How to Build a Safe Workflow for Working With Encrypted Archives
You finally need something inside an encrypted archive — a legal document, a client backup, a project handover from years ago — but you’re suddenly unsure what to do next. Is it safe to open this file on your current machine? Are you even allowed to touch it? Should you upload it to an “online unlocker”, or will that leak sensitive data forever?
Most problems with encrypted archives don’t come from encryption itself. They come from rushed decisions and improvised workflows: uploading confidential archives to random websites, copying files around without documentation, or letting multiple people “try things” without a clear process. A safe workflow solves this by giving you a repeatable, privacy-first way to handle encrypted archives from the moment you receive them until the moment you archive or destroy them.
This article walks you through how to design such a workflow: how to verify you are working only with archives you own, how to use offline tools, how to handle passwords and metadata responsibly, and how to plan for long-term access and compliance — whether you’re an individual user or an enterprise team.
🧭 Navigation
Important
The information provided in this article applies exclusively to RAR / WinRAR archives for which you have full, demonstrable ownership or properly documented authorization. If you are not the rightful owner of the data, do not directly control it, or cannot clearly prove permission to access it, you must stop immediately. Attempting to access, recover, or modify data without explicit authorization may violate criminal law, civil statutes, corporate compliance requirements, and privacy regulations in many jurisdictions. You alone are responsible for ensuring that your actions are lawful and properly permitted before proceeding.
📌 TL;DR: What a Safe Encrypted-Archive Workflow Looks Like
A safe workflow for encrypted archives is a repeatable sequence of checks and actions that protects privacy, respects legal boundaries, and minimizes the risk of data loss or exposure. Instead of reacting ad hoc to each locked file, you follow a consistent pattern: verify that you are authorized to work with the archive, move it into a controlled environment, perform non-destructive diagnostics first, decide whether access is feasible, and only then consider password-related actions or repairs.
In practice, this means you should:
- Confirm ownership and authorization before touching the archive, especially in shared or corporate environments.
- Use offline, trustworthy tools to inspect metadata and basic structure without extracting contents or sending files to third parties.
- Start with non-destructive diagnostics (format checks, error messages, structural cues) before making any changes or running repairs.
- Separate roles and permissions so that not everyone can access every archive or password, and keep basic logging of who did what.
- Handle passwords and hints as sensitive metadata, storing them securely and in a way that future you (or your team) can still understand.
- Plan for the full lifecycle of the archive: from intake to regular use, to long-term storage, and eventual deletion or handover.
When this workflow is written down, communicated, and supported by a dedicated offline toolkit, it becomes much easier for both individuals and teams to handle encrypted archives confidently — without improvisation, risky uploads, or compliance surprises.
🎯 Why a Defined Workflow Matters for Encrypted Archives
Encrypted archives protect sensitive data — which is exactly why mismanaging them can be so dangerous. Without a defined workflow, people often:
- Try random tools, including dubious online services.
- Share archives and passwords informally over chat or email.
- Forget where an archive came from or who is allowed to open it.
- Lose track of which version is the “real” one after repeated copies.
All of these behaviors create risk. A safe workflow brings order by forcing you to ask: Am I sure this is my archive?, Am I allowed to access it?, and What is the least invasive way to understand what’s going on? Before you move forward, you should be able to answer questions similar to those discussed in how to ensure you’re recovering only RAR files you own ↗️, so you don’t accidentally cross legal or ethical boundaries.
For organizations, a defined workflow also supports audits and compliance. It aligns nicely with higher-level guidance like legal considerations when working with your own encrypted archives ↗️, because you can show that handling is consistent, documented, and intentionally limited to authorized staff.
⚖️ Core Principles of a Safe Encrypted-Archive Workflow
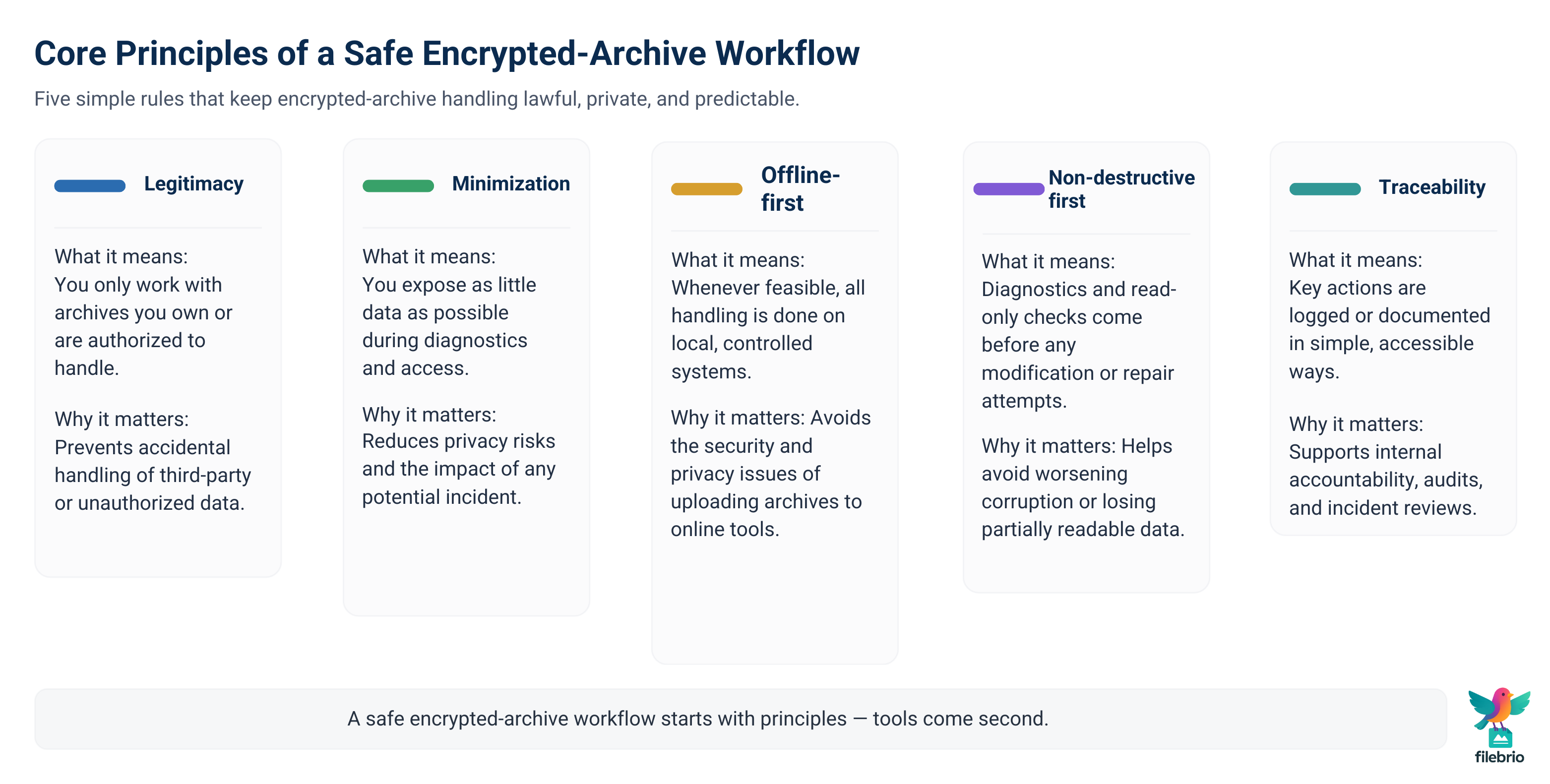
While every organization will adapt the details, most safe workflows are built on a few shared principles:
| Principle | What It Means | Why It Matters |
|---|---|---|
| Legitimacy | You only work with archives you own or are authorized to handle. | Prevents accidental handling of third-party or unauthorized data. |
| Minimization | You expose as little data as possible during diagnostics and access. | Reduces privacy risks and impact of any potential incident. |
| Offline-first | Whenever feasible, all handling is done on local, controlled systems. | Avoids the privacy and security issues of uploading to online tools. |
| Non-destructive first | Diagnostics precede any modification or repair attempts. | Helps avoid worsening corruption or losing partial data. |
| Traceability | Key actions are logged or documented in simple, accessible ways. | Supports internal accountability, audits, and incident reviews. |
These principles are fully consistent with broader legal and ethical guidelines for working with password-protected files ↗️. They focus on doing the right thing before you think about any kind of password-related action or recovery attempt, and they avoid step-by-step technical instructions that might be misused.
📂 Staged Workflow: From Intake to Archive Closure
To make principles practical, it helps to turn them into “stages” that can be followed consistently. A safe encrypted-archive workflow typically has at least these stages:
- Intake and ownership verification. Confirm who sent the archive, what project or account it belongs to, and that you have a legitimate reason to handle it.
- Quarantine and backup. Move the archive into a controlled location (e.g., a secure folder or isolated workspace) and make a read-only backup.
- Non-destructive diagnostics. Look at format, error messages, and basic structure before changing anything. Guidance such as how to diagnose a locked RAR archive without risking data loss ↗️ can be helpful here.
- Feasibility and risk evaluation. Decide whether access is technically feasible and legally appropriate, in line with ideas similar to evaluating safe options for regaining access to a RAR archive you own ↗️.
- Access and usage. If everything checks out, proceed with controlled extraction or access on a trusted device.
- Lifecycle decisions. After you’ve finished using the data, decide what to keep, where to store it, and what to retire or delete.
Each stage should be written down in simple language so that both technical and non-technical staff can follow it. This turns a one-time “procedure” into a routine habit that doesn’t depend on who happens to be working that day.

💼 Integrated Toolkit for Safe Encrypted-Archive Operations
Trying to run this workflow with a random mix of tools quickly becomes confusing. You may have one app for archive browsing, another for file integrity checks, and a third for limited repair — none of which were really designed for privacy-first diagnostics. A better approach is to adopt an integrated, offline toolkit focused on encrypted archives you legitimately own.
FileBrio RAR Master, as part of the broader FileBrio Office Suite, is designed around exactly this kind of workflow. Instead of juggling multiple utilities, you can work in a single environment that:
- Understands RAR and WinRAR formats deeply.
- Supports non-destructive investigation of locked archives.
- Keeps every operation entirely local on your machine.
| Workflow Need | Typical Challenge | How an Integrated Toolkit Helps |
|---|---|---|
| Verify structure and health | Difficult to see what’s going on without extracting anything. | Provides structure-aware diagnostics similar to the FileBrio RAR Master features overview ↗️. |
| Stay offline | Online tools may log or store your archives indefinitely. | Aligns with the offline approach described in why offline recovery tools are safer for privacy ↗️. |
| Compare local vs online options | Non-experts may be tempted by “instant unlock” sites. | Helps visualize and explain the differences you’d see in offline vs online RAR recovery comparisons ↗️. |
For organizations, standardizing on one offline suite also simplifies training and documentation. Instead of teaching three or four tools, you can provide a single, well-defined path for encrypted-archive work.
________________________
FileBrio RAR Master — part of the FileBrio Office Suite — is a privacy-first, offline Windows toolkit for diagnosing and safely regaining access to your own password-protected RAR / WinRAR archives.
- Local processing only — nothing leaves your PC.
- Smart diagnostics to separate password issues from corruption.
- Owner-verified recovery workflows designed strictly for legitimate use.
Reminder: FileBrio RAR Master may be used only with archives you own or are explicitly authorized to access. It performs all analysis and recovery operations locally on your device, without uploading data anywhere.
________________________
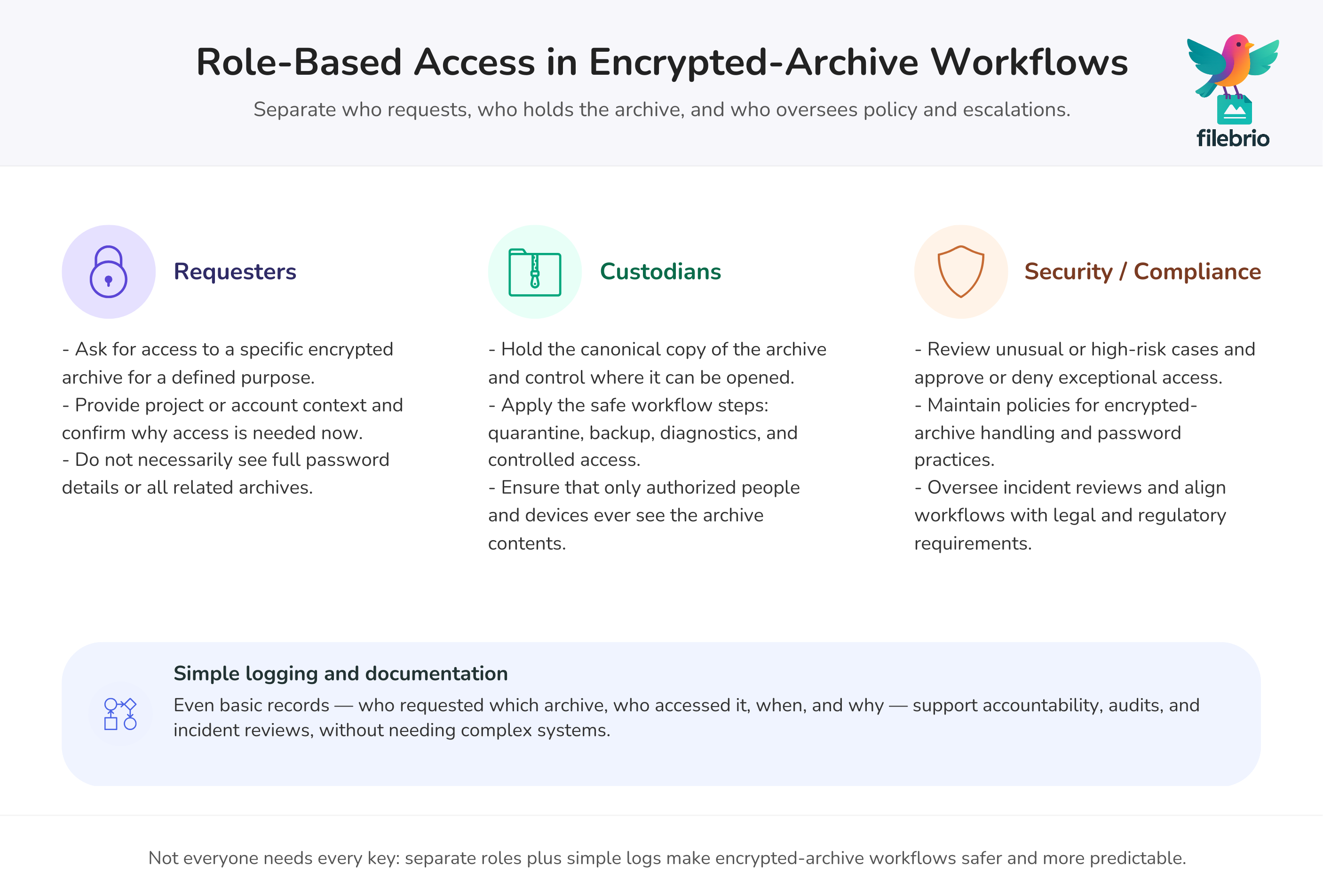
👥 Role-Based Access, Logging, and Separation of Duties
In a team or enterprise, a safe workflow is not just about tools — it’s also about who is allowed to do what. A good pattern is to separate roles so that:
- Not everyone has direct access to every archive.
- Not everyone sees every password or hint.
- At least one person is responsible for oversight and documentation.
For example, a typical setup might include:
- Requesters who ask for access to a given archive.
- Custodians who hold the archive and control where it can be opened.
- Security or compliance staff who review unusual cases or escalations.
Logging doesn’t have to be complicated. Even a simple internal ticket or spreadsheet that lists “who accessed which archive when, and why” can support the kind of documentation described in how to maintain long-term access to encrypted RAR archives in enterprises ↗️. It also helps you demonstrate that you followed consistent, responsible procedures if questions arise later.
🔑 Working Safely With Passwords and Metadata
Passwords and hints are the most delicate part of any encrypted-archive workflow. Treat them as sensitive metadata, not as disposable notes. At the same time, avoid central “master lists” that everyone can read without controls.
Safe handling usually includes:
- Storing hints and metadata separately from the archive itself, following practices similar to how teams should store RAR password metadata safely across devices and roles ↗️.
- Recording context, not just strings: where the archive came from, who owns it, and under what policy it was created.
- Using secure locations (password managers, encrypted notes, or dedicated vaults) instead of plain text documents.
- Planning for future access, taking inspiration from how to safely store RAR password metadata for future access ↗️.
At policy level, your workflow should echo the spirit of common mistakes when working with password-protected RAR archives ↗️ by discouraging things like reusing simple passwords, sharing them over chat, or writing them in unprotected documents. Over time, this significantly lowers the risk that you’ll lock yourself out of your own archives — or accidentally expose them.
🧪 Using Test and Dummy Archives for Training and Validation
Training new staff on encrypted-archive handling can be risky if you use real customer or internal data. A simple, powerful alternative is to build your workflow around dummy archives: test files that mimic real structure and protection levels, but contain no sensitive content.
With dummy archives, you can:
- Demonstrate each workflow stage in a safe environment.
- Test how tools behave with different formats and error scenarios.
- Practice incident response in a controlled way.
This approach is closely aligned with the ideas in how to safely evaluate RAR protection using dummy archives ↗️. When everyone has seen how the workflow plays out on harmless data, they are much less likely to panic — or improvise — when they have to handle a real encrypted archive under time pressure.
🚨 Handling Incidents, Errors, and Suspicious Situations
Even with the best workflow, things can still go wrong: a file arrives from an unknown sender, error messages look unusual, or someone discovers that an archive has been shared outside normal channels. Your workflow should explicitly describe what to do when something feels off.
Typical guidelines include:
- Stop and document. Don’t keep trying random actions; record what you saw and when.
- Escalate to the right person or team, especially for legal or regulatory questions.
- Avoid uploading “problematic” archives to random online tools just to see what happens — this conflicts with the privacy-first approach in why offline recovery tools are safer for privacy ↗️.
- Review policies and approvals before attempting any repair or password-related action.
Incidents should feed back into your workflow. If you discover that people frequently skip intake checks or ownership verification, it may be time to refine your process using lessons from legal considerations when working with encrypted archives ↗️ and similar policy-oriented resources.
🔐 Secure Offline Suite for Encrypted Archive Workflows
All of these steps are easier when you have a dedicated, trusted suite on your side. Instead of teaching people “never upload sensitive archives anywhere”, you can say: “Whenever you need to work with encrypted archives, use this offline suite and follow the documented workflow.”
FileBrio Office Suite, and its RAR-focused components such as RAR Master, are built for exactly this role: a secure, local environment where encrypted archives can be inspected and handled responsibly. From a workflow perspective, this means you can:
- Standardize on a single, controlled toolset for encrypted archives.
- Align technical handling with internal policies and with materials like the FileBrio RAR Master support and legal guidance ↗️.
- Deploy the suite from an official, up-to-date source, such as the FileBrio Office Suite download page ↗️, instead of ad-hoc installers.
By anchoring your workflow to one offline suite, you give both individuals and teams a clear path: “this is how we handle encrypted archives here,” with tools and policies working together rather than against each other.
________________________
FileBrio RAR Master — a secure, offline Windows toolkit for regaining access to your own password-protected RAR / WinRAR archives while keeping all data strictly on your device.
- Offline-only processing — never uploads your archives.
- Smart issue detection — password vs corruption.
- Fast recovery workflow optimized for legitimate ownership.
⬇️ Download FileBrio RAR Master
Reminder: FileBrio RAR Master is intended only for archives you own or are explicitly authorized to access. All operations run locally on your PC.
________________________
📦 Long-Term Access and Archive Lifecycle Management
Encrypted archives often outlive individual projects, employees, or even entire departments. A safe workflow therefore has to include lifecycle management: how archives are created, used, stored, and eventually retired.
Practical steps include:
- Defining retention periods for different archive categories (e.g., short-term project data vs long-term legal or financial records).
- Planning for staff turnover so that access does not disappear when a single person leaves the company.
- Regularly checking the health of storage systems and migrating archives before media becomes obsolete or unreliable.
- Reviewing password and metadata practices periodically to ensure that they still match your technical and legal reality.
Resources like how to maintain long-term access to encrypted RAR archives (teams & enterprises) ↗️ and legal considerations when working with encrypted archives ↗️ are useful reference points when defining these lifecycle rules. They help you balance strong security with the practical need for future access — so that archives don’t become impossible to open for your own organization later.
⚖️ Legal Reminder
This article is provided for general informational and educational purposes only. Any examples, scenarios, or references to password recovery, archive security, or related tools (including FileBrio RAR Master or similar software) are intended solely to help you better understand how to protect and manage your own data.
You may only apply any techniques, workflows, or tools described here to files and archives that you fully own or are explicitly and verifiably authorized to access. Attempting to bypass, remove, or recover passwords for third-party data without clear permission may violate criminal law, civil law, or internal company policies in your jurisdiction.
Nothing in this article constitutes legal advice. Laws and regulations differ between countries and organizations, and you are solely responsible for ensuring that your actions comply with all applicable legislation, contracts, and internal policies. If you are unsure whether a particular action is lawful or permitted, consult a qualified legal professional before proceeding.
📚 See Also
- How to Check the Internal Structure of RAR Archives Without Extracting Files ↗️
- What to Try Before Considering Any Password Guessing on Your Own RAR File ↗️
- What to Do When WinRAR Shows ‘Unexpected End of Archive’ ↗️
- Lost Your RAR/WinRAR Password? How to Assess Your Situation Before Taking Action ↗️
- Opening RAR/WinRAR Archives With or Without a Password: A Practical Guide to Safe Access Options ↗️
- How to Avoid Losing Access to Decade-Old RAR Archives ↗️
- How to Determine If a RAR Archive Uses Header Encryption ↗️