
How RAR Security Works and Why Passwords Can’t Be Reset Like Email Credentials
You forget a RAR password, stare at the prompt, and instinctively look for a “Forgot password?” link. There isn’t one. No support line to call, no reset email to send — just a stubborn archive that refuses to open. It can feel broken or unfair, but in reality, this behavior is exactly what strong encryption is supposed to do. Understanding why there is no reset button is the key to making sensible, safe decisions about your own data.
This article explains, in practical terms, how RAR security is designed, why no central service can simply “restore” access, and what realistic, lawful options remain when you’ve locked yourself out of an archive you legitimately own.
🧭 Navigation
⚡ TL;DR — Why RAR Passwords Can’t Be Reset
RAR and WinRAR archives are secured by local encryption, not by an online account. There is no central server, no password reset mechanism, and no support agent who can override the math. A strong RAR password is converted into an encryption key using functions designed to be expensive to guess, especially in RAR5. If the password is long and random, exhaustive guessing becomes mathematically unrealistic, no matter what tool you use. When you lose that password, your options are limited to: carefully reconstructing it from memory and context, using privacy-first offline tools to understand whether recovery is even feasible, or accepting that the archive is effectively sealed while improving your future security and documentation practices.
🧠 Why RAR Passwords Are Different from Online Accounts
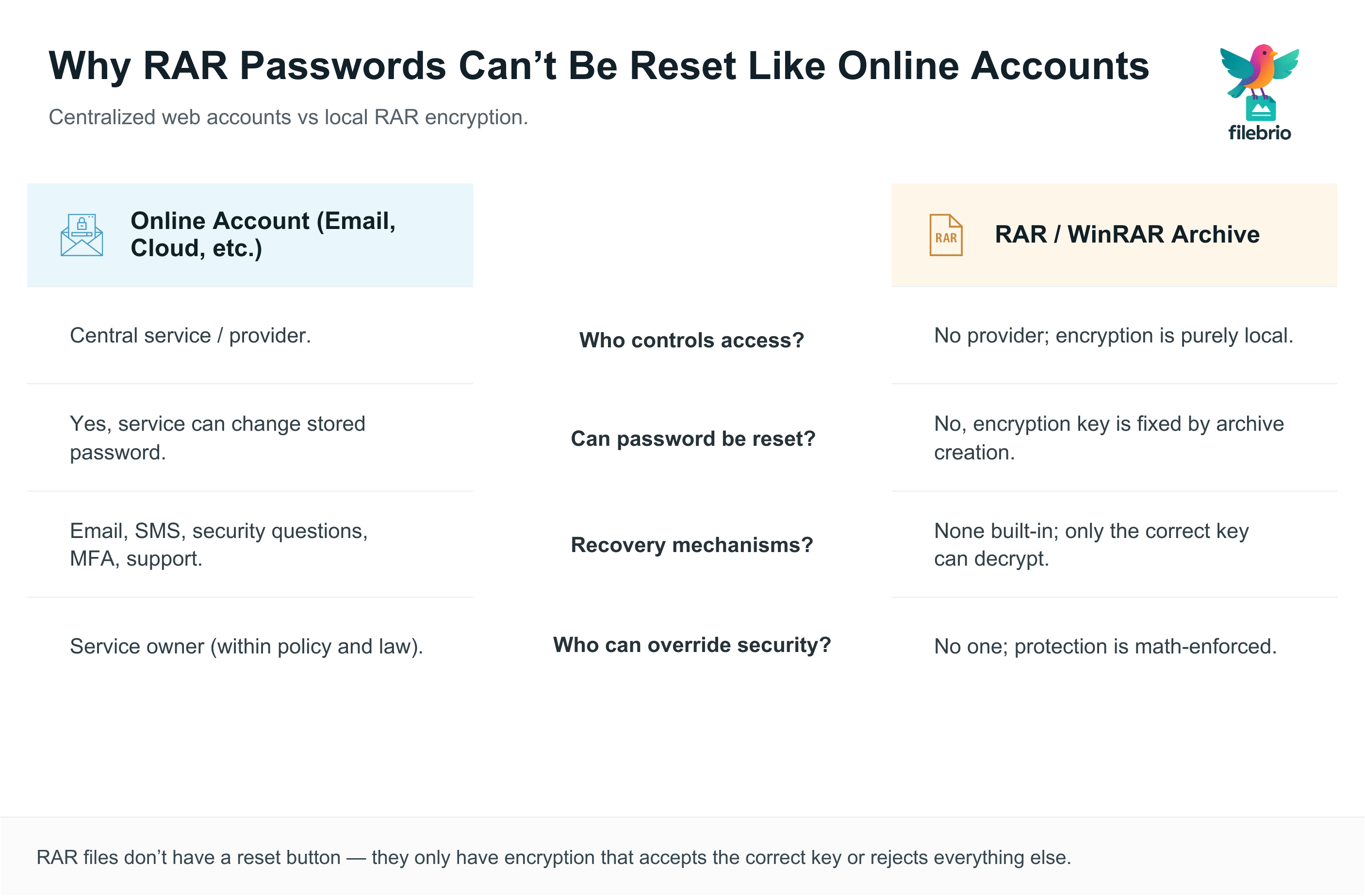
Most people are used to web accounts: you forget a password, click a link, and a reset email arrives. That workflow depends on two things:
- There is a central service that controls access to the data.
- That service can change the secret used to protect your account (the password) while still keeping the data intact.
RAR archives work differently. Once an archive is created with a password, the protection is built directly into the file itself. There is no external server or support portal that can log in and change it for you. The archive doesn’t “know” who you are — it only knows whether the decryption key produced from your password is correct.
| Aspect | Online Account (Email, Cloud, etc.) | RAR / WinRAR Archive |
|---|---|---|
| Who controls access? | Central service / provider. | No provider; encryption is purely local. |
| Can password be reset? | Yes, service can change stored password. | No, encryption key is fixed by archive creation. |
| Recovery mechanisms? | Email, SMS, security questions, MFA, support. | None built-in; only correct key can decrypt. |
| Who can override security? | Service owner (within policy and law). | No one; protection is math-enforced. |
To see how this design translates into practice, it helps to look at how encryption controls access to your protected RAR contents ↗️. Instead of a central account database, the archive uses cryptography directly: either the key is right and decryption works, or it isn’t and decryption fails.
🔐 How RAR Encryption Protects Your Data
Modern RAR formats (especially RAR5) are built to resist unauthorized access even when attackers have the archive file in their hands. At a high level:
- Your chosen password is turned into a cryptographic key using a key-derivation function (KDF).
- The archive content is encrypted using strong algorithms (such as AES-256 in RAR5).
- Optionally, file names (headers) may also be encrypted, hiding even the list of contained files.
A separate overview of how RAR4 and RAR5 secure your protected data ↗️ shows why this combination of KDF + encryption algorithm is so effective when passwords are chosen well.

The KDF itself matters greatly. RAR5 uses a more robust derivation function than older formats. Instead of simply hashing your password once, it runs it through a deliberately expensive process so that trying billions of guesses per second becomes more difficult. You can dig into this in how the RAR5 KDF strengthens your encrypted RAR file ↗️, which explains why modern archives are harder to attack with raw computing power.
🔐 Need a Safe, Offline Way to Check Whether Your Archive Is Even Recoverable?
Before taking any action with a locked RAR archive, the most important step is understanding
whether the archive is healthy, corrupted, or using encrypted headers.
Many people assume the problem is “just a forgotten password,” but modern RAR security makes several
issues look identical — wrong password alerts, empty file lists, damaged metadata, and more.
FileBrio RAR Master helps you confirm the real situation without exposing the archive to the Internet
or triggering irreversible damage.
- 🧩 Detects encrypted headers — explains why filenames may appear hidden or missing
- 📦 Checks archive structure, metadata health, and RAR4/RAR5 format differences
- 🔍 Distinguishes password issues from corruption (critical before any recovery attempt)
- 🛡️ Works entirely offline — no uploads, no privacy risk
- 📊 Ideal for personal and corporate environments where confidentiality matters
Even strong encryption behaves predictably once you know what the archive is actually doing.
Start with a safe, private diagnostic:
________________________
FileBrio RAR Master — part of the FileBrio Office Suite — is a privacy-first, offline Windows toolkit for diagnosing and safely regaining access to your own password-protected RAR / WinRAR archives.
- Local processing only — nothing leaves your PC.
- Smart diagnostics to separate password issues from corruption.
- Owner-verified recovery workflows designed strictly for legitimate use.
Reminder: FileBrio RAR Master may be used only with archives you own or are explicitly authorized to access. It performs all analysis and recovery operations locally on your device, without uploading data anywhere.
________________________
📧 Why There Is No “Reset My RAR Password” Button
Once you understand the basics of RAR encryption, the lack of a reset feature makes sense. There is nowhere to send a reset link, and no “master key” that can be swapped out from the outside. The archive is a sealed mathematical object: change the password or key, and you change what contents the decryption produces.
| Scenario | What a Web Service Does | What a RAR Archive Can Do |
|---|---|---|
| Forgotten password | Service marks old password invalid, sets a new one after verifying identity. | Archive has no identity concept; it only knows valid/invalid decryption. |
| Support request | Operator may reset or grant access under policy. | No operator exists; file is just encrypted data. |
| Compromised account | Service can lock account, revoke sessions. | Archive cannot be “locked” or “unlocked” externally. |
If the password is weak or predictable, it may still be recovered by sophisticated guessing or by using your own memory patterns. But that is a function of password quality, not of some built-in reset channel. When the password is long and random, the protection can reach a point where even legitimate owners must accept that recovery is no longer realistic. This is discussed in how length impacts protection of your RAR password ↗️, which introduces the idea of entropy (unpredictability) as a key factor.
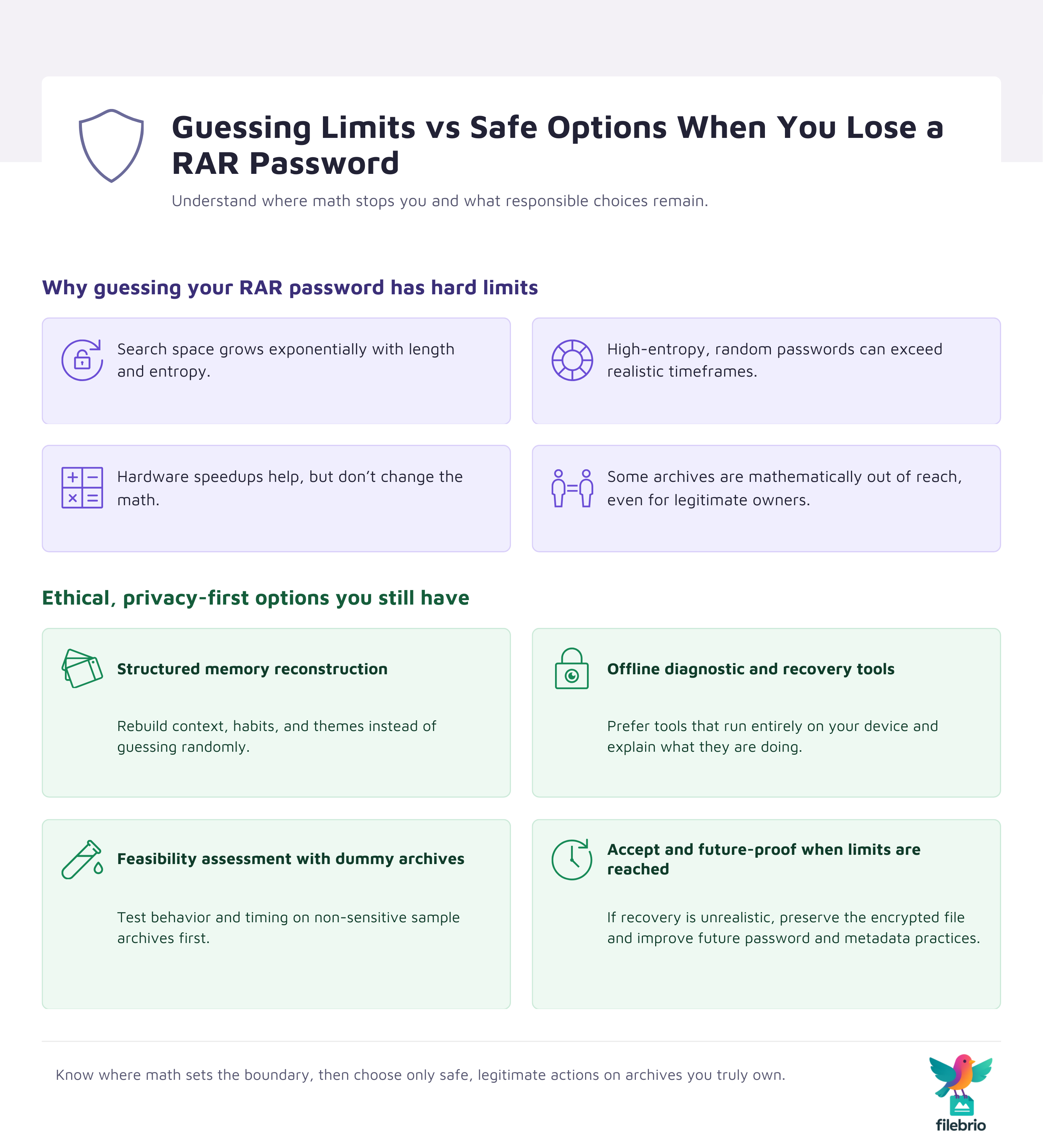
⏱️ High-Level Limits of Password Guessing
Because there is no reset mechanism, people often turn to password guessing. It’s important to approach this with realistic expectations. The core questions are:
- How large is the space of possible passwords that fit your habits?
- How quickly can those possibilities be tested in practice?
- How much time, hardware, and electricity are you realistically willing to invest?
A high-level, non-technical introduction to these trade-offs is given in how to interpret timing estimates for your RAR password ↗️. It explains why even huge speed improvements do not magically make very large search spaces manageable.
The key insight is that password security scales exponentially with length and complexity. Moving from, say, 8 characters of limited variety to 14 characters drawn from a large set can push the required effort from “doable” into “effectively impossible within a human lifetime.” The article on why entropy matters for your encrypted RAR file ↗️ provides examples of how small changes in your choices dramatically change guessing complexity.
For owners of locked archives, this means that some situations are genuinely hopeless from a mathematical perspective. Recognizing that boundary early prevents wasted time and reduces the temptation to send sensitive archives to untrusted online services claiming miraculous results.
🛠️ A Secure, Offline Path for Diagnosing Locked RAR Archives
When you realize there is no password reset button for RAR files, the next step is choosing the
safest and most realistic workflow.
Blind guessing wastes time; uploading the archive to unknown online “unlockers” puts your data at risk.
What you need instead is a controlled, offline diagnostic path that keeps your files private while providing
clarity on feasibility.
FileBrio RAR Master gives you that environment:
- 🔒 100% offline — ideal for sensitive, personal, or regulated archives
- 🧠 Helps you evaluate whether your password style makes recovery possible
- 📂 Analyzes structure to rule out corruption before you invest effort
- 📁 Supports RAR4 and RAR5 with accurate encrypted-header handling
- 🧭 A safe first step before attempting memory-based reconstruction
| Your Situation | What FileBrio Helps You Determine |
|---|---|
| Archive shows “wrong password” | Password issue vs corrupted data block |
| No filenames visible | Encrypted headers vs malformed metadata |
| Unsure if recovery is worth attempting | Feasibility assessment based on structure + password style |
If you’re deciding your next step, begin with safe diagnostics that respect privacy and ensure you’re operating
within technical and legal boundaries:
________________________
FileBrio RAR Master — a secure, offline Windows toolkit for regaining access to your own password-protected RAR / WinRAR archives while keeping all data strictly on your device.
- Offline-only processing — never uploads your archives.
- Smart issue detection — password vs corruption.
- Fast recovery workflow optimized for legitimate ownership.
⬇️ Download FileBrio RAR Master
Reminder: FileBrio RAR Master is intended only for archives you own or are explicitly authorized to access. All operations run locally on your PC.
________________________
🛡️ Legitimate and Safe Options When You’ve Lost Access
If you legitimately own or administer a RAR archive and can no longer recall the password, your options fall into a few ethical, privacy-respecting categories:
- Structured memory reconstruction. Rebuild the context around how and when you created the archive. A separate guide explores how to design strong memorable RAR passwords ↗️, which also helps you understand your own style and patterns.
- Careful use of offline diagnostic and recovery tools. Prefer software that operates entirely on your local machine and explains what it is doing. See why offline tools keep your encrypted RAR data private ↗️ for a deeper discussion of the privacy advantages.
- Feasibility assessment before serious effort. Test your situation with non-sensitive sample archives to understand how RAR protection behaves. Guidance on how to test RAR protection with your dummy files ↗️ can help you calibrate expectations before touching irreplaceable data.
All of these actions must stay within the boundaries of access to data you truly own or are authorized to manage. If you are dealing with shared, corporate, or client archives, you should also ensure your planned actions align with organizational policy and law — more on this below.
📂 Designing RAR Security That Stays Accessible
The harshness of “no reset” is also an opportunity to design better practices going forward. Good RAR security should:
- Be strong enough to protect against unauthorized access.
- Remain usable for you (and authorized collaborators) years later.
- Survive hardware changes, staff turnover, and software updates.
That balance is explored in how to strengthen RAR archive security while preserving future access ↗️. It discusses strategies like combining high-entropy passphrases with carefully stored hints and metadata.
On the personal side, it often helps to maintain structured notes about how your passwords are formed — without writing down the exact secrets. An example is how to organize metadata for your RAR passwords safely ↗️, which explains how you can preserve enough context for future you to reconstruct the right idea, without leaving a plain-text password lying around.
⚖️ Legal and Ethical Boundaries Around Access
Because RAR security is purely file-based, there is nothing in the archive itself that distinguishes legitimate from illegitimate attempts. That distinction comes from context: ownership, contracts, and policy. This is why organizations and individuals must think about the legal side of any recovery attempt.
A good starting point is legal factors when accessing your encrypted RAR files ↗️, which outlines why proper documentation of authority and intent is important if anyone else — such as a third-party specialist — becomes involved.
In high-stakes environments (corporate, legal, regulatory), this often goes hand in hand with formal processes, approvals, and audit trails. Even though this article focuses on technical security, those non-technical controls are just as important for ensuring that strong encryption serves its intended purpose: protecting the right people, in the right ways.
📜 Legal Reminder
This article is provided for general informational and educational purposes only. Any examples, scenarios, or references to password recovery, archive security, or related tools (including FileBrio RAR Master or similar software) are intended solely to help you better understand how to protect and manage your own data.
You may only apply any techniques, workflows, or tools described here to files and archives that you fully own or are explicitly and verifiably authorized to access. Attempting to bypass, remove, or recover passwords for third-party data without clear permission may violate criminal law, civil law, or internal company policies in your jurisdiction.
Nothing in this article constitutes legal advice. Laws and regulations differ between countries and organizations, and you are solely responsible for ensuring that your actions comply with all applicable legislation, contracts, and internal policies. If you are unsure whether a particular action is lawful or permitted, consult a qualified legal professional before proceeding.
🔗 See Also — Related Guides
- How RAR Security Works and Why Passwords Can’t Be Reset Like Email Credentials ↗️
- Why Some RAR Archives Become Impossible to Open — Security Explained ↗️
- Brute-Forcing a RAR/WinRAR Password? Legal Boundaries, Practical Limits, and Safe Use Cases ↗️
- Free RAR/WinRAR Password Recovery Tools: Safe, Offline Options for Accessing Your Own Files ↗️
- How to Ensure You’re Recovering Only RAR Files You Own ↗️