
Legal and Ethical Guidelines for Working With Password-Protected Files
When you work with password-protected files — especially encrypted RAR or WinRAR archives — the real challenge is rarely technical alone. It’s a mix of security design, ownership clarity, legal boundaries, and practical decision-making. Strong encryption exists to keep sensitive data safe, but that same protection can create obstacles when an authorized user loses access or when an archive becomes corrupted.
This guide explains how to approach such situations responsibly: what “legitimate access” actually means, how to diagnose issues without causing harm, which recovery paths are lawful and safe, and how to prevent lockouts in the future. Throughout the article, you’ll also see where professional tools and structured workflows can help — without crossing ethical or legal lines.
🧭 Navigation
Important
The information provided in this article applies exclusively to RAR / WinRAR archives for which you have full, demonstrable ownership or properly documented authorization. If you are not the rightful owner of the data, do not directly control it, or cannot clearly prove permission to access it, you must stop immediately. Attempting to access, recover, or modify data without explicit authorization may violate criminal law, civil statutes, corporate compliance requirements, and privacy regulations in many jurisdictions. You alone are responsible for ensuring that your actions are lawful and properly permitted before proceeding.
⚖️ TL;DR — Legal & Ethical Big Picture
Password protection exists to defend data, not to get in your way. When you’re locked out of your own RAR archive or another encrypted file, it’s natural to search for “ways back in,” but the law and basic ethics draw a clear line: you may only work on files you legitimately own or are clearly authorized to access. Anything else can be illegal, even if the tools look simple or “automatic.”
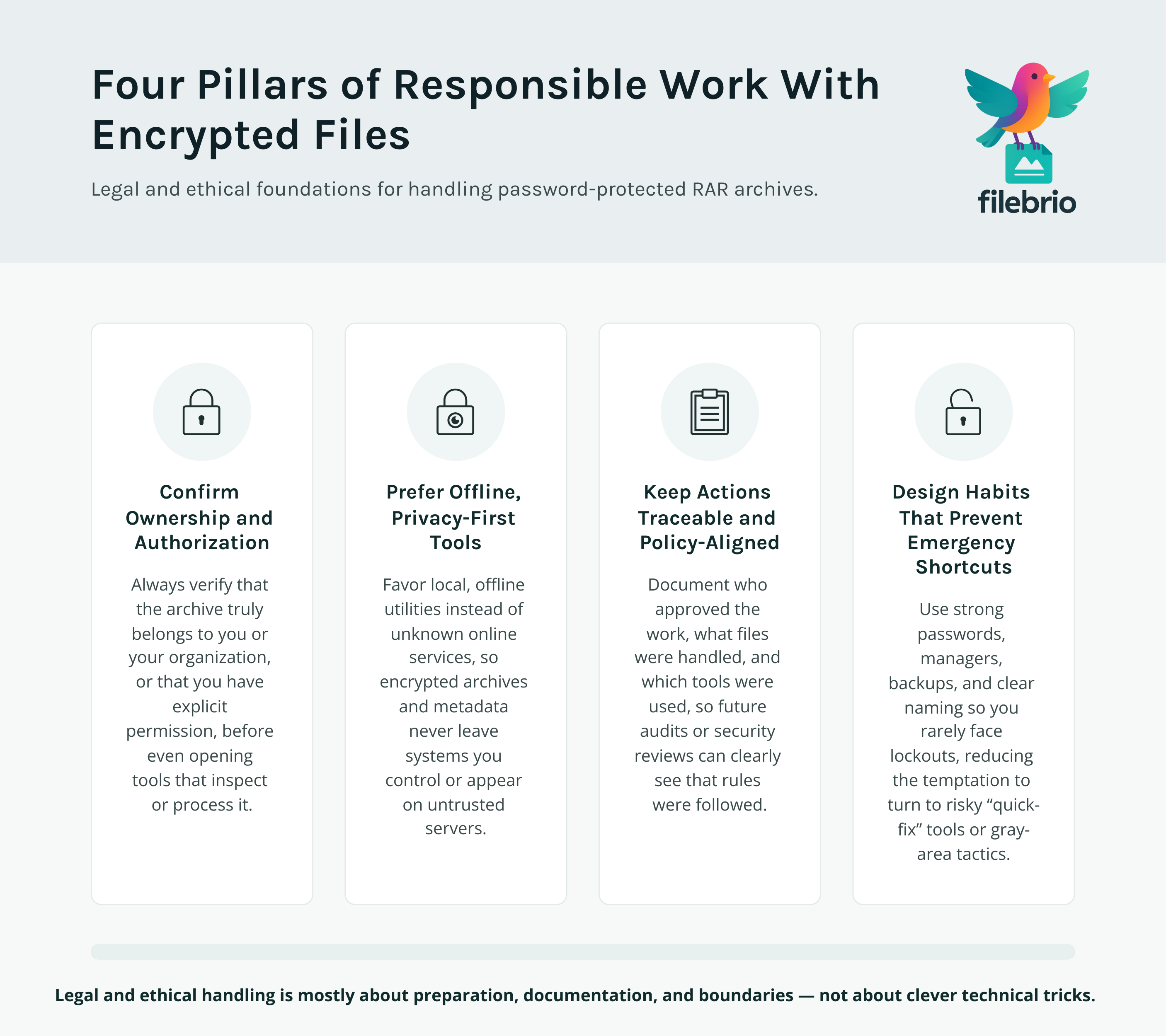
In practice, responsible handling of password-protected files means four things:
- Always confirm ownership and authorization before you touch an encrypted file.
- Favor offline, local tools that respect privacy over unknown online services.
- Keep your actions traceable, documented, and aligned with workplace policies.
- Design your own password and archive habits so you don’t need risky “rescue” steps later.
This article walks through how to think about ownership, diagnostics, safe recovery, legal frameworks, and long-term protection without crossing into step-by-step attack instructions or unsafe behavior.
🧠 Understanding Password-Protected Files & RAR Encryption
“Password-protected file” is a broad term. It covers RAR and WinRAR archives, but also ZIP, 7z, office documents, disk containers, and more. While the exact cryptographic design differs between formats, the legal and ethical issues are similar: encryption exists to strictly limit who can access the data.
Modern RAR (especially RAR5) uses strong encryption. When a password is set correctly, there is no hidden “reset link,” backdoor account, or master key held by the software vendor. That’s intentional. It’s what protects sensitive documents, backups, or corporate archives if a device is lost.
From a legal and ethical perspective, this implies:
- If you are legitimately authorized, forgetting a password is primarily a usability problem, not a signal that security is weak.
- If you are not authorized, trying to defeat protection is not “just a technical puzzle” — it may be an attempt to bypass access control and can be treated similarly to breaking into a locked room.
- Tools that work with encrypted RAR files must respect this boundary and encourage responsible use only for your own data or data you are clearly entrusted with.
Because encryption is designed to be resilient, there are also hard mathematical limits: some archives will be unrecoverable if passwords are too long and random, or if critical metadata is missing. Part of ethical behavior is recognizing those limits and not promising miracles that contradict them.
📁 Clarifying Ownership and Legitimate Intent
Before you even open a password-recovery or diagnostic tool, one question matters more than any technical detail: do you have the right to work with this archive or file?
For personal use, that might be straightforward — you created the RAR archive on your own computer, or someone explicitly sent it to you along with a password. In shared or corporate environments, things can be more complex: you may be acting on behalf of a team, a department, or a client. In those cases, documenting that relationship is important.
High-level steps that help clarify ownership and intent include:
- Keeping a record of who created an archive and for which project or purpose.
- Storing passwords or password metadata in secure managers, so lockouts are less likely.
- Using written authorization (emails, tickets, internal approvals) when you work with archives owned by a company or client.
- Separating “curiosity” from legitimate work: you should never test your skills on data that doesn’t belong to you.
If you’re unsure how to diagnose a locked archive without risking harm, you can follow safe preliminary checks described in resources such as safe approaches to diagnosing your protected archive ↗️, which focus on non-destructive inspection rather than aggressive attempts.
In more sensitive contexts, you may also need to prove that you are working only on files you own or administer. Guidance like checks to ensure you’re working with your own RAR files ↗️ and steps to record ownership of your protected archives ↗️ can help formalize this process so that your actions are clearly legitimate.

🧪 Diagnosing Your Situation Without Crossing Lines
When a password-protected archive refuses to open, there are several distinct possibilities:
- The password is simply wrong or no longer remembered.
- The archive is partially corrupted (disk, transfer, or storage issues).
- The archive format changed or is misinterpreted by the software you’re using.
- The file was never actually what you thought it was (misnamed or replaced).
Ethical diagnostics focus on safe observation rather than “trying everything.” The goal is to answer questions like “Is this really a RAR file?”, “Is it structurally intact?” and “Is there obvious corruption?” before touching the password at all.
Good practices include:
- Working only on copies of the original file to preserve evidence and reduce risk of damage.
- Checking metadata, headers, and error messages instead of immediately jumping to password attempts.
- Avoiding any tools that rewrite the archive unless you fully understand what they do.
- Keeping a simple log of what you’ve tried so that future experts aren’t troubleshooting in the dark.
In corporate workflows, it’s often helpful to align diagnostics with wider data-protection practices, such as those discussed in practices that preserve security for your encrypted corporate files ↗️. This helps ensure that even when troubleshooting, you are not accidentally weakening security controls or exposing sensitive information.
💼 All-In-One Safe Toolkit for Protected Archives (Commercial Overview)
Once you’ve confirmed that you are working with your own data and have a legitimate reason to access it, you need tools that are technically capable and designed with legal and ethical safeguards in mind.
FileBrio RAR Master is part of the FileBrio Office Suite and focuses on exactly this scenario: you have your own password-protected or damaged RAR/WinRAR archives, you want to understand what went wrong, and you need to explore recovery options without sending confidential data to the cloud.
At a high level, it is built around three priorities:
- Privacy-first processing — all analysis and operations are performed locally on your machine.
- Transparency — clear diagnostics, readable error messages, and health indicators, instead of opaque “magic” claims.
- Responsible use — workflows and documentation that repeatedly emphasize legitimate ownership and compliance.
Compared to generic utilities, an integrated toolkit helps you stay within safe boundaries:
| Need | Risky Approach | Safer Approach |
|---|---|---|
| Check why a RAR file won’t open | Upload archive to random websites promising “instant unlock” | Use local diagnostics and structured checks on your own machine |
| Understand technical limits | Rely on vague forum posts with no legal context | Use tools that explain feasibility, limits, and responsibilities |
| Maintain compliance | No record of who accessed what, when, and why | Documented, policy-aware workflows tied to your own environment |
If you want to see how this fits into a broader feature set, you can review the all-in-one RAR recovery toolkit ↗️ overview, which describes how diagnostics, repair, and password-related features are grouped with safeguards in mind.
________________________
FileBrio RAR Master — part of the FileBrio Office Suite — is a privacy-first, offline Windows toolkit for diagnosing and safely regaining access to your own password-protected RAR / WinRAR archives.
- Local processing only — nothing leaves your PC.
- Smart diagnostics to separate password issues from corruption.
- Owner-verified recovery workflows designed strictly for legitimate use.
Reminder: FileBrio RAR Master may be used only with archives you own or are explicitly authorized to access. It performs all analysis and recovery operations locally on your device, without uploading data anywhere.
________________________
🛡️ Safe and Lawful Recovery Options for Your Own Files
Once diagnostics confirm that the file is indeed a RAR archive and that the problem is likely related to a missing password or corruption, you have to decide how far you can legitimately and realistically go.
Responsible recovery focuses on your own archives and respects three constraints:
- Legal constraints: local laws and contracts may prohibit attempts on data you don’t own, even if you technically could try.
- Technical constraints: extremely strong passwords and encrypted headers may make recovery mathematically infeasible.
- Operational constraints: corporate compliance rules, audit trails, and data-protection frameworks may limit what is allowed.
In a lawful, privacy-respecting approach, you might:
- Use structured memory techniques and context cues (for example, what project, date, or naming pattern the archive relates to) rather than random guessing.
- Run feasibility estimates to understand whether attempted recovery is realistic or simply a waste of time and energy.
- Rely on local tools that explicitly avoid sending sensitive archives over the network.
When there is doubt about legality or contractual permissions, the correct next step is not “try anyway,” but stop and ask — management, legal, or data-protection officers can clarify what you are allowed to do. Working with encrypted archives is often intertwined with regulatory regimes and contractual obligations, especially in regulated industries.
📜 Legal and Compliance Considerations in Everyday Use
In many regions, breaking technical access controls without authorization can be considered a criminal act, regardless of whether you ultimately read the data. The key decision point is consent and authorization, not just whether you possess the file.
Some practical compliance-oriented habits include:
- Policy alignment: make sure your actions match internal policies for handling encrypted data, backups, and incident response.
- Minimal access: only attempt access to the smallest necessary set of files; don’t bulk-process archives “just in case.”
- Documentation: keep simple records — who authorized the work, what tools were used, and what the intended outcome is.
- Data minimization: avoid duplicating archives unnecessarily across devices or third-party services.
If your organization provides a central workflow for encrypted archives, such as data-classification labels or designated custodians, follow those routes first. When in doubt, it is better to escalate questions than improvise, especially in industries subject to audits.
When you need to interpret rules and responsibilities for encrypted archives in a broader legal context, high-level guidance like guidelines for privacy-first workflows for your encrypted files ↗️ can help you frame your internal policies around principle-based thinking rather than ad-hoc reactions.
🔐 Building Strong Protection While Staying Accessible
Legal and ethical problems often arise because archives were protected “just enough to be annoying,” not thoughtfully designed for long-term use. The safest situation is when your protection is strong, but your future self and authorized colleagues can still access the data without extreme measures.
Core ideas:
- Use robust encryption modes: modern RAR5 with encryption enabled is a good default for sensitive data.
- Choose high-entropy passwords: length and randomness matter — but balance that with memorability and secure storage.
- Rely on secure password managers: these tools are far safer than relying solely on memory for critical archives.
- Maintain backups: properly stored backups reduce temptation to use questionable services if one copy becomes inaccessible.
- Store context, not just secrets: date, project name, and a safe hint can be invaluable when reconstructing legitimate passwords later.
From an ethical standpoint, designing good security today means you are less likely to resort to risky “emergency” behaviors later — like uploading archives to unknown sites or letting unvetted tools scan entire folders of confidential data. Good hygiene is both a security measure and a way to prevent future ethical dilemmas.
🖥️ Secure Offline Solution for Teams and Organizations (Commercial Block)
Teams and enterprises face a more complex reality: rotating staff, multiple devices, shared archives, audits, and strict confidentiality requirements. When encrypted archives become inaccessible, it isn’t just an inconvenience — it can impact projects, regulatory timelines, or clients.
In this context, tools and workflows must satisfy both IT security and compliance stakeholders. That’s where a dedicated, offline-focused suite like FileBrio Office Suite with FileBrio RAR Master fits in.
Compared with ad-hoc tools, a structured solution can help you:
- Centralize practices: standardize how diagnostics and recovery feasibility checks are performed.
- Respect chain of custody: keep all operations local, with logs that align with your internal processes.
- Avoid risky uploads: there is no reason to send sensitive archives to third parties when offline options exist.
- Educate users: use built-in materials and documentation to help staff understand limits and responsibilities.
In many organizations, the right approach combines clear policies with appropriate tooling and guidance on safe, offline methods such as why offline tools keep your encrypted RAR data private ↗️. This reduces the temptation to rely on untrusted “quick fixes” and supports compliance across teams.
________________________
FileBrio RAR Master — a secure, offline Windows toolkit for regaining access to your own password-protected RAR / WinRAR archives while keeping all data strictly on your device.
- Offline-only processing — never uploads your archives.
- Smart issue detection — password vs corruption.
- Fast recovery workflow optimized for legitimate ownership.
⬇️ Download FileBrio RAR Master
Reminder: FileBrio RAR Master is intended only for archives you own or are explicitly authorized to access. All operations run locally on your PC.
________________________
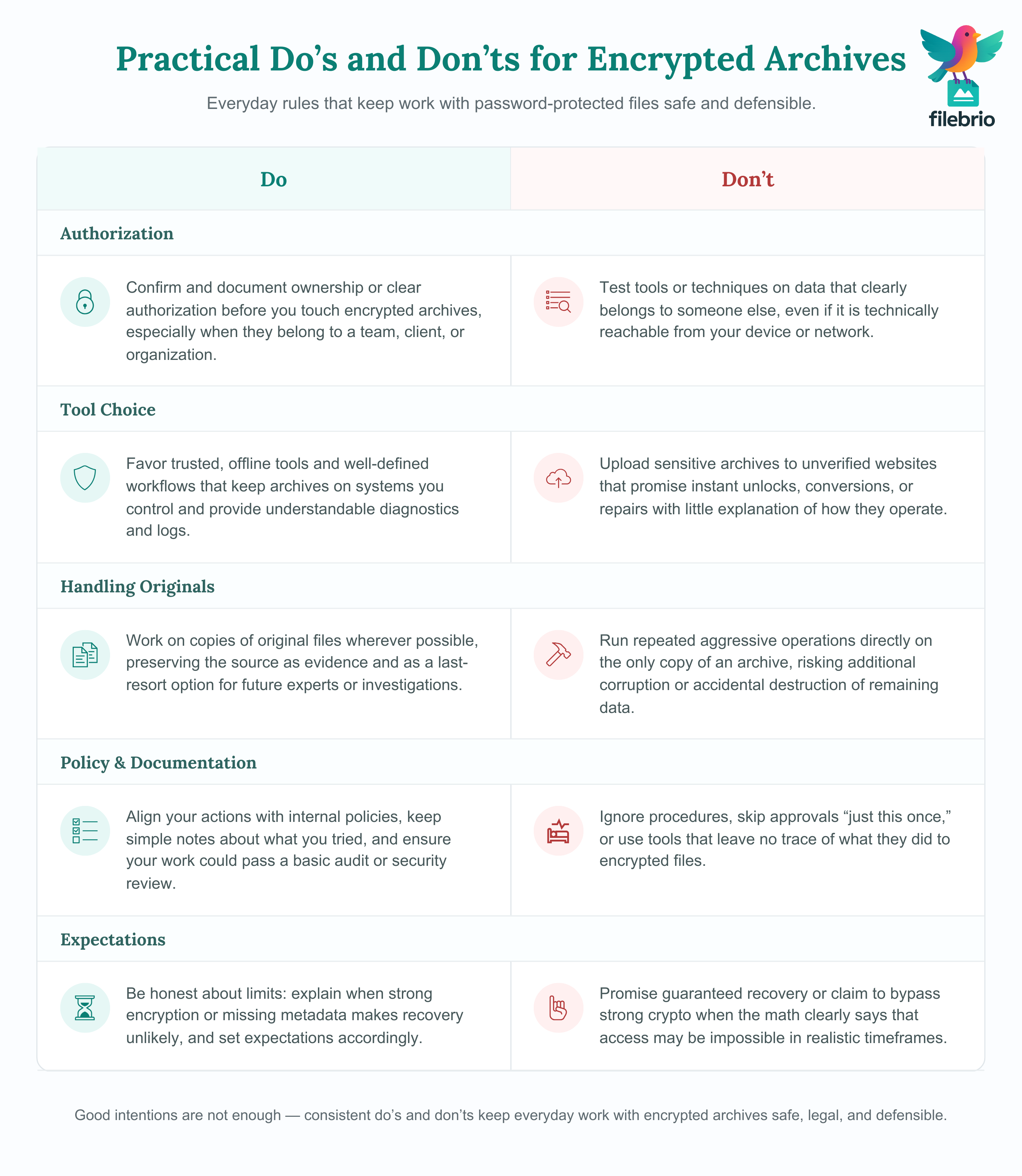
✅ Practical Guidelines & Common Mistakes to Avoid
Even well-intentioned users can drift into unsafe territory if they lack clear guidelines. Here are practical do’s and don’ts that help keep your behavior aligned with legal and ethical expectations.
Do:
- Confirm and document ownership or clear authorization before you touch encrypted archives.
- Work on copies of original files, preserving the source for evidence and future experts.
- Favor trusted, offline tools and well-defined workflows over random utilities found online.
- Use password managers and documented metadata so you don’t need emergency “recovery” for every single archive.
- Educate colleagues about the limits of what’s realistically possible with strong encryption.
Don’t:
- Test tools or techniques on data that doesn’t belong to you, even if it is technically accessible.
- Upload sensitive archives to unverified sites that claim to unlock, convert, or “fix” anything instantly.
- Ignore internal policies or skip authorization steps “just this once.”
- Promise full recovery when the math says a password is essentially unguessable.
- Rely on tools that hide what they are doing or provide no audit trail.
Many problems arise from simple, repeated errors — for example, sending private archives to low-quality online services or trying to “experiment” on production data. Overviews such as common missteps when handling your passworded RAR archive ↗️ show how easily good intentions can lead to risky behavior.
If you need additional assurance that your approach is in line with responsible vendor guidance, check resources like the FileBrio support and policy section, including responsible recovery guidelines ↗️, which focuses on lawful, well-documented use.
For those who want a single, privacy-centered toolset that aligns with these guidelines, the broader compare online unlockers and local tools ↗️ overview explains how an offline-first strategy can reduce risk. When you’re ready to equip your own workstation, you can get FileBrio RAR Master ↗️ as part of the FileBrio Office Suite rather than relying on scattered utilities.
🧾 Legal Reminder & When to Involve Professionals
Legal obligations around encrypted data vary between jurisdictions and industries, and they can change over time. That’s why high-level principles in this article are not a substitute for proper legal advice or for your organization’s own compliance frameworks.
This article is provided for general informational and educational purposes only. Any examples, scenarios, or references to password recovery, archive security, or related tools (including FileBrio RAR Master or similar software) are intended solely to help you better understand how to protect and manage your own data.
You may only apply any techniques, workflows, or tools described here to files and archives that you fully own or are explicitly and verifiably authorized to access. Attempting to bypass, remove, or recover passwords for third-party data without clear permission may violate criminal law, civil law, or internal company policies in your jurisdiction.
Nothing in this article constitutes legal advice. Laws and regulations differ between countries and organizations, and you are solely responsible for ensuring that your actions comply with all applicable legislation, contracts, and internal policies. If you are unsure whether a particular action is lawful or permitted, consult a qualified legal professional before proceeding.
As a rule of thumb, you should consider involving legal or compliance professionals when:
- You are handling archives that contain regulated data (for example, health, financial, or personal records).
- Ownership or authorization is disputed, unclear, or split across multiple entities.
- You need to demonstrate due diligence to auditors, regulators, or external partners.
- The archive originates from an incident (lost laptop, departed employee, contractual dispute) rather than normal day-to-day work.
At the same time, involving technical experts can be useful when you need an honest feasibility assessment — including a candid explanation that some archives are simply unrecoverable. A responsible vendor or consultant should clearly explain these limits, not oversell capabilities.
🔗 See Also: Learn More About Safe RAR Use
- Legal Considerations When Working With Your Own Encrypted Archives ↗️
- How to Prove Ownership of a RAR Archive in Corporate Environments ↗️
- How to Strengthen RAR Archive Security While Preserving Future Access ↗️
- RAR/WinRAR File Passwords Explained: How Encrypted Archives Work and What Access Options You Have ↗️
- How to Safely Evaluate RAR Protection Using Dummy Archives ↗️