
Why Offline Recovery Tools Are Safer for Privacy
You lose access to an important RAR archive and search the web for help. Within seconds, you see dozens of sites promising to “open any RAR,” “remove any password,” or “unlock your archive online.” The offer is tempting: upload your file, wait a bit, and hope for the best. But behind that convenience is a serious question: who else gets a copy of your encrypted data — and what happens to it later?
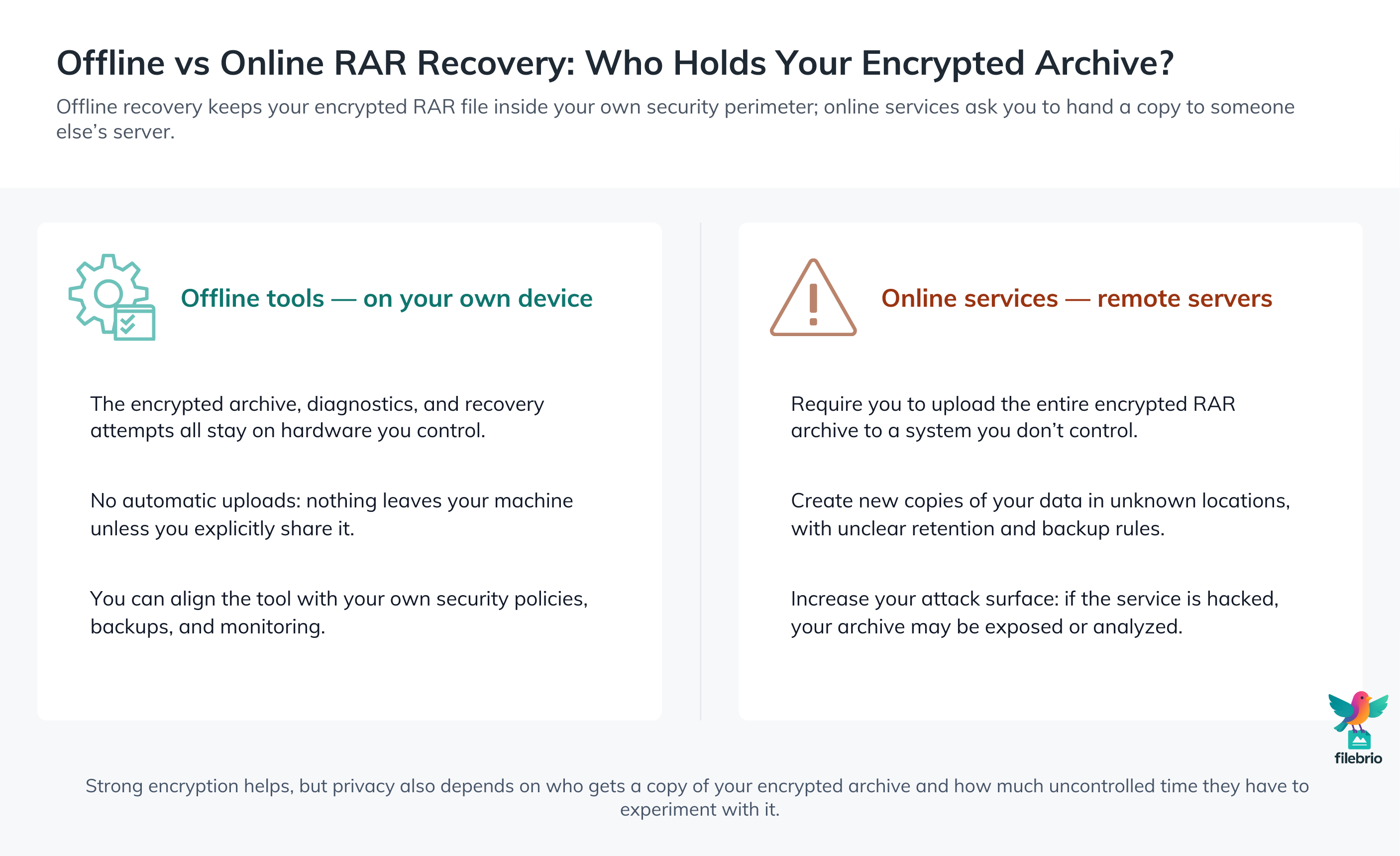
When you use online services, you give strangers everything they need to explore your confidential archives at their leisure: the encrypted file, metadata, and sometimes additional personal information. In contrast, offline recovery tools keep operations on your own device, under your control, with no third party involved. That difference is exactly why offline tools are almost always safer for privacy when you work with encrypted RAR archives you legitimately own.
This article explains what “offline vs online” really means, how RAR encryption interacts with privacy, why uploads are so risky, and how to build a safe, offline-first workflow that respects both security and legality.
🧭 Navigation
Important
The information provided in this article applies exclusively to RAR / WinRAR archives for which you have full, demonstrable ownership or properly documented authorization. If you are not the rightful owner of the data, do not directly control it, or cannot clearly prove permission to access it, you must stop immediately. Attempting to access, recover, or modify data without explicit authorization may violate criminal law, civil statutes, corporate compliance requirements, and privacy regulations in many jurisdictions. You alone are responsible for ensuring that your actions are lawful and properly permitted before proceeding.
✨ TL;DR — Why Offline Beats Online for RAR Privacy
Offline recovery tools keep everything on your own computer: the encrypted archive, any diagnostics, and any attempts you make to regain access. Nothing leaves your machine unless you choose to send it somewhere else. Online services work differently: to “help,” they typically require you to upload your entire encrypted RAR file — handing a copy of your private data to a server you don’t control, in a jurisdiction you may not even know.
From a privacy and security point of view, that upload is the main risk. Once your archive sits on a remote server, you can’t verify who has access, how long it is stored, whether it’s backed up, copied, or analyzed, or what will happen if that service is hacked years later. Even if the provider is honest, the platform itself becomes a new attack surface for your confidential files.
In contrast, offline tools let you:
- Keep encrypted archives and diagnostics under your direct control.
- Follow a repeatable, privacy-first workflow on devices you trust.
- Respect legal and contractual obligations that forbid third-party uploads.
The safest pattern is clear: analyze and attempt recovery offline, using tools you trust, and only on archives you own or are explicitly authorized to handle. Online services might look convenient, but they almost always trade convenience for privacy — sometimes in ways you only discover when it’s too late.
🌐 What “Offline vs Online” Really Means for RAR Recovery
“Offline” and “online” can sound like marketing terms, but in the context of RAR recovery they describe very concrete behaviors:
- Offline tools: Software installed on your own device. All operations — opening, analyzing, and attempting recovery — happen locally. The only data leaving your system is whatever you explicitly send.
- Online services: Websites or cloud platforms that ask you to upload your RAR file. The recovery logic runs on their servers, and your archive is stored and processed elsewhere.
That difference matters because encrypted RAR archives often contain complete snapshots of your life or work: projects, personal photos, financial records, internal documents, or client data. Uploading that bundle of information, even in encrypted form, expands the number of places where copies can exist.
To understand why this is risky, it helps to review why your forgotten RAR password cannot be reset ↗️. RAR encryption is designed so that, without your password, the contents should remain opaque. But opacity is not the same as invisibility: files, filenames, metadata, and archive structure may still reveal sensitive patterns, depending on how the archive was created.
When you keep everything offline, only your own system ever sees those patterns. When you upload the archive, you grant a third party the opportunity to analyze and store them — even if they never manage to open the archive itself.
🧠 How RAR Encryption and Passwords Interact With Privacy
At a cryptographic level, modern RAR formats can be very strong. As explained in how RAR4 and RAR5 secure your protected data ↗️, RAR can combine modern ciphers, key-derivation functions, and optional header encryption to keep unauthorized users out.
However, privacy is not just a technical property; it’s also about who gets the chance to try things, for how long, and with what data. A few key points:
- Password quality still matters. Weak or reused passwords make attacks easier, even if the algorithm itself is strong.
- Metadata can leak clues. When headers or filenames are not encrypted, visible names or structure can reveal more than you expect.
- Access to the archive is a resource. Every copy of your encrypted file is another opportunity for someone to try to access it in ways you can’t see.
That’s why privacy discussions often focus on who holds the encrypted data, not just on how it’s encrypted. You can use the ideas in how to interpret timing estimates for your RAR password ↗️ to understand the difficulty of guessing a strong password in theory — but the moment you hand your archive to an unknown server, you lose control over how much computation and time that server might spend trying to open it.
Offline tools don’t magically make encryption stronger; they make your risk smaller by limiting who has a copy of the encrypted material and by keeping all recovery attempts inside your own security perimeter.
🧰 All-In-One Offline Toolkit for Safe RAR Diagnostics
To make offline recovery realistic, you need more than a single “open file” button. You need a structured environment where diagnostics, feasibility checks, and safe workflows are all available without leaving your machine.
FileBrio RAR Master, as part of the FileBrio Office Suite, is designed exactly for this offline-first approach. Instead of scattering your data across multiple utilities and services, you can rely on an offline vs online RAR recovery ↗️ comparison built into a single toolkit that:
- Analyzes your archive format and basic health locally.
- Helps you assess whether safe recovery is realistic before investing time.
- Maintains all operations on your own device, with no uploads to third-party servers.
This “all-in-one” design is not just convenient; it’s a privacy feature. When every diagnostic step and recovery attempt happens in one audited, offline application, it’s easier to implement a policy that forbids uploading sensitive archives to external tools — and easier to train others to follow it.
________________________
FileBrio RAR Master — part of the FileBrio Office Suite — is a privacy-first, offline Windows toolkit for diagnosing and safely regaining access to your own password-protected RAR / WinRAR archives.
- Local processing only — nothing leaves your PC.
- Smart diagnostics to separate password issues from corruption.
- Owner-verified recovery workflows designed strictly for legitimate use.
Reminder: FileBrio RAR Master may be used only with archives you own or are explicitly authorized to access. It performs all analysis and recovery operations locally on your device, without uploading data anywhere.
________________________
🚨 Typical Risk Patterns With Online RAR Recovery Websites
Online RAR recovery sites often look harmless: a simple upload form, a reassuring sentence about “security,” and a promise of quick results. But several common patterns make them risky, especially for confidential or regulated data.
Typical red flags include:
- Vague retention policies: No clear statement about how long your file is stored or how it’s deleted.
- Lack of jurisdiction clarity: Servers may be in countries with very different privacy laws.
- Advertising-based models: Incentives may favor collecting and profiling data rather than minimizing it.
To see how these risks play out in practice, consider the scenarios discussed in why online extraction threatens your protected RAR data ↗️ and why opening RAR files online risks your protected data ↗️. Both highlight the same theme: whenever you upload an archive to a third-party service, you create a new, uncontrollable copy of highly concentrated information.
Even services that claim to “delete everything after 24 hours” require you to trust their implementation, logging, and backup policies. If the stakes are high — personal identity documents, client projects, legal archives — that level of blind trust is rarely acceptable.
Offline tools avoid these risk patterns entirely by design. There is no upload, no shared server, and no hidden retention; the only copies of your archive are the ones you create and store yourself.

👁️ What Offline Tools Can See (and What They Don’t Transmit)
A natural question is: “If an offline tool can analyze my encrypted RAR file, doesn’t that still expose something?” The answer is that the tool does see whatever your local system sees — but the crucial difference is that this information never needs to leave your device.
For example, a privacy-focused offline toolkit can help you:
- Check whether the archive appears structurally healthy or corrupted.
- Confirm if headers or filenames are encrypted.
- Run high-level feasibility and timing estimates for legitimate access attempts.
Because all of this happens locally, you can combine these diagnostics with safe workflows such as how to assess safe access paths for your locked RAR file ↗️. You keep control over logs, temporary files, and system access, and you can integrate the tool within your own security policies, VPNs, and backup strategies.
In other words, offline tools do not magically know less about your archive — they simply share less. That reduction in sharing is exactly what improves privacy: fewer external entities see your files, fewer systems hold copies, and fewer unknown variables exist in your threat model.
🧪 Using Dummy Archives to Test Privacy-Safe Workflows
If you’re changing how you handle encrypted RAR files, you shouldn’t start by experimenting on your only copy of an important archive. A much safer way is to use dummy archives — test RAR files that contain only non-sensitive content — to explore your offline workflows first.
As described in how to test RAR protection with your dummy files ↗️, dummy archives let you:
- Practice your offline diagnostics and recovery steps with zero privacy risk.
- Measure approximate performance and behavior of your tools on your own hardware.
- Train colleagues on the standard process without ever exposing real data.
Dummy archives are particularly useful if you are tempted by online services. You can compare the experience: once you see how easily an offline toolkit can handle basic diagnostics and high-level feasibility checks, the “need” to upload real encrypted archives often disappears.
By the time you apply your workflow to a real archive you own, you will have rehearsed each step in a controlled environment, with clear expectations and documented procedures.

🛡️ Secure Offline Workflow for Real RAR Archives
Offline tools are safest when they operate inside an equally careful offline workflow. The goal is to treat every encrypted RAR archive as a sensitive object whose privacy and integrity must be preserved throughout its lifecycle.
A typical offline-first pattern might look like this:
- Initial assessment: Use local tools to confirm archive health and determine whether you’re dealing with a forgotten password, corruption, or both — following ideas similar to those in how to evaluate your situation after losing your RAR password ↗️.
- Feasibility evaluation: Before any intensive attempts, use high-level estimates and your password habits to judge whether access is realistically recoverable and lawful.
- Controlled attempts: If you proceed, keep all operations on trusted machines, with logs and backups under your control, and stop if the effort no longer makes sense.
Throughout this process, a dedicated suite like FileBrio RAR Master lets you keep diagnostics, attempts, and results in one place, entirely offline. To align this with your organization’s policies and responsibilities, you can consult the responsible recovery guidelines ↗️ that frame how the software should be used ethically and legally on archives you own or administer.
________________________
FileBrio RAR Master — a secure, offline Windows toolkit for regaining access to your own password-protected RAR / WinRAR archives while keeping all data strictly on your device.
- Offline-only processing — never uploads your archives.
- Smart issue detection — password vs corruption.
- Fast recovery workflow optimized for legitimate ownership.
⬇️ Download FileBrio RAR Master
Reminder: FileBrio RAR Master is intended only for archives you own or are explicitly authorized to access. All operations run locally on your PC.
________________________
🧯 Avoiding Common Mistakes That Expose Encrypted Archives
Many privacy incidents around encrypted RAR files are not caused by advanced attacks; they’re caused by rushed decisions. When someone is locked out of an archive, panic and urgency can lead to shortcuts that seemed unthinkable when the archive was created.
Typical mistakes include:
- Uploading highly sensitive archives to unknown sites “just this once.”
- Sharing copies of encrypted files through unsecured channels for “help.”
- Using untrusted software downloaded from random sources without verification.
These patterns are explored in why online password tools fail for your protected RAR data ↗️, which highlights how shortcuts can create more risk than they solve. A simple rule of thumb helps: if you wouldn’t email the contents of an archive in plain text, you probably shouldn’t upload the encrypted archive to an unknown service either.
Offline recovery tools make it easier to avoid these mistakes because they give you a credible alternative. When you have a documented, offline process and trusted software in place, you don’t need to improvise under pressure — you simply follow the procedure you’ve already tested.
📜 Ownership, Documentation, and Long-Term Access
Privacy and legality are closely linked. Working offline helps you protect your data, but you must still ensure that your actions are limited to archives you own or are clearly authorized to manage.
For personal use, that means being honest about which archives belong to you and which might have come from others. For business use, it often means having policies and records that prove you are acting within your role. Guidance such as how to safely restore access to your locked RAR archive ↗️ and how to ensure you’re recovering only RAR files you own ↗️ can help you frame your actions responsibly.
From a long-term perspective, you should also consider how offline workflows interact with password policies, metadata, and archive inventories. If, years from now, someone needs to assess safe options again, they should be able to combine privacy-first guidance like this article with structured decision-making processes similar to those in how to assess safe access paths for your locked RAR file ↗️.
Good documentation — what the archive is, who owns it, how it was created, and where it may lawfully be opened — is as much a part of privacy as encryption itself. Offline tools then become the mechanism by which you respect that documentation and keep sensitive archives within the boundaries you’ve defined.
⚖️ Legal Reminder
This article is provided for general informational and educational purposes only. Any examples, scenarios, or references to password recovery, archive security, or related tools (including FileBrio RAR Master or similar software) are intended solely to help you better understand how to protect and manage your own data.
You may only apply any techniques, workflows, or tools described here to files and archives that you fully own or are explicitly and verifiably authorized to access. Attempting to bypass, remove, or recover passwords for third-party data without clear permission may violate criminal law, civil law, or internal company policies in your jurisdiction.
Nothing in this article constitutes legal advice. Laws and regulations differ between countries and organizations, and you are solely responsible for ensuring that your actions comply with all applicable legislation, contracts, and internal policies. If you are unsure whether a particular action is lawful or permitted, consult a qualified legal professional before proceeding.
📚 See Also: Safer Options for Accessing Your Own RAR Files
- Free RAR/WinRAR Password Recovery Tools: Safe, Offline Options for Accessing Your Own Files ↗️
- Online RAR/WinRAR Unlockers: Hidden Risks and Why Local Tools Offer Better Security ↗️
- Decrypting RAR/WinRAR Passwords Online: Privacy Risks and Better Local Alternatives ↗️
- Unlocking Password-Protected RAR/WinRAR Archives: Safe Methods for Legitimate Access ↗️
- Lost Your RAR/WinRAR Password? How to Assess Your Situation Before Taking Action ↗️