How Password Length and Entropy Affect Guessing Complexity
Understanding how password length and entropy shape guessing difficulty is one of the most important parts of evaluating real RAR archive security. Longer passwords help, but only when the characters are unpredictable and not built from familiar patterns or reused structures. This article breaks down these ideas in clear, high-level terms—showing how RAR encryption reacts to weak vs. strong choices, why human habits change effective complexity, and how to design passwords that stay both resilient and realistically manageable over time. It also explains how offline, local tools like FileBrio RAR Master can help responsible users analyze their own archives without exposing sensitive data.
🧭 Navigation
Important
The information provided in this article applies exclusively to RAR / WinRAR archives for which you have full, demonstrable ownership or properly documented authorization. If you are not the rightful owner of the data, do not directly control it, or cannot clearly prove permission to access it, you must stop immediately. Attempting to access, recover, or modify data without explicit authorization may violate criminal law, civil statutes, corporate compliance requirements, and privacy regulations in many jurisdictions. You alone are responsible for ensuring that your actions are lawful and properly permitted before proceeding.
⚡ TL;DR — Length, Entropy, and Guessing Difficulty
For encrypted RAR archives, password length and entropy together define how hard it is to guess your password. A longer password is helpful, but only if it is made from diverse, non-obvious characters and doesn’t follow simple patterns like “name + year.” Entropy is a measure of how unpredictable each character is; higher entropy means every additional character multiplies the number of possibilities, not just adds a few more. In practice, short, low-entropy passwords can sometimes be guessed quickly, while longer, predictable ones can still be within reach of modern hardware over time.
This article explains these ideas in high-level, non-technical terms so you can better judge the protection level of your own RAR archives, understand when recovery is realistically possible, and design safer passwords that you can still manage over the long term.
🔐 Password Length vs Entropy: Why They Matter Together
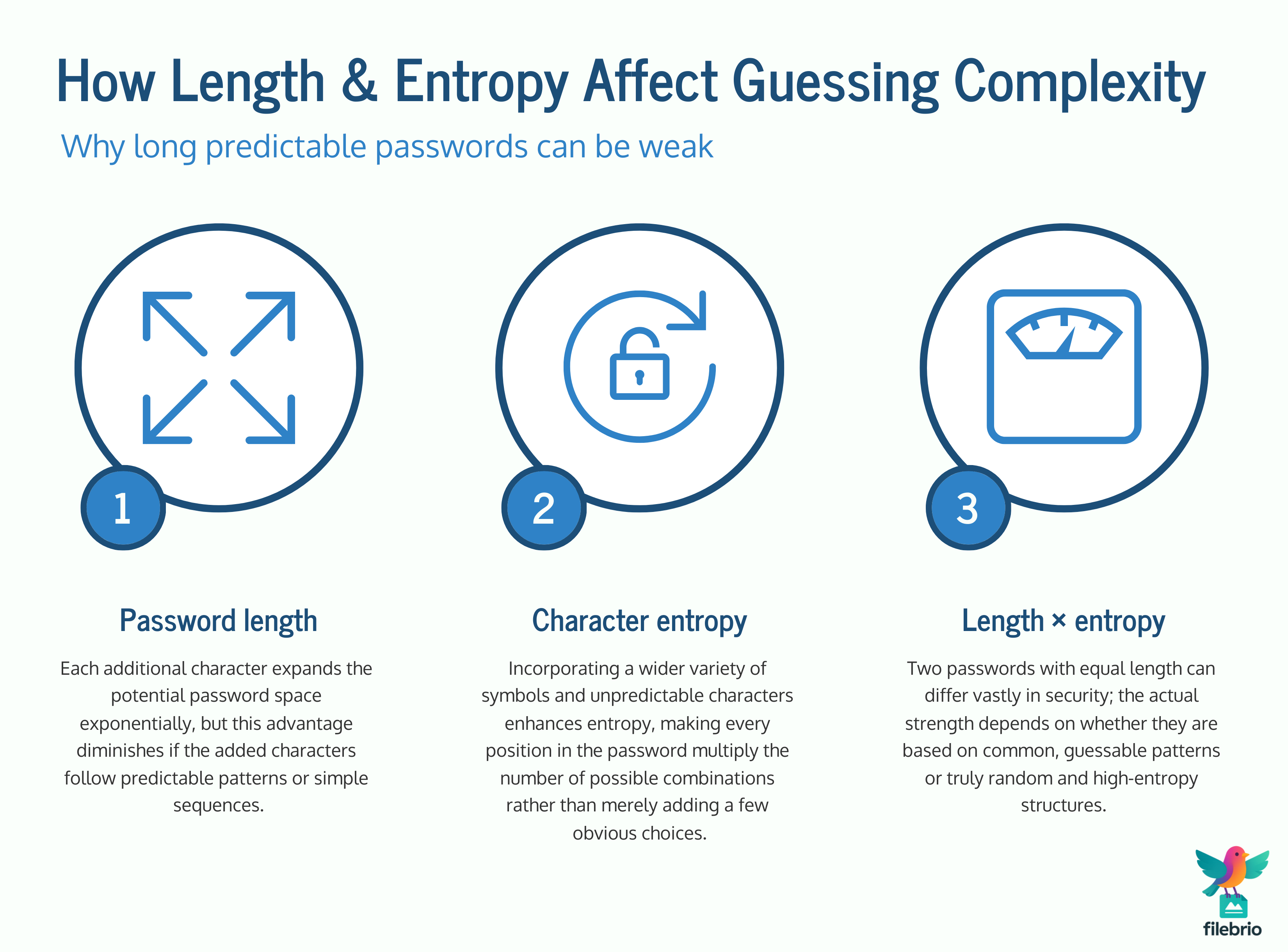
When people first hear about password security, the advice they often remember is “make it longer.” Length really does matter: each extra character expands the space of possible passwords. But length alone is not the whole story. A 12-character password made of a repeated word may be far easier to explore than a shorter but highly random password.
Entropy is a way to describe how unpredictable each character in a password is. Very roughly:
- If you always use only lowercase letters and simple words, your entropy per character is low.
- If you freely mix lowercase, uppercase, digits, and symbols in non-obvious ways, entropy per character is higher.
- If you follow fixed patterns (like “word + year + !”), you reduce effective entropy because the pattern is predictable.
Length tells us how many characters there are to guess; entropy tells us how “wide” the choices per character are. True guessing complexity is the combination of both. That is why two users with the same password length can have radically different protection levels depending on their habits.
In the context of RAR archives, this matters because the cryptography is designed to resist random guessing for as long as possible. The more entropy your password has, the more that resistance pays off in reality.
🧠 How RAR Encryption Treats Password Complexity
RAR formats such as RAR4 and RAR5 use strong encryption designed so that there is no “shortcut” to discover the password: from a high-level perspective, the only generic approach is to attempt many candidate passwords and see whether one of them unlocks the archive. You can think of the encryption as a locked door that does not wear down when you “try keys”; it either opens if the exact key is presented or remains closed.
If you want a deeper conceptual overview of how RAR4 and RAR5 protect data without going into commands or code, you can read about how RAR4 and RAR5 secure your protected data ↗️. The key idea here is that modern RAR encryption behaves as if every wrong password attempt provides no helpful information about the next attempt.
This makes password length and entropy especially important:
- More length means the conceptual “key space” is larger.
- More entropy means the distribution of keys inside that space is more uniform and harder to narrow down.
On top of encryption itself, modern RAR implementations apply a key-derivation function that intentionally slows down each password check. That means even if hardware gets faster, a single guess is made deliberately expensive. If you want to understand why this layer is so important, see the high-level explanation of how the RAR5 KDF strengthens your encrypted RAR file ↗️.
📊 Human Habits, Patterns, and Real-World Guessing Difficulty
So far, everything sounds abstract. In real life, most people don’t pick passwords by rolling dice; they pick them according to habits and patterns. Those patterns can dramatically lower entropy, even if the password is long.
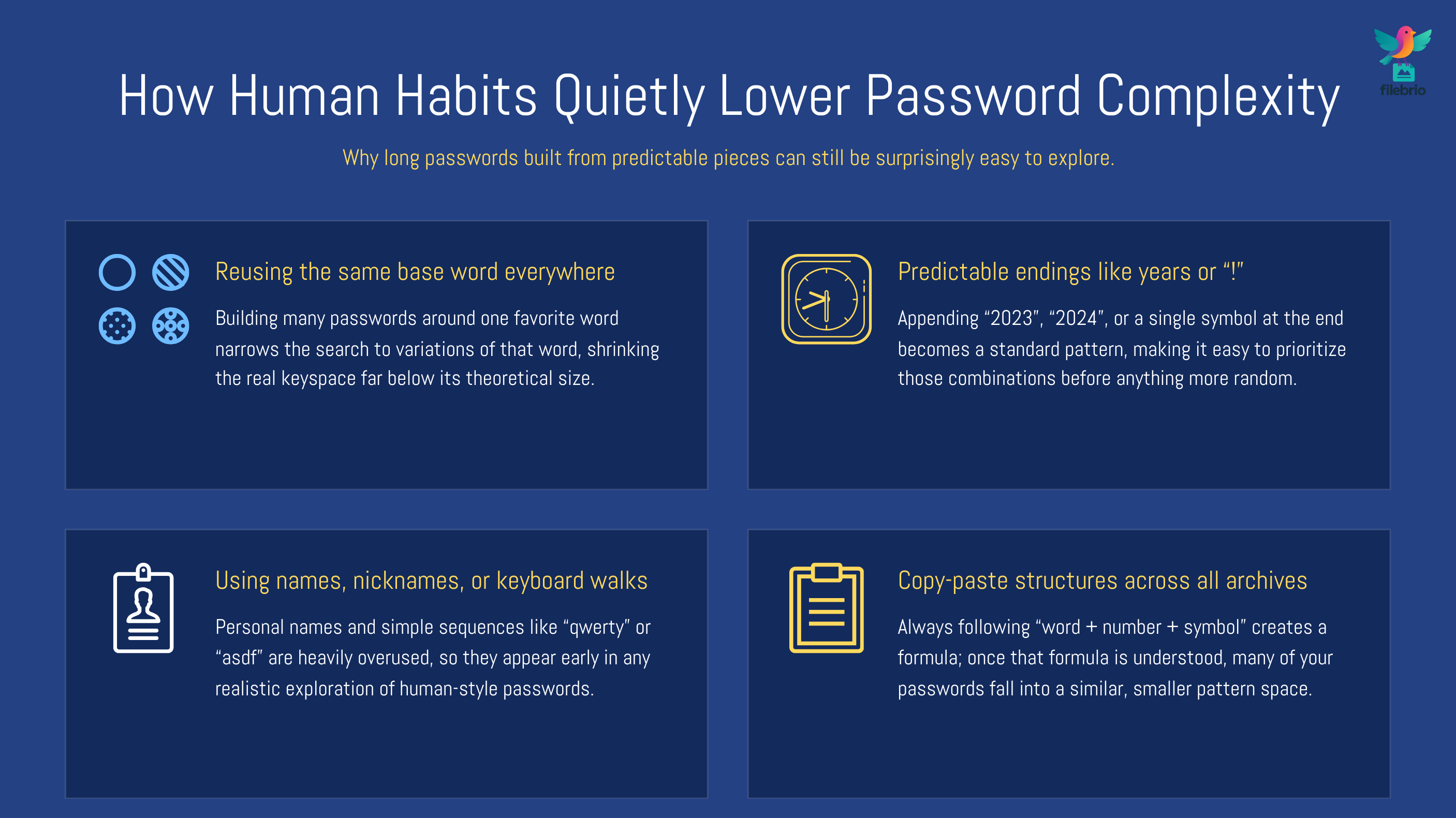
Common behaviors that reduce real-world complexity include:
- Reusing the same base word across multiple archives.
- Adding predictable endings like “2023,” “2024,” or “!” to slightly adjust an old password.
- Using names, nicknames, or simple keyboard sequences.
- Keeping the same structure for every password: “word + number + symbol,” always in the same order.
From a theoretical perspective, the password might look long. But from a behavioral perspective, a large part of the “space” can be skipped if someone understands how you usually think about passwords. This is one reason why high-level security guidance emphasizes not only length, but also the unpredictability of the pattern behind it.
If you want to explore broader behavioral risks that affect RAR security, you may be interested in the overview of mistakes that endanger your protected RAR files ↗️ — it focuses on habits and errors, not technical commands.
💼 All-In-One RAR Security & Recovery Companion
When you are dealing with a locked RAR archive you legitimately own, questions about length and entropy quickly become practical: “Does my password style give me any realistic chance of recovery?” and “How can I analyze the archive without exposing sensitive data?”
Users often face several pain points:
- They are not sure how strong their original password really was in practice.
- They are afraid of uploading confidential archives to unknown online services.
- They want a way to inspect technical details (format, headers, structure) without complex tools.
- They need guidance that explains limits and feasibility in clear, non-technical language.
FileBrio RAR Master, as part of the FileBrio Office Suite, is designed as an all-in-one, privacy-first toolkit that keeps all processing local on your own Windows machine. Instead of scattering tasks across different utilities or web forms, you can:
| Need | How an All-In-One Toolkit Helps |
|---|---|
| Understand archive health | Inspect structure and basic metadata to see if the file is intact before focusing on the password. |
| Gauge realistic recovery chances | Use high-level indicators, including length and complexity hints, to understand whether attempts make sense. |
| Stay privacy-first | Keep archives on your own computer, avoiding unnecessary uploads to third-party sites. |
| Work within legal boundaries | Follow responsible-use guidance tailored to accessing only archives you own. |
If you ever reach the point where you need to estimate whether trying to access your own archive is worth the effort, it is useful to read about how to judge feasibility of your forgotten RAR password ↗️ first. It focuses on effort vs limits rather than technical attack details.
________________________
FileBrio RAR Master — part of the FileBrio Office Suite — is a privacy-first, offline Windows toolkit for diagnosing and safely regaining access to your own password-protected RAR / WinRAR archives.
- Local processing only — nothing leaves your PC.
- Smart diagnostics to separate password issues from corruption.
- Owner-verified recovery workflows designed strictly for legitimate use.
Reminder: FileBrio RAR Master may be used only with archives you own or are explicitly authorized to access. It performs all analysis and recovery operations locally on your device, without uploading data anywhere.
________________________
🧪 High-Level Ways to Sense Whether a Password Is Strong Enough
While you should avoid actually “testing” your password on sensitive archives in unsafe ways, you can still reason about its strength conceptually. Here are high-level questions that help you understand where your password stands without sharing it or trying anything risky:
- Does it rely on a single real-world word? If so, length might be misleadingly high; attackers often prioritize word-like structures.
- How many different character types are used? Only letters? Or letters, digits, and symbols in non-obvious places?
- Is it a slight variation of another password you use? That reduces entropy because patterns can be reused.
- Is it tied to public or easily discoverable facts? Birthdays, anniversaries, and public names weaken security.
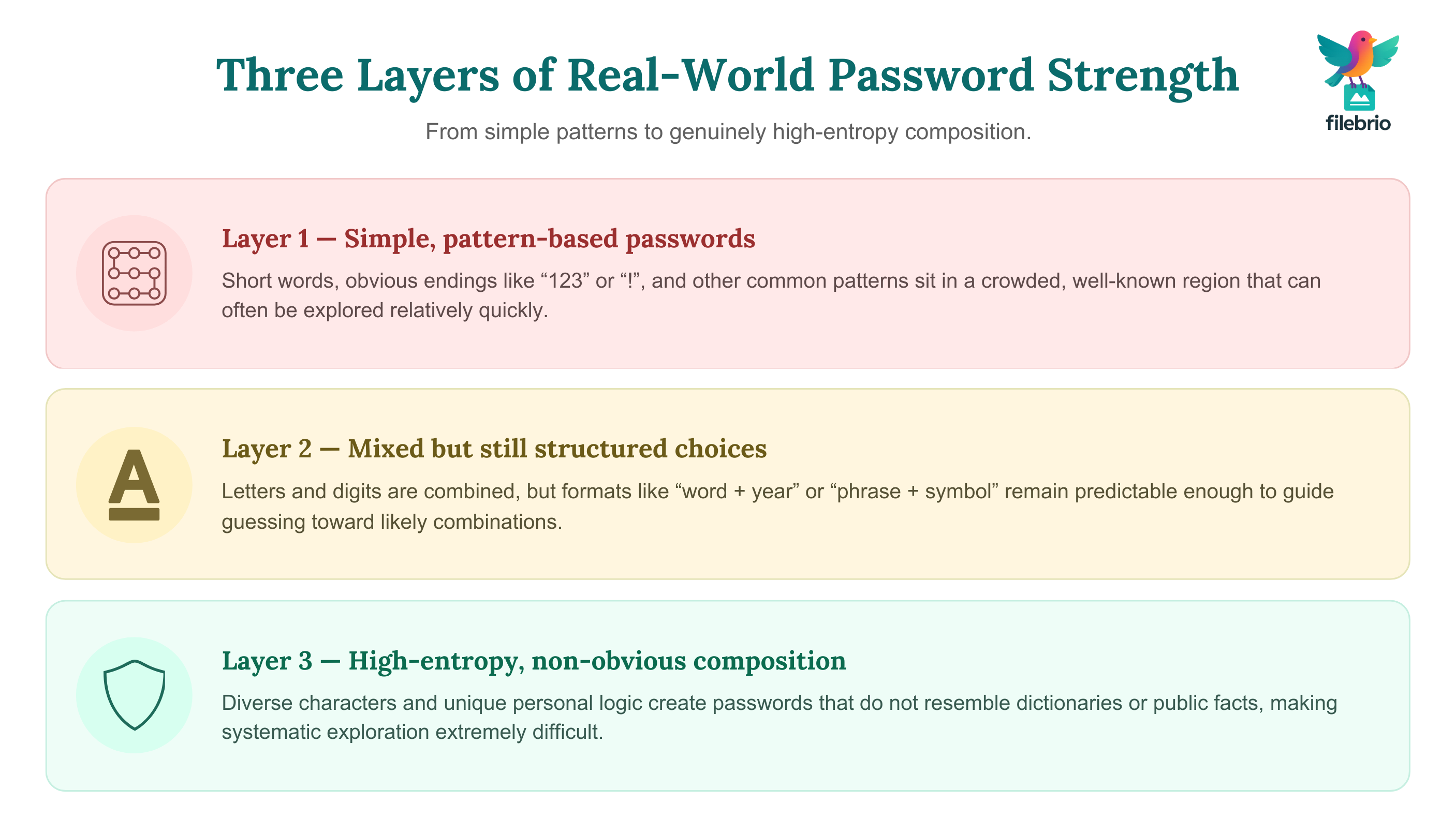
One useful mental model is to imagine multiple “layers” of complexity:
| Layer | Typical Characteristics | High-Level Complexity Insight |
|---|---|---|
| Layer 1: Simple patterns | Short, common words; predictable endings like “123”, “!” | Often vulnerable even if length is moderate. |
| Layer 2: Mixed but structured | Mix of letters and digits, but repeating patterns (e.g., word + year) | Better than Layer 1, but still shaped by human habits. |
| Layer 3: High-entropy composition | Diverse characters, non-obvious combinations, personal but not public references | Much harder to explore in any systematic way. |
For a broader perspective on how to raise security while still keeping future access manageable, consider the guidelines in how to strengthen RAR archive security while preserving future access ↗️.
🛡️ Secure Offline Analysis and Recovery with FileBrio
Once you have a sense of how strong your password might be, you still need safe tools to analyze your archive and decide what to do next. Many users search for quick online services that claim to “open” or “fix” RAR files instantly, but those options usually mean uploading private data to an unknown server and losing control over where your information ends up.
Typical pain points at this stage include:
- Uncertainty about whether an archive is damaged, protected, or both.
- Confusion about messages that mention corruption, unexpected end, or wrong passwords.
- Concerns about privacy, especially when archives contain confidential or personal information.
- Difficulty understanding which tools are legitimate and which are risky.
FileBrio RAR Master focuses on offline, local-first workflows. That means:
- Your archive stays on your own device while you inspect structure and basic health.
- You can explore high-level feasibility indicators (including password characteristics) without exposing data to third parties.
- You gain clearer expectations about what is mathematically realistic versus what is not.
When you need to reason about rough time ranges without instructions or commands, the dedicated high-level calculator page can help you understand RAR password strength estimates and time-to-crack calculations ↗️ in a conceptual way, not as a how-to manual.
________________________
FileBrio RAR Master — a secure, offline Windows toolkit for regaining access to your own password-protected RAR / WinRAR archives while keeping all data strictly on your device.
- Offline-only processing — never uploads your archives.
- Smart issue detection — password vs corruption.
- Fast recovery workflow optimized for legitimate ownership.
⬇️ Download FileBrio RAR Master
Reminder: FileBrio RAR Master is intended only for archives you own or are explicitly authorized to access. All operations run locally on your PC.
________________________
🧰 How to Design Stronger, More Sustainable RAR Passwords
High entropy does not have to mean “impossible to remember.” The goal is to move away from predictable patterns while still staying within what you can manage. A practical approach is to build structure that is unique to you but not tied to public facts and not easily condensed into a dictionary.
Some high-level design ideas:
- Combine multiple unrelated concepts. Instead of one word, think of several ideas that don’t naturally appear together.
- Use varied character types in genuinely non-obvious places. Insert digits or symbols inside words, not only at the very end.
- Avoid reusing the same pattern across all archives. If one password becomes known, you don’t want the rest to follow the same logic.
- Design a private transformation rule. For example, you might consistently transform certain letters—but avoid anything that matches common substitutions too closely.
To go deeper into building strong yet memorable protection for your RAR files, see the dedicated guidance on how to design strong memorable RAR passwords ↗️. And for longer-term retention, the strategies in how to avoid forgetting RAR passwords in the future ↗️ can help you stay secure without locking yourself out later.
If you ever decide to standardize your approach across many archives, a neutral overview of all features in the suite is available in the product page that describes FileBrio RAR Master features ↗️.
📉 When Longer Still Isn’t Enough: Practical Limits and Expectations
Even with good habits, there are still limits. At some point, entropy becomes so high that realistic attempts on an archive you own become impractical; in other cases, entropy is so low that even a modest effort might succeed. The challenge is that you often only know your position approximately.
Conceptually:
- Very short, low-diversity passwords may be within reach of modern systems, especially if patterns are known.
- Moderate-length passwords with mixed but predictable patterns sit in a gray zone where feasibility depends heavily on hardware and time.
- High-entropy, longer passwords can make the number of possibilities so large that attempts become unrealistic on a human timescale.
It is useful to think about this before you ever lose access to a file. For example, you can design policies for your own archives so that the length and entropy levels you choose are deliberately aligned with your risk tolerance and future needs. If you work in environments where recovery and clarity matter, tools like FileBrio RAR Master help you approach your own archives responsibly without promising unrealistic results.
For scenarios where the archive’s condition or password strength may already be close to the edge, you can read more about how to strengthen RAR archive security while preserving future access ↗️ as a way to plan ahead for new archives you create.
⚙️ How to Protect Yourself Going Forward
Thinking about length and entropy is only one part of protecting RAR archives. Broader security hygiene is just as important. Here are high-level actions that help reduce risk without requiring low-level technical knowledge:
- Plan your archive strategy. Decide which files truly require strong encryption and which can stay unencrypted or lightly protected.
- Use strong, unique passwords for truly sensitive archives. Avoid reusing patterns that appear in your email, social media, or other accounts.
- Keep your tools updated. Current versions of RAR-related software are more likely to support modern encryption and solid diagnostics.
- Document context safely. Note why an archive exists, what it protects, and where its password hints live—without writing the password itself.
- Maintain secure backups. Protect against storage failure so you do not face both lost hardware and a forgotten password at once.
High-level best practices for long-term archive usability are discussed in articles such as how to strengthen RAR archive security while preserving future access ↗️ (for designing new archives) and in product-focused documentation covering RAR password recovery tools ↗️ for legitimately owned files.
⚖️ Legal Reminder and Responsible Use
This article is provided for general informational and educational purposes only. Any examples, scenarios, or references to password recovery, archive security, or related tools (including FileBrio RAR Master or similar software) are intended solely to help you better understand how to protect and manage your own data.
You may only apply any techniques, workflows, or tools described here to files and archives that you fully own or are explicitly and verifiably authorized to access. Attempting to bypass, remove, or recover passwords for third-party data without clear permission may violate criminal law, civil law, or internal company policies in your jurisdiction.
Nothing in this article constitutes legal advice. Laws and regulations differ between countries and organizations, and you are solely responsible for ensuring that your actions comply with all applicable legislation, contracts, and internal policies. If you are unsure whether a particular action is lawful or permitted, consult a qualified legal professional before proceeding.
In addition to your own responsibilities, software vendors typically provide guidance, licensing terms, and support channels to help you act within legal and ethical boundaries. For FileBrio tools, this includes clear information about responsible use, privacy, and supported scenarios.
You can review these points in more detail on the official page describing the legal and responsible use policy ↗️ and, when you decide to deploy the suite more broadly, you can also review licensing options through the main Office Suite resources. Whenever you work with encrypted RAR files, always make sure you are handling only archives you own or are fully authorized to access.
📚 See Also: Further Reading
- GPU Acceleration in Password Guessing: Benefits, Limits, and Safety Considerations ↗️
- Why RAR5 is More Secure — and What That Means for File Access ↗️
- Known-Plaintext Concepts and What They Reveal About RAR Security Models ↗️
- Why Common RAR Passwords Fail: Patterns, Risks, and Security Lessons ↗️
- Understanding Password Encodings in RAR Archives (Unicode, Cyrillic, etc.) ↗️
- Brute-Forcing a RAR/WinRAR Password? Legal Boundaries, Practical Limits, and Safe Use Cases ↗️
- Open RAR Files Without a Password? What’s Possible, What Isn’t, and How to Access Your Data Safely ↗️