
Known-Plaintext Concepts and What They Reveal About RAR Security Models
If you have an old RAR archive with sensitive data and keep seeing the phrase “known-plaintext attack” in security articles, it is natural to wonder: does this mean my archive is vulnerable, or that someone can easily guess my password? In practice, RAR’s modern encryption design makes real-world abuse of known-plaintext ideas extremely limited — especially when you choose a strong password and handle the archive responsibly.
This article explains, in high-level terms, what known-plaintext actually is, how it fits into RAR4 and RAR5 security models, and how you can use the same concepts safely to better understand, test, and harden protection on your own archives.
🧭 Navigation
Important
The information provided in this article applies exclusively to RAR / WinRAR archives for which you have full, demonstrable ownership or properly documented authorization. If you are not the rightful owner of the data, do not directly control it, or cannot clearly prove permission to access it, you must stop immediately. Attempting to access, recover, or modify data without explicit authorization may violate criminal law, civil statutes, corporate compliance requirements, and privacy regulations in many jurisdictions. You alone are responsible for ensuring that your actions are lawful and properly permitted before proceeding.
🧾 TL;DR — Known-Plaintext and RAR in Plain Language
“Known-plaintext” means an attacker knows (or can reliably guess) some original content inside an encrypted file and compares it to its ciphertext. In some older or weakly designed systems, this can reveal information about keys or structure.
Modern RAR encryption (especially RAR5 with strong passwords) is built to resist this kind of analysis. For your own archives, thinking in known-plaintext terms is still useful — not to “attack” anything, but to:
- Understand how much predictable data might exist inside your RAR archive.
- Evaluate whether your password and settings match the sensitivity of the data.
- Design safer workflows using dummy test archives instead of real, sensitive content.
- Plan strong passwords and long-term access without exposing files to risky tools or online services.
This article stays strictly high-level and focuses on safe, lawful use for RAR archives you own or are explicitly responsible for.
🧠 Understanding Known-Plaintext at a High Level
In cryptography, a “known-plaintext scenario” exists when someone can see both:
- The encrypted data (ciphertext), and
- The original, unencrypted data (plaintext) for at least some part of that ciphertext.
Classic examples include predictable file headers (like “PK” for ZIP, magic bytes for images, or common document templates) or situations where the attacker has access to the same message both before and after encryption. The question cryptographers ask is: can this extra knowledge be used to derive more information about the key or about the rest of the encrypted data?
Good modern encryption schemes are designed assuming attackers will have some known plaintext. The security model treats this as normal, not exceptional. RAR’s use of strong ciphers and key-derivation functions follows the same principle: even if part of the content is guessable, the system should not leak meaningful shortcuts to the key.
For everyday users, the important takeaway is that “known-plaintext” is a theoretical lens used by cryptographers to stress-test algorithms. It does not automatically mean that someone who knows the first few bytes of your document can easily recover your RAR password.
🔐 How RAR Encryption Models Limit Known-Plaintext Impact
RAR archives use strong, modern building blocks. RAR4 and especially RAR5 are designed with the assumption that an attacker might know or guess parts of the contents. Instead of relying on secrecy of the format, they rely on cryptographic strength.
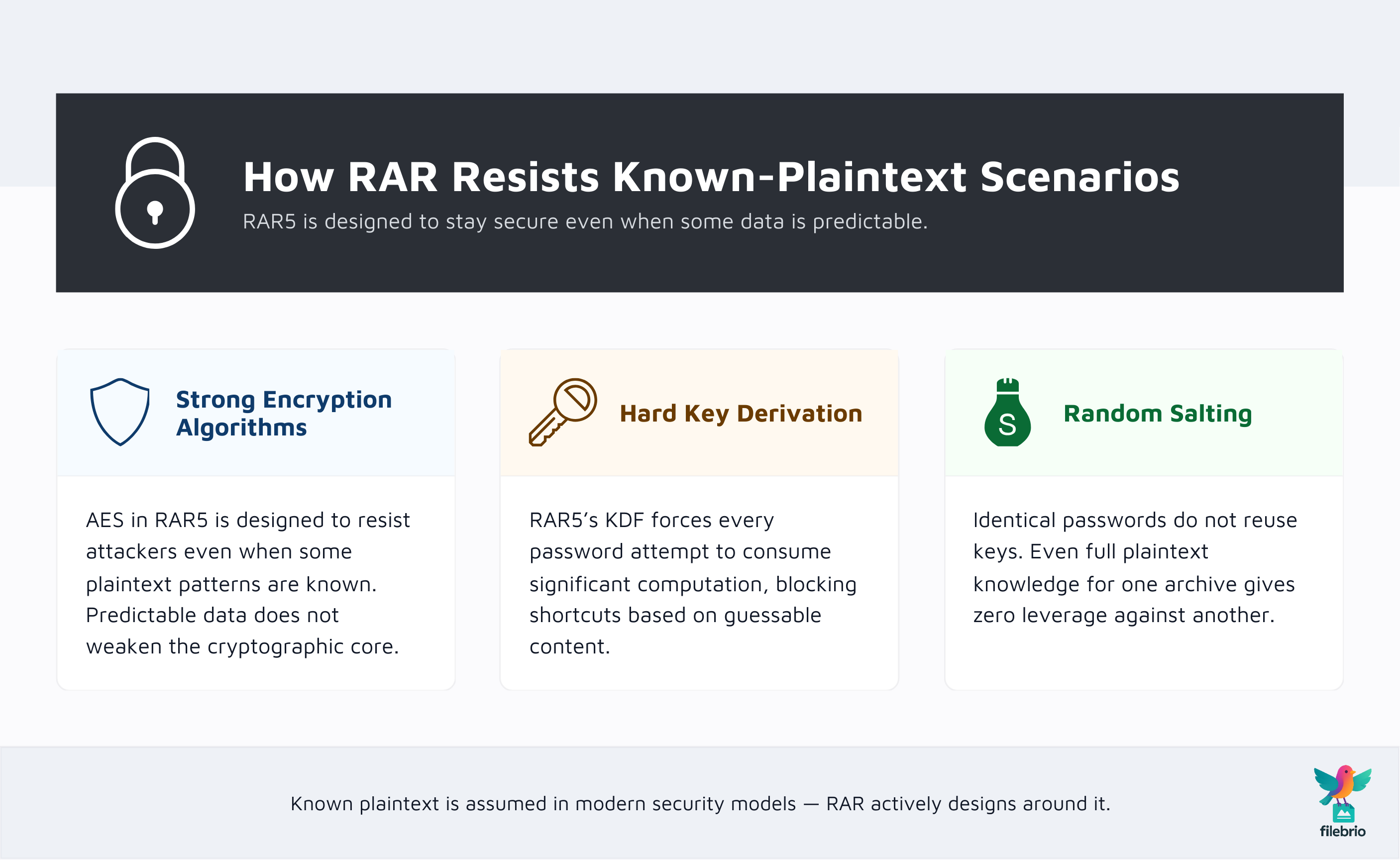
If you want a broader conceptual overview of the algorithms and modes involved, you can review how RAR4 and RAR5 protect your data ↗️. At a high level, the security model rests on three pillars:
- Strong encryption algorithms. RAR5 typically uses AES in a robust configuration. The algorithm itself is designed to resist analysis even when the attacker has both plaintext and ciphertext pairs.
- Key-derivation hardness. Instead of using the password directly, RAR5 applies an intensive key-derivation function. You can read more about this in how the RAR5 KDF strengthens your encrypted RAR file ↗️. The purpose is to make each password attempt computationally expensive.
- Randomness and salting. Random salts ensure that even identical passwords produce different keys for different archives, preventing precomputed shortcuts.
In such a model, simply knowing that a certain block of data should decode to “Dear John” or “Report Q3 2012” is not enough to meaningfully weaken the key space. Known-plaintext is already built into the threat model when RAR’s algorithms are designed and evaluated.
From a user perspective, the most effective control you can adjust is your password itself — length, complexity, and uniqueness. For a high-level understanding of why that matters, see explanations of how length impacts protection of your RAR password ↗️.
📊 What RAR Headers, Metadata, and File Structure Reveal
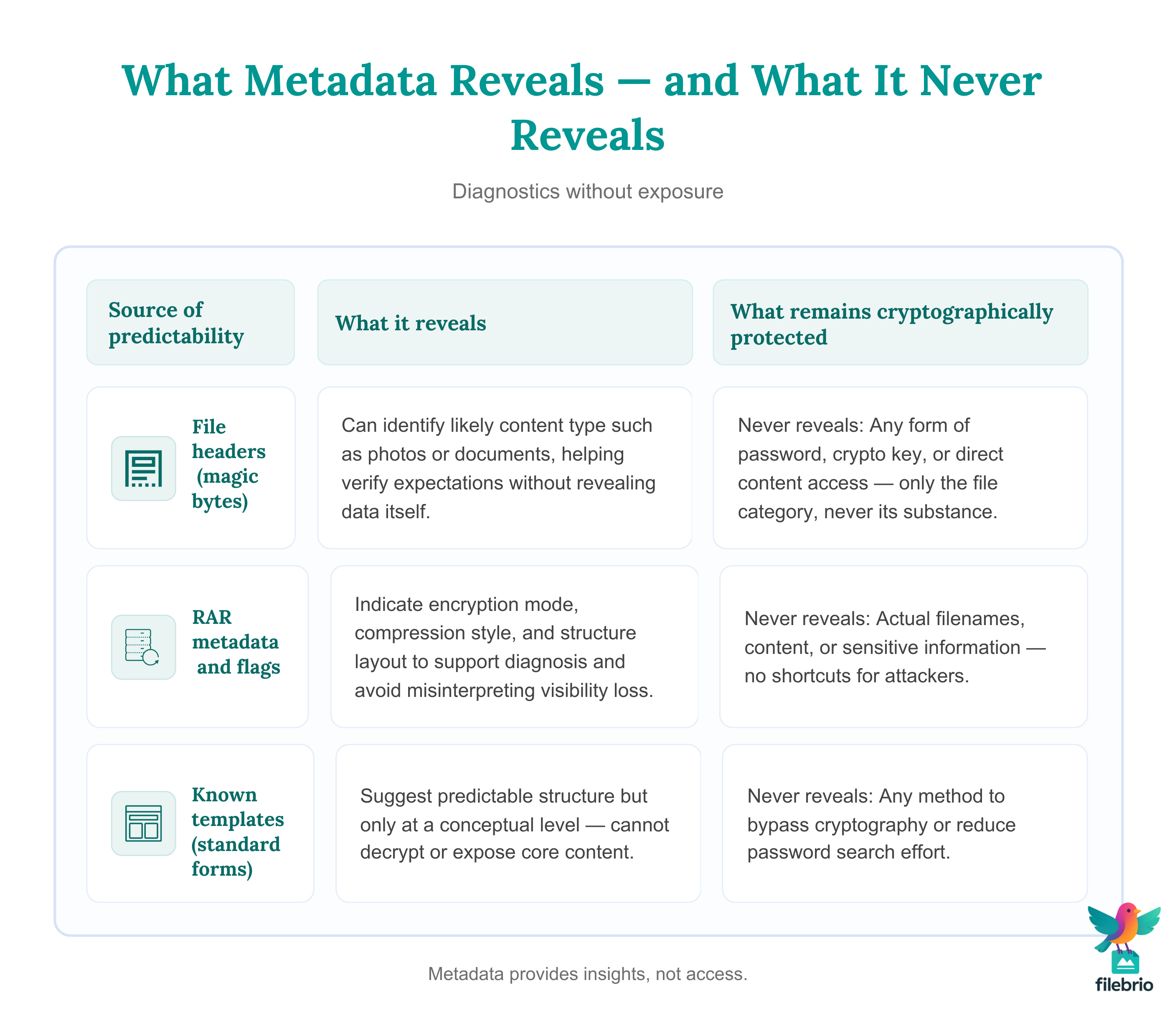
A RAR archive is more than just opaque cipher blocks. It contains structure: headers, flags, metadata, and sometimes unencrypted segments that describe the contents and compression. This structural information can be thought of as a kind of “meta-plaintext” — predictable patterns that appear around or alongside the encrypted payload.
These structures are very useful for diagnostics. For example, you can explore how file types influence diagnostics for your RAR archive ↗️ to understand why certain embedded formats give stronger confidence about what is inside without revealing the actual data.
| Source of Predictability | What It Typically Reveals | What It Does Not Provide |
|---|---|---|
| File headers (magic bytes) | Likely file type (image, document, database, etc.) | The archive password or key |
| RAR metadata and flags | Compression type, encryption flags, archive layout | Actual document content or secrets |
| Known templates (e.g., standard forms) | Guess that some content follows a familiar pattern | Shortcuts to access the rest of the encrypted data |
Well-designed tools read these structures in a strictly diagnostic way. They do not “take advantage” of known plaintext in a risky manner; they merely use metadata to decide whether an archive is healthy, which format it uses, and whether recovery is even mathematically feasible. For deeper context, see high-level guides on how to inspect internal layout of your RAR file safely ↗️ and how you can later interpret issues via read RAR metadata to understand what went wrong ↗️.
💡 Using Known-Plaintext Ideas for Safer Diagnostics (No Guessing)
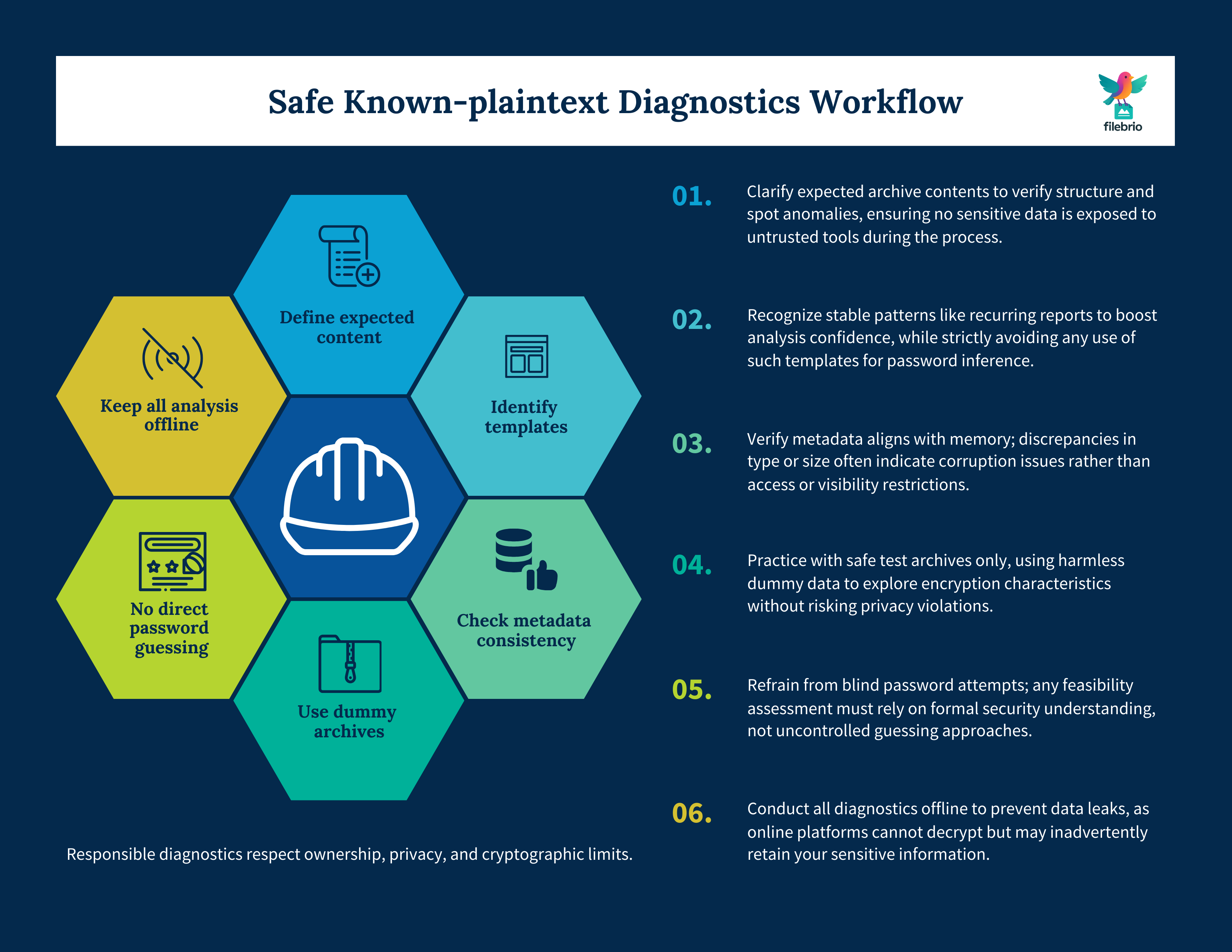
Thinking in terms of known plaintext can still help you, the legitimate owner, reason about your archive’s condition and the realism of recovery — without any risky password-guessing procedures.
A few examples of safe, high-level questions you can ask:
- “Do I know what types of files are likely inside?” If you are confident the archive contains only documents or only photos, that shapes your expectations during diagnostics and integrity checks.
- “Do I expect any obvious templates?” For example, repeated exported reports or standard invoices. This does not weaken the encryption, but it may confirm that the archive is what you think it is.
- “Is the archive structure consistent with my expectations?” If metadata says something very different from what you remember, that may indicate corruption or a mistaken file.
Safe diagnostics revolve around examining structure, metadata, and error messages, not around constructing attack strategies. Time and feasibility estimates should be based on high-level models of complexity and performance, such as those described in how to interpret timing estimates for your RAR password ↗️, rather than on trial-and-error experimentation with unknown tools.
💼 All-In-One Offline Toolkit for Safer RAR Diagnostics
When you own the archive and want to understand what is realistically possible, it is helpful to combine multiple perspectives: header flags, encryption settings, file-type structure, and your own memory about what was stored inside. Doing this by hand is tedious, error-prone, and may tempt you to try random online services that ask you to upload your archives.
Instead, a dedicated local toolset can provide a unified view of:
- Encryption mode and version: whether the archive uses RAR4 or RAR5 and how strong the configuration is.
- Header and metadata status: whether critical information appears intact or damaged.
- Structural expectations: whether the contents match what you’d expect from the types of files you originally stored.
- High-level feasibility analysis: realistic, non-promotional guidance on whether further effort is sensible.
The full set of FileBrio RAR Master features ↗️ is designed with this kind of privacy-first diagnostics in mind. Instead of focusing on raw speed, it prioritizes transparency: clear explanations of formats, header flags, and protection levels so you can make informed decisions about your own archives without exposing them to third-party servers.
________________________
FileBrio RAR Master — part of the FileBrio Office Suite — is a privacy-first, offline Windows toolkit for diagnosing and safely regaining access to your own password-protected RAR / WinRAR archives.
- Local processing only — nothing leaves your PC.
- Smart diagnostics to separate password issues from corruption.
- Owner-verified recovery workflows designed strictly for legitimate use.
Reminder: FileBrio RAR Master may be used only with archives you own or are explicitly authorized to access. It performs all analysis and recovery operations locally on your device, without uploading data anywhere.
________________________
🧪 Practicing on Dummy Archives Instead of Sensitive Data
If you are curious about how RAR’s security model behaves in the presence of known plaintext, the safest way to learn is to work with dummy archives — files you create specifically for testing, containing non-sensitive content that you are comfortable sharing or even discarding.
For example, you can:
- Create small archives with simple text files whose contents you already know.
- Vary passwords, compression options, and header-encryption settings.
- Observe how structure and metadata change when settings are adjusted.
This kind of exploration is educational while staying completely safe; it avoids touching sensitive data, and it respects both the letter and the spirit of responsible use. For a conceptual guide, see explanations of how to test RAR protection with your dummy files ↗️ — again, focused on understanding behavior rather than on any form of offensive activity.
Once you build intuition using test archives, you can return to your real RAR files with a clearer mental model of what “strong” protection looks like and how header flags and metadata reflect that strength.
⚖️ When Known-Plaintext Still Doesn’t Help (Realistic Limits)
From a theoretical perspective, known-plaintext is a classic scenario in cryptographic analysis. From a practical RAR owner’s perspective, however, it is just one of many factors — and usually not the dominant one. In most real situations, the main limiting factors are:
- Password strength. If a password is extremely short or follows obvious patterns, it may be weak regardless of known-plaintext considerations. Length and unpredictability remain central, as described in how length impacts protection of your RAR password ↗️.
- Computational cost per attempt. RAR5’s key-derivation function deliberately increases the time required per password candidate, which you can understand conceptually via how the RAR5 KDF strengthens your encrypted RAR file ↗️.
- Available resources. Hardware, time, and legal/organizational constraints all shape what is realistically feasible in a lawful context.
Even when an attacker hypothetically knows large parts of the plaintext, a well-designed scheme remains secure because each new password guess still requires a full, expensive cryptographic computation. The existence of known plaintext does not magically bypass that cost.
This is why responsible tools focus on modeling feasibility — that is, explaining whether the numbers suggest that further effort is justified — instead of promising unrealistic outcomes based solely on theoretical scenarios.
🛡️ Protecting Your RAR Archives Against Misuse
Understanding RAR’s security model and known-plaintext concepts can help you defend your data more effectively. The goal is not to “exploit” anything but to ensure that your own archives are configured in a way that aligns with your protection needs and long-term access plans.
Key practices include:
- Use strong, unique passwords. Favor longer passphrases with sufficient randomness. Avoid reusing passwords across services or archives.
- Prefer modern formats. When possible, migrate important archives to RAR5 with current settings. This can improve resilience over older formats, complementing the ideas discussed in RAR encryption overviews such as how RAR4 and RAR5 protect your data ↗️.
- Consider the file types inside. If you routinely store highly structured or business-critical files, pay extra attention to integrity and backup. You can learn more from how file types influence diagnostics for your RAR archive ↗️.
- Maintain healthy storage practices. Store archives on reliable media and check them periodically to reduce the chance that future failures are caused by corruption rather than by encryption strength.
Finally, keep in mind that offline, local workflows are significantly safer than uploading confidential archives to unknown servers. High-level privacy discussions like why offline recovery tools are safer for privacy ↗️ provide useful context when you are tempted by quick online solutions.
🧩 Planning Safe Workflows and Ownership Proof
In organizations, the line between “curiosity” and “responsibility” can blur quickly. If you are diagnosing an archive that belongs to your employer or your team, you need processes that document both ownership and authorization clearly before anyone attempts deeper analysis.
Good practice includes:
- Recorded approval. Ensure that someone with authority explicitly authorizes attempts to access the archive.
- Traceable workflows. Keep logs of who handled the archive, on which systems, and with which tools.
- Clear separation of test and production data. Known-plaintext style experiments should be done on test archives, not on live customer data.
When specialized tools are involved, you should also align their use with their license and responsible-use guidelines. For example, centralizing processes around a vetted solution like RAR password recovery tool ↗️ capabilities inside FileBrio RAR Master can help standardize practice and avoid ad hoc experimentation with untrusted software.
If questions arise about legal boundaries, compliance, or acceptable use, your policies should refer to official documentation such as the product’s legal and responsible use policy ↗️ and your internal security standards. This ensures that any work involving encrypted archives remains within clearly defined, auditable boundaries.
🛠️ Secure Offline Solution for RAR Analysis and Recovery
Known-plaintext concepts highlight how important it is to understand what part of your archive is predictable and what part truly benefits from strong encryption and robust key derivation. To turn that understanding into practical, responsible workflows, you need tools that respect both your privacy and your time.
Instead of scattering your efforts across multiple utilities, an integrated, offline suite can help you:
- Analyze encryption settings, header flags, and structural metadata in one place.
- Model feasibility using high-level time and complexity estimates rather than trial-and-error.
- Stay fully local, ensuring that sensitive archives never leave your controlled environment.
- Document actions and results in ways your security and compliance teams can review.
Comparisons such as offline vs online RAR recovery ↗️ help illustrate why local, offline tools are generally safer for sensitive data, while summaries like encrypted header warning ↗️ explain situations where even perfect tools cannot overcome mathematical limits.
When you are ready to equip your environment with a transparent, diagnostics-first solution, you can explore FileBrio RAR Master features ↗️ and download the suite from the official FileBrio Office distribution page at get FileBrio RAR Master ↗️. This keeps your known-plaintext explorations and feasibility assessments safely on your own systems, under your own control.
________________________
FileBrio RAR Master — a secure, offline Windows toolkit for regaining access to your own password-protected RAR / WinRAR archives while keeping all data strictly on your device.
- Offline-only processing — never uploads your archives.
- Smart issue detection — password vs corruption.
- Fast recovery workflow optimized for legitimate ownership.
⬇️ Download FileBrio RAR Master
Reminder: FileBrio RAR Master is intended only for archives you own or are explicitly authorized to access. All operations run locally on your PC.
________________________
📚 Legal Reminder
This article is provided for general informational and educational purposes only. Any examples, scenarios, or references to password recovery, archive security, or related tools (including FileBrio RAR Master or similar software) are intended solely to help you better understand how to protect and manage your own data.
You may only apply any techniques, workflows, or tools described here to files and archives that you fully own or are explicitly and verifiably authorized to access. Attempting to bypass, remove, or recover passwords for third-party data without clear permission may violate criminal law, civil law, or internal company policies in your jurisdiction.
Nothing in this article constitutes legal advice. Laws and regulations differ between countries and organizations, and you are solely responsible for ensuring that your actions comply with all applicable legislation, contracts, and internal policies. If you are unsure whether a particular action is lawful or permitted, consult a qualified legal professional before proceeding.
🔗 See Also: Further Reading on RAR Security
- Why Encrypted Headers Make Content Discovery Impossible — and What That Implies for Recovery ↗️
- How RAR Header Encryption Affects Recovery Feasibility and What Clues It Still Reveals ↗️
- How to Check Whether Your RAR Archive Uses Header Encryption (Without Specialized Tools) ↗️
- RAR Recovery Records and .rev Volumes: How They Help Protect and Restore Data ↗️
- How to Read RAR Metadata to Understand What Went Wrong ↗️