
How to Share Encrypted RAR Files Safely with Colleagues or Clients
You might have a payroll export, legal documents, or a client project locked inside an encrypted RAR archive — and now you need to share it with someone else without accidentally exposing sensitive data. At that moment, many users improvise: send the archive over email, share it via a random cloud link, or reveal the password in chat. This article is about turning that fragile, ad-hoc process into a deliberate, policy-aligned workflow that protects everyone involved.
We’ll look at how to confirm you’re only sharing archives you legitimately own, how to decide who should receive them, and how to exchange passwords in a way that doesn’t undermine the encryption you rely on. You’ll also see how a standardized offline toolset and clear security policies can make encrypted RAR sharing feel routine instead of risky — both for one-to-one collaboration and for larger teams working with sensitive archives every day.
🧭 Navigation
Important
The information provided in this article applies exclusively to RAR / WinRAR archives for which you have full, demonstrable ownership or properly documented authorization. If you are not the rightful owner of the data, do not directly control it, or cannot clearly prove permission to access it, you must stop immediately. Attempting to access, recover, or modify data without explicit authorization may violate criminal law, civil statutes, corporate compliance requirements, and privacy regulations in many jurisdictions. You alone are responsible for ensuring that your actions are lawful and properly permitted before proceeding.
📌 TL;DR — Safe Sharing of Encrypted RAR Files
When you share an encrypted RAR or WinRAR archive with colleagues or clients, you’re not just sending “a file” — you are delegating access to whatever sensitive data it contains. To do this safely, you need to combine ownership verification, proper authorization, secure channels, and careful password handling. The goal is to ensure that only the intended recipient can open the archive, that access is justifiable, and that you have a record of what was shared and why.
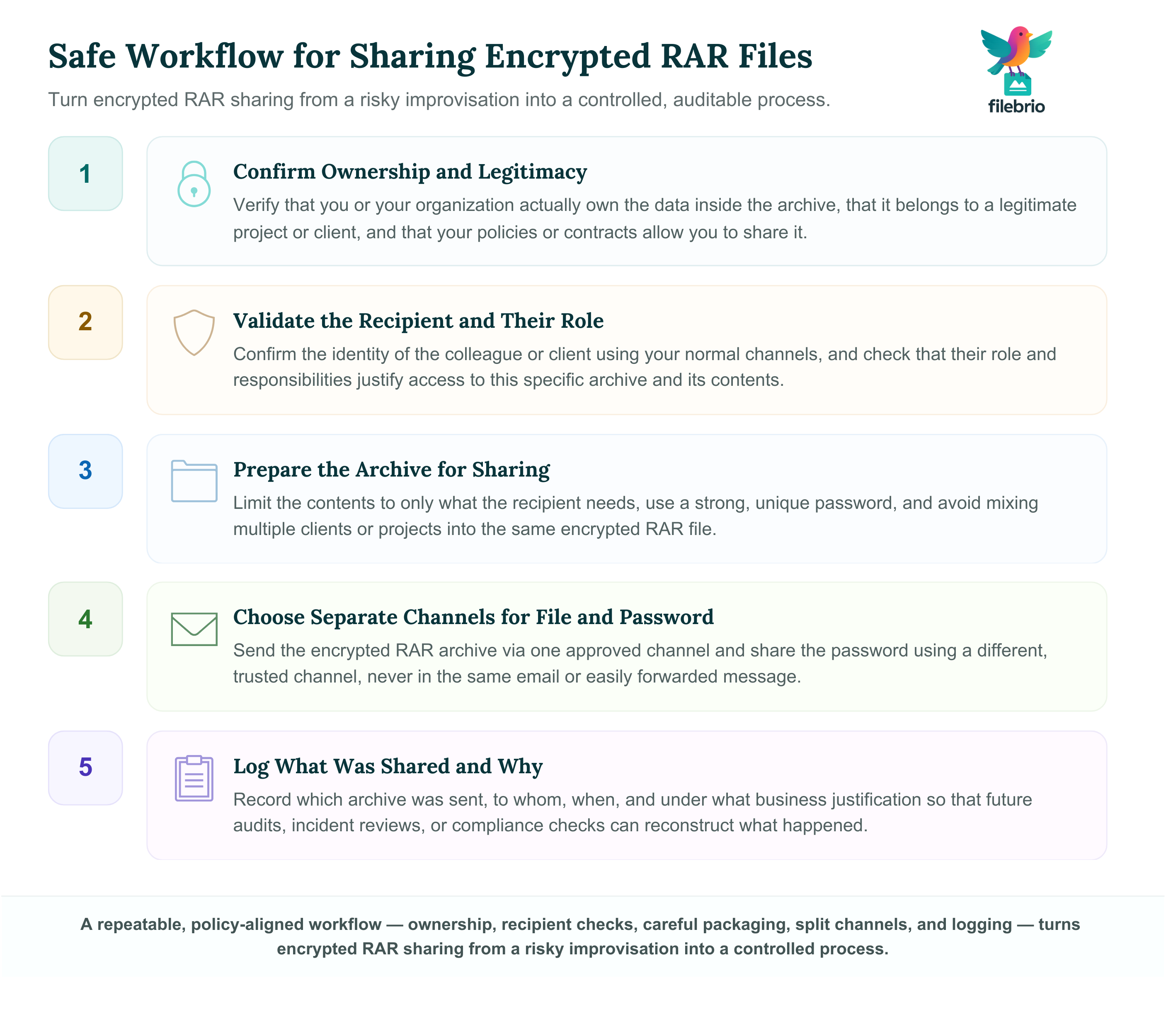
At a high level, a safe workflow looks like this:
- Confirm ownership and legitimacy: you or your organization actually own the data inside the archive and have the right to share it.
- Validate the recipient: ensure the colleague or client is allowed to see this specific content and that their identity is verified through your usual channels.
- Prepare the archive: use a strong, unique password and only include the data that needs to be shared, not unrelated material.
- Choose secure transport and key exchange: send the encrypted RAR via one channel, and share the password via a separate, trusted channel.
- Maintain records: log what you shared, with whom, and under which business justification, so you can audit later if needed.
You should avoid shortcuts such as weak passwords, sending the archive and the password in the same unprotected email, or uploading confidential RAR files to unvetted third-party websites. Instead, follow clearly documented policies, rely on offline, privacy-focused tools, and favor workflows that preserve future access while keeping unauthorized parties out.
🧠 Why Secure Sharing of Encrypted RAR Files Matters
Encryption is often added at the very last step: someone selects “Set password…” in WinRAR or another tool, chooses a phrase, and assumes the risk is now gone. But once you start sharing the archive, the security problem shifts. The main question becomes: who else will see the archive and the password, and under what conditions?
From a policy standpoint, secure sharing of encrypted archives is a core part of ethical ways to handle your encrypted RAR files ↗️. If your organization allows arbitrary sharing of password-protected archives without clear rules, it can:
- Expose confidential information to the wrong colleague or an incorrect client contact.
- Leak RAR passwords that later get reused on other systems.
- Destroy the audit trail needed for investigations or compliance reviews.
By designing a repeatable process for sharing encrypted RAR files, you reduce these risks and give employees a safe default: they know which tool to use, how to verify recipients, where to send archives, and how to exchange passwords without undermining the protection.
📂 Common Sharing Scenarios and Typical Risks
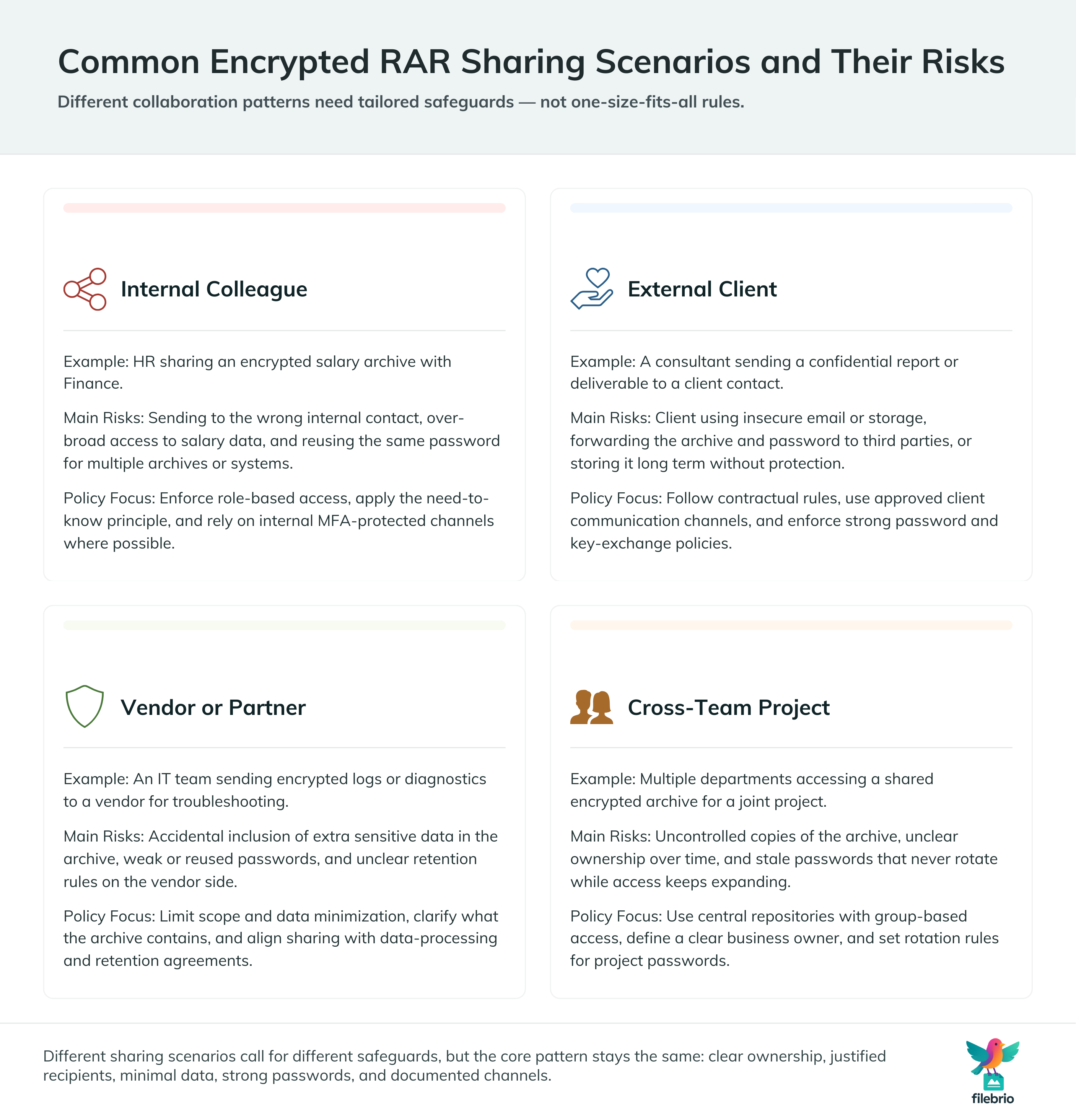
Different collaboration scenarios lead to different risk profiles. Understanding these helps you choose proportional safeguards instead of over- or under-reacting.
| Scenario | Example | Main Risks | Policy Considerations |
|---|---|---|---|
| Internal colleague | HR sharing an encrypted salary archive with Finance | Misaddressed email, over-broad access, password reuse | Recipient role, need-to-know principle, internal MFA |
| External client | Consultant sending a confidential report | Insecure client email, forwarding to third parties | Contractual rules, approved channels, password policy |
| Vendor / partner | IT team sharing logs or diagnostics | Accidental inclusion of extra data, weak passwords | Scope limitation, data minimization, retention limits |
| Cross-team project | Multiple departments accessing shared archive | Uncontrolled copies, unclear ownership, stale passwords | Central repository, group-based access, rotation rules |
Many of these risks overlap with broader guidance on how to design a secure workflow for your encrypted files ↗️. Your RAR-sharing policy should be one concrete module within that larger framework: a focused chapter that describes how to handle archives in motion, rather than just at rest.
👥 Ownership, Authorization, and Who Should Receive the Archive
Before you share any encrypted archive, you should first ask a foundational question: Do we own this data, and do we have the right to share it? That includes verifying that the archive contains only company-controlled material or content covered by your agreements with the client.
Good practice aligns with how to verify ownership before accessing your RAR file ↗️ and how to document control of your sensitive encrypted files ↗️. In a sharing context, that translates to:
- Knowing which team or person is the data owner for the archive.
- Checking whether the intended recipient has a legitimate role-based need for access.
- Recording the business justification: why this specific person or group should receive the archive.
Access for colleagues should normally follow internal authorization procedures (ticketing systems, approvals, or written requests). For clients and external partners, your contracts and data processing agreements should describe under which circumstances encrypted archives can be shared and which side is responsible for key management.
🧺 Preparing the RAR Archive Before You Share
Once ownership and authorization are clear, the next step is to prepare the archive itself. Safe sharing begins with how the RAR file is built, not just how it is sent later.
Key preparation points include:
- Limit the contents. Only include files that are actually needed by the recipient. Data minimization reduces impact if something goes wrong.
- Use a strong, unique password. Apply guidance similar to how to reinforce protection of your encrypted RAR files ↗️, avoiding common phrases or reused secrets.
- Consider separate archives per audience. Instead of one giant RAR for multiple clients, create separate archives with tailored contents.
- Protect future access. For team scenarios, follow how teams can organize shared RAR password metadata ↗️ so that access is preserved even when staff change roles.
On the individual level, it is equally important to avoid storing passwords in personal notes or emails. Safer patterns follow ideas from how to organize metadata for your RAR passwords safely ↗️ so you are not tempted to turn “temporary” storage into a long-term vulnerability.
🧰 All-In-One Solution For Policy-Aligned RAR Workflows
Policies are only as strong as the tools people actually use. If employees or contractors cannot easily work with encrypted archives using approved software, they will fall back to whatever is convenient — including untrusted online utilities they find when searching for quick fixes.
An all-in-one, offline toolkit like FileBrio RAR Master within the broader Office Suite can help you bring practice in line with policy. Instead of improvising per case, staff can rely on a standard environment that supports secure creation, inspection, and recovery of legitimately owned archives.
| Need | Risk Without Standard Tools | Benefit of a Managed Toolkit |
|---|---|---|
| Create encrypted RARs for clients | Users choose random tools, inconsistent options | Consistent encryption settings and safer defaults |
| Diagnose access issues | Uploads to online “helpers,” data exposure | Offline diagnostics aligned with company rules |
| Recover access to owned archives | Users search for risky utilities on the internet | Centralized, audited toolkit for legitimate recovery |
In your internal documentation, you might reference an all-in-one RAR recovery toolkit ↗️ as the approved way to work with encrypted archives, complemented by guidance on how to protect sensitive files while allowing authorized recovery ↗️. For users who want to understand capabilities and constraints in more detail, you can also direct them to a RAR user guide and FAQ ↗️ that clarifies what is and isn’t possible under your responsible use policy.
When the time comes to deploy this standard toolkit broadly, your IT team can obtain it centrally via the official installer instead of letting everyone choose their own tools.
________________________
FileBrio RAR Master — part of the FileBrio Office Suite — is a privacy-first, offline Windows toolkit for diagnosing and safely regaining access to your own password-protected RAR / WinRAR archives.
- Local processing only — nothing leaves your PC.
- Smart diagnostics to separate password issues from corruption.
- Owner-verified recovery workflows designed strictly for legitimate use.
Reminder: FileBrio RAR Master may be used only with archives you own or are explicitly authorized to access. It performs all analysis and recovery operations locally on your device, without uploading data anywhere.
________________________
📡 Channels, Key Exchange, and Human Factors
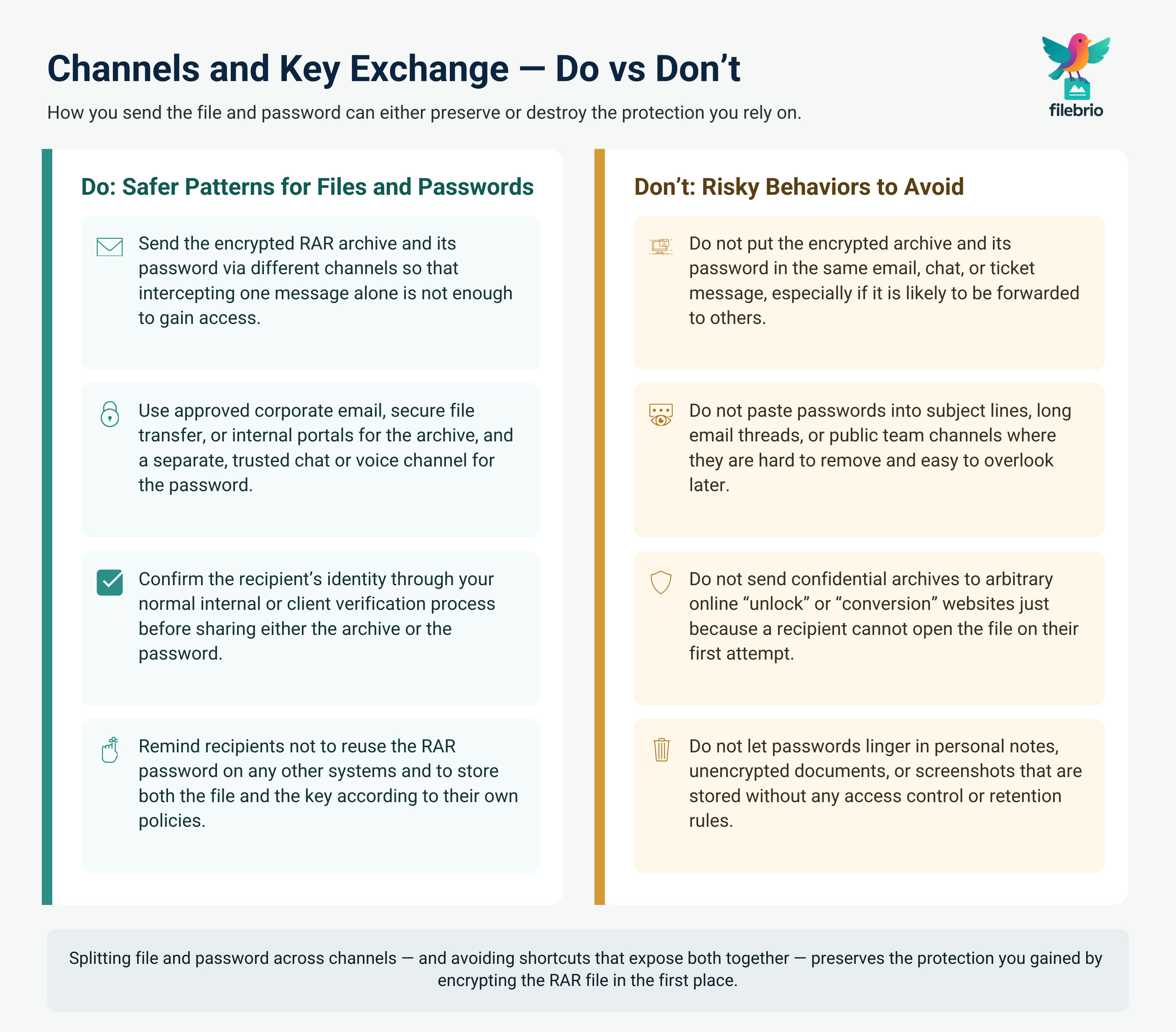
Even a perfectly prepared archive can be compromised by poor handling of its password. A safe sharing process deliberately separates the encrypted payload (the RAR file) from the keying material (the password or passphrase).
Practical guidelines include:
- Sending the encrypted RAR file via one channel (for example, corporate email or an approved secure file transfer system).
- Sharing the password via a different, trusted channel (for example, a corporate chat message to a known contact, or a voice call confirming the phrase).
- Avoiding the inclusion of passwords in the same email that carries the archive, or in subject lines and easily forwarded messages.
These rules mirror the broader design patterns described in how to design a secure workflow for your encrypted files ↗️. Human factors are crucial: recipients must understand that archives should be stored and handled according to policy, and that passwords should never be reused on other systems or shared indiscriminately within their own organization.
For some projects, you may also define rotation rules: passwords expire after a given period or after the project ends, which is consistent with the long-term security principles in how teams can preserve long-term access to encrypted RAR files ↗️. This reduces the damage if older copies of an archive resurface unexpectedly.
🛡️ Secure Offline Solution For Sensitive RAR Exchanges
Public search results are filled with online services that invite users to upload encrypted RAR files for “instant access” or “password help.” From a privacy and compliance perspective, sending confidential material to these sites is usually unacceptable — especially when you are sharing archives that contain client data, HR records, or regulated information.
A safer strategy is to base your workflows around offline, locally controlled tools. This aligns with the principles in why offline tools keep your encrypted RAR data private ↗️, where the encrypted archive never leaves systems under your management. Users can work with the archive according to your internal guidelines, instead of being tempted to experiment with unknown third parties.
To keep these offline tools aligned with your policies, you should adopt software that explicitly supports legal and responsible use policy ↗️ requirements. At the same time, you can let staff know where to turn when they encounter sharing or access issues by referencing an app capabilities overview ↗️ in your internal knowledge base.
When you are ready to standardize and distribute this toolkit across your organization, you can obtain it from the official FileBrio Office Suite distribution point. Instead of downloading ad-hoc utilities from random sources, teams will install the same vetted package every time, using the centralized installer available on the official suite download page.
________________________
FileBrio RAR Master — a secure, offline Windows toolkit for regaining access to your own password-protected RAR / WinRAR archives while keeping all data strictly on your device.
- Offline-only processing — never uploads your archives.
- Smart issue detection — password vs corruption.
- Fast recovery workflow optimized for legitimate ownership.
⬇️ Download FileBrio RAR Master
Reminder: FileBrio RAR Master is intended only for archives you own or are explicitly authorized to access. All operations run locally on your PC.
________________________
🏢 Organizational Processes, Logging, and Long-Term Access
Secure sharing is not just about avoiding leaks today; it is also about knowing what happened yesterday. When questions arise months later — “Who sent this archive?” “Who had access?” “Why was this client file shared?” — you need processes and records that can answer them.
This is where your RAR-sharing workflow connects to broader best practices on ways to prevent losing your RAR data on storage devices ↗️ and how to reinforce protection of your encrypted RAR files ↗️. Your policies should define:
- Where shared archives may be stored (central repositories, approved project folders, or specific platforms).
- How long these archives may be kept, and when they must be deleted or re-encrypted.
- What logs are required to track which user sent or received a given archive.
At the same time, you must prevent a common failure mode: losing track of the password while still needing the data. Guidance like how teams can preserve long-term access to encrypted RAR files ↗️ and how teams can organize shared RAR password metadata ↗️ helps design systems where archives remain accessible under controlled conditions but never become “open” just because people are afraid of losing the key.
⚙️ Governance, Training, and Clear Responsibilities
No matter how detailed your written procedures are, they will fail if people do not understand them or if responsibilities are unclear. Effective governance combines policy, tools, and training in a way that makes safe behavior the easiest option.
As part of governance, you should:
- Ensure your policies are consistent with how to protect sensitive files while allowing authorized recovery ↗️, especially when clients request archives via email or transfer services.
- Describe who approves new sharing workflows, and which teams own the encrypted archives they produce.
- Direct staff to a standardized offline toolkit distribution channel, such as the official FileBrio tools download page ↗️, so they do not rely on unvetted applications.
Training modules should cover both the technical aspects of creating and sharing RAR archives and the broader ethical and legal boundaries outlined in ethical ways to handle your encrypted RAR files ↗️. Users need to understand that encryption is not just a checkbox but part of a responsible process that includes authorization, secure channels, and auditable decisions.
⚖️ Legal Reminder
This article is provided for general informational and educational purposes only. Any examples, scenarios, or references to password recovery, archive security, or related tools (including FileBrio RAR Master or similar software) are intended solely to help you better understand how to protect and manage your own data.
You may only apply any techniques, workflows, or tools described here to files and archives that you fully own or are explicitly and verifiably authorized to access. Attempting to bypass, remove, or recover passwords for third-party data without clear permission may violate criminal law, civil law, or internal company policies in your jurisdiction.
Nothing in this article constitutes legal advice. Laws and regulations differ between countries and organizations, and you are solely responsible for ensuring that your actions comply with all applicable legislation, contracts, and internal policies. If you are unsure whether a particular action is lawful or permitted, consult a qualified legal professional before proceeding.
📚 See Also
- Legal Considerations When Working With Your Own Encrypted Archives ↗️
- Restoring Access To RAR/WinRAR Archives: Safe And Legal Methods For Handling Your Own Files ↗️
- How To Diagnose A Locked RAR Archive Without Risking Data Loss ↗️
- Online RAR/WinRAR Unlockers: Hidden Risks And Why Local Tools Offer Better Security ↗️
- Open RAR Files Online (With Or Without Password): Risks, Privacy Concerns, And Safer Alternatives ↗️
- Free RAR/WinRAR Password Recovery Tools: Safe, Offline Options For Accessing Your Own Files ↗️
- Why Online RAR Password Tools Fail — And What Legitimate Users Can Do Instead ↗️