
How to Identify Whether Your RAR File Is Encrypted or Simply Corrupted
When a RAR file won’t open, the first step is understanding *why*. A locked archive with a missing password behaves completely differently from a damaged or incomplete file, and confusing the two leads to wasted time and unnecessary risk.
Many users mix these situations together. A normal password prompt can look like an error, while corruption warnings can seem like “wrong password.” People try passwords on a broken file or run repairs on an archive that’s perfectly healthy but simply encrypted. RAR tools actually provide clear clues. Error messages, the presence or absence of a file list, how quickly failures occur, and even the archive’s size all point toward either encryption or corruption.
This article outlines a simple, offline-safe way to identify which issue you’re dealing with. You’ll learn the common signs of each, how encrypted headers affect visibility, and how to read high-level metadata without extracting anything—so you can choose safe next steps without putting your data at risk.
🧭 Navigation
⚡ TL;DR — Quick Encryption vs Corruption Check
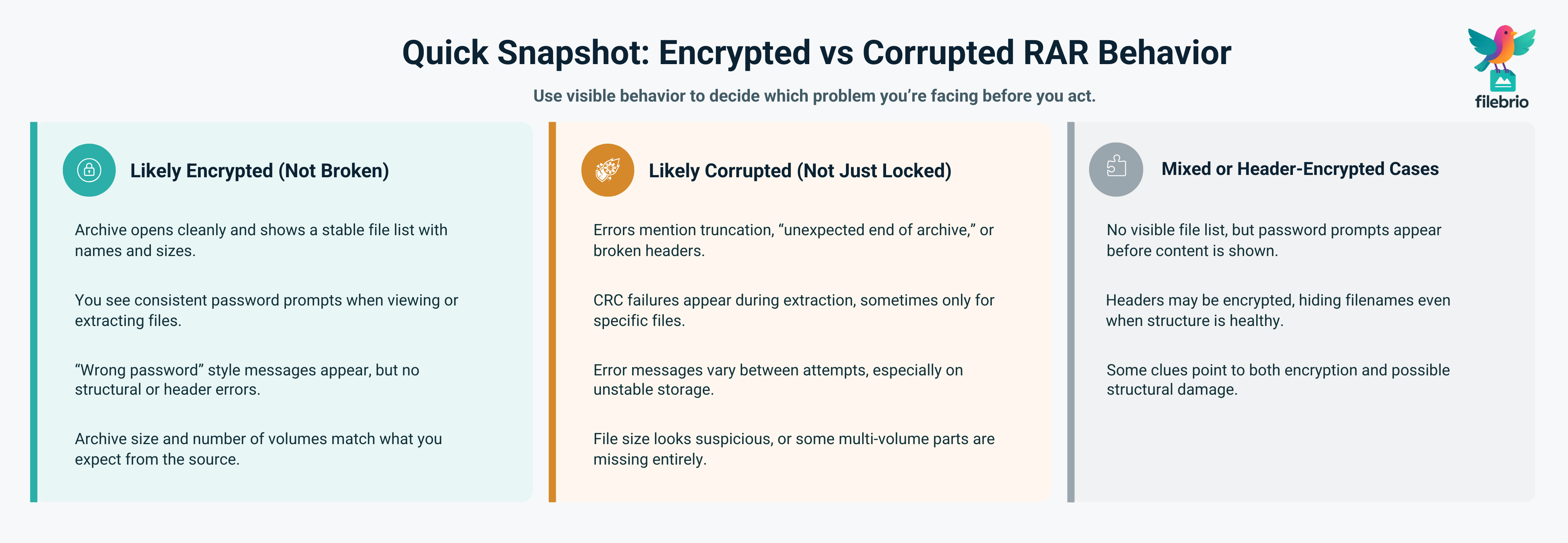
If your RAR file opens cleanly in a tool like WinRAR and shows a file list but asks for a password when you try to view or extract contents—especially with clear “wrong password” style messages—you’re most likely dealing with normal encryption, not corruption. If the archive shows severe errors, “unexpected end of archive,” broken headers, or inconsistent error messages, and especially if the file size seems suspicious or parts are missing, you’re likely dealing with corruption. Mixed symptoms (no file list, but strong hints of encryption) can indicate encrypted headers, which hide filenames and make diagnosis harder. Before trying passwords or repair tools, stabilize the archive, examine the structure safely, and only then choose either a password-focused route or a repair-focused route based on what you find.
🧠 Why Distinguishing Encryption vs Corruption Matters
From the outside, both encryption and corruption look like the same thing: you can’t reach your data. But under the surface, they are almost opposites. Encryption is an intentional barrier that protects a structurally healthy archive. Corruption is an unintentional structural problem that makes an archive unhealthy, even if you know the password perfectly.
Why does this distinction matter so much?
- Different tools solve different problems. Password-focused tools help when the archive is healthy but locked by encryption. Repair-focused workflows help when the structure itself is damaged. Mixing them up wastes time and can reduce your recovery chances.
- Different expectations apply. A well-protected, strongly encrypted RAR file may be mathematically infeasible to open without the correct password, as discussed in conceptual resources like how RAR4 and RAR5 secure your protected data ↗️. A corrupted archive, on the other hand, may have some fragments recoverable—but never a guaranteed full restoration.
- Risk profiles differ. Trying random repairs on a corrupted archive can destroy what is left. Trying random passwords on a healthy encrypted archive can be safe structurally, but may be pointless if you have no realistic password clues.
Step one, then, is not “find a tool” but “name the problem correctly.” Once you know whether you’re facing encryption, corruption, or both, the rest of the decisions become far more logical.
📚 High-Level Concepts: Encryption, Passwords, and Archive Integrity
RAR archives combine two big ideas: encryption, which controls who can read content, and integrity, which controls whether the content has been preserved correctly. You can have:
- A healthy encrypted archive — everything is structurally fine, but you need the correct password.
- A damaged but unencrypted archive — no password is required, but some or all contents may be unreadable.
- A damaged encrypted archive — the hardest case, where both security and integrity are at play.
At a conceptual level:
- Encryption affects who can see data inside the archive. Strong encryption designs make “reset-style” access impossible and tie visibility to knowledge of the password.
- Integrity is about whether bits have been lost or changed unintentionally—through disk failures, interrupted downloads, or storage mishandling.
When the RAR format is used with advanced features such as header encryption—where even filenames are protected—the line between “encrypted” and “corrupted” might feel blurry, because a healthy encrypted archive with hidden headers can look empty. Guides such as how encrypted headers hide your protected RAR contents ↗️ and how header encryption shapes your RAR recovery chances ↗️ explain how visibility changes when header protection is enabled.
🧩 A Clear All-In-One Way to Understand What’s Really Happening
When a RAR file won’t open, the hardest part is often the beginning — not knowing whether you’re facing encryption, corruption, or a mix of the two. A file that refuses to extract might still be perfectly healthy but locked, while a file that shows strange errors might be damaged even if you know the password.
Instead of guessing, it helps to rely on a tool that can read the small structural signals RAR still exposes even when filenames are hidden or the archive is partially damaged.
| What’s Hard to See | What You Can Still Learn |
|---|---|
| Filenames and per-file details | Whether the file is encrypted or structurally damaged |
| Which internal block failed | RAR version (RAR4/RAR5) and general layout |
| Exact problem source | Whether the archive looks intact, truncated, or inconsistent |
FileBrio RAR Master brings these clues together in one clean, offline interface. It helps you understand whether your archive is:
- healthy and encrypted,
- corrupted at the structural level, or
- both encrypted and damaged.
This clarity allows you to choose the correct next steps instead of bouncing between repairs and password attempts blindly.
________________________
FileBrio RAR Master — part of the FileBrio Office Suite — is a privacy-first, offline Windows toolkit for diagnosing and safely regaining access to your own password-protected RAR / WinRAR archives.
- Local processing only — nothing leaves your PC.
- Smart diagnostics to separate password issues from corruption.
- Owner-verified recovery workflows designed strictly for legitimate use.
Reminder: FileBrio RAR Master may be used only with archives you own or are explicitly authorized to access. It performs all analysis and recovery operations locally on your device, without uploading data anywhere.
________________________
🔐 Typical Signs Your RAR Is Encrypted (Not Broken)
So how do you know that you are dealing with encryption instead of corruption? Several positive signs usually point in the direction of a structurally healthy, but intentionally locked, archive.
1. The Archive Opens Cleanly and Shows a File List
If your RAR tool opens the file without complaining about structure, and you can clearly see filenames, sizes, and maybe folder hierarchy, this is a strong indicator that the archive itself is structurally sound. It may still be encrypted, but it is not obviously broken.
2. You Receive Clear Password Prompts
When you attempt to open or extract files, the tool asks for a password in a predictable way. If you enter an incorrect password, you see consistent “wrong password” style messages or data that fails integrity checks as soon as decryption is attempted.
This behavior aligns with the design of RAR encryption described in what encryption modes mean for your locked RAR files ↗️, where password-based keys control content access without changing archive structure.
3. Error Messages Focus on Passwords, Not Structure
Messages such as “wrong password” or “incorrect password” suggest that your tool is successfully parsing the archive structure and only failing at the decryption phase. By contrast, structural errors typically mention corruption, unexpected ends, or broken headers. A good supporting reference here is how to interpret error messages from your RAR file ↗️, which explains the difference between password-related and integrity-related complaints.
4. Archive Size and Origin Make Sense
If the archive size looks plausible (for example, consistent with what you expect from its content) and the file comes from a trusted, intact source, there is less reason to suspect corruption. In such cases, focusing on password diagnosis—rather than repair—often makes more sense.
💥 Typical Signs Your RAR Is Corrupted (Not Just Locked)
Corruption symptoms usually look different from normal encryption behavior. Instead of a clean file list and clear password prompts, you are more likely to see structural complaints or irregular behavior.
1. “Unexpected End of Archive” and Similar Errors
Errors that explicitly suggest truncation, missing data, or incomplete archives generally point to integrity issues, not password problems. If the file was interrupted during download or stored on a failing device, some blocks might simply be missing. Even with the correct password, you may not be able to reconstruct the missing parts.
In such cases, it can be useful to review guidance like how to stabilize your partially corrupted RAR file ↗️, which emphasizes safe first moves rather than aggressive repair attempts.
2. CRC Failures in the Middle of Extraction
If the extraction process starts normally and then fails with CRC errors—possibly for only some files—this usually means that the archive structure is intact, but certain compressed blocks are damaged. This is a classic sign of corruption rather than bad passwords.
3. Inconsistent or Varying Errors Across Attempts
When you see different errors at different times, especially if the archive is stored on a removable drive or aging disk, you may be dealing with a storage-level issue. This kind of inconsistency is not typical of simple encryption, where wrong passwords produce stable, repeatable complaints.
4. The Archive Barely Opens or Crashes the Tool
If your RAR application struggles just to open the file, crashes, or freezes consistently at the same point, the problem is likely structural. At this stage, careful diagnosis is better than repeated attempts. Approaches from how to safely diagnose your locked RAR file ↗️ and steps to minimize loss from your failing RAR contents ↗️ can help keep the situation from getting worse.
🧩 Edge Cases: Encrypted Headers, Mixed Symptoms, and Confusing Messages
Some RAR features blur the line between “encrypted” and “corrupted” from a user’s perspective—especially encrypted headers. When headers are encrypted, filenames and some metadata are hidden until the correct password is provided. To someone unfamiliar with the feature, a healthy, header-encrypted archive can look suspiciously like an empty or broken file.
Edge-case behavior can include:
- No visible file list, even though the archive is valid and well-formed.
- Prompts for passwords before any information about contents is shown.
- Errors that mention both passwords and structural elements, depending on how the tool handles header encryption.
Articles such as what metadata hints remain in your protected RAR contents ↗️ and simple ways to spot header encryption in your RAR file ↗️ discuss how header protection affects visibility and what limited clues may still be available even when names are hidden.
Mixed scenarios also exist, where an archive is both encrypted and damaged. In those cases, you might correctly enter a password but still see errors due to lost or corrupted blocks. In the most severe examples, cryptographic strength and structural damage combine to produce archives that are nearly impossible to open, as described in high-level feasibility discussions like why strong encryption blocks access to your RAR file ↗️.
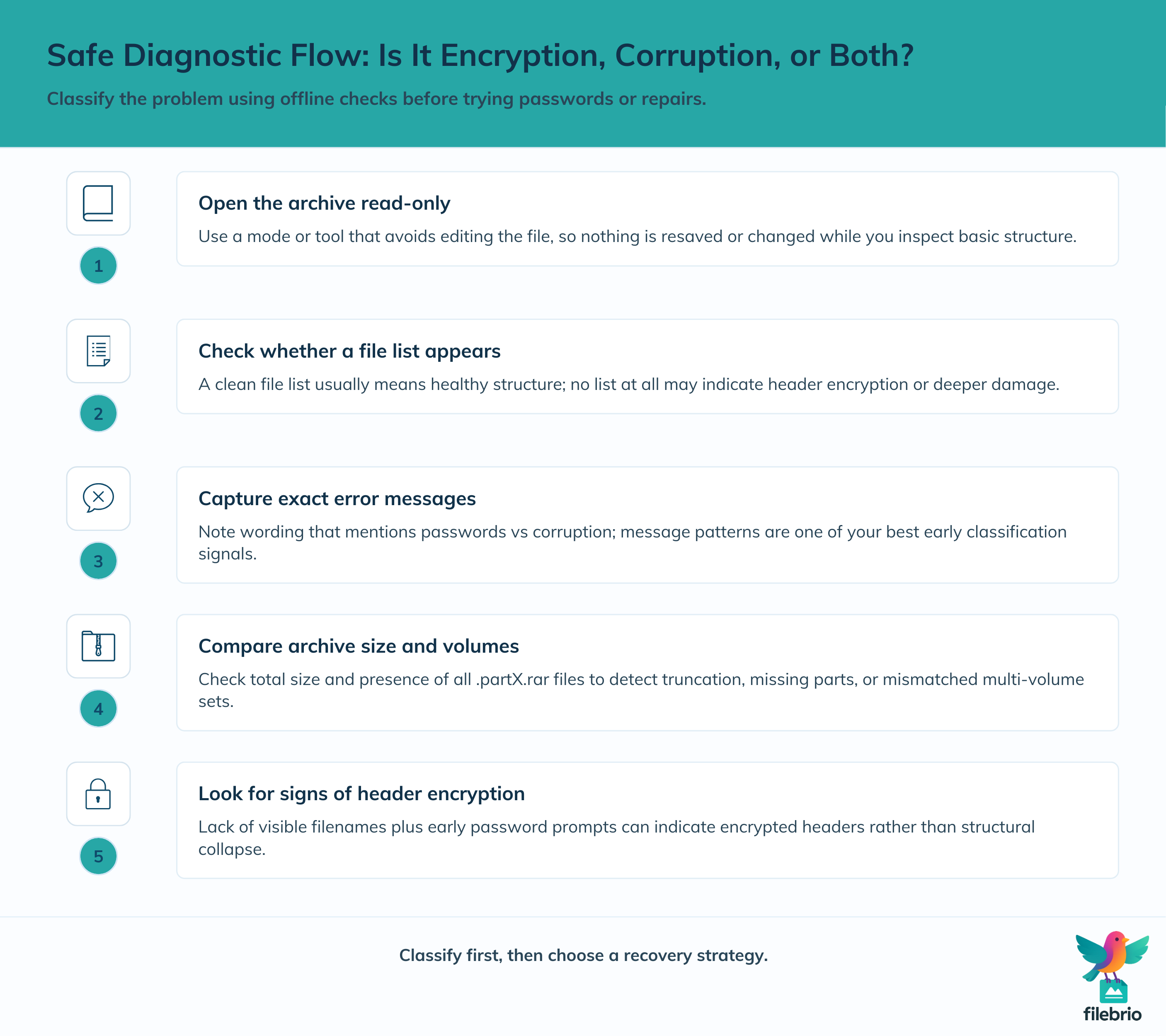
🔎 Safe Diagnostic Flow to Classify the Problem
Rather than reacting to the first error message, you can follow a simple, safe flow to classify the issue. The goal is not to perform low-level forensics, but to get enough clarity to choose the right direction: password recovery or repair.
| Step | Purpose | What You Learn |
|---|---|---|
| 1. Open the archive read-only | Prevent accidental changes | Whether the tool can parse basic structure |
| 2. Observe if a file list appears | Check structural health | Healthy structure vs potential header problems |
| 3. Note exact error messages | Classify by type | Password-related vs corruption-related patterns |
| 4. Compare archive size with expectations | Spot truncation | Signs of incomplete downloads or partial copies |
| 5. Check whether header encryption is likely | Explain lack of visible filenames | Healthy-but-hidden vs genuinely broken behavior |
Throughout this process, your priority is to preserve the archive as-is while you gather information. Detailed structural checks that do not alter the file—such as the approaches described in how to inspect internal layout of your RAR file safely ↗️—are much safer than repeated extraction attempts.
🔐 A Secure Offline Environment for Complex RAR Issues
Once you identify whether your archive shows signs of encryption, corruption, or both, the next question is how to analyze it safely. With sensitive archives, you don’t want to upload them anywhere, and with structurally fragile ones, you don’t want tools that modify the file while probing it.
This is where a private, offline diagnostic approach becomes essential.
| Challenge When Diagnosing | What an Offline Tool Provides |
|---|---|
| Empty or missing file list | Clear identification of encryption vs header issues |
| Suspicious errors or inconsistent behavior | Checks for truncation and structural anomalies |
| Concern about exposing private archives online | 100% local analysis — nothing leaves your device |
| Uncertainty about realistic next steps | Format-aware guidance for healthy vs damaged archives |
With FileBrio RAR Master, you get a controlled space to inspect the archive’s structure, verify its health, and decide whether recovery should focus on password access or repair — all without risking the only copy you have.
________________________
FileBrio RAR Master — a secure, offline Windows toolkit for regaining access to your own password-protected RAR / WinRAR archives while keeping all data strictly on your device.
- Offline-only processing — never uploads your archives.
- Smart issue detection — password vs corruption.
- Fast recovery workflow optimized for legitimate ownership.
⬇️ Download FileBrio RAR Master
Reminder: FileBrio RAR Master is intended only for archives you own or are explicitly authorized to access. All operations run locally on your PC.
________________________
📊 Using Metadata and Structure to Understand What Went Wrong
RAR archives contain metadata and header information that can reveal a surprising amount about their condition. Even when contents are encrypted, some structural hints may still be visible, depending on configuration. By focusing on metadata rather than raw extraction, you can classify problems more safely.
Useful metadata-driven checks include:
- Header flags and fields that indicate whether encryption is enabled, whether recovery records are present, and how many file entries are expected.
- File count and sizes compared against what you remember or documented elsewhere.
- Archive-level comments or notes, where some users record context or instructions.
High-level guides such as how header flags reflect your RAR file’s health ↗️ and how to read metadata clues in your RAR file ↗️ explain how this informational layer helps distinguish “locked but healthy” from “damaged but unprotected.” When used cautiously, these insights allow you to decide whether you are dealing with a password barrier, a structural problem, or a combination of both.
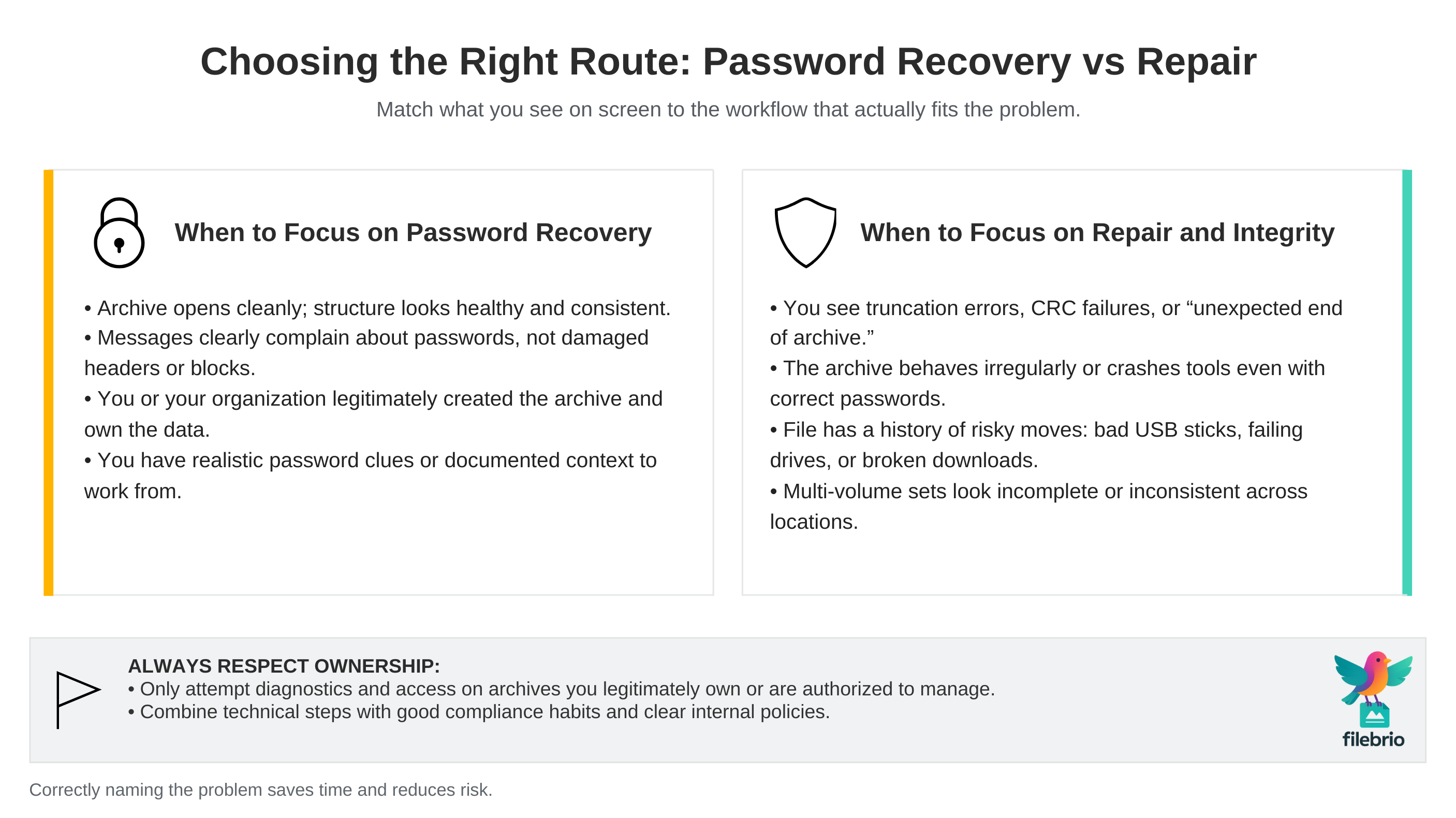
🛣️ Choosing the Right Next Step: Password Recovery vs Repair
Once you have a reasonable classification, you can make better decisions about what to try next. Having a clear mental separation between encryption and corruption prevents you from bouncing aimlessly between password guessing and file repair.
When to Focus on Password Recovery
Password-focused next steps make more sense when:
- The archive appears structurally healthy and opens cleanly.
- Error messages concentrate on passwords, not on structure or missing data.
- You have strong reason to believe you or your organization created the archive and legitimately own the data.
At this stage, you might explore context-based memory work, organizational metadata, or other non-destructive techniques that help you recall or reconstruct the password. Broader frameworks for evaluating safe access paths, such as those outlined in how to assess safe access paths for your locked RAR file ↗️, can help keep efforts realistic and lawful.
When to Focus on Repair and Integrity
Repair-focused next steps make more sense when:
- You see clear signs of integrity issues: truncation, CRC failures, or obvious corruption messages.
- The archive does not behave like a typical encrypted file, even when the context suggests it should.
- The file has a history of being moved, downloaded, or stored in risky environments (unstable USB sticks, failing drives, etc.).
Here, your priority is to stabilize the file and investigate recovery options that protect what is still intact. Concepts from how recovery records safeguard your damaged RAR files ↗️ and ways to prevent losing your RAR data on storage devices ↗️ are especially helpful for planning safe repair attempts and future prevention.
Always Respect Ownership and Boundaries
Regardless of whether the problem is encryption or corruption, all diagnostic and recovery efforts should apply only to archives you legitimately own or are formally authorized to manage. Good ownership verification habits, such as those described in checks to ensure you’re working with your own RAR files ↗️, are a core part of safe and compliant workflows.
🛡️ Preventing Confusion in Future RAR Archives
Once you’ve gone through the anxiety of not knowing whether a RAR file is encrypted or corrupted, it’s worth adjusting how you create, store, and document archives in the future. The goal is to make future diagnosis easier—for both you and any authorized colleagues who might handle the same data later.
Practical prevention strategies include:
- Documenting whether an archive is supposed to be encrypted when you create it, including which business process or person is responsible for the password.
- Storing notes or metadata about passwords and archive purpose in secure, separate systems so you can distinguish “forgotten password” from “unexpected damage” later.
- Using reliable storage and backup practices to lower the risk of corruption in the first place.
- Including recovery records where appropriate so that minor damage is easier to correct.
High-level guidance like ways to boost security without losing access to your data ↗️ and safe approaches to diagnosing your protected archive ↗️ can be combined into a long-term strategy: strong protection, clear documentation, and safe diagnostics when something goes wrong.
📎 Summary
“My RAR file won’t open” can mean very different things depending on whether the root cause is encryption or corruption. A healthy, strongly encrypted archive keeps unauthorized users out by design; a corrupted archive, by contrast, may lock out even its legitimate owner by damaging the structure that reading tools rely on. By paying attention to whether you see clean file lists, stable password prompts, and structurally focused error messages, you can quickly move from confusion to an informed classification.
Once you know which side of the line your problem sits on—encryption, corruption, or a mix—you can choose the right next step: context-based password work and feasibility analysis for healthy encrypted archives, or stabilization and careful repair attempts for damaged ones. Throughout this process, a privacy-first, offline mindset and clear ownership boundaries help ensure that your data remains both safe and legally protected. In the long run, better documentation, stronger storage habits, and thoughtful use of RAR features can make it much easier to answer the key question this article started with: “Is my RAR file encrypted, corrupted, or both—and what should I actually do about it?”
⚖️ Legal Reminder
This article is provided for general informational and educational purposes only. Any examples, scenarios, or references to password recovery, archive security, or related tools (including FileBrio RAR Master or similar software) are intended solely to help you better understand how to protect and manage your own data.
You may only apply any techniques, workflows, or tools described here to files and archives that you fully own or are explicitly and verifiably authorized to access. Attempting to bypass, remove, or recover passwords for third-party data without clear permission may violate criminal law, civil law, or internal company policies in your jurisdiction.
Nothing in this article constitutes legal advice. Laws and regulations differ between countries and organizations, and you are solely responsible for ensuring that your actions comply with all applicable legislation, contracts, and internal policies. If you are unsure whether a particular action is lawful or permitted, consult a qualified legal professional before proceeding.
📚 See Also
- Why RAR Archives Become Corrupted: Common Causes and How to Prevent Them ↗️
- What to Do When WinRAR Shows “Unexpected End of Archive” — Meaning and Safe Actions ↗️
- How to Verify File Integrity After Successfully Accessing a RAR Archive ↗️
- How to Prevent RAR Data Loss on USB Drives, HDDs, and Cloud Storage ↗️
- RAR/WinRAR File Passwords Explained: How Encrypted Archives Work and What Access Options You Have ↗️