
Why RAR5 Is More Secure — and What That Means for File Access
RAR5 arrived as a major evolution in archive security — stronger encryption, smarter key handling, safer metadata protection, and structural improvements designed to withstand modern threats. But stronger protection also means one important thing for legitimate users: your own ability to access your RAR files depends entirely on what you remember, preserve, and maintain over time.
You’re here because you either have a RAR5 archive you can’t open, are considering converting older files to RAR5, or want to understand what “better security” really implies for long-term access. This article gives you the full picture — high-level cryptography, practical impacts on access, structural changes, risks of forgetting passwords, and safe strategies for staying in control of your own data.
🧭 Navigation
Important
The information provided in this article applies exclusively to RAR / WinRAR archives for which you have full, demonstrable ownership or properly documented authorization. If you are not the rightful owner of the data, do not directly control it, or cannot clearly prove permission to access it, you must stop immediately. Attempting to access, recover, or modify data without explicit authorization may violate criminal law, civil statutes, corporate compliance requirements, and privacy regulations in many jurisdictions. You alone are responsible for ensuring that your actions are lawful and properly permitted before proceeding.
📌 TL;DR — Why RAR5 Security Is Stronger and How It Impacts Access
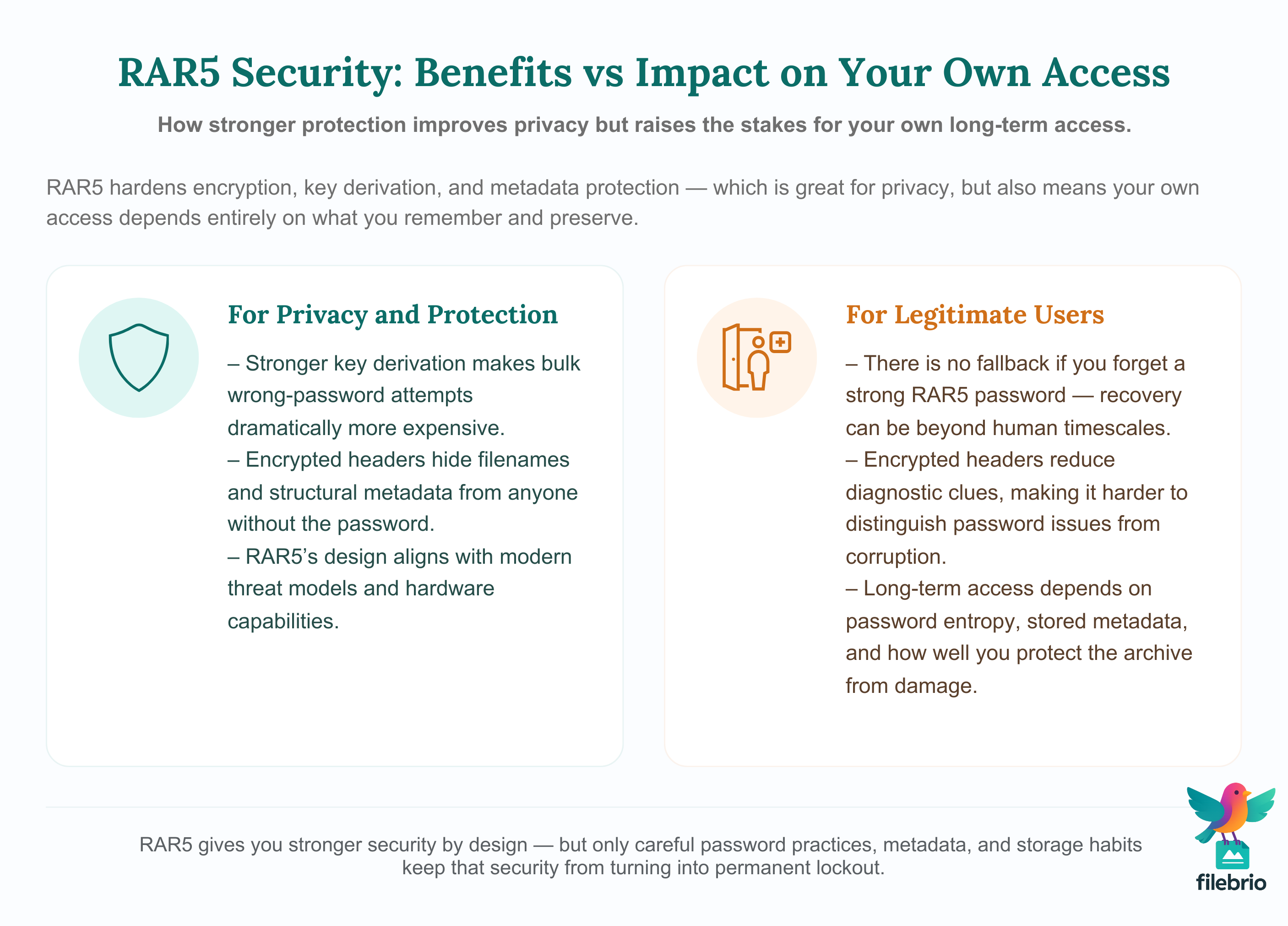
RAR5 is significantly more secure than previous RAR formats because it modernizes three critical components: the encryption, the key derivation function, and how metadata is protected. Instead of simply encrypting data, RAR5 introduces a more expensive key derivation step that slows down each password attempt, making bulk guessing attempts dramatically harder even on modern hardware. It also expands support for encrypted headers, meaning filenames and structural metadata are hidden by default, reducing the amount of information visible to anyone who doesn’t know the correct password.
This enhanced protection is great for privacy — but it also means that RAR5 provides no fallback whatsoever if you forget your own password. With strong user-selected passwords, the combination of high entropy and RAR5’s KDF can push recovery far beyond practical human timescales. Diagnostic visibility also decreases because header encryption hides details that tools normally use to validate guesses or assess file health. For legitimate users, this means planning ahead: storing password metadata, maintaining secure notes, protecting the archive from corruption, and using reliable offline tools for any diagnostics or recovery attempts. If you handle sensitive or long-term archives, proper preparation determines whether RAR5 feels “strong and reliable” or “unopenable forever.”
🔐 What RAR5 Changes Compared to RAR4
RAR5 was designed to modernize the security model of WinRAR archives. Earlier formats like RAR4 were secure for their time, but hardware and cryptographic research evolve. RAR5 introduces improvements that make archives more resistant to unauthorized access — and more predictable in how they behave under different conditions.
RAR5’s main advancements include:
- Stronger key derivation that increases the cost of generating cryptographic keys from passwords.
- Default encrypted headers that hide filenames and structural metadata.
- More consistent handling of Unicode, metadata, and archives created across devices.
- Improved error resilience and recovery capabilities (when combined with recovery records).
To compare how earlier versions differ and why newer designs matter, you can review how RAR4 and RAR5 secure your protected data ↗️, which explains the evolution of cipher use, metadata visibility, and internal architecture.
🧠 The RAR5 Key Derivation Function: Why It Matters
The most important change RAR5 introduces is a more expensive key derivation function (KDF). Instead of taking your password and running it through a relatively fast hashing process, RAR5 forces every password attempt to undergo a significantly heavier computation.
This matters for two reasons:
- It dramatically slows down incorrect password attempts.
- It makes large-scale guessing attempts inefficient even on GPUs.
In simpler terms: the same password is just as strong under RAR4 and RAR5 in theory, but under RAR5, the cost of verifying each guess is much higher, which multiplies your effective real-world security.
A deeper explanation of why the KDF matters is available in how the RAR5 KDF strengthens your encrypted RAR file ↗️. The article also shows how RAR5’s design discourages mass guessing and protects password-derived keys more effectively.
🧮 How Password Entropy Behaves Under RAR5
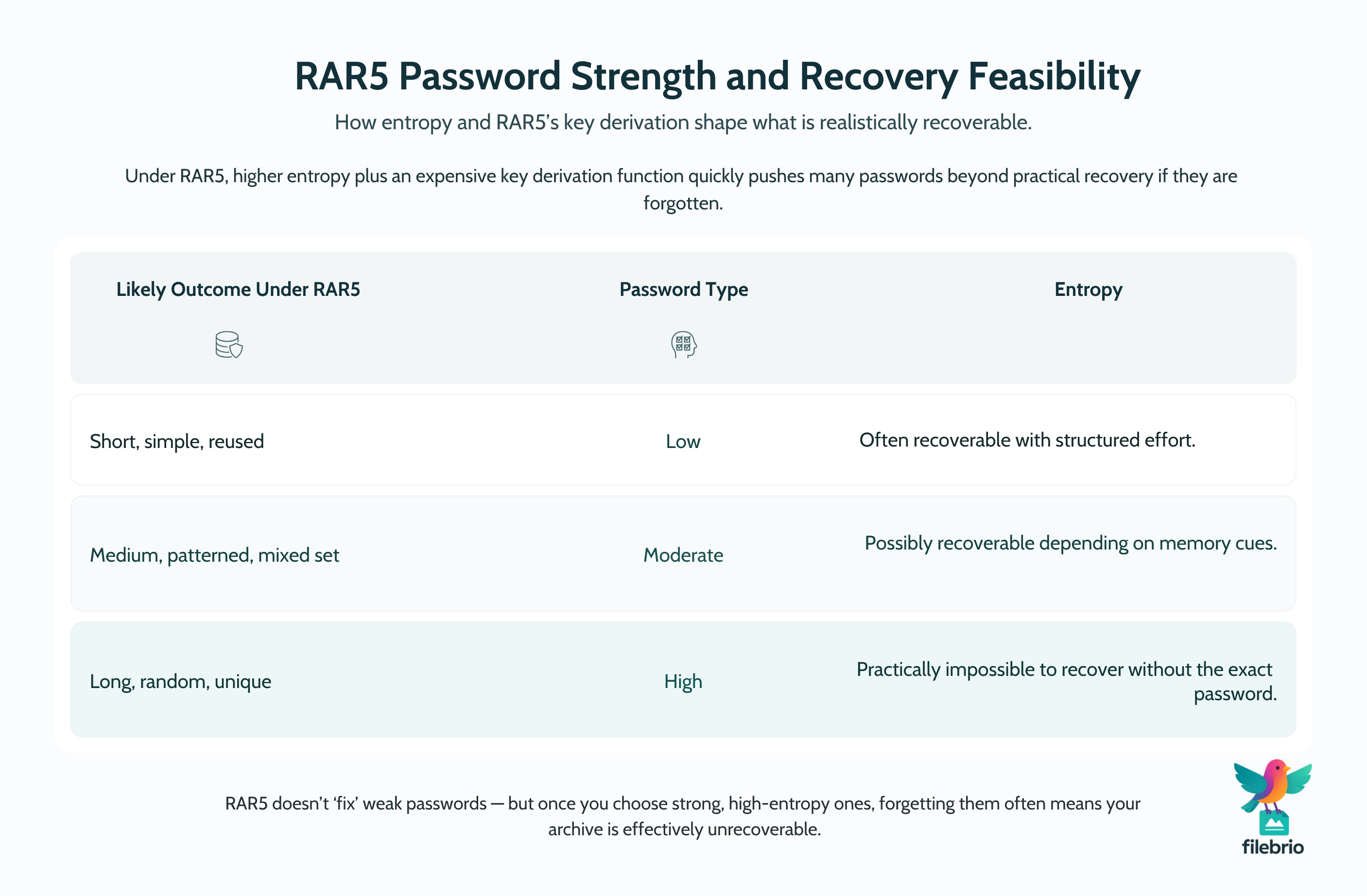
Password entropy — the randomness and unpredictability of the password — determines whether your archive is realistically recoverable. Under RAR5, entropy matters even more because:
- Each attempted password costs more computation time.
- Search space (all possible passwords) grows exponentially with length.
- GPU acceleration helps, but cannot overcome exponential explosion.
For a clearer conceptual picture of how password size and randomness affect difficulty, review how length impacts protection of your RAR password ↗️. Even moderate increases in complexity under RAR5 can place archives firmly in the “mathematically inaccessible” category if you lose the password.
Under RAR5, the relationship is roughly:
| Password Type | Entropy | RAR5 Outcome |
|---|---|---|
| Short, simple, reused | Low | Often recoverable with structured effort |
| Medium, patterned, mixed set | Moderate | Possibly recoverable depending on memory cues |
| Long, random, unique | High | Practically impossible to recover without the exact password |
This is both a feature and a sharp-edged tool: stronger encryption = stronger consequences if password memory is lost.
🗂️ Encrypted Headers, Metadata, and Privacy Effects
One of RAR5’s most user-visible changes is the way it hides metadata through encrypted headers. When enabled (often by default), this feature conceals:
- Filenames
- File sizes
- Directory structure
- Some structural markers that diagnostic tools rely on
This increases privacy — someone cannot even see what the archive contains without the password — but it also removes helpful information that could assist legitimate diagnostics. To understand why, review why encrypted headers make content discovery impossible ↗️.
Because of this feature, a corrupted or partially damaged RAR5 archive with encrypted headers may present very little actionable information. The archive can become “blind,” meaning tools cannot distinguish between:
- wrong password
- corrupted content
- missing data segments
- incorrect archive format assumptions
This doesn’t indicate a problem with the archive format — it indicates that the privacy model is working exactly as designed.
🧪 How RAR5 Affects Real-World Diagnostics and Access
RAR5’s enhancements help keep unauthorized users out — but they also affect your ability to diagnose legitimate issues. The combination of:
- slow KDF
- strong encryption
- encrypted headers
- more compact metadata
means that RAR5 archives provide fewer clues about what’s happening inside.
Typical consequences include:
- Very little feedback on incorrect passwords — error messages look identical across different failure causes.
- Harder corruption assessment — especially if damage occurs early in the archive.
- Difficulty distinguishing password issues from structural issues.
For additional strategies to tell password and corruption scenarios apart, see how to identify whether your RAR file is encrypted or simply corrupted ↗️, which explains the high-level clues to look for.
🧰 All-In-One Solution for Working With RAR5 Archives
RAR5’s security design requires a workflow built around:
- local processing
- privacy-focused diagnostics
- structural understanding of archive formats
FileBrio Office Suite — especially its dedicated RAR module — helps legitimate users safely:
- inspect archives without exposing them online
- analyze structure vs. password vs. corruption symptoms
- evaluate whether the archive is realistically recoverable
Its feature set is described in FileBrio RAR Master’s full capability overview ↗️, which outlines diagnostics, offline workflows, and format-aware tools.
You can always obtain all FileBrio tools safely from the official installer page ↗️ without relying on third-party sites.
________________________
FileBrio RAR Master — part of the FileBrio Office Suite — is a privacy-first, offline Windows toolkit for diagnosing and safely regaining access to your own password-protected RAR / WinRAR archives.
- Local processing only — nothing leaves your PC.
- Smart diagnostics to separate password issues from corruption.
- Owner-verified recovery workflows designed strictly for legitimate use.
Reminder: FileBrio RAR Master may be used only with archives you own or are explicitly authorized to access. It performs all analysis and recovery operations locally on your device, without uploading data anywhere.
________________________
🚫 Why RAR5 Makes Wrong-Password Attempts Much Harder
RAR5’s KDF ensures that every password attempt requires a measurable amount of computation. This means:
- guessing efforts scale slowly
- large search spaces quickly become unmanageable
- GPU acceleration provides only limited relief
Even with powerful hardware, the key derivation cost limits the number of guesses per second. This is why the feasibility of recovering an archive depends largely on password behavior rather than the tools themselves. For more detail, see how to interpret timing estimates for your RAR password ↗️, which explains why “faster hardware” alone cannot overcome entropy.
From a protection standpoint, this is ideal — unauthorized access remains blocked. From a legitimate user standpoint, the message is clear:
RAR5 requires you to plan ahead if you ever want to access the archive again.
📅 Planning Future-Proof Access to RAR5 Archives
If you intend to store long-term backups or sensitive data, RAR5’s stronger protection means you must adopt better self-access strategies. Some practical recommendations:
- Store password metadata securely.
Not the password itself — just reliable private notes about styles, lengths, structures, languages, and patterns. For practical guidance, see how to preserve password metadata for future access ↗️. - Protect the archive from corruption.
Strong encryption does not defend you from physical damage. - Use recovery records for critical archives.
They add redundancy that can save you if parts of the file degrade. - Keep archives in verified storage locations.
Rotting USB drives, old HDDs, and multiple platform transfers increase the risk of partial unreadability. - Plan for team access if multiple people need it.
RAR5 offers no “password recovery mode,” so consistent documentation is vital.
If you want guidance on preserving access for years or decades, how teams can preserve long-term access to encrypted RAR files ↗️ offers a high-level framework for future-proofing access.

🛡️ Secure Offline Toolkit for RAR5 Access
Because RAR5 hides metadata and uses intense computation per password attempt, offline tools are the only safe environment for working with sensitive RAR5 archives. Anything uploaded online risks privacy, leaks, interception, or mishandling by unknown systems.
FileBrio RAR Master provides structured workflows for:
- analyzing encrypted RAR5 archives
- checking for corruption or structural damage
- verifying archive format and header protection
- evaluating the feasibility of safe recovery attempts
For situations where metadata is limited or encrypted, learn more about RAR5’s decryption limits ↗️, which describe when strong encryption and header protection combine to make access impossible — even for legitimate owners.
________________________
FileBrio RAR Master — a secure, offline Windows toolkit for regaining access to your own password-protected RAR / WinRAR archives while keeping all data strictly on your device.
- Offline-only processing — never uploads your archives.
- Smart issue detection — password vs corruption.
- Fast recovery workflow optimized for legitimate ownership.
⬇️ Download FileBrio RAR Master
Reminder: FileBrio RAR Master is intended only for archives you own or are explicitly authorized to access. All operations run locally on your PC.
________________________
⚖️ Legal and Ethical Reminder
Always ensure the archive you are analyzing is your own or that you have explicit authorization to access it. Strong encryption is designed to preserve confidentiality — and attempting access without rights can violate privacy laws and organizational policies. Your goal should always be legitimate diagnostics, protection planning, or future-proof access to your own data, handled responsibly and ethically.
For high-level principles on appropriate handling of protected RAR files, review ethical ways to handle your encrypted RAR files ↗️.
This article is provided for general informational and educational purposes only. Any examples, scenarios, or references to password recovery, archive security, or related tools (including FileBrio RAR Master or similar software) are intended solely to help you better understand how to protect and manage your own data.
You may only apply any techniques, workflows, or tools described here to files and archives that you fully own or are explicitly and verifiably authorized to access. Attempting to bypass, remove, or recover passwords for third-party data without clear permission may violate criminal law, civil law, or internal company policies in your jurisdiction.
Nothing in this article constitutes legal advice. Laws and regulations differ between countries and organizations, and you are solely responsible for ensuring that your actions comply with all applicable legislation, contracts, and internal policies. If you are unsure whether a particular action is lawful or permitted, consult a qualified legal professional before proceeding.
🧷 Summary & Practical Next Steps
RAR5’s enhancements make it one of the strongest consumer-grade archive protection formats available today. With slower key derivation, hidden metadata, better Unicode support, and improved structural rules, RAR5 archives resist unauthorized access more effectively than older formats. But stronger defenses also mean stronger consequences for forgotten passwords, lost metadata, and damaged storage.
For legitimate users, the best approach is a balanced one: design password practices you can sustain, keep secure metadata notes, protect your archives from corruption, and use offline tools to conduct diagnostics. RAR5 gives you serious security — but it expects you to take responsibility for long-term access planning.
🔗 See Also: Learn More About RAR Protection
- How Password Protection Works Inside RAR SFX Installers ↗️
- Ethical Ways to Use Public Information When Designing Security Policies ↗️
- Why “Breaking RAR Passwords Online” Is Misleading — And Safer Local Options ↗️
- What RAR “Decryption” Really Means and How to Handle Encrypted Files Safely ↗️
- Why Removing RAR Passwords Online Is Unsafe — And Better Offline Alternatives ↗️