Understanding Password Encodings in RAR Archives (Unicode, Cyrillic, etc.)
Passwords in RAR archives don’t behave like ordinary text — especially when multiple scripts, keyboard layouts, or older system locales are involved. A password that looks the same on screen may translate into very different underlying bytes depending on whether it was typed using Unicode, Cyrillic code pages, legacy ANSI encodings, or mixed layouts. Those differences directly affect the cryptographic key that protects the archive, and even small encoding mismatches can make a perfectly remembered password fail.
This guide breaks down how RAR interprets characters across languages and platforms, why visually identical passwords may not be equivalent internally, and how to recognize when encoding — not corruption or user error — is the real reason an archive won’t open. You’ll also find practical, responsible guidance for working with your own multi-script archives, designing future-proof passwords, and keeping everything fully offline using tools that respect privacy and compliance requirements.
🧭 Navigation
Important
The information provided in this article applies exclusively to RAR / WinRAR archives for which you have full, demonstrable ownership or properly documented authorization. If you are not the rightful owner of the data, do not directly control it, or cannot clearly prove permission to access it, you must stop immediately. Attempting to access, recover, or modify data without explicit authorization may violate criminal law, civil statutes, corporate compliance requirements, and privacy regulations in many jurisdictions. You alone are responsible for ensuring that your actions are lawful and properly permitted before proceeding.
⚡ TL;DR — Quick Summary
RAR archives do not store your password directly; they derive a cryptographic key from what you type, and that process depends on how characters are encoded (for example, older ANSI code pages vs modern Unicode). If you created a password using one keyboard layout or system locale (say, Russian Windows using Cyrillic), and later try to open the archive on a system using a different encoding or layout, the bytes fed into the key-derivation function can change — which makes the “same” visual password fail.
This article explains, at a high level, how RAR handles password encodings, why Unicode and multi-script passwords behave differently across systems, how to recognize when encoding is the real issue, and what safe, lawful steps you can take to analyze and protect your own archives without exposing data or using online tools.
🧠 How RAR Password Encodings Actually Work
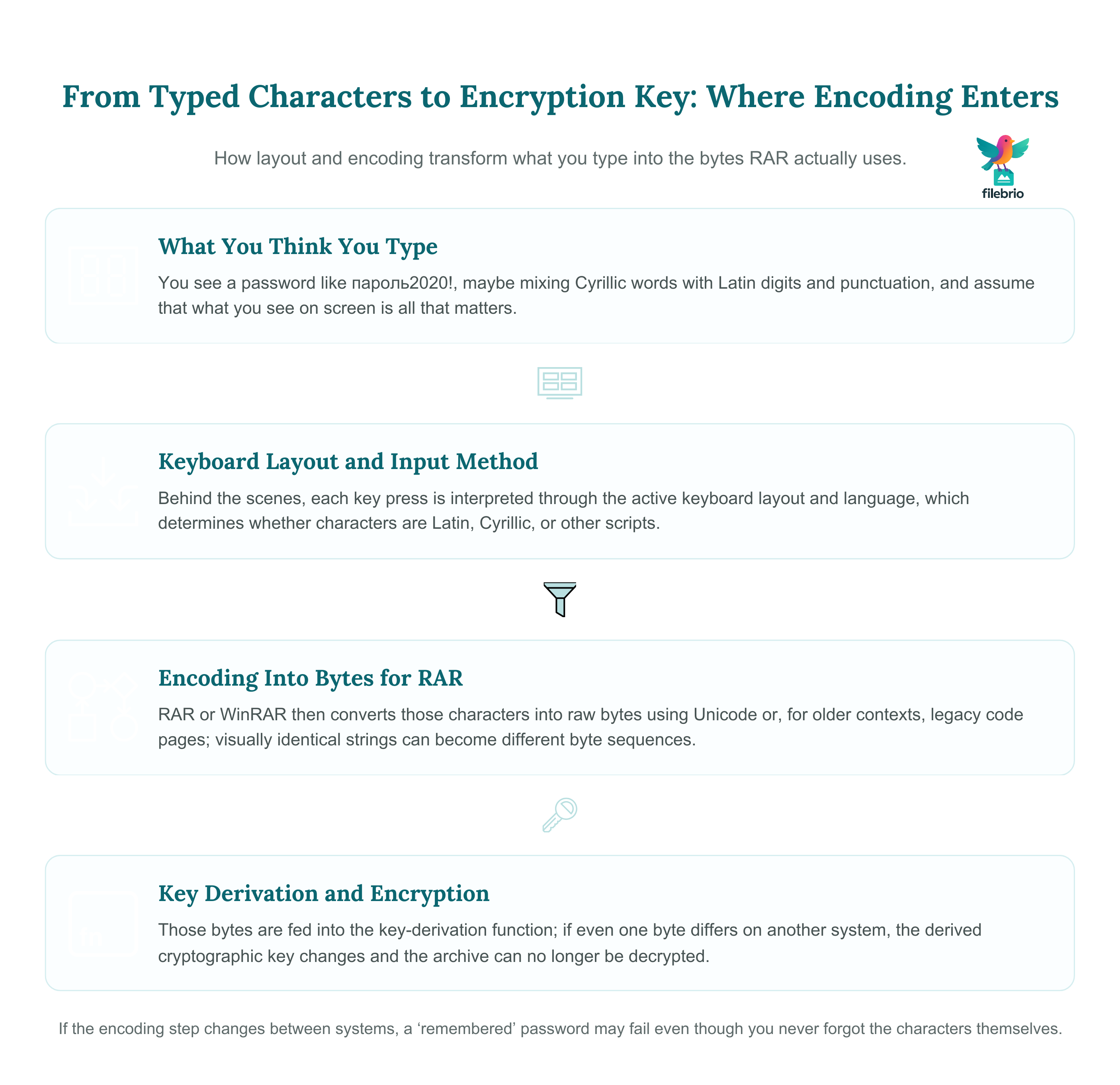
When you protect a RAR or WinRAR archive with a password, the archive does not simply “remember” the characters you typed. Instead, the password string is converted into bytes using a specific encoding, then passed through a key-derivation function to generate the cryptographic key that protects your data. If the same visual characters produce different bytes on another system, the resulting key will not match, and decryption fails.
To understand encoding behavior, it helps to keep three conceptual layers in mind:
- Characters you see — for example, пароль2020! or пароль mixed with Latin digits.
- Keyboard and layout — which keys you pressed and which layout (English, Russian, Bulgarian, etc.) was active at the time.
- Underlying encoding — how the application converts those characters into bytes before key derivation.
Modern RAR versions rely heavily on Unicode, but older environments and compatibility layers may still use legacy code pages. That means two visually identical passwords may map to different bytes depending on how they were entered, which language layout was active, and which version of the software was used.
If you need a more general conceptual background on how encryption and key derivation protect archives, it can be helpful to review how RAR4 and RAR5 protect your data conceptually, such as in resources about how RAR4 and RAR5 secure your protected data ↗️. Understanding that foundation makes encoding issues easier to reason about.
RAR4 vs RAR5: Why Encoding Matters More Over Time
RAR5 introduced modernized structures and a stronger key-derivation function. That improved security, but it also made the relationship between password bytes and the final key even more important. If encoding changes the bytes, the derived key is different and the archive remains inaccessible, even though you “remember” the characters correctly.
Security-focused changes like stronger derivation functions and higher iteration counts are discussed in more detail in guides about long-term security and future access. Understanding these principles helps you see why a password that once worked flawlessly can suddenly fail when you migrate to a new computer or operating system.
Encoding vs Entropy: Two Different Concerns
It is easy to mix two separate topics:
- Encoding — how characters are turned into bytes.
- Entropy and complexity — how hard it is, in principle, to guess the password.
Encoding issues can make any password fail, even one with excellent entropy. Complexity is discussed in high-level resources about how length impacts protection of your RAR password ↗️ and timing estimates such as how to interpret timing estimates for your RAR password ↗️. This article focuses instead on how to avoid accidental incompatibilities so that the strong password you chose continues to work over time.
🔤 Unicode, Cyrillic, and Other Scripts in RAR Passwords
For many users, the practical questions are straightforward:
- “I created the archive using Cyrillic, but now it only accepts Latin characters.”
- “My password mixes two languages; it used to work, now it fails after reinstalling Windows.”
- “I changed system locale and my old backups stopped accepting the same password.”
These situations often arise from how Unicode and legacy encodings are handled.
Unicode as a Common Denominator
Unicode was designed to represent characters from virtually all written languages. Modern applications aim to convert all keyboard input into Unicode internally and then derive keys from that consistent representation. In practice, differences remain:
- Older archives created before widespread Unicode adoption may rely on code-page based encodings.
- Some operating system settings or compatibility modes can still influence how characters are normalized.
- Mixed-script passwords (for example, Latin letters, Cyrillic letters, emojis, and symbols) can behave differently when input methods change.
From a safety perspective, the key insight is that you should treat the environment used to create the archive as part of the “password recipe” — not just the characters themselves. That is why many users prefer to evaluate their RAR security model in a structured way, for example by first understanding their overall workflows and then building a secure workflow for encrypted archives ↗️ that takes locales and encodings into account.
Cyrillic and Regional Encodings
Cyrillic alphabets are a common source of confusion. Historically, different systems used different code pages (for example, Windows-1251 vs KOI8-R), and that history still shows up in long-lived archives. Consider these typical patterns:
- You created an archive years ago on a regional version of Windows using Cyrillic-only passwords.
- You later moved to a new machine with a different default encoding and switched to a newer WinRAR build.
- The password, as you remember it, now fails, even though your recollection is accurate.
In these cases, the mismatch often lies in the encoding step, not necessarily in your memory. Modern archives created on current systems are less affected, but legacy RAR files can still exhibit these behaviors.
Mixed Scripts: Latin + Cyrillic + Symbols
Many users create intuitive passwords by combining:
- Latin characters from product names or websites,
- Cyrillic words or nicknames, and
- Digits, punctuation, or even emoji.
This can be safe and practical when done carefully, but it increases the chances that encoding differences will appear later. For example, some characters that look similar across scripts (like Latin “A” and Cyrillic “А”) are distinct code points. On the original system you might have mixed them accidentally; years later, you may unconsciously “normalize” them when retyping, which leads to different underlying bytes.
Filename Encoding vs Password Encoding
It is also useful to distinguish between how filenames and passwords are encoded. Filename encryption and visibility are covered in more detail in resources about how filename encryption hides your protected RAR contents ↗️, but the key point here is this:
- Filename encoding affects how names appear in the archive list and whether characters look correct.
- Password encoding affects whether the key derived from your input matches the key used to encrypt the archive.
It is entirely possible for filenames to display incorrectly while the password still works, or for filenames to display perfectly while the password fails due to encoding differences. That is why purely visual checks are not enough to diagnose encoding-related access issues.
🌐 Common Symptoms of Encoding-Related Access Problems
Encoding issues mimic many other RAR problems. Before assuming the archive is corrupted or the password is wrong, it helps to look for specific patterns that suggest an encoding mismatch. A separate high-level guide on how to safely diagnose your locked RAR file ↗️ can give you a structured, non-destructive starting point; here we focus on encoding-specific symptoms.
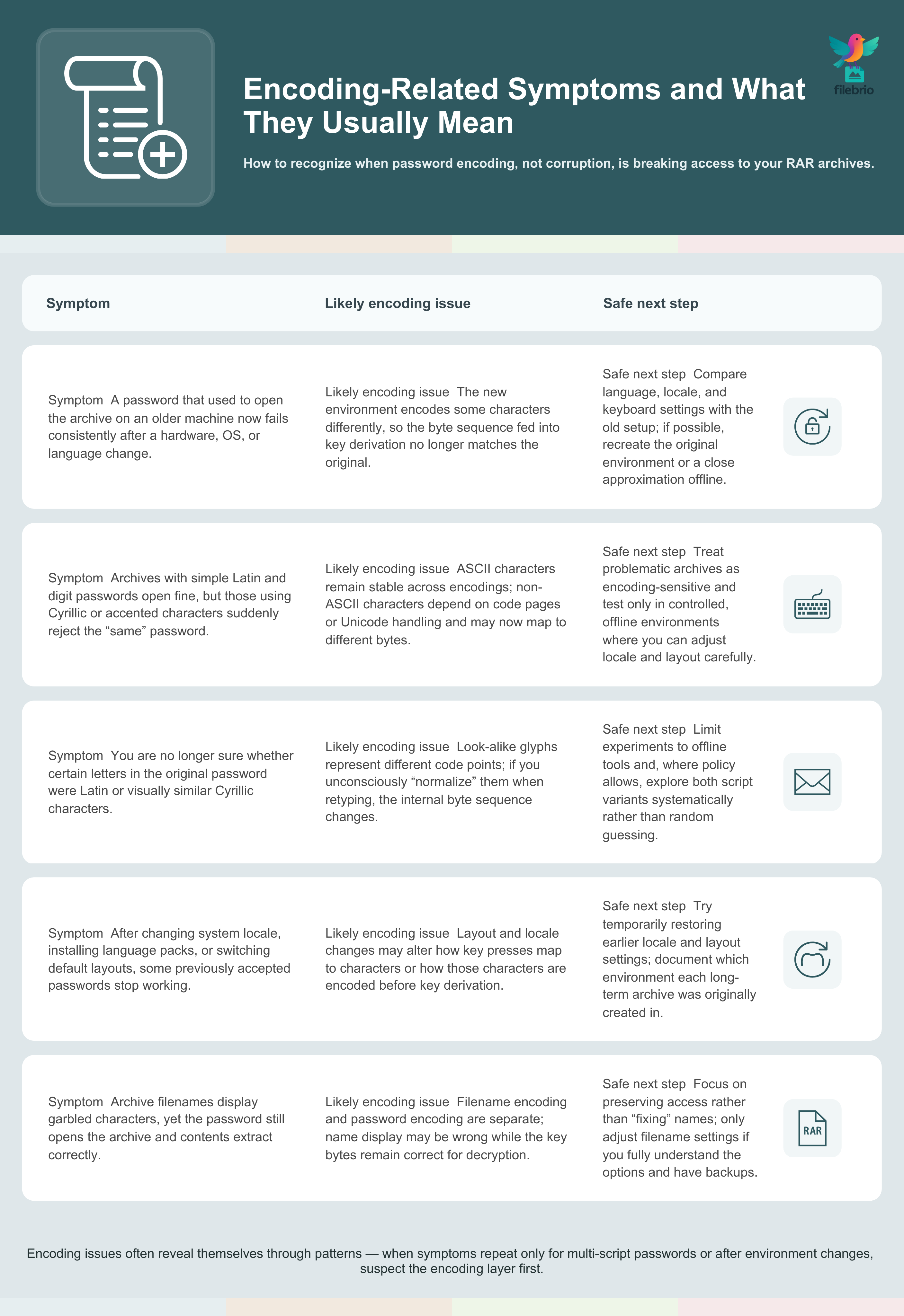
Typical Signs to Watch For
| Symptom | Encoding-Related Explanation (High Level) |
|---|---|
| The password worked on your old PC but fails on a new system with a different language/locale. | The new environment may encode characters differently, so the derived key no longer matches the original. |
| Passwords using only digits and basic Latin letters still work, but those with Cyrillic or accented characters fail. | ASCII characters are stable across encodings, while non-ASCII characters depend on code pages or Unicode handling. |
| Your password includes characters that look similar across scripts (e.g., Latin vs Cyrillic letters), and you are no longer sure which version you used. | You may be retyping different code points now, leading to different bytes and thus a different derived key. |
| After changing keyboard layouts or installing language packs, some previously accepted passwords stop working. | Input methods and layout switching can alter how key presses map to characters and bytes. |
Separating Encoding Issues from Other Problems
Encoding is only one of several reasons a RAR archive might refuse access. Others include genuine corruption, incorrect passwords, or security features like encrypted headers. For a broader perspective on limits and long-term safety, it is useful to think about how you will reinforce protection of your encrypted RAR files while preserving future access ↗️. That mental model helps distinguish “hard cryptographic limits” from “environment and encoding mismatches that can be corrected.”
If you want to experiment safely with how encodings behave, do it only on non-sensitive dummy data. Practice archives let you observe how different layouts and characters interact with encryption without endangering valuable content. Guides on how to test RAR protection with your dummy files ↗️ describe how this kind of learning can be done responsibly, at a conceptual level.
💼 All-In-One RAR Workflow for Multi-Script Passwords
When you are dealing with archives that may use Unicode, Cyrillic, or mixed-script passwords, you quickly realize that you need more than a single-purpose tool. You need a structured workflow that keeps everything offline, auditable, and privacy-focused while still giving you visibility into archive properties and behavior.
FileBrio Office Suite and its RAR-focused component, FileBrio RAR Master, are designed around that idea. Instead of scattering your sensitive archives across online tools, you can keep everything on your own machine and use a consistent set of diagnostics and access workflows.
| Need | What a Local All-in-One Workflow Provides |
|---|---|
| Understand how the archive is protected | High-level insight into format (RAR4/RAR5), header protection, and encryption status, so you can reason about encodings in context. |
| Evaluate feasibility without guesswork | Conceptual indicators of complexity and structure, so you avoid unrealistic expectations or risky online tools. |
| Preserve privacy | All processing remains fully offline, on your own hardware, with no uploads or third-party storage. |
| Document your actions | Repeatable, policy-aligned steps you can explain to colleagues, compliance teams, or auditors. |
For a broader picture of what the RAR-focused toolkit can offer, you can review FileBrio RAR Master features ↗️, which summarizes how diagnostics, access workflows, and safety checks are layered together in one environment. When you are ready to evaluate it directly, you can get the FileBrio tools installer ↗️ and keep your entire workflow local on your own systems.
________________________
FileBrio RAR Master — part of the FileBrio Office Suite — is a privacy-first, offline Windows toolkit for diagnosing and safely regaining access to your own password-protected RAR / WinRAR archives.
- Local processing only — nothing leaves your PC.
- Smart diagnostics to separate password issues from corruption.
- Owner-verified recovery workflows designed strictly for legitimate use.
Reminder: FileBrio RAR Master may be used only with archives you own or are explicitly authorized to access. It performs all analysis and recovery operations locally on your device, without uploading data anywhere.
________________________
🛡️ Safe Recovery Options When Encoding Gets in the Way
Once you suspect that encodings or locales are interfering with access, it is tempting to immediately start “trying variations” of the password. From a safety perspective, it is better to move slowly and systematically. You want to protect the archive, avoid accidental damage, and stay firmly within legal and ethical boundaries.
Step Zero: Confirm You Are Working on Your Own Data
Before doing anything else, ensure that you are dealing only with archives you legitimately own or are formally responsible for. In corporate and professional settings, this typically means documented approvals, tickets, or formal requests. Conceptual resources on how to verify ownership before accessing your RAR file ↗️ provide practical framing for what “legitimate access” means in real-world workflows.
High-Level Diagnostic Actions (Conceptual)
At a high level, safe encoding-focused diagnostics tend to follow this order:
- Check the environment — Confirm language packs, keyboard layouts, and regional settings on the system where the password originally worked.
- Recreate original conditions where possible — If you still have access to the original machine or a backup of its configuration, replicating that context is often the least risky path.
- Use non-destructive metadata views — Where tools allow, look at header-level signals, archive version, and protection flags without modifying the data.
- Consult policy — In an organization, align any further actions with your internal security and compliance rules.
Throughout this process, it is helpful to keep an eye on overall risk and feasibility. Conceptual estimators, like those described in RAR password strength estimators and time-to-crack calculators ↗️, give you a high-level sense of how realistic further access attempts are, without turning your workflow into a trial-and-error exercise.
Why Offline Tools Are So Important Here
Encoding-sensitive archives are often among your most important ones: personal backups, long-term business records, or compliance-related datasets. Uploading them to public sites, even if those sites claim not to persist data, introduces unnecessary risk. That is why privacy-focused guidance consistently encourages staying local, as emphasized in high-level resources about why offline tools keep your encrypted RAR data private ↗️.
When you keep everything offline, you maintain control over:
- Which machines ever see the archive.
- How diagnostics are run and recorded.
- Who has physical and logical access to the environment.
FileBrio RAR Master implements this principle by focusing entirely on local processing. Access workflows are designed so that archives, derived data, and diagnostics remain under your control on your own hardware, consistent with responsible-use policies.
🧱 Future-Proof Password Design and Storage Tips
Encoding issues are easier to avoid than to fix. Once an archive is locked behind a password whose exact byte representation you no longer remember, there may be no practical way back. Designing your passwords and metadata with future you in mind is one of the most effective protection strategies.
Prefer Unicode-Clean, Well-Documented Passwords
There is nothing inherently unsafe about using Cyrillic, Greek, or other scripts in passwords. The challenge is ensuring that you can reproduce the same characters and encoding years later. Some practical, high-level guidelines:
- Record which script you used — noting “Cyrillic word + Latin digits” is more informative than writing only the word itself in a vague way.
- Be explicit about look-alike characters — if you intentionally used Cyrillic letters that resemble Latin ones, document that choice.
- Avoid relying solely on system defaults — recognize that future systems may have different locales, fonts, and language settings.
It can also help to align your approach with broader best practices for archive security, such as those in resources on how to reinforce protection of your encrypted RAR files while preserving future access ↗️. Password design is just one piece of that long-term strategy.
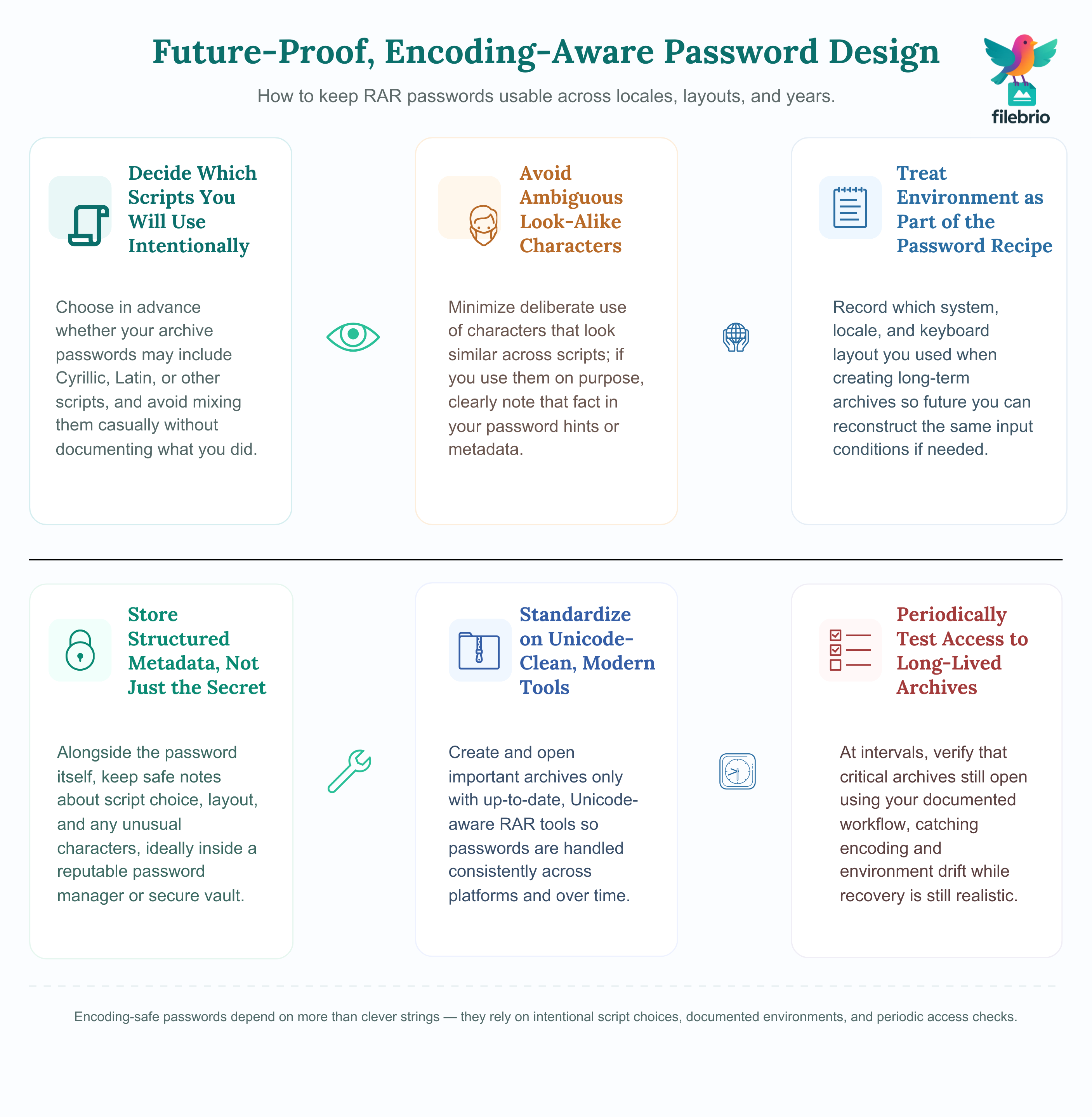
Think in Terms of Metadata, Not Just Passwords
For long-term retention, password-related notes and metadata are just as important as the password string itself. You do not have to write down the exact password in plain text; instead, you can design safe, structured hints and contextual notes. That kind of approach is especially useful in team environments and long-lived archives.
A broader, workflow-level strategy for managing encrypted archives — including how you document encoding, locales, and scripts used — fits naturally into guidance on ways to improve RAR protection with safe retention ↗️ and related topics about secure workflows.
Review Your Workflow Periodically
As operating systems, language settings, and tools evolve, it is wise to review your RAR handling habits regularly. That includes:
- Checking that new archives are still created in a predictable, well-understood environment.
- Ensuring that password policies and documentation processes remain up to date.
- Verifying that you have at least one trusted, offline toolchain installed and maintained.
Periodic reviews are easier when you follow a repeatable process, such as the one outlined in resources about how to design a secure workflow for your encrypted files ↗️. Encoding awareness can simply be built into that overall process.
🧰 Secure Offline Solution for Complex Encodings
Multi-script passwords, Unicode nuances, and legacy archives can be intimidating. A scattered collection of tools and ad-hoc steps increases the risk of mistakes, policy violations, or privacy issues. A focused, offline suite helps you approach the problem in a disciplined way.
FileBrio RAR Master, part of the broader FileBrio Office Suite, is built to support exactly these situations. Instead of pushing users toward online tools, it emphasizes:
- Centralized, local diagnostics — see format, protection flags, and structural hints about your archives without sending them anywhere.
- Policy-aligned workflows — behavior that fits naturally into organizational rules and responsible-use requirements.
- Scalability on your own hardware — including advanced modes for larger or more complex archives where strictly local processing is a must.
If you want a more detailed functional overview, you can review RAR password recovery tool capabilities ↗️ from a high-level perspective. For users and teams who handle many archives with diverse encodings and scripts, it can also be useful to study options for higher-performance workflows described in professional RAR unlocker modes ↗️, all within a privacy-first, offline environment.
When you are ready to examine the suite on your own systems, you can download the FileBrio Office Suite installer ↗️ and keep the entire evaluation fully under your control.
________________________
FileBrio RAR Master — a secure, offline Windows toolkit for regaining access to your own password-protected RAR / WinRAR archives while keeping all data strictly on your device.
- Offline-only processing — never uploads your archives.
- Smart issue detection — password vs corruption.
- Fast recovery workflow optimized for legitimate ownership.
⬇️ Download FileBrio RAR Master
Reminder: FileBrio RAR Master is intended only for archives you own or are explicitly authorized to access. All operations run locally on your PC.
________________________
📂 Teams, Audits, and Documenting Legitimate Access
Encoding issues become even more complex in organizations where multiple people need to access the same encrypted archives over many years. Personnel changes, policy updates, and hardware refreshes all increase the likelihood that future teams won’t remember exactly how specific passwords were constructed.
That is why many organizations treat encoding details as part of their formal documentation. Instead of relying on individual memory, they define templates that record:
- Which scripts and character sets are allowed in archive passwords.
- Which keyboard layouts and locales are considered “standard.”
- How metadata and hints should be stored and protected.
These topics naturally intersect with legal and compliance obligations. For example, if you ever need to explain your handling of encrypted archives to auditors or regulators, it helps to have a conceptual framework like the one described in legal factors when accessing your encrypted RAR files ↗️. That same framework can guide how you document ownership, access, and encoding choices over time.
When encoding-related access issues arise, you will often also need to demonstrate that you are working only with archives you are authorized to handle. Combining internal documentation with privacy-focused tools and clearly defined workflows makes that much easier to prove.
⚖️ Legal Reminder — Working Only With Archives You Own
This article is provided for general informational and educational purposes only. Any examples, scenarios, or references to password recovery, archive security, or related tools (including FileBrio RAR Master or similar software) are intended solely to help you better understand how to protect and manage your own data.
You may only apply any techniques, workflows, or tools described here to files and archives that you fully own or are explicitly and verifiably authorized to access. Attempting to bypass, remove, or recover passwords for third-party data without clear permission may violate criminal law, civil law, or internal company policies in your jurisdiction.
Nothing in this article constitutes legal advice. Laws and regulations differ between countries and organizations, and you are solely responsible for ensuring that your actions comply with all applicable legislation, contracts, and internal policies. If you are unsure whether a particular action is lawful or permitted, consult a qualified legal professional before proceeding.
For organization-wide deployments and policy questions — including responsible-use rules, legal language, and support procedures — it may be helpful to align your internal guidelines with information from legal and responsible use policy resources ↗️. Combining solid policy, clear documentation, and fully offline tools gives you a defensible, privacy-first foundation for all work with encrypted archives.
🔎 See Also — Related RAR Security Guides
- Why the RAR5 Key Derivation Function Matters for Security ↗️
- How File-Type Structure Affects RAR Diagnostics and Feasibility Analysis ↗️
- RAR Filename Encryption Explained: Privacy, Security, and Diagnostic Limits ↗️
- How to Strengthen RAR Archive Security While Preserving Future Access ↗️
- How to Build a Safe Workflow for Working With Encrypted Archives ↗️
- How to Evaluate Safe Options for Regaining Access to a RAR/WinRAR Archive You Own ↗️