
Restoring Access to RAR/WinRAR Archives: Safe and Legal Methods for Handling Your Own Files
You open a RAR or WinRAR file that clearly belongs to you—old financial records, client deliverables, an internal project snapshot—and instead of familiar contents you see an error message or a password prompt you no longer recognize. A few searches later, your browser is full of promises: “instant unlock,” “online decryption,” “no password needed.” It is very easy to feel that you must either trust one of these risky offers or give up on your own data.
In reality, you have more measured, safer options. Restoring access to an encrypted archive you legitimately own is not about magic “unlocking”; it is about diagnosing what is really wrong, respecting legal boundaries, and using privacy-first tools to explore what is realistically possible. Sometimes that leads to full recovery; sometimes it leads to an honest conclusion that the archive has become mathematically or structurally unrecoverable—but you reach that conclusion safely, without exposing sensitive information.
This article walks step by step through safe, legal methods for handling your own RAR/WinRAR archives when you cannot open them anymore. You will learn how to confirm ownership and authorization, diagnose technical issues, evaluate whether recovery attempts make sense, choose offline tools over risky websites, and improve your habits so fewer archives require “rescue” in the future.
🧭 Navigation
Important
The information provided in this article applies exclusively to RAR / WinRAR archives for which you have full, demonstrable ownership or properly documented authorization. If you are not the rightful owner of the data, do not directly control it, or cannot clearly prove permission to access it, you must stop immediately. Attempting to access, recover, or modify data without explicit authorization may violate criminal law, civil statutes, corporate compliance requirements, and privacy regulations in many jurisdictions. You alone are responsible for ensuring that your actions are lawful and properly permitted before proceeding.
📝 TL;DR — A Safe Roadmap for Restoring Access
If you cannot open a RAR/WinRAR archive, do not start with random guessing or online “unlockers.” Instead, follow a structured, privacy-first roadmap focused on archives you legitimately own. First, confirm that you are authorized to access the data and that you are not inadvertently working with a file that belongs to someone else or to your employer without proper approval. Legal context comes before any technical steps.
Next, diagnose what is actually blocking access. An archive that “won’t open” may be affected by a forgotten password, file corruption, missing volumes, format or version mismatches, or a combination of these. Non-destructive diagnostics—checking error messages carefully, inspecting metadata, verifying file integrity on a copy—often reveal whether you are dealing with a password problem, a damaged file, or both. Only after you understand the symptoms should you evaluate whether the archive is still technically recoverable and whether your situation justifies any password-related work at all.
From there, choose safe, offline methods for any recovery attempts. Avoid uploading sensitive archives to unknown websites, and prefer tools that keep all processing local while giving you clear diagnostics and responsible recovery options. In many cases, structured memory work, older backups, or policy-compliant help from your IT or security team provide better outcomes than unbounded password attempts. Finally, treat the incident as a lesson: strengthen your password design habits, store metadata securely, and build team-wide or corporate practices that make future access failures much less likely.
- Always work on a copy of the archive.
- Only handle files you legitimately own or are authorized to access.
- Prefer offline, privacy-focused tools over online “decryption” sites.
- Use recovery experiences to improve future password and archive management practices.

⚖️ Step 1: Confirm Ownership and Legal Boundaries
Any responsible attempt to restore access to an encrypted archive starts with one simple question: am I legitimately allowed to access this data? Encryption exists to protect confidentiality. That protection does not disappear just because a file seems convenient to you.
In a personal context, “ownership” usually means that you created the archive yourself or that it clearly belongs to your private files (backups of your own documents, photos, or projects). In professional settings, things are more nuanced: the archive may be tied to your employer, a customer, or shared corporate assets. Your organization’s policies, contracts, and regulations determine what is allowed.
Because of this, a safe recovery process should always include simple but explicit checks:
- Who created the archive, and under what context (personal, corporate, client)?
- Who is the data controller or owner according to your policies or contracts?
- Has the archive been handed off from a previous role or employee, and is there traceable authorization?
High-level guidance on ensuring you are working only with your own data is covered in how to verify ownership before accessing your RAR file ↗️, which can help you document legitimacy before you touch anything technical. For corporate environments, it is also wise to align with broader legal and ethical guidelines for working with password-protected files ↗️, so that your actions match both local law and internal compliance frameworks.
🔍 Step 2: Understand Why Your Archive Won’t Open
Once ownership and authorization are clear, the next step is to understand what is actually happening when you try to open the archive. A surprising number of “password problems” turn out to be something else.
Ask yourself:
- Do you see a clear “wrong password” error immediately after typing a value?
- Do error messages mention “unexpected end of archive,” checksums, or corruption?
- Can you see a file list at all, or does the archive appear empty or unreadable?
Each pattern tells a different story. An instant “wrong password” suggests the archive is structurally sound but protected with a password you are not reproducing correctly. Errors during extraction often point to corruption or incomplete data. If the archive shows almost no information until you enter a password, header encryption and filename protection may be active.
To structure this analysis, it helps to use a diagnostic mindset. Articles like ways to diagnose your unopened RAR file issue ↗️ and how to identify the real reason a RAR archive won’t open ↗️ break down the common scenarios: wrong password, corruption, format mismatch, or missing volumes. Studying those patterns before you act can prevent you from wasting time on the wrong problem.
Remember to always work on a copy of the archive while you test. If your storage medium is failing or if you need to attempt repairs later, you will be glad you preserved the original file in its untouched state.
🧪 Step 3: Check Whether Your Archive Is Still Technically Recoverable
Not every inaccessible archive is recoverable, even when it clearly belongs to you. Strong encryption, severe corruption, or both may push a file beyond the reach of realistic recovery efforts. Before investing significant time, you should evaluate whether the archive is still technically viable.
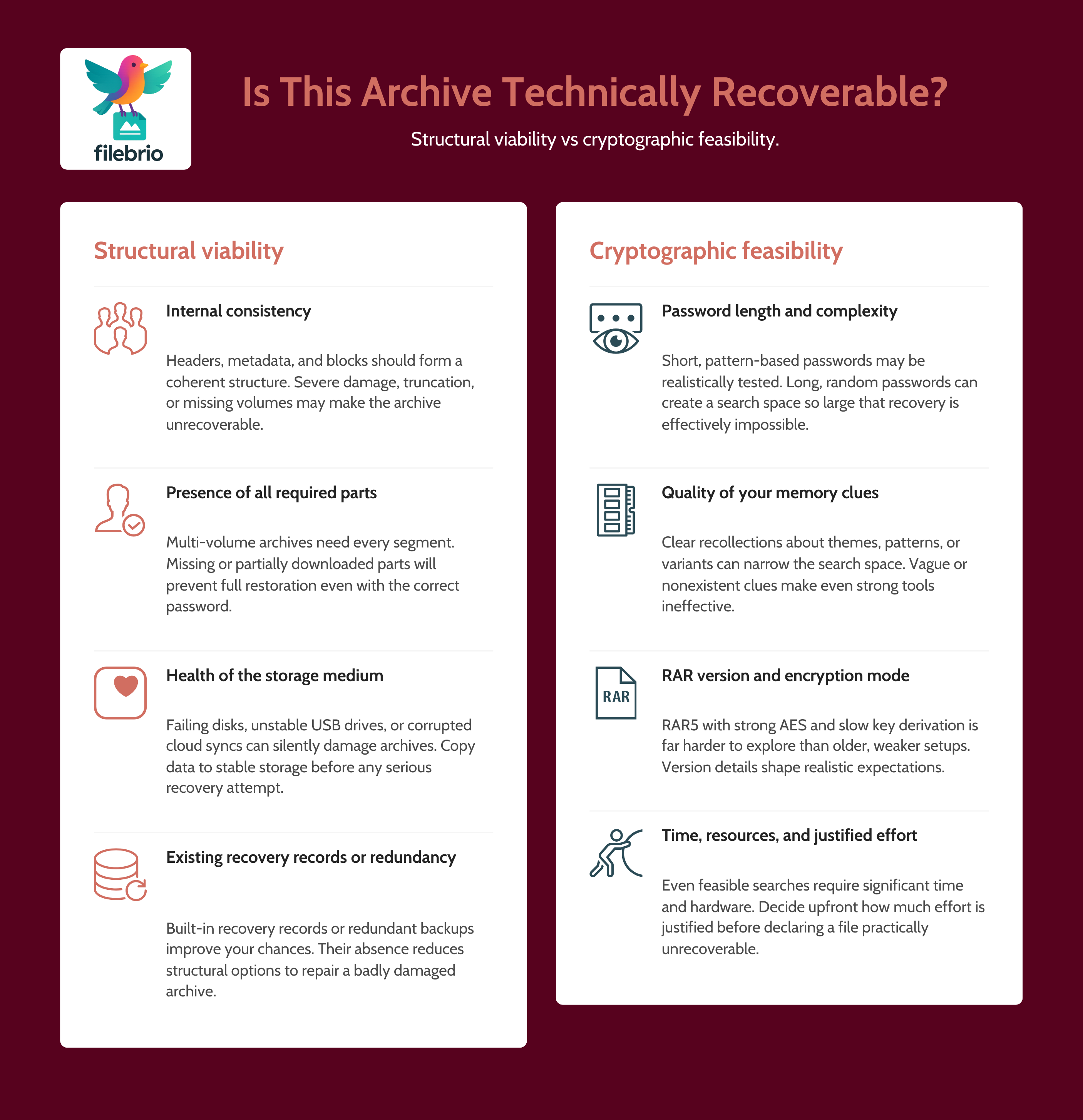
This evaluation has two parts:
- Structural viability: is the archive internally consistent, or is it heavily damaged or truncated?
- Cryptographic feasibility: assuming the archive is structurally sound, does your password situation leave any realistic path to success?
Structural viability is about the health of the file itself. Tools that inspect headers, metadata, and recovery records can tell you whether blocks are missing, whether multi-volume sets are incomplete, and whether built-in recovery features exist. A detailed framework for this kind of analysis is described in how to confirm whether your RAR archive is still technically recoverable ↗️, which can help you separate “difficult but possible” cases from “almost certainly unrecoverable” ones.
Cryptographic feasibility is about realistic effort. If your password was short and based on a limited character set, or if you still have strong memory clues, there may be a narrow search space worth exploring. If it was a long, random string or generated by a password manager you no longer have access to, the effective search space might be vast. High-level guidance on when to continue and when to stop is available in when it makes sense to attempt password recovery — and when the archive is mathematically unopenable ↗️.
🧩 All-In-One Suite to Centralize Safe RAR Recovery Work
By this stage, you can see that “restoring access” is a combination of ownership checks, diagnostics, and feasibility analysis—not just a single button labeled “decrypt.” Trying to piece that together by hand with scattered utilities and risky websites is stressful and error-prone, especially when the archive contains sensitive personal or business data.
Many users and organizations find it easier to rely on a dedicated desktop suite that brings these tasks together in one place. The right toolkit can:
- Run structural diagnostics on a copy of the archive before any password attempts.
- Highlight whether you are dealing with RAR4 or RAR5, header encryption, recovery records, or multi-volume sets.
- Help you separate pure password issues from corruption or format problems.
- Operate entirely offline, so your confidential archives never leave your own systems.
If you want to understand how such an approach can look in practice, you can review what FileBrio RAR Master can do ↗️ as an example of an all-in-one RAR recovery toolkit. Having clearly documented capabilities makes it easier to build policies and procedures around safe, legal recovery of your own archives.
________________________
FileBrio RAR Master — part of the FileBrio Office Suite — is a privacy-first, offline Windows toolkit for diagnosing and safely regaining access to your own password-protected RAR / WinRAR archives.
- Local processing only — nothing leaves your PC.
- Smart diagnostics to separate password issues from corruption.
- Owner-verified recovery workflows designed strictly for legitimate use.
Reminder: FileBrio RAR Master may be used only with archives you own or are explicitly authorized to access. It performs all analysis and recovery operations locally on your device, without uploading data anywhere.
________________________
🚦 Step 4: Safe Options Before Any Password Attempts
Even if diagnostics suggest that your archive is structurally sound and protected by a forgotten password, you still do not have to jump straight into active password work. There are several lower-risk avenues to explore first.
1. Structured memory and context work. Many users regain access by systematically revisiting their own habits instead of launching unbounded guessing. You might review similar archives you created around the same time, notes in password managers, or patterns you typically used for that type of data. Articles such as practical methods to reaccess your locked RAR file ↗️ offer safe approaches to re-evaluating your own password choices before you consider anything more intensive.
2. Look for alternative sources or older backups. Sometimes the encrypted archive isn’t the only copy of the data. Older unencrypted backups, parallel folders, or archived emails may exist. Restoring data from those sources may be faster and safer than attempting deep recovery on a single encrypted file.
3. Consult internal IT or security teams. In corporate environments, your IT or security department may already have tools, policies, and procedures for handling locked archives that belong to the organization. Coordinating with them helps ensure that any recovery attempt is properly authorized and documented.
All of these options preserve your privacy and reduce the chance that you will make stressful, high-effort attempts on an archive that could have been handled in a simpler way.
⚙️ Step 5: When Limited, Legitimate Password Work Is Appropriate
After you have exhausted safer alternatives and confirmed that the archive is both technically viable and legitimately yours, it may be appropriate to engage in limited, carefully controlled password work—always offline and always within clear boundaries.
Key principles include:
- Work only on a copy: keep the original archive untouched and store it in a safe location.
- Define your search space: base any attempts on realistic patterns drawn from your memory and habits, not on open-ended “try everything forever” approaches.
- Set time and scope limits: decide in advance how long you will run any process and under what conditions you will stop.
Before starting, it is essential to remember that strong encryption gives RAR archives the ability to become effectively unrecoverable. There is no hidden reset mechanism: as explained in how RAR security works and why passwords can’t be reset like email credentials ↗️, access depends entirely on the strength and recall of your chosen password.
If you are evaluating whether it is worth investing effort in a constrained password search, high-level guidance on safe strategy selection is offered in how to evaluate safe options for regaining access to a RAR/WinRAR archive you own ↗️. It focuses on balancing feasibility, privacy, and legal boundaries so that any attempts you make stay within responsible limits.
🛡️ Secure Offline Environment for Privacy-First Recovery
Once you decide that limited password work is warranted, where you carry it out becomes crucial. Uploading sensitive archives to anonymous websites significantly increases your risk, even if the site claims to “delete everything after processing.” You have no practical way to verify those claims, and any breach or misuse could expose highly personal or confidential data.
A secure, offline environment gives you controlled conditions for diagnostics and recovery:
- All operations are performed on your own hardware, within your own network or approved infrastructure.
- You can combine structural diagnostics, format checks, and responsible password work in one place.
- You retain full control over logs, audit trails, and the resulting decrypted data.
Comparisons between online and offline approaches are explored conceptually in compare online unlockers and local tools ↗️, which can help you justify an “offline-first” policy. For organizations, it is equally important that such tools are backed by clear rules and support. Resources like the FileBrio support and legal details ↗️ page illustrate how software can be framed explicitly for responsible use, making it easier to align operations with internal and external requirements.
When you are ready to deploy or update a privacy-first toolkit, you can get the latest FileBrio Office Suite installer from the official download page ↗️ so that your recovery environment stays consistent with your policies and security expectations.
________________________
FileBrio RAR Master — a secure, offline Windows toolkit for regaining access to your own password-protected RAR / WinRAR archives while keeping all data strictly on your device.
- Offline-only processing — never uploads your archives.
- Smart issue detection — password vs corruption.
- Fast recovery workflow optimized for legitimate ownership.
⬇️ Download FileBrio RAR Master
Reminder: FileBrio RAR Master is intended only for archives you own or are explicitly authorized to access. All operations run locally on your PC.
________________________
🕵️ Step 6: Avoiding Common Recovery Risks and Pitfalls
Many of the worst outcomes in RAR recovery scenarios come not from encryption itself but from rushed or misinformed reactions. Knowing what to avoid is just as important as knowing what to do.
1. Avoid unvetted online “unlockers.” Sites that promise to “instantly open any RAR file” often gloss over technical realities while asking you to upload sensitive data. Once the archive is on a remote server, you have no meaningful control over how it is stored or used. For a deeper look at why such tools often disappoint—and sometimes create more risk than benefit—see why online RAR password tools fail ↗️.
2. Be wary of tools that over-promise decryption capabilities. Any software claiming to bypass strong encryption without the correct key should be treated skeptically. Strong RAR encryption is designed to resist exactly those attempts. Safe offline solutions focus instead on diagnostics, controlled recovery options, and clear feasibility boundaries.
3. Do not ignore privacy when you are desperate. When important data feels “lost,” it is tempting to overlook where your archives are being sent, what tools you are installing, or who might gain access. Instead, follow privacy-first principles as outlined in why offline recovery tools are safer for privacy ↗️, and treat your encrypted archives as sensitive even when they feel inaccessible.
4. Avoid ad-hoc, undocumented attempts in corporate environments. If you work within an organization, uncoordinated recovery efforts can conflict with audit, compliance, and legal obligations. It is safer to align with established policies and escalate to responsible teams when needed.

📦 Step 7: Long-Term Practices to Reduce Future Lockouts
Every difficult recovery situation is also a signal to improve your habits so that the next archive you create is easier to manage, even years in the future.
1. Use strong yet manageable passwords. You want passwords that are long and high entropy, but still tied to structures your future self can understand and support with metadata. Balancing these needs is easier when you design your password strategy consciously rather than improvising each time you create a new archive.
2. Document metadata and context safely. Instead of storing raw passwords in plain text, focus on storing metadata—where the archive fits in your workflows, what kind of password structure it uses, and who is responsible for it. In personal contexts, principles from how to organize metadata for your RAR passwords safely ↗️ can keep “future you” out of trouble. In team or enterprise contexts, you can adopt shared variants that span roles and devices.
3. Integrate archive practices into your security posture. For organizations, encrypted RAR archives should not live outside the normal governance process. They need to be covered by password policies, classification schemes, and retention rules. Concepts from how to strengthen RAR archive security while preserving future access ↗️ can help you design policies that are both secure and workable.
4. Educate users on realistic expectations. Whether at home or at work, people should understand that strong encryption means there may be no second chances if passwords are truly lost and no backups exist. That understanding encourages better documentation and more careful handling of important archives.
⚖️ Legal & Ethical Reminder
This article is provided for general informational and educational purposes only. Any examples, scenarios, or references to password recovery, archive security, or related tools (including FileBrio RAR Master or similar software) are intended solely to help you better understand how to protect and manage your own data.
You may only apply any techniques, workflows, or tools described here to files and archives that you fully own or are explicitly and verifiably authorized to access. Attempting to bypass, remove, or recover passwords for third-party data without clear permission may violate criminal law, civil law, or internal company policies in your jurisdiction.
Nothing in this article constitutes legal advice. Laws and regulations differ between countries and organizations, and you are solely responsible for ensuring that your actions comply with all applicable legislation, contracts, and internal policies. If you are unsure whether a particular action is lawful or permitted, consult a qualified legal professional before proceeding.
📚 See Also: Related RAR Access Guides
- How to Diagnose a Locked RAR Archive Without Risking Data Loss ↗️
- Legal Considerations When Working With Your Own Encrypted Archives ↗️
- How to Ensure You’re Recovering Only RAR Files You Own ↗️
- Open RAR Files Without a Password? What’s Possible, What Isn’t, and How to Access Your Data Safely ↗️
- Resetting a RAR/WinRAR Password: Why Resets Don’t Exist and What Safe Options You Actually Have ↗️
- Brute-Forcing a RAR/WinRAR Password? Legal Boundaries, Practical Limits, and Safe Use Cases ↗️
- RAR/WinRAR File Passwords Explained: How Encrypted Archives Work and What Access Options You Have ↗️