
Trying to Open a RAR File Online? Why It’s Risky and What to Do Instead
You can’t open a RAR archive, you’re in a hurry, and search results offer an easy fix: “upload your file here, we’ll open or convert it for you — maybe even remove the password.” It sounds convenient, especially when you just want to peek inside a backup or grab a single document. But there’s a hidden cost: the moment you upload that archive, you’ve given a complete package of your data to someone else, often without any clear idea who they are or how they handle it.
Encrypted or not, a RAR archive usually represents a snapshot of your life or work — projects, contracts, personal photos, client data, financial records. Handing all of that to a random server for “help” is very different from opening it locally on your own machine. This article explains why opening RAR files online is risky, what privacy concerns you should consider, and how to use safer offline alternatives that keep control in your hands.
Everything here applies only to archives you own or are explicitly authorized to handle. The goal is to help you protect your data and avoid exposing sensitive contents to untrusted services, not to access files that belong to someone else.
🧭 Navigation
Important
The information provided in this article applies exclusively to RAR / WinRAR archives for which you have full, demonstrable ownership or properly documented authorization. If you are not the rightful owner of the data, do not directly control it, or cannot clearly prove permission to access it, you must stop immediately. Attempting to access, recover, or modify data without explicit authorization may violate criminal law, civil statutes, corporate compliance requirements, and privacy regulations in many jurisdictions. You alone are responsible for ensuring that your actions are lawful and properly permitted before proceeding.
✨ TL;DR — Why Opening RAR Files Online Is Risky
When you “open a RAR file online,” you are almost always doing one thing: uploading the entire archive to a third-party server. That server can keep copies, inspect metadata, log IP addresses, and potentially attempt to access your data, now or in the future. Even if the archive stays encrypted, you’ve handed someone a complete, portable package of your information that may sit in backups, logs, or analytics systems you will never see.
Online services typically give you:
- Little or no transparency about where your file is stored or for how long.
- No realistic way to verify that it was truly deleted.
- Privacy and legal exposure if the archive contains client, corporate, or personal data.
By contrast, offline tools keep everything local: the encrypted archive, diagnostics, and any attempts to restore access stay on devices you control. This dramatically reduces your risk surface. You can still benefit from strong RAR encryption, but you don’t create extra copies on unknown servers or rely on vague promises about deletion and security.
The safest pattern is simple: diagnose and work with locked RAR archives offline, using trustworthy local tools, and only on files you legitimately own. Treat online unlockers and converters as a last resort — and in many cases, something to avoid entirely.
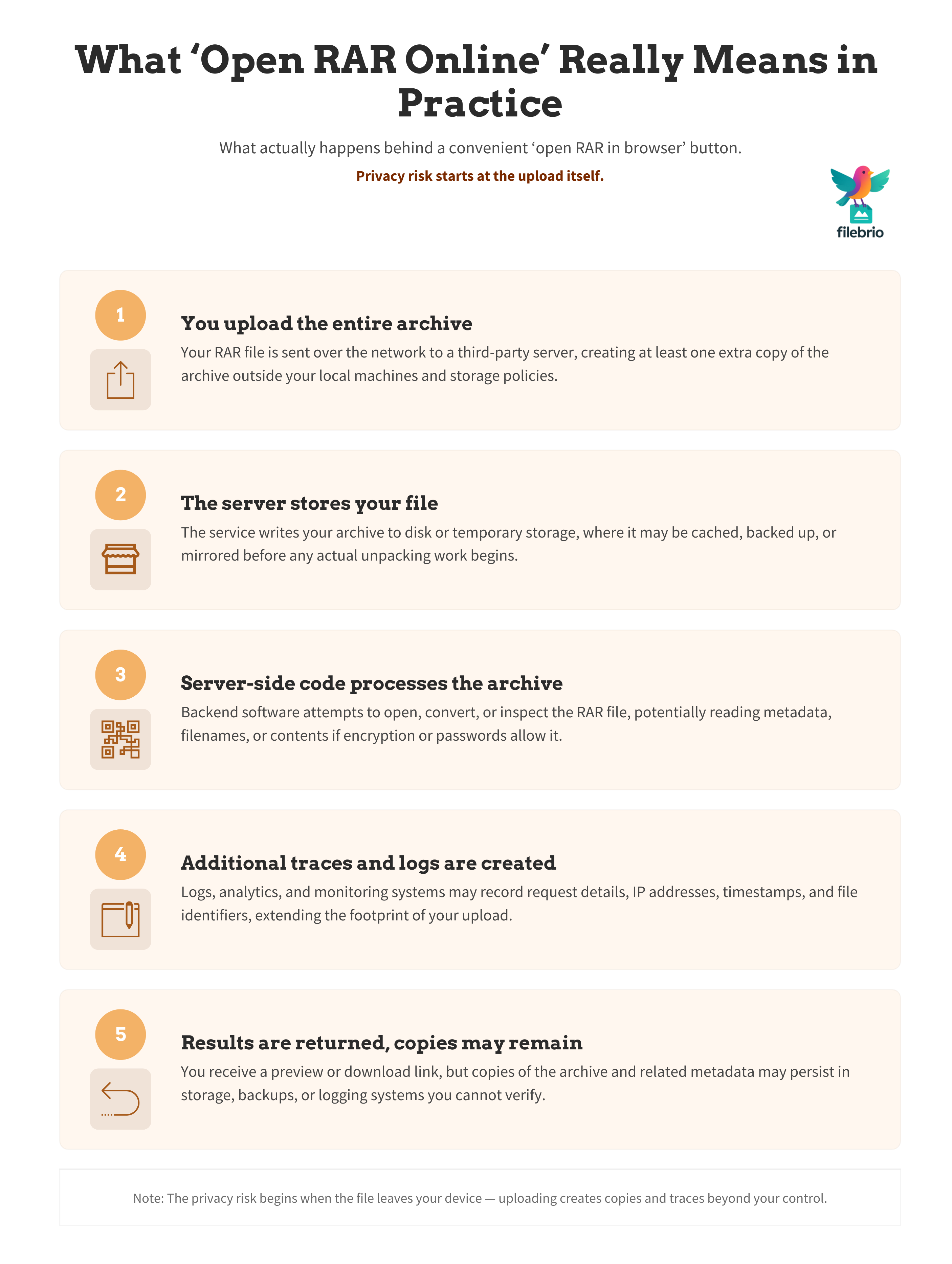
🌐 What “Open RAR Online” Really Means
Search queries like “open RAR file online” or “view RAR contents in browser” sound innocent, but they almost always translate into the same technical action: send us your archive, we’ll process it on our servers. There is no magic way for a website to look inside a RAR file sitting only on your local disk; the file has to be uploaded.
In practice, that means:
- An HTTP upload of your entire RAR archive to a remote system.
- Server-side code that unpacks or attempts to open the archive.
- Some form of temporary or permanent storage while processing happens.
Even if you do not enter a password, the archive itself might still leak information. Depending on how the RAR was created, filenames and headers can reveal project names, client names, folder layouts, or other sensitive labels. Understanding how encryption controls access to your protected RAR contents ↗️ helps clarify what is and isn’t hidden when you upload a file.
There’s also an expectation trap: many users assume that if an online tool doesn’t manage to open the archive, no harm was done. In reality, the harm is the upload itself — you’ve created another copy of your confidential data in a place you don’t manage, with no guaranteed deletion, and possibly in a different legal jurisdiction.
🧠 How RAR Encryption and Passwords Shape Privacy
Modern RAR formats (especially RAR5) combine strong encryption and key-derivation functions to make unauthorized access extremely difficult when passwords are chosen well. A high-level overview in how RAR4 and RAR5 secure your protected data ↗️ shows why properly configured archives can be very resistant to guessing.
But privacy is not only about cryptography; it’s about who holds the encrypted data and what they can observe:
- If headers and filenames are not encrypted, an online service may still see descriptive information, even if content remains protected.
- If your password is weak or reused, handing the archive to someone else gives them an easy chance to try standard guesses at scale.
- Even with strong passwords, multiple copies of the same encrypted archive increase the number of parties who could theoretically attempt access.
Articles such as why your forgotten RAR password cannot be reset ↗️ and how length impacts protection of your RAR password ↗️ highlight an important reality: there is no “reset button” for RAR archives. If you lose the password and created a genuinely strong one, recovery may be mathematically infeasible — for you, for an online service, and for anyone else.
That makes the privacy risk of uploads even less attractive. You might get nothing in return for exposing your archive: no recovery, no access, just an extra copy of your encrypted data on someone else’s server. Keeping everything offline ensures that any residual privacy risk is at least confined to systems you control.
🧰 All-In-One Local Toolkit Instead of Online Unlockers
If online tools are risky, you still need a practical way to work with RAR files that you own: checking what’s wrong, understanding error messages, and exploring legitimate options to restore access. Trying to piece this together with random utilities and scripts can be confusing and error-prone.
FileBrio RAR Master, part of the FileBrio Office Suite, is designed as an all-in-one RAR diagnostics and recovery environment that runs entirely on your own machine. Instead of uploading archives to the cloud, you use a single local toolkit whose offline vs online RAR recovery ↗️ approach is built around privacy, legality, and controlled diagnostics.
In a local setup like this you can:
- Inspect high-level archive properties and error messages without extracting anything.
- Apply safe diagnostic methods similar to those in how to safely diagnose your locked RAR file ↗️, all within one environment.
- Decide whether further effort is realistic and lawful before you attempt more intensive work.
Because everything runs offline, the privacy risk you accept is limited to the devices and accounts you already manage. That’s a completely different risk profile from handing your archive to an unknown server somewhere on the internet.
________________________
FileBrio RAR Master — part of the FileBrio Office Suite — is a privacy-first, offline Windows toolkit for diagnosing and safely regaining access to your own password-protected RAR / WinRAR archives.
- Local processing only — nothing leaves your PC.
- Smart diagnostics to separate password issues from corruption.
- Owner-verified recovery workflows designed strictly for legitimate use.
Reminder: FileBrio RAR Master may be used only with archives you own or are explicitly authorized to access. It performs all analysis and recovery operations locally on your device, without uploading data anywhere.
________________________
🚨 Common Risk Patterns With Online RAR Services
Online “open RAR” services tend to share the same core behaviors, even if their designs differ. Understanding these patterns makes it easier to decide when they’re simply not an option for you.
Typical risk patterns include:
- Opaque retention: The site claims your files are deleted “after some time,” but does not define how, where, or under what controls.
- Unclear jurisdiction: Servers may be in countries with different privacy laws, and data might cross borders without your knowledge.
- Advertising and tracking: Some services may monetize traffic with trackers and logs, indirectly connecting your encrypted archives to your profile.
- Security unknowns: No visibility into how files are stored, whether encryption is used at rest, or how backups are handled.
The article why online password tools fail for your protected RAR data ↗️ goes deeper into how promises like “we can open anything” often collide with cryptographic reality. Similarly, extract RAR files online without a password: why online tools are risky and safer offline methods ↗️ explains why the illusion of convenience can hide a serious long-term privacy cost.
In short: if the data in your archive would matter to you, your clients, or your employer, uploading it to a service that you cannot audit is almost never a responsible move.
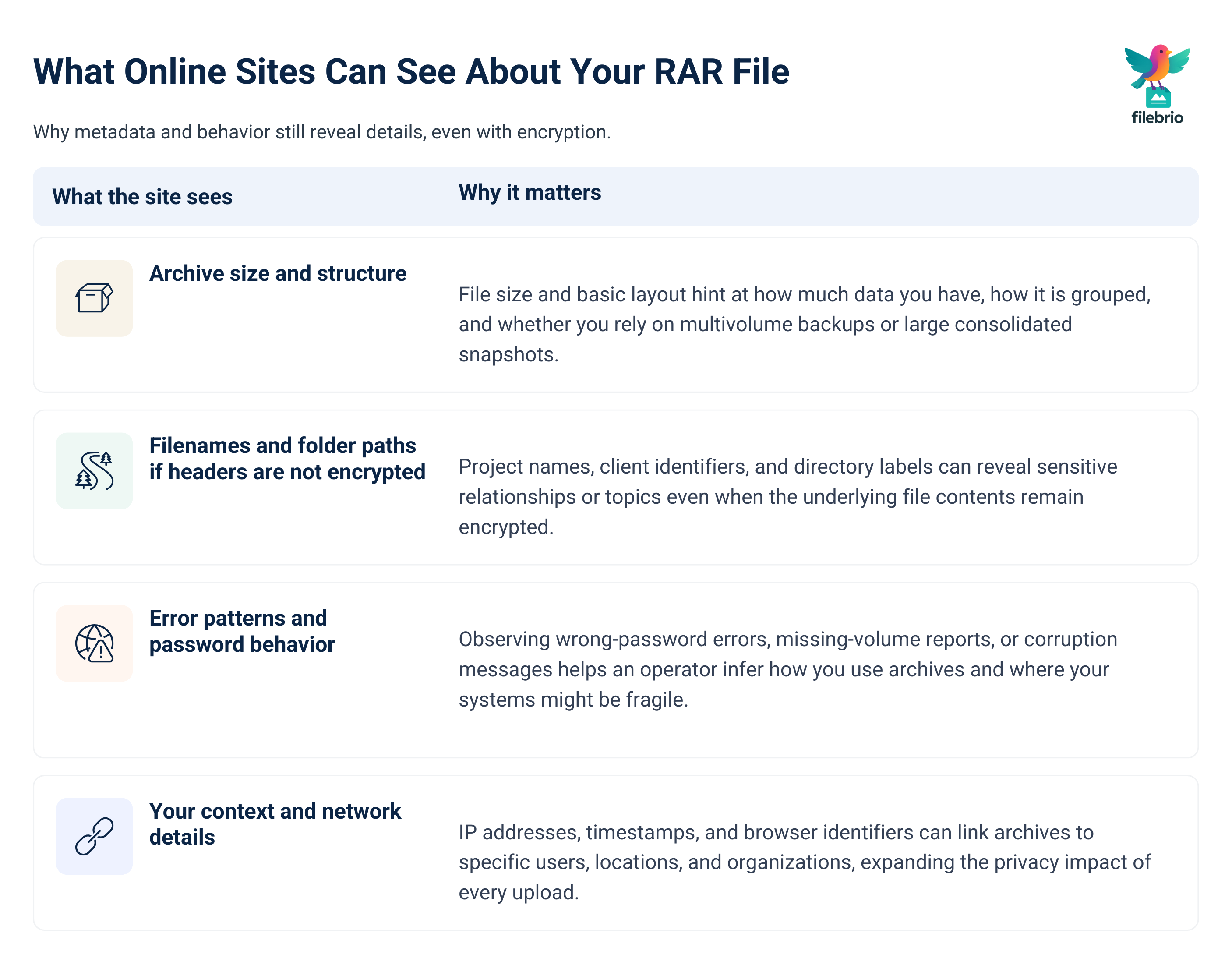
👁️ What Online Sites See When You Upload a RAR
Even if an online site never successfully opens your encrypted archive, it still sees more than you might expect once you hit “upload.” Depending on the archive’s configuration, a remote server may observe:
- File size and structure: Rough indicators of how much data you have and how it is packaged.
- Filenames and folder paths: If headers and filenames are not encrypted, project names or client identifiers may be visible.
- Error behavior: Whether passwords appear incorrect, volumes are missing, or corruption is detected.
High-level diagnostics like those described in how to assess safe access paths for your locked RAR file ↗️ are valuable — but they should be run locally. Every error message and structural clue you reveal to an online service can help someone build a picture of your archive, your habits, and your environment.
By keeping diagnostics offline, you can still learn what’s going wrong without giving an external party a detailed, timestamped snapshot of your data. That’s especially important when archives contain regulated or confidential information, where unsanctioned disclosure — even in encrypted form — might conflict with policies or contracts.
🧪 Safer Experiments: Use Dummy Archives, Not Real Data
When you’re unsure how a tool behaves, or you’re evaluating whether an offline workflow feels practical, you don’t need to experiment on real, sensitive archives. You can create dummy RAR files — archives filled with non-sensitive content — to test how different pieces of software handle opening, listing, and diagnostics.
As described in how to test RAR protection with your dummy files ↗️, this lets you:
- Measure performance and behavior on your own hardware without leaking private data.
- See what information a given tool or workflow reveals before any password is entered.
- Train yourself or colleagues on safe handling procedures using harmless test material.
Dummy archives are also a good way to compare offline and online behavior in a low-risk way. For example, you might notice that an online site logs your IP and keeps download links available for longer than you are comfortable with — even when the test archive contains nothing confidential. That alone can be enough to decide that real archives do not belong there.
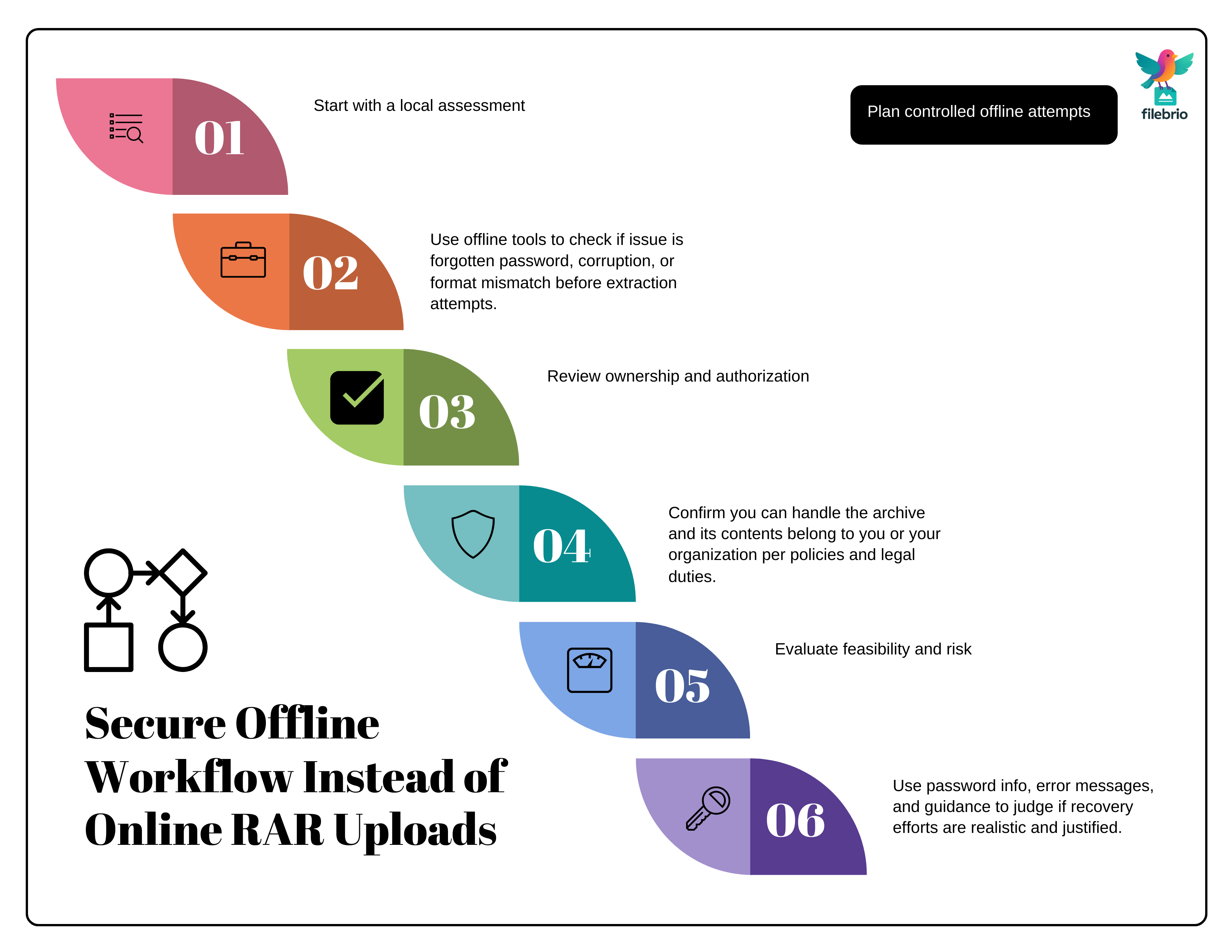
🛡️ Building a Secure Offline Workflow for Real RAR Files
Offline tools are safest when you use them inside a structured workflow: a sequence of steps you follow whenever you face a problematic archive. This reduces the chance you’ll panic and break your own rules in the moment.
A privacy-first offline workflow might look like this:
- Initial assessment: Use local tools to determine whether the problem is a forgotten password, corruption, or something else, following principles similar to ways to diagnose your unopened RAR file issue ↗️.
- Feasibility and safety: Combine what you know about the password with high-level guidance from how to assess safe access paths for your locked RAR file ↗️ before investing more effort.
- Controlled attempts: If you proceed, keep attempts and diagnostics on trusted machines only, with backups in place and clear stop conditions.
- Documentation: Record what you tried, what you observed, and any conclusions so you (or your organization) can review decisions later.
The broader approach in how to design a secure workflow for your encrypted files ↗️ is a useful model. It emphasizes that the safest workflows are those you can repeat calmly, under documented rules, without improvising under pressure or involving untrusted websites.
🧰 Privacy-First Suite for Everyday RAR Work
Once you commit to an offline strategy, it helps to standardize around a single, trusted toolkit. This makes training, documentation, and compliance much easier — especially if multiple people or departments occasionally deal with encrypted RAR archives.
FileBrio RAR Master is built to be that toolkit: a local environment where you can collect your RAR-related workflows in one place instead of depending on random utilities or websites. The FileBrio RAR Master features ↗️ overview shows how diagnostics, archive health checks, and responsible recovery modes come together.
Because it’s part of the FileBrio Office Suite, you can integrate it into a broader privacy policy that explicitly forbids uploading sensitive archives to third-party sites. When you’re ready to put this into practice, you can obtain the suite from the official FileBrio Office Suite download page ↗️ and roll it out on systems that are already under your control.
________________________
FileBrio RAR Master — a secure, offline Windows toolkit for regaining access to your own password-protected RAR / WinRAR archives while keeping all data strictly on your device.
- Offline-only processing — never uploads your archives.
- Smart issue detection — password vs corruption.
- Fast recovery workflow optimized for legitimate ownership.
⬇️ Download FileBrio RAR Master
Reminder: FileBrio RAR Master is intended only for archives you own or are explicitly authorized to access. All operations run locally on your PC.
________________________
🧯 Avoiding Common “Quick Fix” Mistakes
Most privacy incidents involving encrypted archives don’t start with malicious intent. They start with a frustrated user who wants a “quick fix” and believes that one upload won’t matter. Unfortunately, that one upload can matter a lot — especially when it involves corporate, legal, or personal archives that were never meant to leave your environment.
Some of the most common mistakes include:
- Uploading client or internal archives to web services without explicit approval.
- Sharing RAR files over unencrypted channels so others can “try different tools.”
- Trusting any site that promises to open “any RAR” regardless of encryption strength.
The patterns described in why online RAR password tools fail ↗️ highlight why these shortcuts are rarely worth the risk. They usually provide no better chance of access than a properly configured offline toolkit, but they massively increase your exposure.
By contrast, if you already have a documented offline workflow and a standard toolset, you’re far less likely to break your own rules. When you know there is a safe path — and you’ve rehearsed it with dummy archives — you aren’t tempted to gamble with online services just to “see what happens.”
📜 Ownership, Compliance, and When to Walk Away
Working offline protects privacy, but you still must respect legal and ethical boundaries. It’s critical to ensure that you only attempt diagnostics or recovery on archives you own or are explicitly authorized to manage.
Guidance like how to safely restore access to your locked RAR archive ↗️ and how to ensure you’re recovering only RAR files you own ↗️ helps frame this correctly. It’s not enough to have a technical method; you need clear rights to the data.
In some cases, the safest and most responsible choice is to accept that recovery is not feasible. If an archive uses strong encryption with a lost password, no offline or online tool can legitimately promise access. The limits described in the FileBrio RAR Master encrypted header warning and recovery limits ↗️ documentation are there to protect you from unrealistic expectations and from services that over-promise.
Part of a mature privacy and compliance posture is knowing when to stop — and documenting why. When you combine that judgment with an offline-first workflow, you can honestly say you did everything reasonable without exposing sensitive RAR archives to unnecessary risk.
⚖️ Legal Reminder
This article is provided for general informational and educational purposes only. Any examples, scenarios, or references to password recovery, archive security, or related tools (including FileBrio RAR Master or similar software) are intended solely to help you better understand how to protect and manage your own data.
You may only apply any techniques, workflows, or tools described here to files and archives that you fully own or are explicitly and verifiably authorized to access. Attempting to bypass, remove, or recover passwords for third-party data without clear permission may violate criminal law, civil law, or internal company policies in your jurisdiction.
Nothing in this article constitutes legal advice. Laws and regulations differ between countries and organizations, and you are solely responsible for ensuring that your actions comply with all applicable legislation, contracts, and internal policies. If you are unsure whether a particular action is lawful or permitted, consult a qualified legal professional before proceeding.
📚 See Also: Safer Options Around Online RAR Handling
- Why Online RAR Password Tools Fail — and What Legitimate Users Can Do Instead ↗️
- Extract RAR Files Online Without a Password: Why Online Tools Are Risky and Safer Offline Methods ↗️
- Open RAR Files Without a Password? What’s Possible, What Isn’t, and How to Access Your Data Safely ↗️
- Why Offline Recovery Tools Are Safer for Privacy ↗️
- How to Evaluate Safe Options for Regaining Access to a RAR/WinRAR Archive You Own ↗️
- Restoring Access to RAR/WinRAR Archives: Safe and Legal Methods for Handling Your Own Files ↗️