions enterprises ask — such as those discussed in how to maintain long-term access to encrypted RAR archives (teams & enterprises) ↗️ — apply at a smaller scale to individuals: who should be able to open which archive, under what circumstances, and with what evidence of legitimacy?
If you do decide to invest more heavily in tools for your own RAR workflows, it can help to review FileBrio pricing plans ↗️ so that your long-term strategy includes both software and well-managed metadata, rather than relying purely on memory.
⚖️ Legal and Ethical Reminder
This article is provided for general informational and educational purposes only. Any examples, scenarios, or references to password recovery, archive security, or related tools (including FileBrio RAR Master or similar software) are intended solely to help you better understand how to protect and manage your own data.
You may only apply any techniques, workflows, or tools described here to files and archives that you fully own or are explicitly and verifiably authorized to access. Attempting to bypass, remove, or recover passwords for third-party data without clear permission may violate criminal law, civil law, or internal company policies in your jurisdiction.
Nothing in this article constitutes legal advice. Laws and regulations differ between countries and organizations, and you are solely responsible for ensuring that your actions comply with all applicable legislation, contracts, and internal policies. If you are unsure whether a particular action is lawful or permitted, consult a qualified legal professional before proceeding.
🧩 See Also: Password Memory, Metadata, and Future Access
- How to Create Strong Yet Memorable RAR Passwords That You Won’t Lose in the Future ↗️
- How to Store RAR Password Metadata Securely for Future You ↗️
- How to Safely Store RAR Password Metadata for Future Access ↗️
- How to Avoid Forgetting RAR Passwords in the Future: Practical Retention Strategies ↗️
- How to Strengthen RAR Archive Security While Preserving Future Access ↗️