
Why Some RAR Archives Become Impossible to Open — Security Explained
Imagine clicking a familiar RAR archive you’ve kept for years… and suddenly nothing works. Every password you try fails, repair options don’t help, and online tools only spit out errors. At some point, someone tells you, “This archive is basically impossible to open now” — but nobody can clearly explain why.
This article is written exactly for that situation. We’ll walk through the encryption, entropy, and structural reasons why certain RAR archives become mathematically or technically inaccessible — even when they belong to you and you’re acting in good faith. Along the way, you’ll see where effort still makes sense, where it hits hard cryptographic limits, and how to avoid ending up with “perfectly secure but permanently unusable” backups in the future.
🧭 Navigation
Important
The information provided in this article applies exclusively to RAR / WinRAR archives for which you have full, demonstrable ownership or properly documented authorization. If you are not the rightful owner of the data, do not directly control it, or cannot clearly prove permission to access it, you must stop immediately. Attempting to access, recover, or modify data without explicit authorization may violate criminal law, civil statutes, corporate compliance requirements, and privacy regulations in many jurisdictions. You alone are responsible for ensuring that your actions are lawful and properly permitted before proceeding.
📌 TL;DR — Why Some RAR Archives Become Impossible to Open
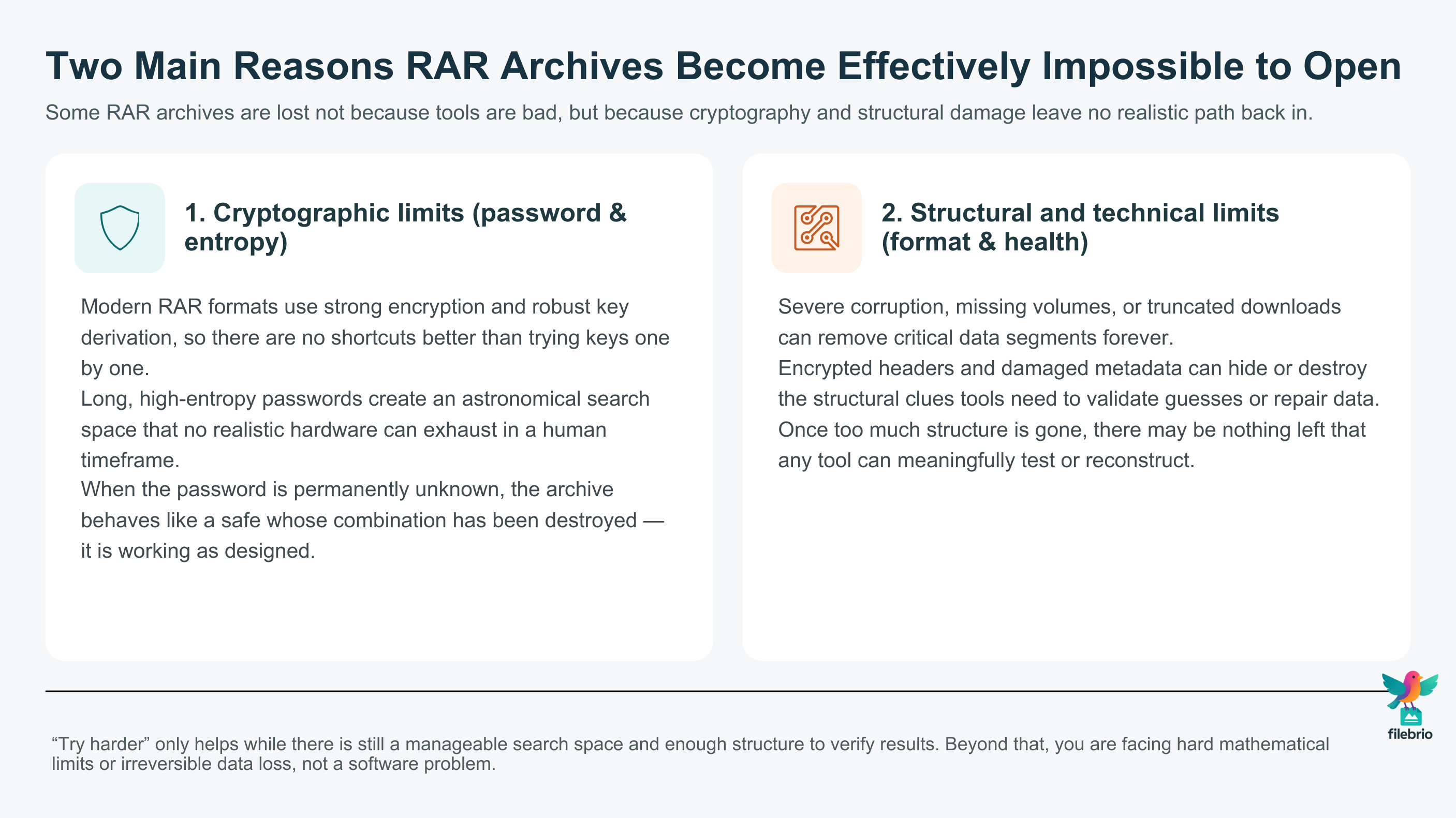
Some RAR archives really do become effectively impossible to open — even for their legitimate owners. There are two big reasons: cryptographic limits and technical or structural damage. Modern RAR formats use strong encryption (AES-256 with robust key derivation in RAR5). If your password is long, random, and unknown, the total number of possible passwords quickly grows beyond what any hardware can realistically check in a human timescale. This isn’t a software limitation; it is a direct consequence of how cryptography and entropy work.
On top of that, archive structure matters. Severe corruption, missing volumes, or encrypted headers can all remove the very metadata that tools rely on to verify guesses or reconstruct data. At some point, there may be nothing left that can be meaningfully tested or repaired. In those cases, “try harder” is no longer a strategy — you face either mathematical impossibility or irreversibly damaged data.
However, most real-world cases are not pure black or white. Before assuming your archive is lost forever, it’s worth doing basic diagnostics, checking storage health, confirming format and header encryption, and reviewing realistic password candidates from your own memory. From there, use safe, offline tools and a privacy-first workflow to evaluate feasibility — and accept that for some combinations of strong encryption and forgotten credentials, “unopenable” is a security success, not a failure of the tools. Finally, you can prevent future losses by improving password hygiene, keeping structured metadata, and planning for long-term access instead of relying on memory alone.
🧠 When “Impossible to Open” Is Literally True
When people say a RAR archive is “impossible to open,” they usually mean one of three things:
- They have tried many passwords and nothing worked.
- Repair attempts failed or produced only garbage.
- Online tools or utilities gave up or refused the file.
But from a security and cryptography perspective, “impossible” can be surprisingly literal. Modern RAR encryption is based on strong, well-studied primitives. There is no hidden “reset” function or emergency access channel that lets you bypass the password if the math says otherwise — which is why some archives cross the line into truly unrecoverable territory. If you want a deeper explanation of why your password cannot simply be reset like an email credential, you can also read about why your forgotten RAR password cannot be reset ↗️.
Two key questions define whether an archive is realistically accessible:
- Is the encryption strong, and is the password’s entropy high enough?
- Is there still enough structural and metadata information left to validate candidate passwords and reconstruct data?
If the answer to both is “yes, strong and intact,” but the password is permanently unknown, you are facing something very close to a locked safe whose combination has been burned. The safe isn’t broken; it is working exactly as designed.
🔐 How RAR Encryption and Entropy Set Hard Limits
RAR archives (especially in RAR5 format) rely on modern encryption and robust key derivation functions. In practical terms, this means:
- Your password is converted into a high-entropy cryptographic key.
- The process uses repeated hashing and mixing so that each guess is computationally expensive.
- The cipher (such as AES-256) is designed so that there are no shortcuts better than trying keys one by one.
From a high-level perspective, the security of your archive is essentially the security of your password’s entropy. If you deliberately choose something long and random, you are effectively telling the universe: “Only someone who knows this exact string deserves to see these files.” That promise is enforced by math, not by any company or product.
To understand how this works in context, it helps to review how different RAR generations protect data. A more detailed look at how RAR4 and RAR5 secure your protected data ↗️ shows that newer formats increase their resistance to guessing by strengthening both encryption and key derivation. As hardware improves, the format’s design aims to stay ahead by making each guess more expensive.
When the password is weak or predictable, you still may be able to regain access using controlled, lawful methods. But once the combination of format, key derivation, and password randomness crosses certain thresholds, no tool can realistically traverse the whole search space in any sensible timeframe.
🧮 Password Length, Entropy, and Search Space Explosion
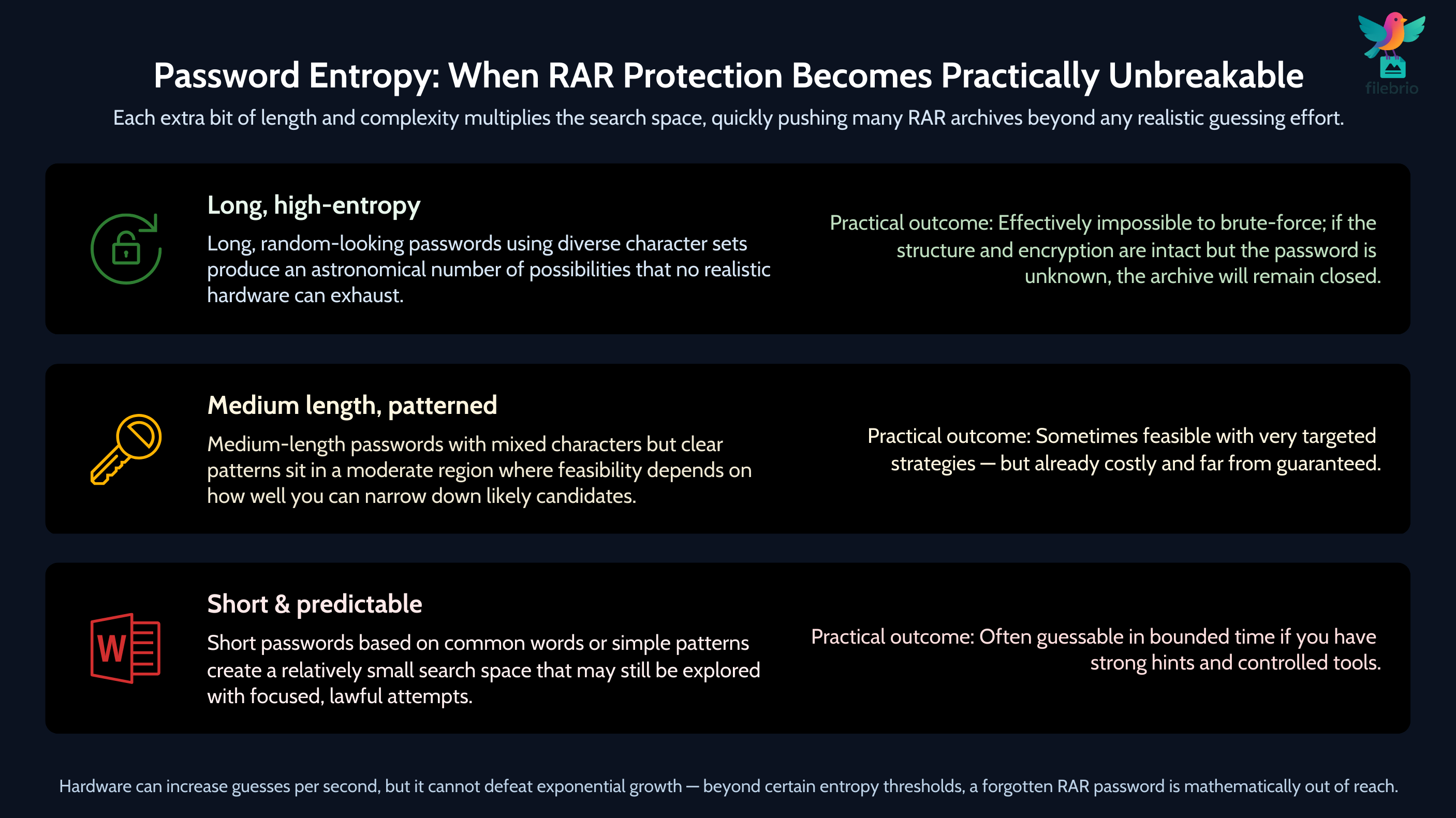
One of the core reasons some archives become impossible to open is that the number of possible passwords grows exponentially with length and complexity. Even without diving into equations, you can think of it like this:
- Each extra character you add multiplies the number of candidate passwords.
- Using mixed character sets (letters, digits, symbols, multiple languages) multiplies it even further.
- This multiplication stacks up incredibly quickly, producing astronomical numbers of combinations.
For a more structured overview of how length and randomness influence difficulty, it helps to look at how length impacts protection of your RAR password ↗️. There you’ll see that even modest increases in length and variety can push guessing time estimates far beyond the age of the universe, even if you had huge amounts of hardware dedicated to the task.
| High-Level Password Characteristics | Search Space Size (Conceptually) | Practical Outcome |
|---|---|---|
| Short, simple, based on common words | Relatively small | Often guessable with focused effort |
| Medium length, mixed characters, but patterned | Moderate | Feasible only with smart, guided attempts |
| Long, random, diverse character set | Enormous (astronomical) | Effectively impossible to exhaust by guessing |
Even with GPU acceleration, there are limits. Hardware can increase the number of guesses per second, but it can’t defeat exponential growth. A more detailed, high-level explanation of this trade-off is available in the discussion of how to interpret timing estimates for your RAR password ↗️. Those estimates never guarantee success; they simply describe how long a specific slice of the search space would take to examine under certain assumptions.
In other words, once your archive sits in the “astronomical search space” category and you no longer remember the password’s structure, math alone is enough to make the archive functionally unopenable.
🧱 Structural, Corruption, and Header-Encryption Limits
Strong encryption is only half the story. Some RAR archives become impossible to open because the structure of the file or its metadata has been damaged or deliberately hidden. There are several important scenarios:
- Severe corruption of archive data (e.g., storage errors, bad sectors, incomplete downloads).
- Missing or damaged volumes in multi-part archives.
- Encrypted headers, which hide file names and structural information.
Header encryption is particularly important. When headers are encrypted, tools cannot see the list of contained files or many of the structural cues they normally rely on. A deeper analysis of how the RAR5 KDF strengthens your encrypted RAR file ↗️ and its surrounding protection shows that this combination of strong key derivation and metadata hiding is intentional: it is meant to protect your privacy and make unauthorized analysis more difficult.
Here’s how structure issues contribute to “impossible to open” outcomes:
| Situation | Effect on Recovery Attempts | Practical Consequence |
|---|---|---|
| Encrypted headers with strong password | Very few visible clues; no filenames or sizes | Tools can’t easily validate guesses; high uncertainty |
| Severe corruption inside encrypted data | Even correct password yields broken content | “Opened” archive, but files unusable |
| Missing volumes in split archive | Critical data segments are gone | Only partial or no reconstruction is possible |
Some advanced features like quick open records and recovery blocks in RAR5 can improve resilience, but they are not magic: if damage goes beyond what they were designed to withstand, or if they were never enabled, the archive can still cross into unrecoverable territory. For background on this, see what quick open records and recovery blocks do for your protected RAR file ↗️ at a conceptual level.
🧪 High-Level Diagnostics: Is Your Archive Near the “Impossible” Zone?
Before declaring your archive lost, it’s worth performing safe, high-level diagnostics that do not risk further damage. The goal is not to brute-force anything, but to answer questions like:
- Is this mainly a password/entropy problem, or is there also corruption?
- Is the archive using strong header encryption and modern format options?
- Are all volumes, if any, actually present and readable?
At this stage, it’s often helpful to review how RAR formats and encryption behave in general, and where realistic limits lie. Articles on how to judge feasibility of your forgotten RAR password ↗️ and how to understand limits on guessing your RAR password ↗️ can provide a framework for deciding whether further attempts make sense at all.
Typical high-level diagnostic questions include:
- Do you remember anything concrete about the password? (length, language, style, reused patterns).
- How old is the archive, and what RAR format was likely used?
- Where was the file stored? (USB sticks, aging HDDs, cloud, etc.).
- Do basic archive checks reveal obvious corruption or missing volumes?
These questions don’t open the archive by themselves. They help you determine whether you’re dealing with “hard but maybe feasible” vs. “mathematically or structurally impossible.” For a broader decision-making framework, you can also look at how to assess safe access paths for your locked RAR file ↗️ before committing serious time or resources.

🧰 All-In-One RAR Security & Recovery Companion
When you’re unsure whether your archive is “difficult” or truly “impossible,” the last thing you want is a chaotic mix of tools and experiments scattered across your system. A structured, all-in-one approach helps you diagnose, evaluate, and, where feasible, recover your own RAR archives without exposing them to untrusted services.
FileBrio Office Suite — with its dedicated RAR toolkit — is designed as a local, privacy-first companion for exactly these scenarios. Instead of pushing your sensitive archives into online sites with unclear policies, you keep everything on your own machine and work within a consistent environment that is built around:
- Local diagnostics: Inspect structure, formats, and basic health indicators before deciding what to attempt.
- Privacy-first access: No uploads, no sharing, and no hidden pipelines to third parties.
- Archive-aware workflows: Features tailored for RAR/WinRAR archives, not generic zip operations.
You can learn more about the capabilities of the RAR module in the feature overview of what FileBrio RAR Master can do ↗️. It’s not about magic shortcuts; it’s about giving you the clearest possible picture of your archive’s condition so you can make informed decisions.
For situations where you need a safe starting point to install tools without hunting around the web, you can always fetch them directly from the official FileBrio installer page ↗️, keeping your workflow centralized and under your control.
________________________
FileBrio RAR Master — part of the FileBrio Office Suite — is a privacy-first, offline Windows toolkit for diagnosing and safely regaining access to your own password-protected RAR / WinRAR archives.
- Local processing only — nothing leaves your PC.
- Smart diagnostics to separate password issues from corruption.
- Owner-verified recovery workflows designed strictly for legitimate use.
Reminder: FileBrio RAR Master may be used only with archives you own or are explicitly authorized to access. It performs all analysis and recovery operations locally on your device, without uploading data anywhere.
________________________
🛰️ Why Online Tools Rarely Help With “Impossible” Archives
When an archive refuses to open, it’s tempting to search for “online unlockers” or “instant password solutions.” Unfortunately, the harder your archive is from a cryptographic perspective, the less helpful online tools become — while simultaneously increasing your privacy risk.
There are several reasons for this:
- Strong encryption does not become weaker just because a website offers a form field.
- Online services are limited by the same math and hardware constraints as local tools.
- Uploading your archive exposes its contents (or metadata) to third-party infrastructure.
In practice, many sites claiming to “unlock” encrypted archives either:
- Focus on trivially weak cases where passwords are short and predictable, or
- Are simply not transparent about what they actually do behind the scenes.
A privacy-focused alternative is to rely on offline tools that keep every operation on your local system. For more context on why this is safer, you can read about why offline tools keep your encrypted RAR data private ↗️ and combine that with comparisons like offline vs online RAR recovery ↗️ that explain, at a high level, how different approaches affect your risk profile.
🧯 How to Prevent Your Future RAR Archives Becoming Unopenable
The harsh reality is that once a RAR archive reaches the “impossible” zone, there is no tool or vendor that can reverse the underlying math or corruption. That’s why prevention and forward planning are so important. The goal is to design your protection so that:
- Your archives are strong enough to resist unauthorized access.
- But you still retain a realistic, long-term path to access them yourself.
Key strategies include:
- Choosing balanced passwords. Not everything needs maximum entropy. Avoid weak, common passwords, but pair strength with structures you can document or remember. See how length and entropy affect your password resilience ↗️ at a conceptual level.
- Storing password metadata securely. Instead of relying on memory alone, maintain private, encrypted notes about patterns, lengths, or partial hints in a secure location.
- Preserving archive health. Protect archives from corruption with reliable storage, backups, and checksums.
- Planning for future access. Consider format longevity and organizational policies if these archives matter for years or decades.
If you are designing protection strategies that must stay accessible in the long term, especially in business or multi-user environments, it’s worth looking into broader guidance on how to reinforce protection of your encrypted RAR files while preserving access ↗️. The goal is not just to be “secure today,” but to avoid locking yourself or your team out tomorrow.
🛡️ Secure Offline Toolkit for Sensitive RAR Archives
When archives are difficult — but not necessarily impossible — you need a workflow that is structured, auditable, and entirely under your control. Sensitive contents (personal backups, client projects, corporate archives) should never become test data for unknown websites or opaque tools.
FileBrio RAR Master is part of a broader Office Suite that is designed with these concerns in mind. Instead of focusing on “clever tricks,” it emphasizes:
- Local-only processing: Your archives never leave your machine unless you explicitly move them.
- Archive-aware diagnostics: Tools that understand RAR formats, metadata, and structural hints.
- Responsible feasibility evaluation: Helping you decide if continued attempts make sense within lawful and practical limits.
If you are approaching borderline cases, it’s especially useful to understand the precise conditions where recovery is no longer realistic. You can explore these boundaries in more detail through resources like limits of RAR decryption ↗️, which describe, at a high level, when encrypted headers and strong passwords together make archives essentially unreachable — and why that is a security feature rather than a flaw.
________________________
FileBrio RAR Master — a secure, offline Windows toolkit for regaining access to your own password-protected RAR / WinRAR archives while keeping all data strictly on your device.
- Offline-only processing — never uploads your archives.
- Smart issue detection — password vs corruption.
- Fast recovery workflow optimized for legitimate ownership.
⬇️ Download FileBrio RAR Master
Reminder: FileBrio RAR Master is intended only for archives you own or are explicitly authorized to access. All operations run locally on your PC.
________________________
⚖️ Legal and Ethical Boundaries Around “Impossible” Archives
Whenever you work with encrypted archives, even your own, you operate in a space where security, privacy, and legal obligations intersect. Some important principles to keep in mind:
- Only work on archives you own or are explicitly authorized to handle.
- Document your rights and responsibilities if you’re handling corporate or client data.
- Respect compliance requirements and privacy regulations that may govern how sensitive data is stored, processed, or recovered.
From a legal and security standpoint, an “impossible to open” archive belonging to someone else is often exactly what the system intended: unauthorized access should remain blocked, even if significant hardware is available. Your focus should be on documented, legitimate recovery of your own archives and on designing workflows that avoid catastrophic lockouts in the first place.
For more structured guidance on handling encrypted material responsibly, especially in professional environments, you may want to review high-level principles on ethical ways to handle your encrypted RAR files ↗️ so that your technical decisions remain aligned with your legal and organizational obligations.
This article is provided for general informational and educational purposes only. Any examples, scenarios, or references to password recovery, archive security, or related tools (including FileBrio RAR Master or similar software) are intended solely to help you better understand how to protect and manage your own data.
You may only apply any techniques, workflows, or tools described here to files and archives that you fully own or are explicitly and verifiably authorized to access. Attempting to bypass, remove, or recover passwords for third-party data without clear permission may violate criminal law, civil law, or internal company policies in your jurisdiction.
Nothing in this article constitutes legal advice. Laws and regulations differ between countries and organizations, and you are solely responsible for ensuring that your actions comply with all applicable legislation, contracts, and internal policies. If you are unsure whether a particular action is lawful or permitted, consult a qualified legal professional before proceeding.
🧷 Summary and Practical Next Steps
Some RAR archives become impossible to open because they are doing their job too well. Strong encryption, high-entropy passwords, and modern key derivation are designed to resist brute-force attempts, and beyond certain thresholds this resistance becomes absolute in any meaningful human timeframe. In parallel, archive structure and health — encrypted headers, missing volumes, or deep corruption — can remove the very information tools rely on to validate guesses or rebuild data.
Your first task is to distinguish between “difficult but plausible” and “mathematically or structurally impossible.” That means reviewing format, storage history, basic metadata, and any reliable memory you have about password patterns. If those checks point toward impossible conditions, continuing to run more tools will not change the outcome — and could even increase risk if you start uploading sensitive material to untrusted sites.
Going forward, the goal is prevention: design password practices that balance strength with future access, store private metadata that helps you reconstruct your own choices, and protect your archives from corruption and loss. When you do need to evaluate or attempt recovery, use privacy-focused, offline utilities that keep you within legal and ethical boundaries while giving you the clearest possible picture of what is still realistically achievable.
🔗 See Also: Learn More About RAR Security
- Why RAR5 is More Secure — and What That Means for File Access ↗️
- How to Determine If a RAR Archive Uses Header Encryption ↗️
- Known-Plaintext Concepts and What They Reveal About RAR Security Models ↗️
- GPU Acceleration in Password Guessing: Benefits, Limits, and Safety Considerations ↗️
- Resetting a RAR/WinRAR Password: Why Resets Don’t Exist and What Safe Options You Actually Have ↗️
- Is It Legal to Brute-Force a RAR/WinRAR Password? Legal Boundaries, Practical Limits, and Safe Use Cases ↗️
- Open RAR Files Without a Password? What’s Possible, What Isn’t, and How to Access Your Data Safely ↗️