Why the RAR5 Key Derivation Function Matters for Security
If you created a strongly protected RAR5 archive a few years ago and now struggle to open it, you are feeling exactly what the format was designed to do: keep attackers out, even when they have powerful hardware. The same design that frustrates attackers can also frustrate you when you have legitimately lost or muddled the password.
Behind this experience sits a quiet but critical component of the format: the RAR5 key derivation function (KDF). It runs every time you type your password, invisibly transforming your text into cryptographic keys while intentionally wasting CPU and memory in the process. Done right, this makes mass guessing vastly more expensive. Done carelessly, it can leave your own data effectively unreachable if you misplace the password.
This article explains in practical terms what the RAR5 KDF does, how it differs from older designs, and what it means for legitimate users who only want to recover access to their own archives. We will also look at how responsible tools can help you estimate feasibility, avoid false hope, and design safer password habits for future RAR5 archives.
🧭 Navigation
Important
The information provided in this article applies exclusively to RAR / WinRAR archives for which you have full, demonstrable ownership or properly documented authorization. If you are not the rightful owner of the data, do not directly control it, or cannot clearly prove permission to access it, you must stop immediately. Attempting to access, recover, or modify data without explicit authorization may violate criminal law, civil statutes, corporate compliance requirements, and privacy regulations in many jurisdictions. You alone are responsible for ensuring that your actions are lawful and properly permitted before proceeding.
📌 TL;DR — RAR5 KDF in Plain Language
In simple terms: the RAR5 key derivation function (KDF) is a slow, deliberate process that takes your password and turns it into cryptographic keys. It is designed to be expensive to run many times in a row. That is good news for your privacy because it dramatically increases the effort needed to try large numbers of password guesses. But it also means that if you lose a strong password, the cost of exploring realistic alternatives can escalate quickly.
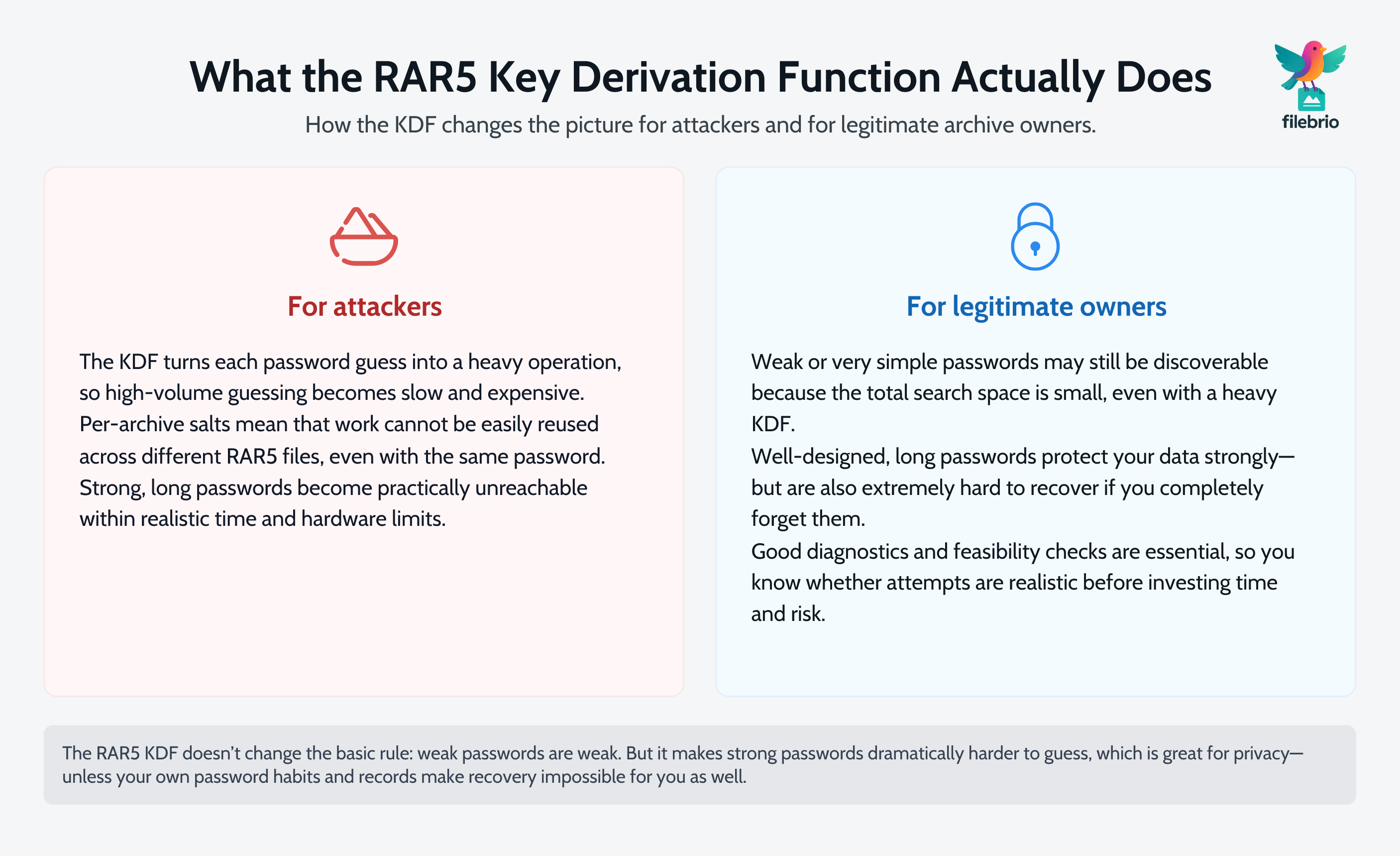
The KDF uses ingredients such as a unique salt and many repeated operations to make each password test costly. Older formats allowed many more guesses per second; RAR5 deliberately pushes this number down to make high-volume guessing far less attractive. For you as a legitimate owner, this means:
- Weak or patterned passwords may still be discovered in a reasonable timeframe because their search space is small.
- Well-designed, long passwords can become effectively unreachable once forgotten, regardless of the software or hardware you use.
- Good diagnostics become more important: you want to know if the archive is structurally healthy and whether the password problem is even worth exploring.
Responsible tools focus on analysis, feasibility estimates, and safe handling rather than promising miracles. They help you verify that the archive is really RAR5, understand how its KDF parameters influence effort, and decide whether limited, lawful attempts make sense. For future archives, the lesson is clear: combine strong passwords with safe metadata storage and backup habits so that the KDF works for you, not against you.
🔑 RAR5 Encryption and the Role of KDFs
To understand why the RAR5 KDF matters, it helps to see where it fits in the overall protection model. A modern RAR5 archive combines several layers:
- Encryption algorithms to protect the contents themselves.
- Header protection to hide filenames and structure in many cases.
- Key derivation to transform your human password into cryptographic keys.
Users often focus only on the encryption algorithm (“Is it strong?”), but in real-world attacks the KDF can be just as important. A poor key derivation step can make a strong cipher much easier to attack by allowing very fast guessing. RAR5 corrects weaknesses of older designs by deliberately making each password test expensive.
If you want a broader, high-level picture of how RAR formats handle encryption, you can later read about how RAR4 and RAR5 secure your protected data ↗️; this current article zooms in on just one (very important) component of that story.
RAR5’s KDF uses per-archive parameters and a random salt to ensure that the same password used in two different archives does not produce identical keys. This means an attacker cannot easily reuse work across multiple archives or precompute giant tables. Even if they capture many of your files, they must still work on each one individually.
From a user’s perspective, this has two main implications:
- Your password is not the key — it is a starting point for a heavy transformation that happens locally on your device.
- That transformation can be tuned so that each guess costs more CPU and memory, dramatically affecting how many guesses per second are realistic.
The combination of strong encryption and a harder KDF is one of the reasons RAR5 is often described as more robust than older archives. Articles such as how RAR5 improves protection of your encrypted files ↗️ look at the broader consequences; here we stay focused on the KDF specifically.
🧱 How the RAR5 KDF Strengthens Your Archive
In very broad terms, a key derivation function strengthens passwords by stretching them. Instead of using your password directly, it runs many internal operations and mixes in random data, so that each guess costs measurable time and energy.
RAR5’s KDF has several important properties:
- It is computationally expensive. Each password guess requires a relatively large number of internal operations.
- It is salted. Each archive stores random data that makes precomputation attacks impractical.
- Parameters can raise the cost per guess. This allows the format to remain resilient even as hardware improves.
For an attacker, the difference between “millions of guesses per second” and “thousands or fewer” is enormous. It turns many naive attack strategies into unrealistic projects. It also means that the simple intuition “just try every combination until something works” breaks down quickly once you assume a reasonably long and complex password.
However, the KDF does not magically fix weak passwords. If someone uses a very short, predictable phrase, the total search space is still small. In such cases, the KDF slows things down but may still allow all plausible candidates to be explored. The real protective power appears when users combine:
- Longer passwords that increase the number of possible combinations.
- Unpredictable structure that avoids common patterns.
- Unique passwords per archive, rather than reusing the same phrase everywhere.
The KDF multiplies the effort required for each guess. Your choices determine how many guesses are needed in total. For a deeper perspective on why length and randomness matter, see resources like how length impacts protection of your RAR password ↗️, which focus specifically on entropy and guessing complexity.
💼 All-In-One Offline Toolkit for Safer RAR5 Diagnostics
When a user realizes that a RAR5 KDF is working against them because they no longer remember the password, panic often leads to risky choices: uploading sensitive archives to unknown websites, running untrusted software, or believing unrealistic promises. None of these change the underlying cryptography, but all of them add privacy and malware risk.
FileBrio RAR Master approaches the problem from a different angle: instead of chasing “magic” solutions, it focuses on transparent diagnostics, feasibility analysis, and safe offline handling on the user’s own machine.
| Concern | How the RAR5 KDF Affects You | How FileBrio RAR Master Helps |
|---|---|---|
| Is my archive really RAR5 and strongly protected? | RAR5 adds heavier KDF use and structural changes. | Detects format version and shows key protection details. |
| Could the archive simply be damaged? | A broken file may fail even with the correct password. | Provides repair-oriented checks and corruption indicators. |
| Is it worth exploring limited password attempts? | KDF cost and password complexity determine feasibility. | Uses high-level estimates to help you gauge realistic effort. |
| Will my data leave my computer? | RAR5 protection is already local and strong. | All analysis is offline, on-device, with no uploads. |
For users who want a broader look at the application itself, the separate overview of this all-in-one RAR recovery toolkit ↗️ explains features ranging from archive diagnostics through password-handling modes, always within clearly defined legal and privacy boundaries.
At a high level, the idea is simple: use safe, offline tools to understand what the KDF and archive structure imply about your situation before you decide on any further steps.
________________________
FileBrio RAR Master — part of the FileBrio Office Suite — is a privacy-first, offline Windows toolkit for diagnosing and safely regaining access to your own password-protected RAR / WinRAR archives.
- Local processing only — nothing leaves your PC.
- Smart diagnostics to separate password issues from corruption.
- Owner-verified recovery workflows designed strictly for legitimate use.
Reminder: FileBrio RAR Master may be used only with archives you own or are explicitly authorized to access. It performs all analysis and recovery operations locally on your device, without uploading data anywhere.
________________________
🧮 KDF Cost, Performance, and Realistic Recovery Feasibility
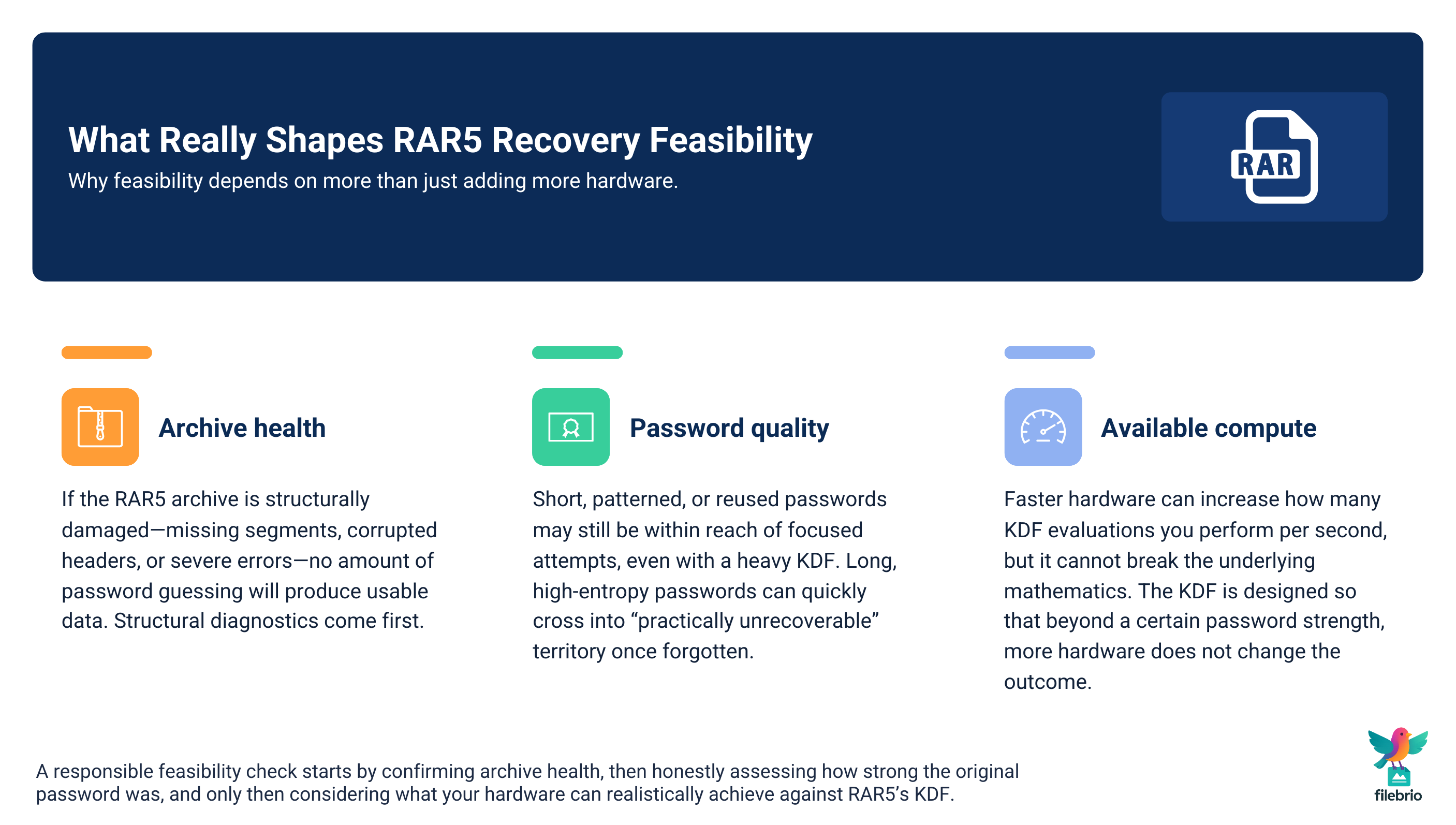
Because the RAR5 KDF is deliberately heavy, one of the most important questions a legitimate user can ask is not “How?” but “Is it even worth trying?” A responsible feasibility check considers at least three factors:
- Archive health. Is the file structurally intact, or is corruption present?
- Password quality. Was the original password weak, moderate, or truly high-entropy?
- Available computing resources. What sort of CPU or GPU is realistically available to you?
First, verifying that your archive is actually recoverable is essential. If headers are severely corrupted or segments are missing, no amount of computation will produce a usable result. Guides like how to verify recoverability of your locked RAR file ↗️ outline the kind of structural signals to pay attention to before investing effort.
Second, your own memory of the password matters. If you know that you used very simple, repeating patterns, the search space may be limited enough that exploring a structured set of possibilities could be realistic. If, on the other hand, you intentionally created a long, random passphrase with no notes, the KDF amplifies this decision into a potentially insurmountable barrier. Articles such as how to judge feasibility of your forgotten RAR password ↗️ focus on this decision-making process.
Third, hardware does matter, but in a bounded way. A more powerful system can perform more KDF evaluations per second, but it cannot bypass the underlying mathematics. This is why even high-performance recovery tools still emphasize analysis and planning over brute enthusiasm. The KDF converts raw hardware power into a slower, carefully metered stream of guesses.
Key takeaway: the RAR5 KDF exists to make mass guessing hard. If your lost password is strong enough, no realistic combination of hardware and software will change that. Understanding this early helps avoid false expectations, wasted time, and unnecessary privacy risks.
🛡️ Protection Strategies for Future RAR5 Archives
Once you understand how the RAR5 KDF works, the natural next question is: “How do I use this knowledge to avoid locking myself out in the future?” The goal is to let the KDF work for you (by slowing attackers) without creating impossible situations for your future self.
Several practical strategies help achieve that balance:
- Choose strong, structured passwords that you can still describe to yourself. Overly random strings you never document may be mathematically excellent but practically unusable if you forget them.
- Maintain a private record of hints and context. You do not need to store the password itself, but clues about its construction can be invaluable years later.
- Standardize your personal rules. If you always follow a certain pattern, you can later reason about it rather than guessing blindly.
Resources about how to reinforce protection of your encrypted RAR files ↗️ often emphasize this balance: security is not just about making things difficult; it is about designing systems that remain usable.
Safe metadata handling is equally important. If you never record anything about how the password was created, you rely entirely on memory. Over long periods, memory is unreliable, especially for complex strings. That is why separate guidance on how to organize metadata for your RAR passwords safely ↗️ treats secure notes, password managers, and offline records as essential companions to strong encryption.
Finally, password strength itself still matters even with a heavy KDF. The function multiplies effort per guess, but if the total space of possible passwords remains small, the result may still be reachable. Revisiting concepts like how length impacts protection of your RAR password ↗️ can help calibrate your intuition about what “strong enough” really means in practice.

🔒 Secure Offline Solution for Legitimate RAR5 Recovery
When you own the archive and are trying to make responsible decisions, you need tools that respect both the mathematics and your privacy. Uploading an encrypted archive to an unknown website does not change the KDF; it only exposes your confidential data to third parties.
FileBrio RAR Master focuses on a privacy-first workflow:
- All operations are local. Your RAR files stay on your own machine; nothing is sent to remote servers.
- Diagnostics-first approach. The application helps you understand whether the archive is healthy, which format it uses, and what the protection level implies.
- Feasibility-oriented recovery modes. Instead of promising unrealistic outcomes, it uses time estimates and structural checks to help you decide whether limited attempts are sensible.
- Clear documentation and legal framing. Policies and help materials emphasize working only with archives you own and treating sensitive data carefully.
If you want to compare this offline, privacy-first approach with riskier options, the dedicated comparison of offline vs online RAR recovery ↗️ explains why on-device tools are generally safer for confidential archives.
From there, you can explore editions and licensing that fit your needs. Whether you are a single user or part of a team, you can review software cost and editions ↗️ and then get FileBrio RAR Master on your PC ↗️ to keep both diagnosis and legitimate recovery workflows fully offline.
________________________
FileBrio RAR Master — a secure, offline Windows toolkit for regaining access to your own password-protected RAR / WinRAR archives while keeping all data strictly on your device.
- Offline-only processing — never uploads your archives.
- Smart issue detection — password vs corruption.
- Fast recovery workflow optimized for legitimate ownership.
⬇️ Download FileBrio RAR Master
Reminder: FileBrio RAR Master is intended only for archives you own or are explicitly authorized to access. All operations run locally on your PC.
________________________
⚖️ Legal Reminder
Even with a strong understanding of the RAR5 KDF, it is essential to stay within legal and ethical boundaries. The same mathematical tools that protect your confidential archives also protect other people’s data. Any analysis, diagnostics, or recovery attempts must be limited strictly to archives you own or are clearly authorized to manage.
If you ever need to demonstrate that you acted responsibly, well-documented procedures, internal approvals (in business settings), and adherence to software license terms are important. For FileBrio tools specifically, you can review the published responsible recovery guidelines ↗️ and contact channels for support and compliance questions.
This article is provided for general informational and educational purposes only. Any examples, scenarios, or references to password recovery, archive security, or related tools (including FileBrio RAR Master or similar software) are intended solely to help you better understand how to protect and manage your own data.
You may only apply any techniques, workflows, or tools described here to files and archives that you fully own or are explicitly and verifiably authorized to access. Attempting to bypass, remove, or recover passwords for third-party data without clear permission may violate criminal law, civil law, or internal company policies in your jurisdiction.
Nothing in this article constitutes legal advice. Laws and regulations differ between countries and organizations, and you are solely responsible for ensuring that your actions comply with all applicable legislation, contracts, and internal policies. If you are unsure whether a particular action is lawful or permitted, consult a qualified legal professional before proceeding.