
How High-Quality Wordlists Are Created: Principles, Ethics, and Safer Alternatives
If you have an encrypted RAR or WinRAR archive that you legitimately own, it is tempting to think that a “magic wordlist” somewhere on the internet will instantly reveal your forgotten password. In reality, high-quality wordlists are less about magic and more about structure, context, and ethics — and they come with very real risks when misused or sourced from untrusted places.
Because we have structured internal resources for RAR security and recovery topics, this guide will also point to a few related deep-dive articles where appropriate, so you can keep exploring safely and responsibly.
🧭 Navigation
Important
The information provided in this article applies exclusively to RAR / WinRAR archives for which you have full, demonstrable ownership or properly documented authorization. If you are not the rightful owner of the data, do not directly control it, or cannot clearly prove permission to access it, you must stop immediately. Attempting to access, recover, or modify data without explicit authorization may violate criminal law, civil statutes, corporate compliance requirements, and privacy regulations in many jurisdictions. You alone are responsible for ensuring that your actions are lawful and properly permitted before proceeding.
🧠 TL;DR — Wordlists, Ethics, and Safer Alternatives
This article explains, at a high level, how high-quality password wordlists are conceptually designed, why they are not a magic solution for every forgotten RAR password, and where the ethical and legal limits start. Instead of teaching you how to build or run attack wordlists, it focuses on:
- The difference between random, low-quality lists and structured, context-aware ones.
- Why high-quality lists are based on real human behavior, patterns, and language — but must still respect privacy and law.
- How to evaluate whether your RAR archive is reasonably recoverable before you even think about heavy password attempts.
- Safer alternatives, like memory work, metadata review, and archive diagnostics, that reduce unnecessary risk.
- How FileBrio RAR Master can help you work completely offline, diagnose your own archives, and stay within legal and ethical boundaries.
📌 What High-Quality Wordlists Are (At a High Level)
At the simplest level, a password wordlist is just a long list of candidate passwords. In practice, “high-quality” wordlists are not random collections of words copied from the internet. They attempt to approximate how real people actually choose passwords — combining language, personal patterns, and common habits — without being purely brute-force over every possible character combination.
For example, people rarely use completely unstructured strings of random symbols for everyday archives. They tend to rely on habits, such as reusing patterns across accounts or archives, using familiar phrases, and adjusting older passwords slightly when forced to “change them”. That’s why articles about behavior and memory around RAR passwords ↗️ are directly relevant to the topic of wordlists.
However, you do not need to build massive industrial-grade lists just to check what is realistically possible with your own RAR archive. Understanding the principles behind wordlists is usually enough to estimate feasibility and decide whether safer alternatives are better for your case.
| Aspect | Low-Quality Wordlists | High-Quality Wordlists (Conceptually) |
|---|---|---|
| Source | Random, uncurated dumps from unknown origins | Structured from known patterns and behavior models |
| Relevance | Mostly unrelated to your actual password habits | Tuned to realistic patterns someone actually used |
| Size | Very large but noisy | Balanced between coverage and practicality |
| Ethical Risk | Often unclear or inappropriate reuse of leaked data | Designed with privacy and legitimacy in mind |
🧪 Why People Use Wordlists for Their Own Encrypted Archives
When someone forgets the password to a RAR archive they created years ago, they often go through the same stages. First, they retry obvious guesses and familiar variations. Then, when frustration grows, they search for “wordlist for RAR password” or similar terms, hoping for a ready-made solution that will “just work”.
In reality, the path from “I forgot my password” to “I want to use a wordlist” should include careful diagnostics and self-analysis. Resources on how to start evaluating a forgotten RAR password ↗️ and using context and memory triggers to reconstruct passwords ↗️ are often more productive than jumping directly to huge lists.
People reach for wordlists because they:
- Assume their password was “simple enough” to be somewhere in a generic list.
- Hope a tool will “do the thinking” for them instead of doing memory work.
- Underestimate how strong modern encryption is and overestimate what wordlists can do.
- Don’t yet realize that evaluation and diagnostics usually come before any serious guessing attempts.
If you skip those earlier steps, you might spend time and computational effort on wordlists that never had a realistic chance of matching your real password style in the first place.
⚖️ Ethical and Legal Boundaries Around Wordlists
Any discussion of wordlists must be framed inside strict legal and ethical boundaries. This article is about understanding wordlist concepts for responsible use on archives that you own and control. It is not a guide for unauthorized access or for building attack infrastructure.
Responsible use means:
- You work only with RAR archives that you clearly own or administer.
- You respect privacy, contracts, and local law at all times.
- You avoid repurposing leaked datasets or unknown third-party lists whose origins you cannot verify.
- You stay within the principles outlined in more general guides on ethical handling of password-protected files ↗️.
In many jurisdictions, using wordlists or any password-guessing methods on data you do not own may be illegal, even if technically possible. Corporate environments also have internal policies; they may require documented ownership, tickets, and approvals before anyone touches a protected archive.
Because of this, you should always treat wordlists as a last-resort analytical tool, only after you have established legitimacy and evaluated whether the effort is justified.
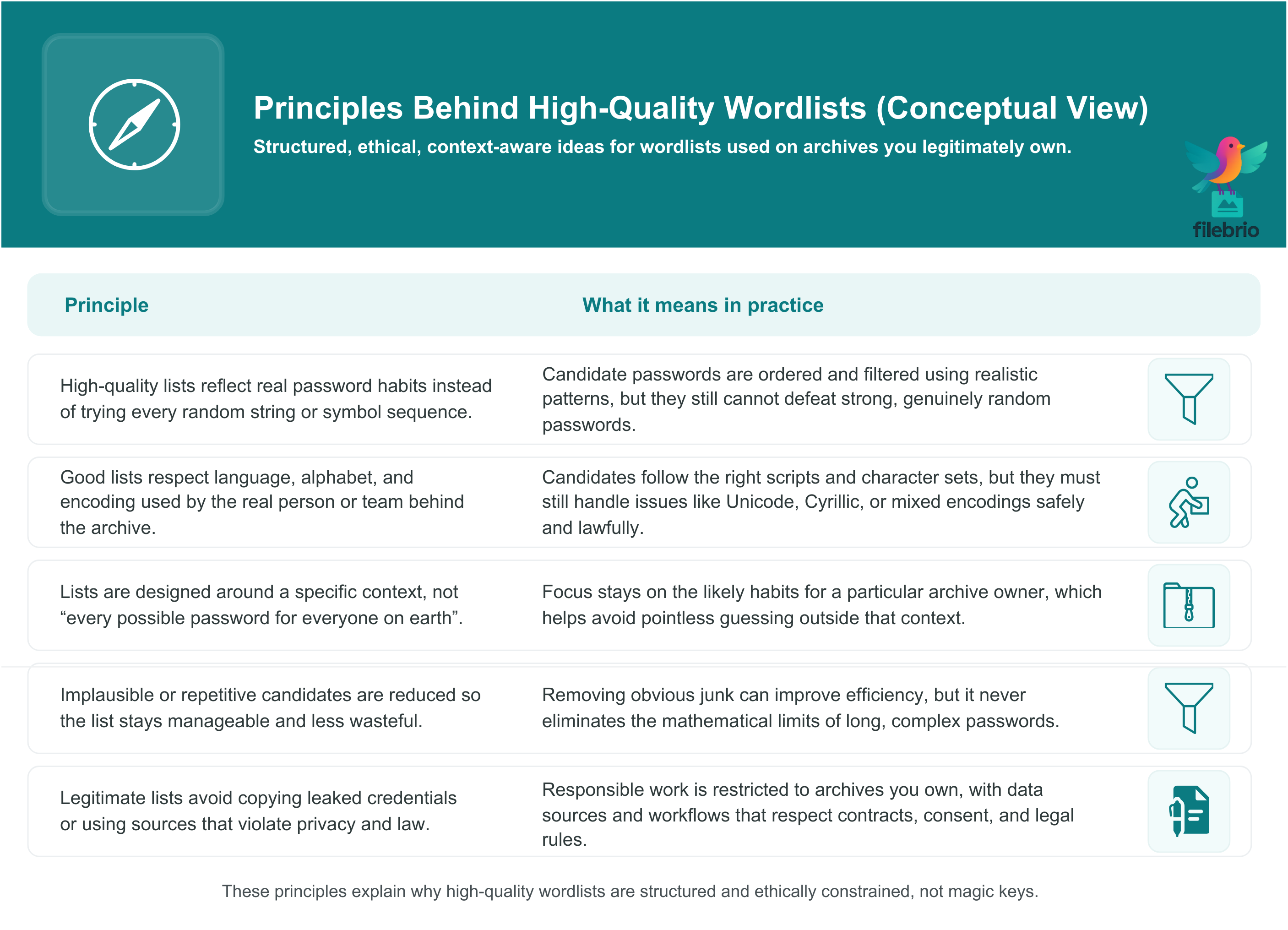
🧱 Principles Behind High-Quality Wordlists (Without Recipes)
High-quality wordlists are built around structure, not randomness. At a conceptual level, creators focus on characteristics that make candidate passwords more plausible given a person, culture, or context. These are principles, not instructions:
- Human behavior modeling: Lists reflect how people actually combine words, numbers, and symbols, rather than exhaustively enumerating every string.
- Language and locale awareness: Good lists respect language, alphabet, and encoding (for example, Unicode or Cyrillic — issues covered in more depth in guides about password encodings and character sets ↗️).
- Context targeting: Lists are designed to match a specific context (personal archive, corporate naming culture, etc.), not every password in the world.
- Noise reduction: Low-value candidates are trimmed to keep the list manageable; repetition and obvious nonsense are minimized.
- Ethical sourcing: Data sources are chosen with respect for privacy and law, not by copying harmful leaks or unauthorized materials.
This is very different from simply downloading a random “top passwords” list. A well-thought-out list tries to put the most realistic guesses first — but it is still constrained by the raw mathematics of password strength. If your RAR password is long and random enough, no amount of list curation can turn an impossible task into an easy one. Resources about password length and entropy ↗️ help you understand where those limits are.
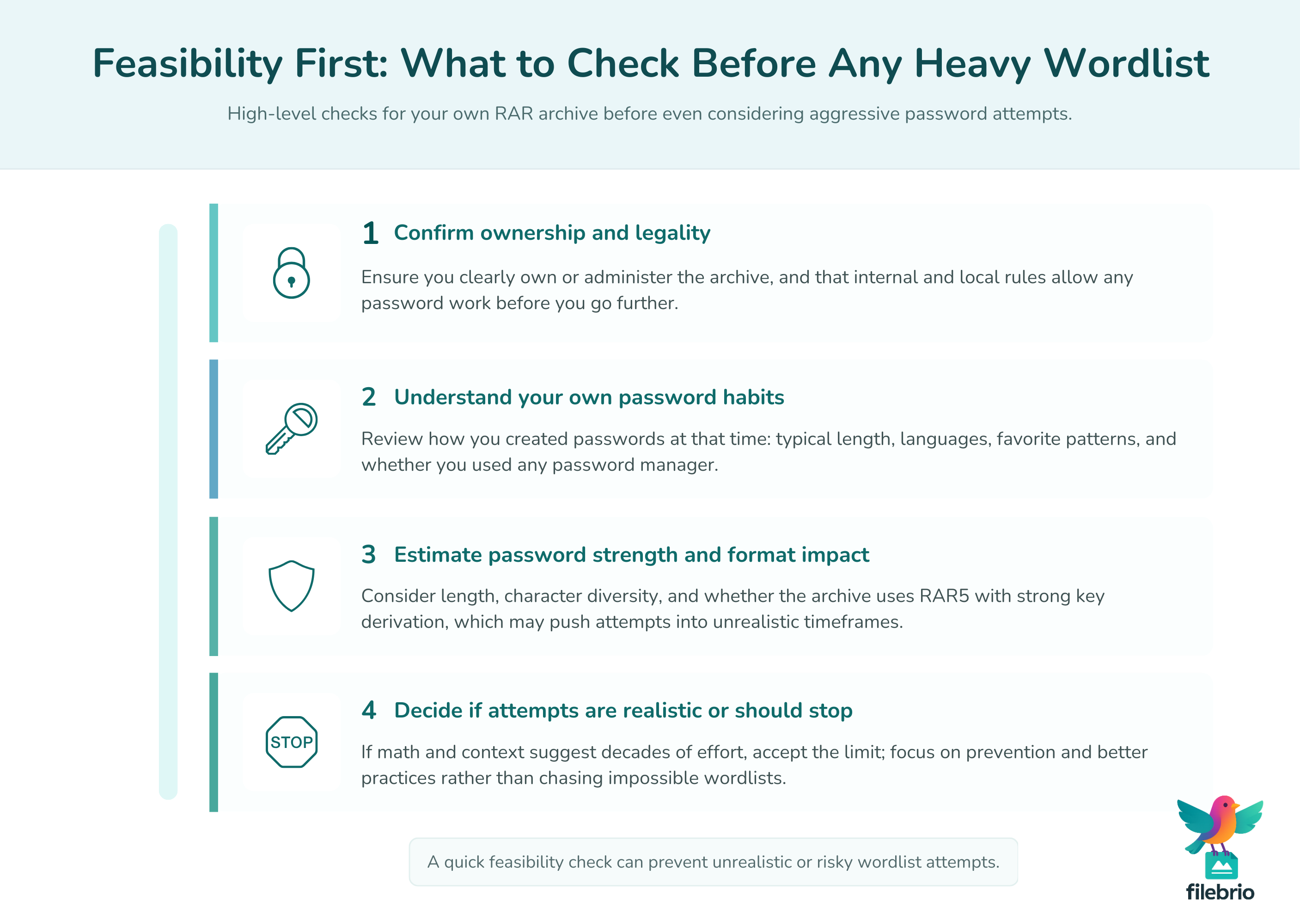
🧮 Evaluating Feasibility Without Aggressive Wordlists
Before you invest time into heavy wordlist-based attempts, it is critical to ask: is this even realistic? You can often estimate feasibility using high-level reasoning instead of generating complex lists.
Important factors include:
- Password length range: Short phrases with limited variety are more within reach than long, high-entropy ones.
- Character diversity: Use of many character sets (upper/lowercase, digits, symbols, multiple scripts) greatly increases complexity.
- RAR format and settings: RAR5 with strong key-derivation parameters is significantly harder to evaluate than older or weaker configurations.
- Available compute resources: Even with modern hardware, realistic speed may be far lower than people expect.
Articles that focus on time estimates and guessing complexity for RAR passwords ↗️ are particularly useful at this stage. They help you understand ranges like “seconds”, “hours”, or “decades” in a high-level way, without turning the process into an unsafe or uncontrolled attack.
Often, it makes more sense to review alternatives first — for example, checking archive health, verifying that the password is really the blocker, and following advice such as what to try before any password guessing on your own RAR file ↗️.
🧰 All-In-One Toolkit for Safe Archive Diagnostics
Many users jump straight into searching for “wordlists” when the real problem is unclear: is the archive damaged, is the password stronger than they remember, or is there a format issue? A structured diagnostics phase can save hours or days of trial and error.
FileBrio RAR Master is part of the FileBrio Office Suite and is designed to help with exactly this kind of safe analysis:
| Need | How FileBrio RAR Master Helps |
|---|---|
| Understand what blocks access | Archive diagnostics to distinguish encryption from corruption and format problems. |
| Check archive health | Metadata and structure checks before any password-related attempts. |
| Stay offline and private | All analysis runs locally on your machine; nothing is uploaded. |
| Plan realistic next steps | Tools to help you interpret feasibility instead of blind guessing. |
You can review the broader capabilities of the suite in the FileBrio RAR Master features overview ↗️ and then get the tools from the official FileBrio installer ↗️. Used together with your own common sense and memory work, diagnostics help you decide whether wordlists are even necessary.
For complex password situations, the dedicated RAR password recovery module ↗️ focuses specifically on handling your legitimately owned archives while keeping processing local and controlled.
________________________
FileBrio RAR Master — part of the FileBrio Office Suite — is a privacy-first, offline Windows toolkit for diagnosing and safely regaining access to your own password-protected RAR / WinRAR archives.
- Local processing only — nothing leaves your PC.
- Smart diagnostics to separate password issues from corruption.
- Owner-verified recovery workflows designed strictly for legitimate use.
Reminder: FileBrio RAR Master may be used only with archives you own or are explicitly authorized to access. It performs all analysis and recovery operations locally on your device, without uploading data anywhere.
________________________
🔐 Safer Alternatives to Heavy Wordlists
In many scenarios, you never need to touch heavy wordlists at all. Safer approaches can dramatically reduce both risk and effort:
- Memory and context work: Reviewing how you used passwords in that period of your life; see guides on practical retention strategies for RAR passwords ↗️ to improve future behavior.
- Metadata and naming clues: Your file names, folder structures, and archive labels can narrow down likely themes, which you can explore mentally rather than by brute enumeration.
- Dummy test archives: Creating harmless sample archives to understand how RAR behaves with certain passwords and settings, without risking real data.
- Archive diagnostics first: Confirming that the archive is technically sound, not corrupted or incomplete, before spending time on guesses.
These approaches reduce the pressure to “throw a wordlist at the problem” and instead lead you toward intentional, legally safe workflows that align with your real password habits.
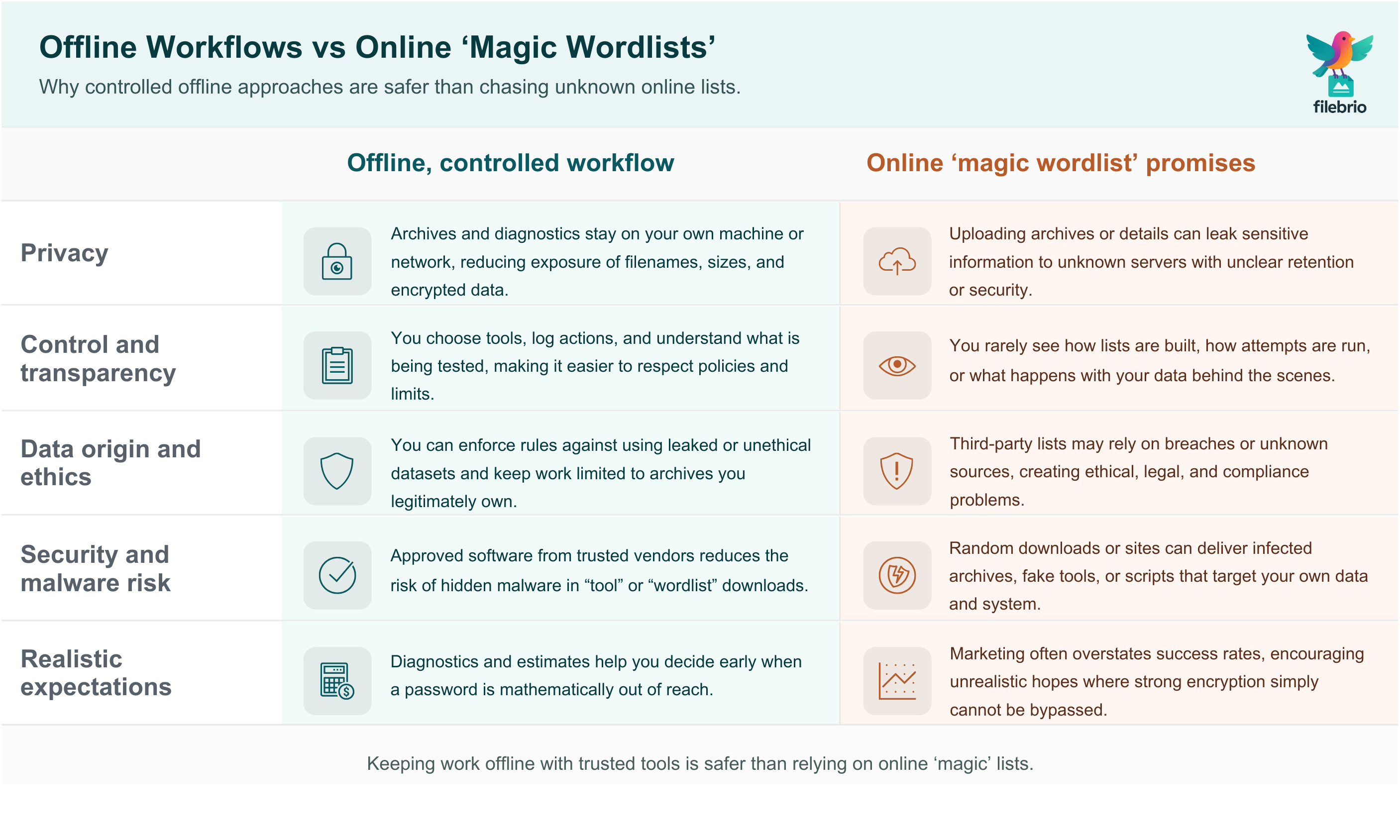
🖥️ Offline Workflows vs Online “Magic Wordlists”
Searching online for ready-made wordlists or sites that promise to “test passwords for you” is risky for several reasons:
- Privacy exposure: Uploading your encrypted archive or even describing it in detail may leak sensitive information.
- Unclear data origins: Some lists are compiled from breaches and leaks, which raises ethical and legal problems.
- Misleading marketing: Some services dramatically overpromise what they can do with limited compute and time.
- Malware risk: Downloads labeled as “wordlists” or “RAR tools” may contain malicious code.
It is generally far safer to keep everything on your own machine and rely on controlled offline tools. Articles about why offline recovery tools are safer for privacy ↗️ and why online RAR password tools so often fail ↗️ explain the broader implications.
When you combine offline workflows, proper diagnostics, and realistic feasibility estimates, you are less likely to chase unrealistic promises or expose your archives to third parties unnecessarily.
🛡️ How to Protect Yourself From Misuse and Data Exposure
Even if your intentions are legitimate, working with anything related to password attempts requires strong self-protection measures. You want to avoid accidentally building a workflow that could harm you or others.
Key protective practices include:
- Limit scope: Work on a copy of the archive when possible, not the only existing instance.
- Separate environments: Use a clean, well-maintained system for any sensitive tasks. Avoid mixing unknown software and personal data.
- No unauthorized data: Do not import unknown lists, especially those built from leaked sources, into your workflow.
- Monitor feasibility: Revisit whether a task is still worth the effort; if an archive appears mathematically out of reach, accept that limit.
- Learn from the experience: Use the situation to design better future password and archive practices so the same problem is less likely to repeat.
Guides such as strengthening RAR archive security while preserving future access ↗️ help you design new workflows that are both safer and more robust, so “wordlist panic” is less likely to happen again.
🧰 Secure Offline Workflow With FileBrio RAR Master
When you need to go beyond pure memory work and still stay within safe, lawful boundaries, you want a workflow that is:
- Completely offline to protect privacy.
- Transparent about what is being checked and why.
- Aligned with realistic limits on what your hardware and encryption settings make possible.
FileBrio RAR Master is built as a privacy-first, Windows-based toolkit for legitimate archive owners. It fits into this picture by offering:
| Stage | Relevant FileBrio Capability |
|---|---|
| Early evaluation | Archive diagnostics and metadata inspection to confirm format and basic health before any intensive work. |
| Feasibility assessment | Support for comparing offline vs online approaches through resources like the online vs offline comparison guide ↗️. |
| Time estimation | Integration with high-level estimation logic (and companion materials) so you can reason about expected effort realistically. |
| Safe access tools | Dedicated modules for legitimate owners, such as the RAR password recovery component and related safety documentation. |
You can start by reading the feature overview, evaluate your situation, and then use the FileBrio tools download page ↗️ to install the suite on a machine you control. This keeps sensitive archives away from cloud services and untrusted environments.
________________________
FileBrio RAR Master — a secure, offline Windows toolkit for regaining access to your own password-protected RAR / WinRAR archives while keeping all data strictly on your device.
- Offline-only processing — never uploads your archives.
- Smart issue detection — password vs corruption.
- Fast recovery workflow optimized for legitimate ownership.
⬇️ Download FileBrio RAR Master
Reminder: FileBrio RAR Master is intended only for archives you own or are explicitly authorized to access. All operations run locally on your PC.
________________________
📚 When to Involve Professionals and Prove Ownership
Sometimes, even with good diagnostics and memory work, you reach a point where you cannot decide whether further attempts are justified. In those cases, involving professionals may help — but only if you can demonstrate clear ownership and stay within legal frameworks.
In corporate or regulated environments, you may need to:
- Document who owns or controls the archive.
- Record why access is required (compliance, audits, incident response, etc.).
- Follow internal procedures that govern work with encrypted data.
More specialized materials on protecting sensitive files while allowing authorized recovery ↗️ and diagnosing locked RAR archives without risking data loss ↗️ explain how to keep control of the process. The core idea: treat your encrypted RAR archives as critical assets, not just files that can be experimented with freely.
📎 Summary and Next Steps
High-quality wordlists are not magical collections of passwords; they are structured, context-aware guesses derived from how people actually behave. At the same time, they are governed by very real mathematical limits and strict legal boundaries. For many legitimate owners of encrypted RAR archives, the smartest move is to:
- Start with self-analysis, archive diagnostics, and feasibility checks.
- Understand how password length, entropy, and format choices affect what is realistically possible.
- Prefer offline, privacy-preserving tools over online “magic list” promises.
- Use wordlist concepts only as a thought framework, not as an invitation to collect questionable data or run uncontrolled attacks.
- Invest time into future-proofing: better password policies, safer storage, and documented ownership.
If you are currently facing a locked archive, step back from the idea of “there must be a perfect wordlist somewhere”. Instead, use structured resources like explanations of how RAR passwords and encrypted archives work ↗️ and high-level guidance on safe recovery options. Combine that knowledge with offline, responsible tools to decide whether pursuing access is wise — or whether time is better spent improving how you handle encryption going forward.
⚖️ Legal Reminder
This article is provided for general informational and educational purposes only. Any examples, scenarios, or references to password recovery, archive security, or related tools (including FileBrio RAR Master or similar software) are intended solely to help you better understand how to protect and manage your own data.
You may only apply any techniques, workflows, or tools described here to files and archives that you fully own or are explicitly and verifiably authorized to access. Attempting to bypass, remove, or recover passwords for third-party data without clear permission may violate criminal law, civil law, or internal company policies in your jurisdiction.
Nothing in this article constitutes legal advice. Laws and regulations differ between countries and organizations, and you are solely responsible for ensuring that your actions comply with all applicable legislation, contracts, and internal policies. If you are unsure whether a particular action is lawful or permitted, consult a qualified legal professional before proceeding.
🔍 See Also: Further Reading on Safe Access
- Why Common RAR Passwords Fail: Patterns, Risks, and Security Lessons ↗️
- How to Diagnose a Locked RAR Archive Without Risking Data Loss ↗️
- How to Evaluate Safe Options for Regaining Access to a RAR/WinRAR Archive You Own ↗️
- FileBrio RAR Master: FAQ for RAR Users ↗️
- How to Strengthen RAR Archive Security While Preserving Future Access ↗️