How to Create Password Policies for RAR Archives in Business Settings
In many organizations, RAR and WinRAR archives quietly sit at the heart of critical workflows: finance exports zipped for email, HR bundles with personal data, engineering snapshots of source code, legal case files with long retention periods. Over time, different people protect these archives in different ways—short ad-hoc passwords, reused phrases, or no clear naming conventions. Then someone leaves the company, a laptop is retired, or a compliance audit lands on your desk… and suddenly nobody remembers how the data was protected.
At that moment, “just try to remember the password” is no longer enough. You need clear, documented rules: when encryption is mandatory, what counts as a strong password, how teams share access without emailing secrets around, and what happens if someone forgets. That is exactly what a RAR password policy provides: consistent standards that protect sensitive archives without turning them into permanent black boxes.
This article walks you through how to design such a policy specifically for RAR/WinRAR usage in a business setting—covering foundations, scope, rule design, shared access, training, and long-term continuity. It focuses strictly on archives your organization owns and is legally allowed to access, and it emphasizes privacy-first, offline-friendly practices that reduce risk while keeping your workflows practical.
🧭 Navigation
Important
The information provided in this article applies exclusively to RAR / WinRAR archives for which you have full, demonstrable ownership or properly documented authorization. If you are not the rightful owner of the data, do not directly control it, or cannot clearly prove permission to access it, you must stop immediately. Attempting to access, recover, or modify data without explicit authorization may violate criminal law, civil statutes, corporate compliance requirements, and privacy regulations in many jurisdictions. You alone are responsible for ensuring that your actions are lawful and properly permitted before proceeding.
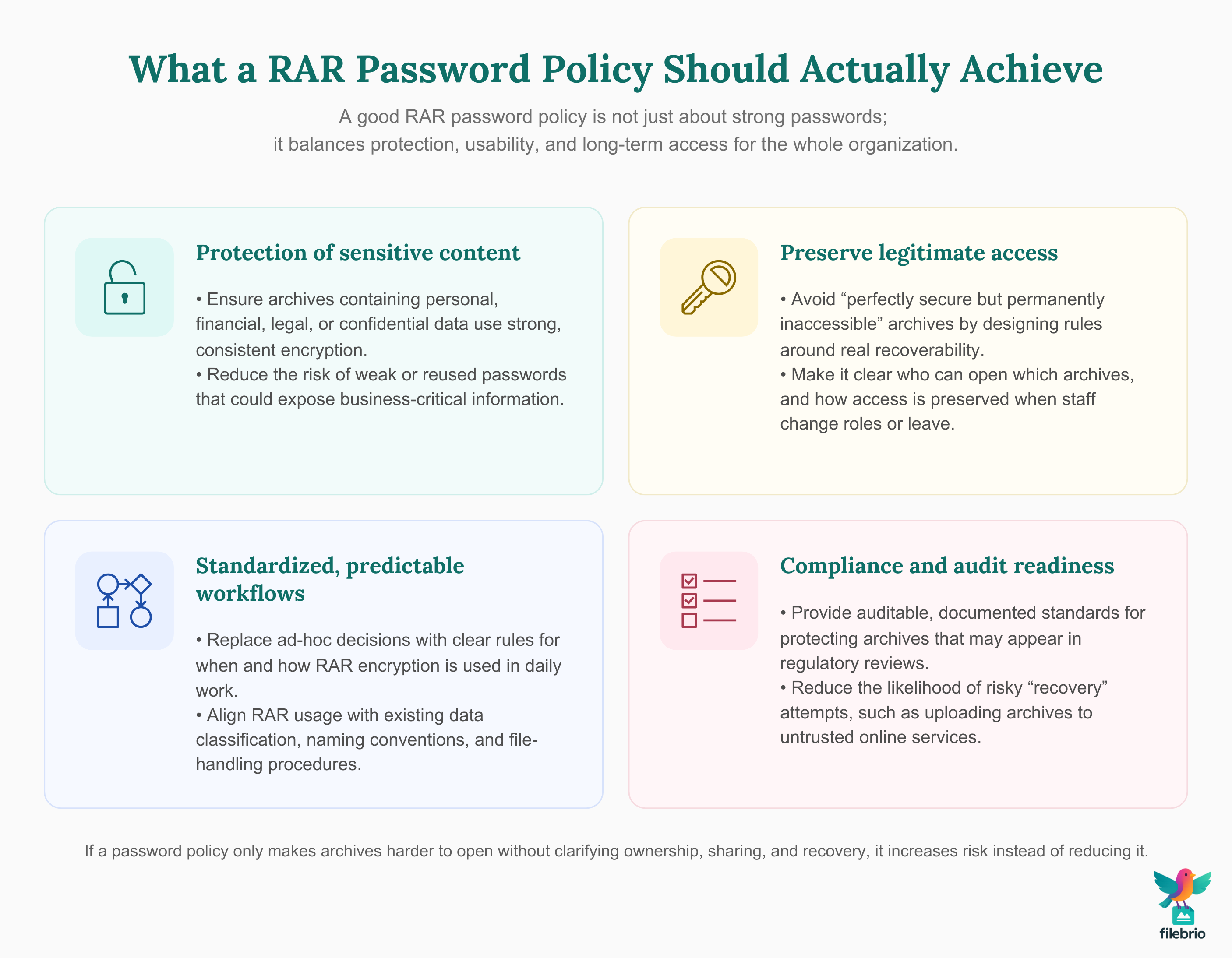
📝 TL;DR — What a RAR Password Policy Should Actually Achieve
A RAR password policy in a business setting has one job: protect sensitive archives in a predictable, auditable way without locking the organization out of its own data. That means going beyond “make your password strong” and defining who uses RAR encryption, which archives must be protected, how passwords are structured, and how teams share access when staff change roles or leave.
Before you write rules, you need to understand how RAR encryption works, what it can and cannot protect, and how features like header encryption and long, high-entropy passwords can make some archives effectively unrecoverable. A good policy acknowledges those limits and uses them deliberately, rather than discovering them during a crisis.
The core elements of a workable policy include: a clear scope (which types of files and departments must use encrypted RAR archives), explicit password standards (minimum length, allowed character sets, reuse rules, and rotation criteria), and guidance for shared access (who owns a password, where hints or metadata are stored, and how to prove ownership if there is a dispute). The policy also needs practical enforcement and support: tools that help staff create and test compliant archives, privacy-first recovery workflows for legitimately owned files, and training that explains not only what to do but why.
Finally, a robust policy is forward-looking. It plans for mergers, system migrations, staff turnover, and long retention periods. That means documenting metadata, keeping secure notes, and designing archives so that future teams can still open them without resorting to risky online tools or unrealistic password-guessing attempts.
🏢 Why RAR Password Policies Matter in Business
In many organizations, RAR archives start as a convenience: an easy way to bundle files and protect them with a single password. Over time, they become a shadow security layer that sits alongside official systems—CRM platforms, DMS solutions, ticketing systems—without always being covered by formal policies.
That creates several risks:
- Inconsistent strength: one employee uses a 6-digit password, another uses a 20-character passphrase, and a third relies on the same token across multiple archives.
- No ownership clarity: nobody knows who “owns” the archive password, so when staff change roles or leave, access is lost or ownership is disputed.
- Audit and compliance gaps: sensitive data may be stored in encrypted archives outside official systems, making it hard to prove compliance with internal or regulatory requirements.
- Ad-hoc “recovery” attempts: when access is lost, someone uploads a sensitive archive to a random website promising to unlock it, creating a privacy incident on top of the original problem.
A formal password policy for RAR archives closes these gaps. It explicitly states when RAR encryption must be used, what “strong enough” means in your context, and which processes must be followed to avoid accidental data loss. It also links archive usage to broader practices for protecting sensitive files while allowing authorized recovery ↗️, so RAR is an integrated part of your security model instead of a risky side-channel.
🧱 Foundations of Strong but Practical RAR Protection
Before you define rules, your policy should rest on a shared understanding of how RAR encryption behaves. Without that, you risk setting expectations that cryptography simply cannot meet.
1. RAR encryption is designed to be hard to guess. Modern RAR4/RAR5 encryption relies on strong ciphers and key derivation functions. When combined with long, high-entropy passwords, this can make password guessing effectively impractical. The article on how RAR4 and RAR5 secure your protected data ↗️ provides an accessible, high-level overview your policy authors should understand.
2. “Stronger” is not always better if you forget. In a corporate setting, an unrecoverable archive is often as bad as a data breach, especially if it contained records you are obliged to retain. Your policy must therefore balance cryptographic strength with organizational recoverability, building in mechanisms (metadata, role-based access, documented hints) that keep data accessible to the right people.
3. Different archives deserve different protection levels. A public brochure doesn’t need the same protection as a compressed database export containing client identifiers. Your policy should recognize classifications—public, internal, confidential, highly confidential—and map them to appropriate RAR settings rather than applying a one-size-fits-all rule.
4. Human error is the most common failure mode. People reuse passwords, store them in plaintext, or forget to update shared notes. Common pitfalls are described in common mistakes when working with password-protected RAR archives ↗️; your policy should explicitly address how to avoid these behaviors.
With these foundations, the rest of the policy can be written in a way that is realistic, educational, and enforceable.
📁 Defining Scope: Which Archives Must Follow the Policy?
A policy that tries to cover “all possible RAR usage” quickly becomes vague and unenforceable. Instead, define a clear scope that aligns with your data classification and real workflows.
Start by mapping where RAR archives appear today. Typical locations include:
- Departmental file shares (finance, HR, legal, engineering).
- Email attachments sent to partners or customers.
- Ticketing systems and helpdesk tools (logs, configuration snapshots).
- Local workstation folders and removable media used by field staff.
Then define which of these cases are in scope. For example, you might state that:
- All archives containing personal data or confidential business information must use policy-compliant RAR encryption.
- Archives created solely for temporary transfer within the same protected environment may use lighter protection—but still follow naming conventions and ownership rules.
- Archives used for internal testing, dummy data, or training may be exempt if they contain no real data at all.
The policy should be explicit that any archive used to store or transfer sensitive data must follow both the password rules and the authorized recovery practices outlined elsewhere in your security documentation, echoing the principles described in how to build a safe workflow for working with encrypted archives ↗️.
🧩 All-In-One Toolkit to Enforce Your RAR Policy in Practice
Even the best-written password policy fails if staff have to juggle multiple tools or guess what “compliant” means in day-to-day work. In practice, teams need a simple, consistent way to create, inspect, and, when necessary, lawfully recover their own RAR archives in line with your rules.
A dedicated desktop suite can help translate policy text into predictable behavior:
- Centralizing diagnostics and archive health checks.
- Highlighting when an archive uses older formats, weak parameters, or risky patterns.
- Providing controlled, offline mechanisms for handling legitimately owned archives that match your policy’s boundaries.
To understand what such an environment can look like, you can review the RAR Master functions summary ↗️, which outlines how a focused toolkit can support policy-compliant RAR usage instead of leaving teams to improvise.
________________________
FileBrio RAR Master — part of the FileBrio Office Suite — is a privacy-first, offline Windows toolkit for diagnosing and safely regaining access to your own password-protected RAR / WinRAR archives.
- Local processing only — nothing leaves your PC.
- Smart diagnostics to separate password issues from corruption.
- Owner-verified recovery workflows designed strictly for legitimate use.
Reminder: FileBrio RAR Master may be used only with archives you own or are explicitly authorized to access. It performs all analysis and recovery operations locally on your device, without uploading data anywhere.
________________________
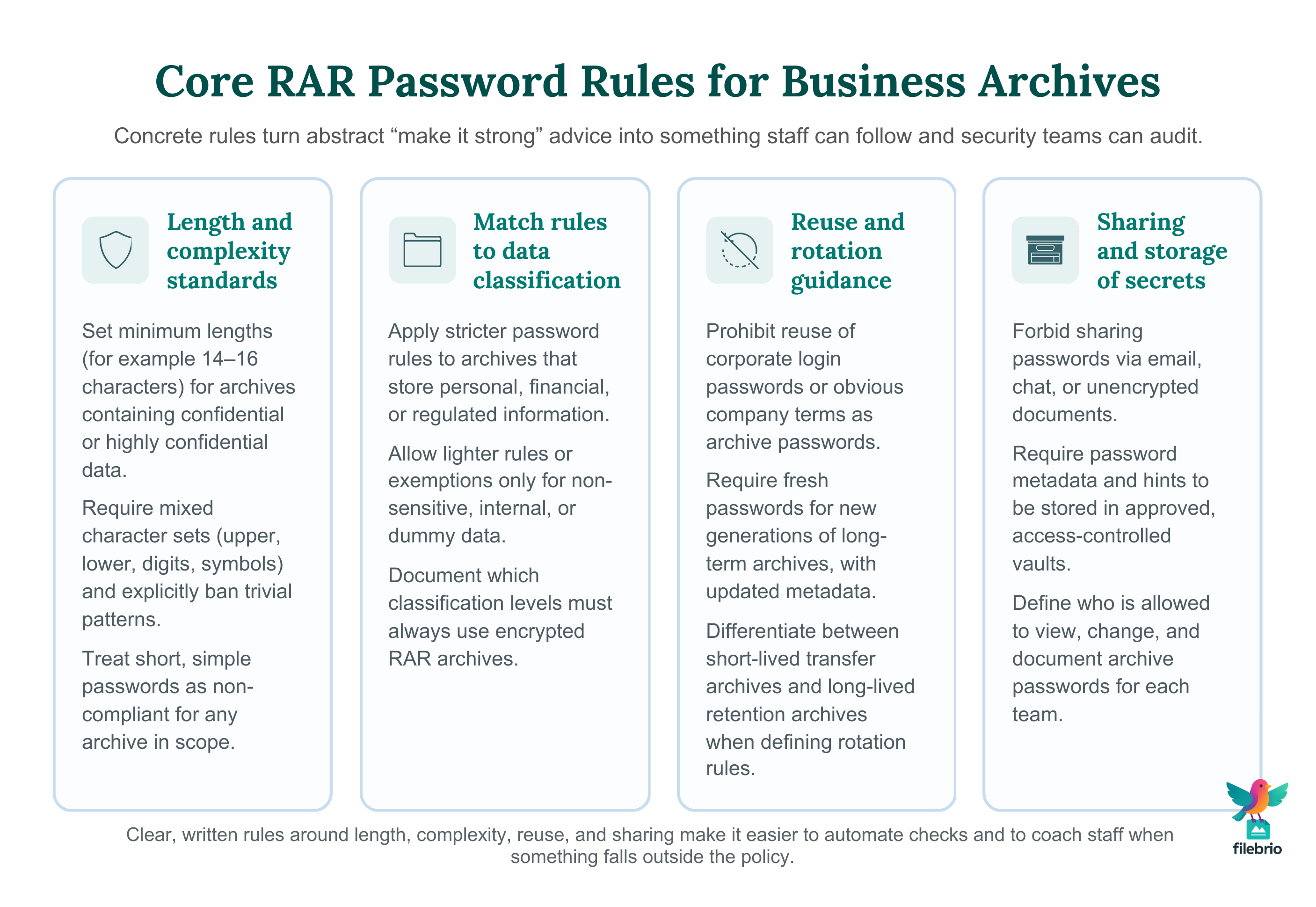
🧾 Designing Concrete RAR Password Rules (Length, Complexity, Rotation)
Once scope and foundations are clear, you can define specific password rules. These should be precise enough to be enforceable, but flexible enough that staff can actually follow them.
1. Length and complexity standards. A common baseline in business settings is:
- Minimum length: e.g., 14–16 characters for confidential data.
- Character mix: at least three of four groups (upper, lower, digits, symbols).
- Prohibited patterns: no department names, user IDs, or obvious company terms.
When setting these values, keep in mind how password length and entropy affect guessing complexity ↗️. The goal is to make random guessing impractical while still allowing staff to construct memorable, policy-compliant passphrases.
2. Rotation and reuse policies. Unlike login passwords, archive passwords often protect data snapshots that may live for years. Your policy should distinguish between:
- Short-lived transfer archives (e.g., monthly client reports), where rotation is less critical but uniqueness matters.
- Long-lived retention archives (e.g., multi-year legal or financial records), where stability and documented metadata are more important than frequent changes.
Mandating rotation for long-term archives can backfire if the old versions are still needed. Instead, you might require that any new “generation” of a long-lived archive uses a fresh password and updated metadata, while old generations remain accessible under their original credentials until officially retired.
3. Ban risky reuse and weak constructions. The policy should explicitly prohibit reuse of personal or corporate login passwords for RAR archives. It should also discourage predictable patterns—like appending “2025!” to a base term—since those are the first things an attacker (or an audit) will check, as explained conceptually in why common RAR passwords fail ↗️.
👥 Handling Team Access, Roles, and Ownership Proof
In a business environment, RAR archives rarely belong to a single individual. They usually represent shared work, so your policy must define who is responsible for passwords and how authorized colleagues can access them.
1. Define “archive owner” and “archive custodians.” A practical model is:
- Owner: the team or role (not just a person) that is accountable for the archive’s contents and password.
- Custodians: specific individuals who currently hold the password and are authorized to use it.
When staff move teams or leave, ownership stays with the role or department, while custodianship is transferred. This avoids orphaned archives and clarifies responsibility.
2. Document legitimate control. Your policy should outline how to prove that a team is working only with archives it owns or is authorized to access, echoing the principles in how to ensure you’re recovering only RAR files you own ↗️. This may include ticket references, job numbers, or signed approvals for sensitive cases.
3. Plan for disputes and audits. When legal or compliance teams ask “who had access to this encrypted archive, and when?”, you will need more than a shared folder full of files. Your policy should require minimal but structured documentation of archive creation, classification, and access events, aligning with broader guidance such as how teams can preserve long-term access to encrypted RAR files ↗️.
🔐 Secure Offline Environment for Policy-Compliant Recovery
Even with good policies, organizations occasionally lose track of passwords for their own archives. When that happens, the worst response is often the most tempting one: upload the file to an online “unlocker” and hope it works. Your policy should make it clear that recovery attempts must stay within a controlled, offline environment that respects ownership and privacy.
A dedicated suite can help by:
- Providing diagnostics to distinguish corruption from password issues before any recovery steps.
- Operating entirely on local machines, so sensitive archives never leave your infrastructure.
- Offering documented, auditable workflows that match your legal and compliance obligations.
Conceptual comparisons between online and offline approaches are discussed in why offline recovery is safer ↗️, and your policy can reference that reasoning when justifying its “offline first” requirement. For further procedural clarity, your legal and security teams can align these rules with the responsible use and support policy ↗️ associated with your chosen tools.
________________________
FileBrio RAR Master — a secure, offline Windows toolkit for regaining access to your own password-protected RAR / WinRAR archives while keeping all data strictly on your device.
- Offline-only processing — never uploads your archives.
- Smart issue detection — password vs corruption.
- Fast recovery workflow optimized for legitimate ownership.
⬇️ Download FileBrio RAR Master
Reminder: FileBrio RAR Master is intended only for archives you own or are explicitly authorized to access. All operations run locally on your PC.
________________________
🛡️ Documenting, Training, and Monitoring Compliance
A policy that lives only in a PDF belongs to the “checkbox security” category. To be effective, your RAR password policy must be taught, applied, and monitored.
1. Provide simple, role-specific guides. Instead of sending staff the entire policy, give them short, practical guides: “How to create a compliant RAR archive for client data,” “How to store team password metadata,” and “What to do if you suspect a policy violation.” These can link into deeper technical or FAQ resources, like the RAR user guide and FAQ ↗️, for users who need more detail.
2. Integrate into onboarding and regular training. Whenever you onboard staff into roles that handle sensitive archives, include a short module on RAR password practices. Periodic refreshers—once per year, for example—help reinforce good behavior and highlight changes in policy.
3. Monitor for non-compliance gently but firmly. Spot-check shared folders or repositories for obvious issues: unencrypted archives in sensitive areas, archives with suspicious naming (e.g., “password_here.txt”), or repeated use of the same password hint for different archives. When you detect problems, treat them as education opportunities first, enforcement second.
4. Use incidents as feedback. Every time the organization struggles to access its own archive, treat it as a mini post-mortem: what part of the policy failed—rules, tools, training, or monitoring? Mapping those findings against frameworks like legal and ethical guidelines for working with password-protected files ↗️ can help you refine the policy over time.
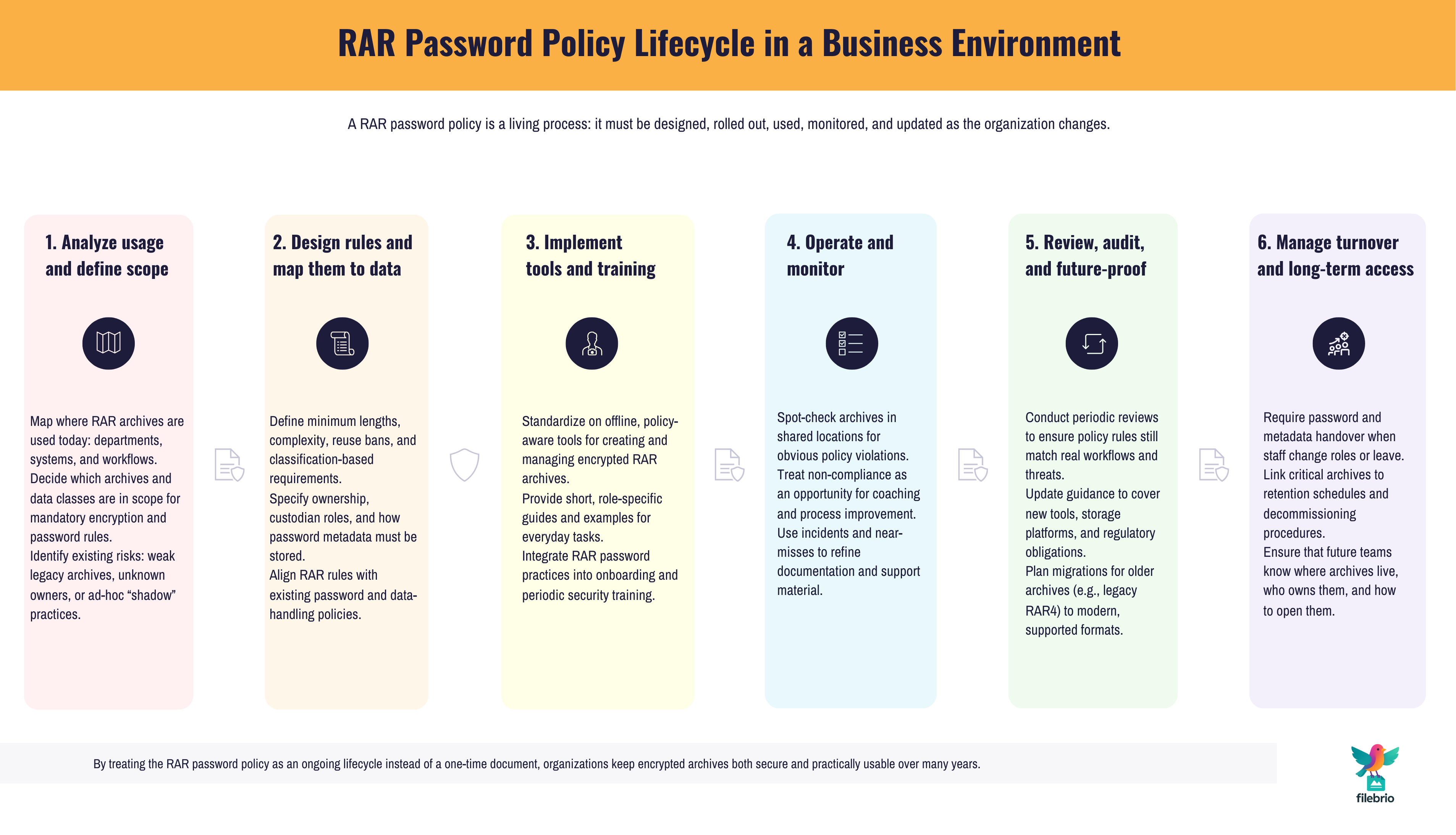
📦 Future-Proofing: Metadata, Turnover, and Long-Term Access
Business archives rarely live for days; many must remain accessible for years or decades. Your policy should therefore include explicit rules for metadata, documentation, and handover, so access does not disappear as people and systems change.
1. Store password metadata in a structured way. For personal use, there are good practices about how to store hints and contextual notes. In a team setting, you need a shared, controlled variant of those ideas. The article on how teams can organize shared RAR password metadata ↗️ offers patterns you can adapt into your policy: who can see what, where notes are stored, and how they are updated.
2. Connect RAR archives to retention and decommissioning processes. When a project ends or a system is retired, your information governance team should know which encrypted archives exist, how long they must be kept, and where their password metadata lives. This aligns with broader guidance on strengthening RAR archive security while preserving future access ↗️.
3. Prepare for organizational change. Mergers, acquisitions, or restructurings often bring surprises: forgotten archives, unknown passwords, and missing documentation. Your policy should require that critical encrypted archives be catalogued and that their ownership and metadata are reviewed during major organizational changes, not after a problem arises.
4. Think beyond today’s tools. Over time, software stacks change, but encrypted archives may persist. Make sure your policy doesn’t rely on a single application that might not be available in ten years. Instead, define requirements (e.g., offline, documented, privacy-first tooling) that any future replacement must meet, and keep a record of where your current solution can be safely installed from official sources ↗️ as part of your long-term access strategy.
⚖️ Legal & Ethical Reminder
This article is provided for general informational and educational purposes only. Any examples, scenarios, or references to password recovery, archive security, or related tools (including FileBrio RAR Master or similar software) are intended solely to help you better understand how to protect and manage your own data.
You may only apply any techniques, workflows, or tools described here to files and archives that you fully own or are explicitly and verifiably authorized to access. Attempting to bypass, remove, or recover passwords for third-party data without clear permission may violate criminal law, civil law, or internal company policies in your jurisdiction.
Nothing in this article constitutes legal advice. Laws and regulations differ between countries and organizations, and you are solely responsible for ensuring that your actions comply with all applicable legislation, contracts, and internal policies. If you are unsure whether a particular action is lawful or permitted, consult a qualified legal professional before proceeding.
📚 See Also: RAR Security & Governance Resources
- How to Protect Sensitive Files While Allowing Authorized Recovery (Corporate Workflows) ↗️
- How to Maintain Long-Term Access to Encrypted RAR Archives (Teams & Enterprises) ↗️
- How to Store RAR Password Metadata Safely Across Devices and Roles ↗️
- How to Strengthen RAR Archive Security While Preserving Future Access ↗️
- Legal and Ethical Guidelines for Working With Password-Protected Files ↗️
- Why Offline Recovery Tools Are Safer for Privacy ↗️
- How to Evaluate Safe Options for Regaining Access to a RAR/WinRAR Archive You Own ↗️