
How to Understand Password Recovery Time Estimates (High-Level RAR Examples)
Online “password time estimators” can look reassuring or terrifying — sometimes both. One tool promises your RAR password would take “millions of years” to guess, another claims “a few hours with a powerful machine.” If you’re locked out of your own encrypted RAR archive, these contradictions don’t help you decide what to do next.
This article explains, in plain language, how password guessing time estimates are built, why they vary so much, and what they actually mean for a RAR or WinRAR archive you legitimately own. We’ll stay at a high level, avoid any step-by-step instructions, and stay focused on privacy, legality, and realistic expectations.
🧭 Navigation
Important
The information provided in this article applies exclusively to RAR / WinRAR archives for which you have full, demonstrable ownership or properly documented authorization. If you are not the rightful owner of the data, do not directly control it, or cannot clearly prove permission to access it, you must stop immediately. Attempting to access, recover, or modify data without explicit authorization may violate criminal law, civil statutes, corporate compliance requirements, and privacy regulations in many jurisdictions. You alone are responsible for ensuring that your actions are lawful and properly permitted before proceeding.
🧾 TL;DR
Password guessing time estimates are rough projections based on how many possible passwords exist (entropy) and how many guesses per second a given setup might handle. For RAR and WinRAR archives, strong encryption and modern key-derivation functions mean that even modest-looking passwords can be completely impractical to explore exhaustively. Different calculators use different assumptions, which is why their numbers often disagree.
Use time estimates as a decision aid, not as a promise. They can help you decide whether it’s worth focusing on memory techniques and diagnostics, or whether the archive is realistically out of reach. Always apply these ideas only to archives you own or are explicitly authorized to access.
🧠 Understanding Password Guessing Time Estimates
At a high level, a password guessing time estimate tries to answer one question:
“If someone tried every plausible password for this archive, in some order, how long would it take on average before they find the right one?”
For RAR archives, this depends on two main pillars:
- How many realistic passwords are in play — the effective password space.
- How quickly each password candidate can be checked against the encrypted archive.
If you want to dig into the theory of entropy and how length and character variety influence difficulty, you can read more in the article about how password length and entropy affect guessing complexity ↗️. Here, we’ll stay focused on how these concepts show up in everyday RAR scenarios.
⏱️ What Actually Goes Into a Time Estimate?
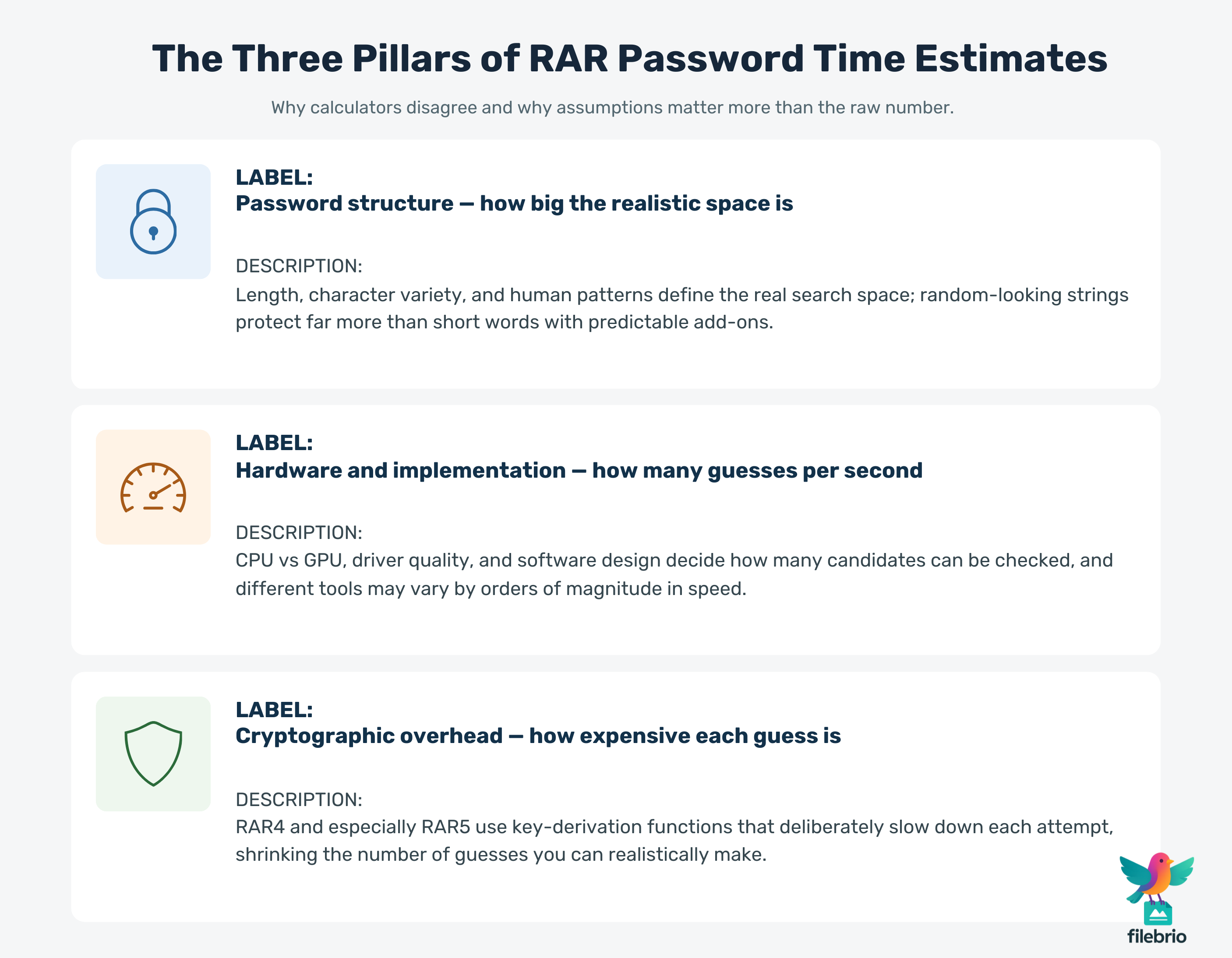
Most estimators (including high-level RAR-focused tools) informally combine three categories of information:
- Password structure — length, character sets, and predictability.
- Hardware and implementation — CPU vs GPU, optimizations, and software design.
- Cryptographic overhead — how RAR4 or RAR5 derive keys and verify candidates.
1. Password Structure
On paper, a 12-character password that uses letters, digits, and symbols has an enormous number of possible combinations. But real people rarely choose truly random strings. Instead, they use patterns: words, years, favorite names, substitutions, or repeated elements.
This creates a gap between the theoretical password space and the realistic one. A simple calculator may assume “all random characters,” which can produce huge, comforting times. A more realistic model might assume that your password follows human patterns, shrinking the search space drastically. That’s why estimates can diverge by many orders of magnitude.
To better understand how RAR formats themselves contribute to protection, it’s worth seeing how different versions behave in a high-level overview of RAR4 and RAR5 encryption ↗️.
2. Hardware and Implementation
The second major ingredient is pure computing power and code quality. A password checker that uses modern GPUs will test many more candidates per second than one that only uses a single CPU core. However, RAR’s encryption and key derivation were specifically designed to slow down this type of bulk testing.
At a conceptual level, you can think in terms of “guesses per second.” Hardware, drivers, libraries, and the quality of the implementation all influence this number. Even with acceleration, different software may perform dramatically differently. The article on GPU acceleration and high-level password guessing considerations ↗️ explains why raw speed isn’t the whole story.
3. Cryptographic Overhead
RAR5 (and to a lesser extent, RAR4) uses a key-derivation function that deliberately turns each guess into a relatively expensive operation. This works like a brake: even if you bring extremely powerful hardware, each candidate still takes a non-trivial amount of time to confirm or reject.
As a result, two naive online calculators that ignore this overhead may show time estimates that are wildly optimistic. High-level, RAR-aware models explicitly assume that each guess consumes a meaningful amount of computation time — and that assumption changes everything once you go beyond a handful of characters and patterns.
🔐 How RAR Encryption Shapes Real-World Speed
RAR archives don’t just rely on “a password.” They rely on a combination of modern algorithms and design choices that all affect guessing time:
- Strong ciphers (for example, AES) to protect the actual data.
- Key derivation functions that stretch the password into a key slowly.
- Optional header encryption, which can hide even filenames and structure.
All of this means that each “attempt” is more than a simple comparison. The software has to:
- Derive a key from the candidate.
- Decrypt or verify a small portion of the archive reliably.
- Check whether the result looks correct.
Because this overhead is deliberately expensive, even a moderate rise in password complexity can move a RAR archive from “maybe” into “effectively unreachable.” The article on why some RAR archives become impossible to open ↗️ goes into the conceptual security side of this phenomenon.
📊 High-Level RAR Scenarios (Without Formulas)
Instead of sharing formulas or specific numbers, it’s safer to think in terms of scenarios. The table below gives qualitative examples of how different patterns affect practical feasibility when you’re dealing with a RAR archive you legitimately own.
| Scenario (Owned RAR Archive) | Effective Complexity | Very Rough Outlook |
|---|---|---|
| Short password, based on a common word plus a single digit | Low | Potentially feasible if you can narrow down that word and digit range. |
| Medium-length password built from a few favorite words and dates | Medium | Outcome depends heavily on how well you can model your own habits. |
| Long, random-looking string from a password manager | Very high | Generally impractical to explore exhaustively, even with serious hardware. |
| Password with mixed scripts (e.g., Unicode, symbols, multiple languages) | Very high | Can be extremely difficult to model or guess, especially if not written down. |
Notice what’s missing: exact speeds and exact times. Those belong in specialized tools that run locally on your own hardware, using careful, lawful assumptions. Conceptually, though, you can see how moving from “short and predictable” to “long and random” shifts a RAR archive along a spectrum from “maybe recoverable” to “mathematically unreachable.”
If you’re trying to decide whether it’s even worth thinking about recovery, it’s helpful to combine these ideas with high-level feasibility checks from guidance on when password recovery attempts make sense ↗️.

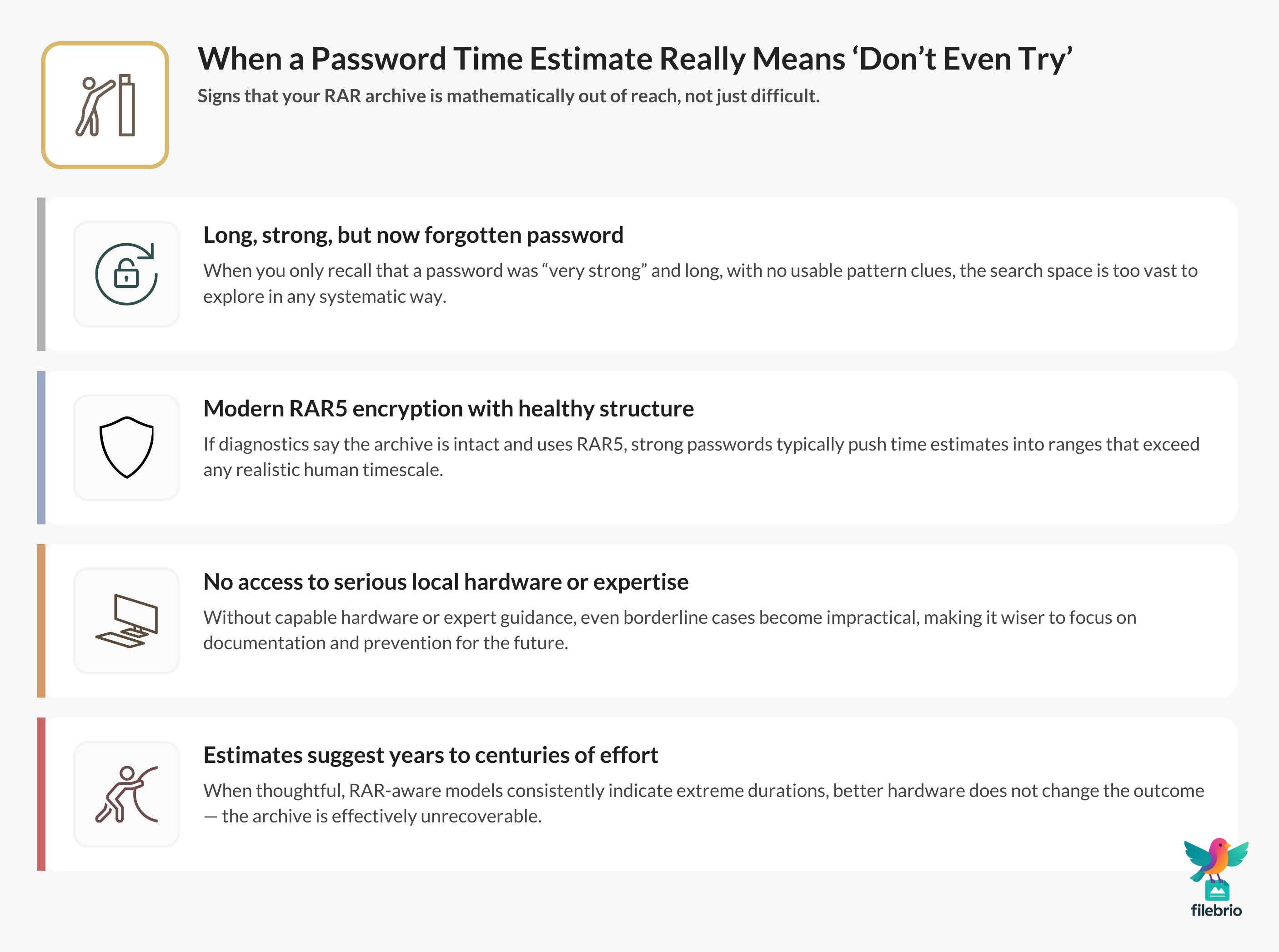
⚖️ When an Estimate Really Means “Don’t Even Try”
Sometimes, after factoring in your password style, archive age, and likely hardware, any honest estimate will essentially say: “This is not realistic.” That may feel disappointing, but it can also be liberating — you know not to spend months of worry and effort on a dead end.
Conceptually, an estimate is effectively saying “no” when:
- The password is long, randomly generated, or built from multiple unrelated words and symbols.
- You have little or no memory of its structure — just that it was “strong.”
- The archive uses modern RAR5 encryption and appears technically healthy.
- You don’t have access to specialized hardware or expert assistance.
In these cases, it’s usually better to focus on verifying that the archive is structurally sound and truly encrypted, rather than chasing unrealistic guesses. A high-level walkthrough of structural checks is available in the article about confirming whether a RAR archive is still technically recoverable ↗️.
💼 All-In-One Local Analysis and Recovery
When you own the archive and want to stay fully within legal and privacy boundaries, a local, offline toolkit is much safer than uploading data to online calculators or unknown services.
FileBrio RAR Master is designed specifically for these scenarios as part of the FileBrio Office Suite. Instead of scattering your troubleshooting across multiple tools and websites, you keep everything on your own machine.
| Need | High-Level Capability |
|---|---|
| Understand your own password difficulty | Helps you correlate your password style with realistic estimation logic. |
| Check archive health first | Archives can be inspected for corruption or structural issues before any recovery attempts. |
| Stay fully offline | All analysis and recovery logic runs locally, so encrypted data never leaves your device. |
If you want a more practical, guided view of time projections, you can later pair these concepts with the dedicated FileBrio password time estimation tool ↗️, which keeps all calculations on your own system.
For a broader, conceptual comparison between privacy-safe offline workflows and risky browser tools, you can also review the offline vs online overview at FileBrio RAR Master’s online–offline comparison page ↗️.
________________________
FileBrio RAR Master — part of the FileBrio Office Suite — is a privacy-first, offline Windows toolkit for diagnosing and safely regaining access to your own password-protected RAR / WinRAR archives.
- Local processing only — nothing leaves your PC.
- Smart diagnostics to separate password issues from corruption.
- Owner-verified recovery workflows designed strictly for legitimate use.
Reminder: FileBrio RAR Master may be used only with archives you own or are explicitly authorized to access. It performs all analysis and recovery operations locally on your device, without uploading data anywhere.
________________________
🛡️ How to Use Time Estimates Safely and Responsibly
Even when used correctly, time estimates should support safe decision-making, not encourage risky or obsessive behavior. Here are practical guidelines for applying them to RAR archives you own:
- Use them as triage, not a promise. If a realistic estimate suggests that exploring your remembered patterns might be feasible, it’s worth investing effort in memory work and diagnostics. If it suggests astronomical effort, accept that boundary.
- Combine with archive diagnostics. Before thinking about guessing, make sure the archive is actually readable and not corrupted. The article on diagnosing a locked RAR archive without risking data loss ↗️ outlines safe first steps.
- Respect legal and ethical limits. Time estimates are not a justification to work on someone else’s data. They’re a tool for responsible owners who want to understand what’s realistic.
- Prefer offline tools. Uploading an encrypted archive to unknown sites just to “see a number” exposes your private data and metadata. The privacy-focused article on why offline recovery tools are safer for privacy ↗️ explains why keeping analysis local is so important.
When you treat estimates as a guardrail instead of a shortcut, they become a valuable part of a safe RAR recovery strategy.
🔒 Secure Offline Recovery for Your Own RAR Files
Time estimates only tell you “how hard” a problem looks. They don’t inspect the archive, manage diagnostic steps, or guide you through safe handling of your own encrypted data. This is where a structured, suite-based approach helps.
FileBrio RAR Master sits inside the FileBrio Office Suite as a dedicated, offline environment for RAR analysis, diagnostics, and recovery within lawful boundaries. Conceptually, it’s built around three principles:
- Privacy-first: All work with your encrypted archives stays on your machine.
- Transparency: Tools emphasize diagnostics, structural checks, and realistic expectations.
- Control: You choose which archives to analyze and how far to go, always within legal use.
- When estimates suggest feasibility, you can structure your efforts within a controlled local environment.
- When estimates suggest “effectively impossible,” you can still use diagnostics to verify integrity and document the situation for internal or compliance purposes.
If you decide to explore the suite, you can get the installer securely from the official FileBrio Office Suite download page ↗️, keeping both tools and data under your direct control.
________________________
FileBrio RAR Master — a secure, offline Windows toolkit for regaining access to your own password-protected RAR / WinRAR archives while keeping all data strictly on your device.
- Offline-only processing — never uploads your archives.
- Smart issue detection — password vs corruption.
- Fast recovery workflow optimized for legitimate ownership.
⬇️ Download FileBrio RAR Master
Reminder: FileBrio RAR Master is intended only for archives you own or are explicitly authorized to access. All operations run locally on your PC.
________________________
🧩 How to Protect Yourself Going Forward
Understanding password guessing time estimates is valuable, but the real long-term benefit is improving how you design and manage RAR protection so you don’t end up in the same situation again.
Designing Strong but Realistic Passwords
Your future passwords should be strong enough to resist realistic guessing, yet still manageable for you and your organization. That typically means combining length, variety, and structure in a way that gives high effective entropy without relying on pure randomness you’ll never recall.
The balance between strength and memorability is discussed in more depth in the article on strengthening RAR archive security while preserving future access ↗️, which focuses on practical, sustainable choices rather than theoretical extremes.
Protecting Your Memory and Metadata
Many “impossible” RAR situations arise not because passwords were too weak, but because they were strong and then forgotten. To reduce that risk:
- Document high-level password patterns or hints in secure, offline notes.
- Record which archives use which policy (e.g., “project-based phrase plus year”).
- Store these notes in locations protected by strong, well-managed credentials.
For additional strategies, see the article on practical retention strategies that help you avoid forgetting RAR passwords in the future ↗️.
📎 When to Contact Professionals and Prove Ownership
Sometimes, after reviewing estimates and diagnostics, you may decide you can’t confidently interpret the situation on your own. In those cases, consulting professionals may be reasonable — but only if you can demonstrate legitimate ownership and choose a reputable partner.
Signs You Might Need Expert Help
- The archive is business-critical, and internal attempts have stalled.
- Time estimates are confusing or contradictory, and you fear making a data-damaging mistake.
- There are compliance or audit requirements around how the archive is handled.
Proving You Own the Archive
Any professional service operating ethically will want reassurance that you’re authorized to work on the data. That may include:
- Internal tickets or written approvals from data owners.
- Documentation about where the archive came from and who created it.
- Context about the projects or systems to which the archive belongs.
If you need a more structured approach to this topic, see the guidelines on ensuring you’re recovering only RAR files you own ↗️, which focus on responsible and well-documented access.
For formal policies, licensing details, and responsible-use statements surrounding FileBrio tools, you can review the information on the FileBrio RAR Master support and legal page ↗️.
⚙️ Summary and Next Steps
Password guessing time estimates are a useful, but limited, lens on RAR security. Used correctly, they help you answer questions like:
- Is it worth investing effort in memory reconstruction and diagnostics?
- Is my old archive realistically within reach, or closer to “mathematically unreachable”?
- How should I design future password and storage practices to avoid facing this situation again?
In practice, you’ll get the most value when you combine high-level estimation, archive health checks, and strong, well-documented password habits. That holistic view protects both your present data and your future self.
⚖️ Legal Reminder: Responsible Use Only
This article is provided for general informational and educational purposes only. Any examples, scenarios, or references to password recovery, archive security, or related tools (including FileBrio RAR Master or similar software) are intended solely to help you better understand how to protect and manage your own data.
You may only apply any techniques, workflows, or tools described here to files and archives that you fully own or are explicitly and verifiably authorized to access. Attempting to bypass, remove, or recover passwords for third-party data without clear permission may violate criminal law, civil law, or internal company policies in your jurisdiction.
Nothing in this article constitutes legal advice. Laws and regulations differ between countries and organizations, and you are solely responsible for ensuring that your actions comply with all applicable legislation, contracts, and internal policies. If you are unsure whether a particular action is lawful or permitted, consult a qualified legal professional before proceeding.
🔗 See Also: RAR Security & Safe Recovery
- How GPU Performance Shapes the Practical Speed of RAR Password Checking ↗️
- What Known-Plaintext Concepts Reveal About RAR Encryption Strength ↗️
- How RAR5’s Security Design Influences Real-World Guessing Feasibility ↗️
- Why Predictable Password Patterns Collapse Under Modern Security Models ↗️
- Why RAR Password Guessing Has Practical and Legal Constraints ↗️
- Why RAR Passwords Can’t Be Reset — and What Safe Alternatives Exist ↗️
- Understanding What’s Realistically Possible Without a RAR Password ↗️