Why Old RAR4 Archives Still Matter — and When to Convert Them
You may have years or even decades of history locked inside old RAR4 archives: accounting exports, project snapshots, legal case files, photo collections, or legacy software bundles. They still open, so it is tempting to ignore them — until a system upgrade, storage failure, or forgotten password suddenly makes one of those archives mission-critical. At that point, the format choice you made years ago becomes very real.
Modern RAR5 brings stronger security and more powerful recovery features, but migration is not just a matter of “recompress everything and move on.” Some archives must stay compatible with older systems; others are so fragile that unnecessary recompression could increase risk. This article helps you draw that line: where RAR4 is still good enough, and where the safer, modern RAR5 format is worth the effort.
We’ll walk through how RAR4 and RAR5 differ, how to assess your existing archive set, and how to plan a conversion strategy that respects privacy, legal requirements, and long-term access. You’ll also see how an offline, policy-aligned toolkit can give you confidence when dealing with large amounts of sensitive legacy data — without ever sending those archives to untrusted online services.
🧭 Navigation
Important
The information provided in this article applies exclusively to RAR / WinRAR archives for which you have full, demonstrable ownership or properly documented authorization. If you are not the rightful owner of the data, do not directly control it, or cannot clearly prove permission to access it, you must stop immediately. Attempting to access, recover, or modify data without explicit authorization may violate criminal law, civil statutes, corporate compliance requirements, and privacy regulations in many jurisdictions. You alone are responsible for ensuring that your actions are lawful and properly permitted before proceeding.
📌 TL;DR — RAR4 vs RAR5 And When Conversion Makes Sense
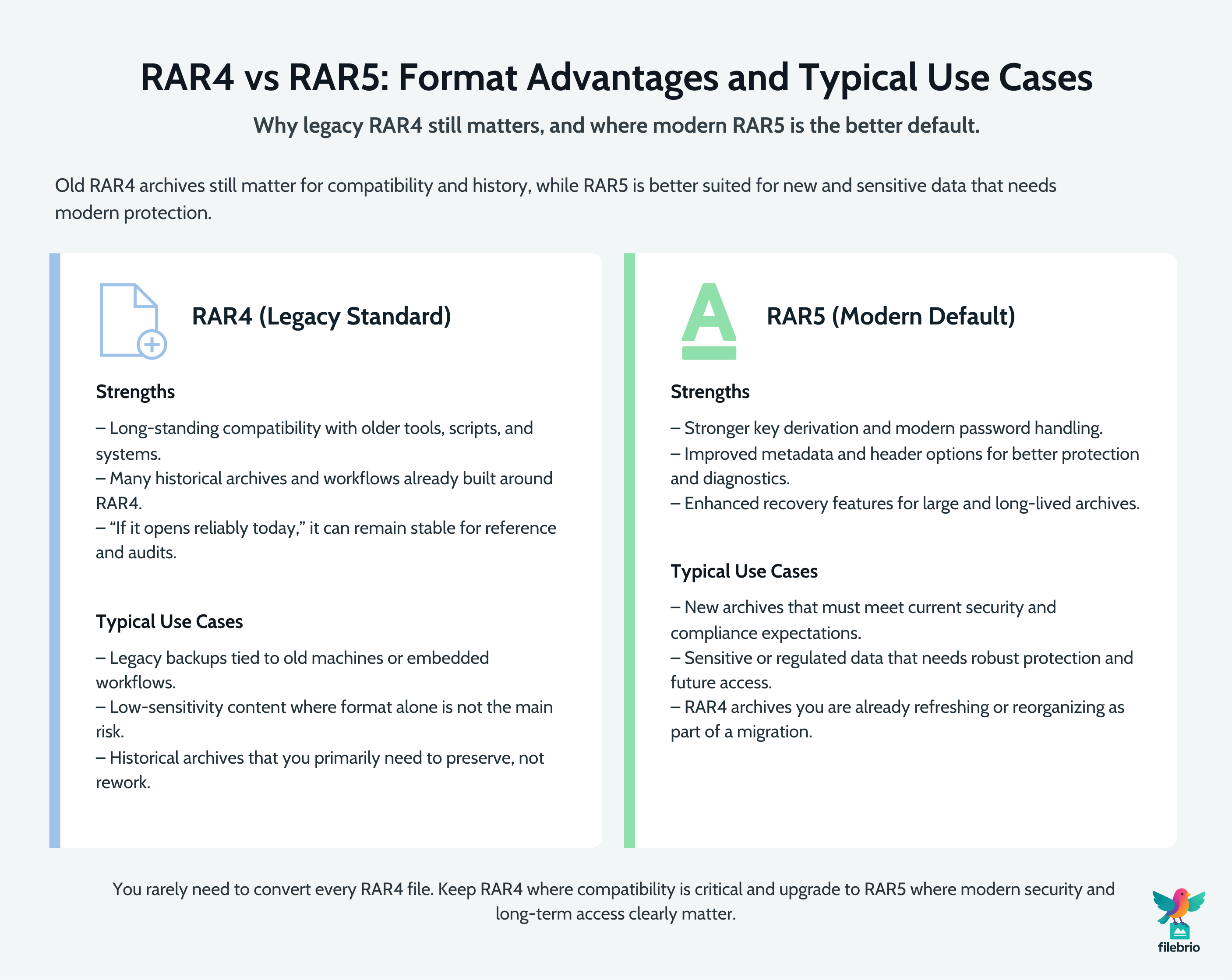
RAR4 is an older archive format that many people still rely on because it “just works” on long-lived systems and with older tools. It remains relevant for compatibility and historical continuity — especially in environments where legacy machines, scripts, or workflows still expect RAR4 archives. However, newer RAR5 brings improved encryption design, stronger key derivation, better metadata handling, and richer recovery features, which can significantly improve both security and diagnostics for sensitive data.
In practice, you rarely need to convert every RAR4 file you have. Instead, prioritize archives that are (1) actively used, (2) contain sensitive data, or (3) are critical for long-term retention. For these, consider re-creating or migrating them as RAR5 with modern options, while keeping a verified backup of the original RAR4 until you are confident nothing was lost. For very old or fragile archives on risky storage, your first priority is to preserve and validate them, then think about format upgrades later.
Safe migration should be done with offline, privacy-first tools, following a written plan that covers ownership, integrity checks, storage destinations, and password strategy. You should avoid uploading old archives to online “converters” or “unlockers” just because they promise convenience. Ultimately, RAR5 becomes part of a broader strategy: strengthen protection for important data, keep archives usable for the future, and retire RAR4 gradually where it no longer serves a clear requirement.
🧠 Why Old RAR4 Archives Still Matter Today
RAR4 is not just a historic curiosity. In many organizations, it still underpins the only copies of certain data sets. Long-running teams have archives from ten or fifteen years ago that were created when RAR4 was the default, and those archives may be referenced during audits, legal disputes, or financial investigations. In that sense, RAR4 is a living part of your information history.
From a security perspective, old RAR4 archives also illustrate how past decisions affect current risk. If those archives use weak passwords or outdated practices, they may be easier to attack than modern ones; if they rely on forgotten settings, they may be hard to open even by legitimate owners. Understanding this security and longevity picture is easier once you know how RAR4 and RAR5 secure your protected data ↗️ at a high level, including the role of encryption modes and key derivation functions.
Finally, RAR4 archives are often intertwined with legacy scripts, backup processes, and restore procedures. Before you “retire” them, you need to check what else depends on that format. In some cases, it is safer to introduce RAR5 alongside RAR4 for new data while letting existing historical archives stay as they are — at least until you have a mature migration and verification plan.
🧬 Technical Differences Between RAR4 And RAR5
To decide when conversion is worthwhile, you need a conceptual understanding of how RAR4 and RAR5 differ. Both use strong encryption when configured correctly, but RAR5 introduces design improvements that tighten protection and enhance diagnostics. These improvements are discussed more broadly in resources about how RAR5 improves protection of your encrypted files ↗️.
At a high level, some important differences include:
- Key derivation and password handling. RAR5 uses a more modern and robust key derivation approach, which better resists high-speed guessing attempts and aligns with contemporary expectations around password-hardening functions.
- Metadata and header options. RAR5 gives more control over what is encrypted and how headers behave, affecting how much information is visible before password entry and how diagnostics can be performed.
- Recovery features. Built-in features like quick open records and improved recovery blocks are described in explanations of what RAR5 quick open records and recovery blocks do ↗️. These make it easier to open and repair archives efficiently while still preserving security.
In short, RAR5 is designed for a world where both attack capabilities and data protection needs have evolved. RAR4 is not automatically unsafe, but it belongs to an earlier generation. Your policies should reflect this: treat RAR5 as your modern standard for new or migrated sensitive archives, while respecting RAR4 where compatibility insists.
🔍 How To Assess Your Existing RAR4 Archive Collection
Before converting anything, you need a clear picture of what you already have. Many organizations discover that their RAR4 archive landscape is larger and more diverse than expected, spanning personal backups, project exports, and ad-hoc “zip-and-send” archives created under deadline pressure.
A structured assessment typically considers:
- Age and origin. How old is the archive, and which team or project created it?
- Content criticality. Does it contain sensitive personal data, financial records, or unique historical information?
- Current accessibility. Can someone still open it today, or is the password already at risk of being lost?
- Storage environment. Is the archive sitting on fragile media, such as aging USB drives or unverified cloud backups?
For technical feasibility, it’s useful to connect your assessment with how file-type structure affects RAR diagnostics and feasibility analysis ↗️. Understanding what kinds of files are inside each archive can influence how much effort you should spend on preservation and conversion, especially if reconstruction would be difficult or impossible if something went wrong.
Assessment is also the moment to prioritize backup and integrity checks on the most fragile RAR4 archives. Before you even consider re-archiving, adopt practices from ways to prevent losing your RAR data on storage devices ↗️: verify copies, store them on reliable media, and ensure you are working from a known-good snapshot, not the only existing instance.

🧰 All-In-One Solution For Mixed RAR4/RAR5 Environments
Managing a mix of old RAR4 and new RAR5 archives is easier when you have a single, trusted toolkit that understands both formats and can operate entirely offline. Without that, people may experiment with random utilities or online “converters,” risking data leakage, inconsistent settings, or even corruption of irreplaceable legacy archives.
By standardizing on a dedicated suite like FileBrio RAR Master features ↗️, you can create a workflow where:
- RAR4 and RAR5 archives are detected and handled consistently.
- Users can analyze structure and metadata before making changes.
- Conversion and repair operations are performed locally, following your own policies.
If older archives show signs of damage, you can also rely on capabilities similar to those described in repair damaged RAR archives ↗️ to diagnose and fix issues before any attempt at migration. At the same time, you retain full control over where archives reside and who is allowed to touch them, instead of sending them to unvetted online services.
When you want to deploy this unified environment across your organization, your IT team can get the FileBrio Office Suite installer ↗️ from the official distribution page and roll it out via your usual management tools, ensuring everyone works with the same audited binaries.
________________________
FileBrio RAR Master — part of the FileBrio Office Suite — is a privacy-first, offline Windows toolkit for diagnosing and safely regaining access to your own password-protected RAR / WinRAR archives.
- Local processing only — nothing leaves your PC.
- Smart diagnostics to separate password issues from corruption.
- Owner-verified recovery workflows designed strictly for legitimate use.
Reminder: FileBrio RAR Master may be used only with archives you own or are explicitly authorized to access. It performs all analysis and recovery operations locally on your device, without uploading data anywhere.
________________________
🔄 When It Makes Sense To Convert RAR4 To RAR5
You don’t need — and often shouldn’t try — to convert every RAR4 archive in existence. Instead, focus on cases where a format upgrade delivers clear benefits with manageable risk. In many environments, conversion is most compelling when it is part of a larger effort to strengthen RAR archive security while preserving future access ↗️.
Common triggers for conversion include:
- Sensitive data under modern regulations. Archives that contain regulated personal data or confidential business information may warrant RAR5’s stronger key derivation and header options.
- Active, long-lived projects. If a project will continue for many years, moving its archives to RAR5 now can simplify future tooling and security reviews.
- Planned infrastructure upgrades. When you are updating backup systems or replacing legacy machines, it’s efficient to upgrade archive formats at the same time.
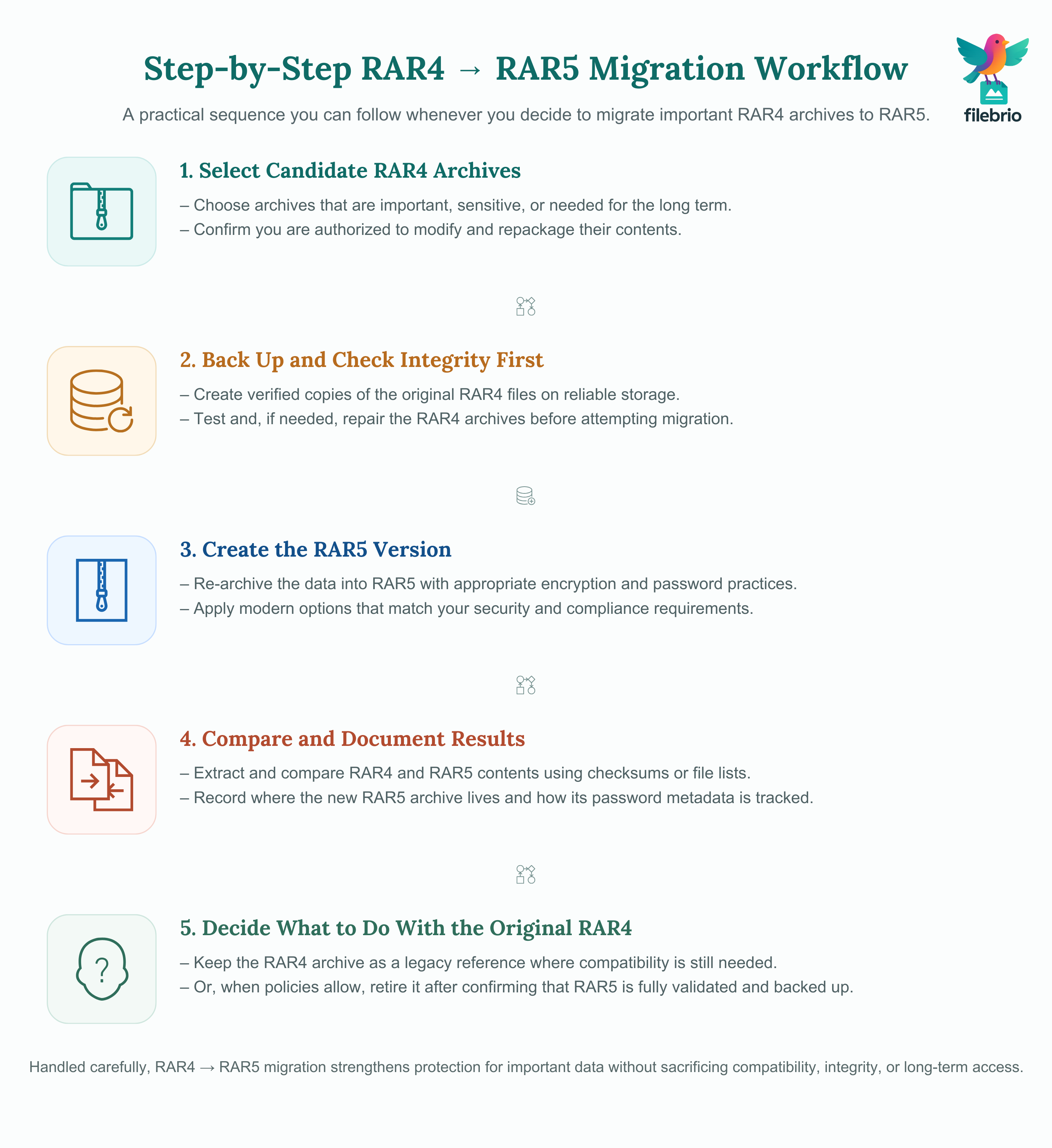
You may also find it easier to adopt RAR5 where you already plan to modernize formats, as discussed in how to safely convert your old RAR files to RAR5 ↗️. The key is to combine format migration with a clear process: verify ownership, confirm integrity, create a RAR5 version, then validate that the contents match before deciding what to do with the original RAR4 file.
🧊 When You Should Keep RAR4 As-Is (At Least For Now)
There are also situations where leaving RAR4 untouched is the safer or more practical choice. Not every archive benefits enough from RAR5’s improvements to justify the effort and risk of migration.
You may decide to keep RAR4 in cases like:
- Strict compatibility requirements. Some legacy systems or embedded workflows only understand RAR4, and adapting them would be expensive or risky.
- Low-sensitivity content. Archives that only contain materials already public or easily reproducible may not justify conversion work.
- Fragile or barely readable media. If you are dealing with near-failing drives, your priority is safe copying and verification, not recompression.
Where you do keep RAR4, focus on preservation and documentation. Ensure you have good backups, clear records of the passwords, and an understanding of who is responsible for long-term access. Planning for that continuity is easier with frameworks like how to maintain long-term access to encrypted RAR archives (teams & enterprises) ↗️, which emphasize ownership, shared metadata, and well-defined handover processes.
🛡️ Secure Offline Solution For Migrating Sensitive Archives
When you do choose to migrate, you want to be confident that the process itself does not expose your data. Uploading old, sensitive RAR4 archives to online “converter” sites is usually incompatible with privacy and compliance obligations. Instead, all handling — inspection, recompression, verification — should happen on offline or well-controlled systems.
A privacy-first toolkit helps you implement your migration plan in a way that aligns with your internal and external obligations. When you compare local tools with cloud-based alternatives, consider the insights from offline vs online RAR recovery ↗️: local operations keep sensitive material within your security boundary and under your logging, monitoring, and incident response framework.
At the same time, make sure your migration strategy respects the technical limits of the format. Some archives — especially those with encrypted headers or edge-case settings — may be difficult or impossible to re-create perfectly. A high-level overview such as encrypted header warning ↗️ can help set expectations and highlight cases where RAR5 migration may not remove underlying feasibility constraints.
________________________
FileBrio RAR Master — a secure, offline Windows toolkit for regaining access to your own password-protected RAR / WinRAR archives while keeping all data strictly on your device.
- Offline-only processing — never uploads your archives.
- Smart issue detection — password vs corruption.
- Fast recovery workflow optimized for legitimate ownership.
⬇️ Download FileBrio RAR Master
Reminder: FileBrio RAR Master is intended only for archives you own or are explicitly authorized to access. All operations run locally on your PC.
________________________
✅ Practical Checklist For Safe RAR4 → RAR5 Migration
To turn concepts into action, it helps to adopt a simple checklist that covers the entire lifecycle of a migration attempt. While every environment is different, a typical workflow might look like this:
- Identify candidate archives. Select RAR4 archives that are both important and likely to benefit from RAR5 features.
- Verify ownership and authorization. Confirm you are dealing with archives you legitimately own and are allowed to modify.
- Back up the original archives. Create verified copies on reliable storage before doing anything else, as recommended in how to protect your RAR files on USB and HDD ↗️.
- Check integrity first. Use your toolkit to test and, if needed, repair the RAR4 archive before attempting conversion; avoid migrating corrupted data.
- Create a RAR5 version. Re-archive or convert the data into a new RAR5 file with appropriate encryption and password practices.
- Compare contents. Extract both versions in a controlled environment and verify that files, sizes, and checksums match.
- Document the result. Record where the new RAR5 archive is stored, who owns it, and how its password is tracked.
For very high-value archives, you may also want to estimate the realistic effort involved in recovering their passwords if they were lost in the future. Educational tools like the RAR password strength estimator ↗️ can offer high-level timing projections so you can calibrate your expectations and design your retention strategy accordingly.
📦 Long-Term Strategy For Legacy Archives And Storage
RAR4 vs RAR5 is just one dimension of your long-term archive strategy. Ultimately, the goal is to ensure that data you must keep remains both secure and accessible over time, regardless of format. That involves thoughtful storage choices, documentation, and periodic review.
As you plan for the future, combine format decisions with broader good practices for storage, integrity, and password management. This includes:
- Using reliable storage media and redundancy, so a failing drive doesn’t destroy your only copy.
- Documenting which archives remain in RAR4 for compatibility reasons and which have been upgraded.
- Ensuring that at least one current toolset in your environment understands both formats and is likely to still run on future systems.
Your policies should treat legacy archives as part of the same overall security posture as newer ones, not as forgotten leftovers. If you consistently monitor the health of your archive set, apply format upgrades where they add real value, and keep everything under an offline, well-governed toolkit, you can let RAR4 and RAR5 coexist without surprises — and transition away from RAR4 on your own timeline rather than in a crisis.
⚖️ Legal Reminder
This article is provided for general informational and educational purposes only. Any examples, scenarios, or references to password recovery, archive security, or related tools (including FileBrio RAR Master or similar software) are intended solely to help you better understand how to protect and manage your own data.
You may only apply any techniques, workflows, or tools described here to files and archives that you fully own or are explicitly and verifiably authorized to access. Attempting to bypass, remove, or recover passwords for third-party data without clear permission may violate criminal law, civil law, or internal company policies in your jurisdiction.
Nothing in this article constitutes legal advice. Laws and regulations differ between countries and organizations, and you are solely responsible for ensuring that your actions comply with all applicable legislation, contracts, and internal policies. If you are unsure whether a particular action is lawful or permitted, consult a qualified legal professional before proceeding.
📚 See Also
- RAR Recovery Records And .rev Volumes: How They Help Protect And Restore Data ↗️
- Understanding Multi-Volume RAR Archives: Password Behavior And Repair Options ↗️
- How To Reconstruct Missing Parts Of Multi-Volume RAR Archives ↗️
- Best Practices For Managing Large RAR Archives Safely ↗️
- How To Protect Sensitive Files While Allowing Authorized Recovery (Corporate Workflows) ↗️
- Why Some RAR Archives Become Impossible To Open — Security Explained ↗️
- Why Offline Recovery Tools Are Safer For Privacy ↗️