
How RAR Header Encryption Affects Recovery Feasibility and What Clues It Still Reveals
When you open a RAR archive and see nothing—no filenames, no metadata, no hints about what the file contains—it can feel like the archive is “broken.” But in many cases, the file is perfectly healthy. What you’re seeing is a deliberate security feature: header encryption.
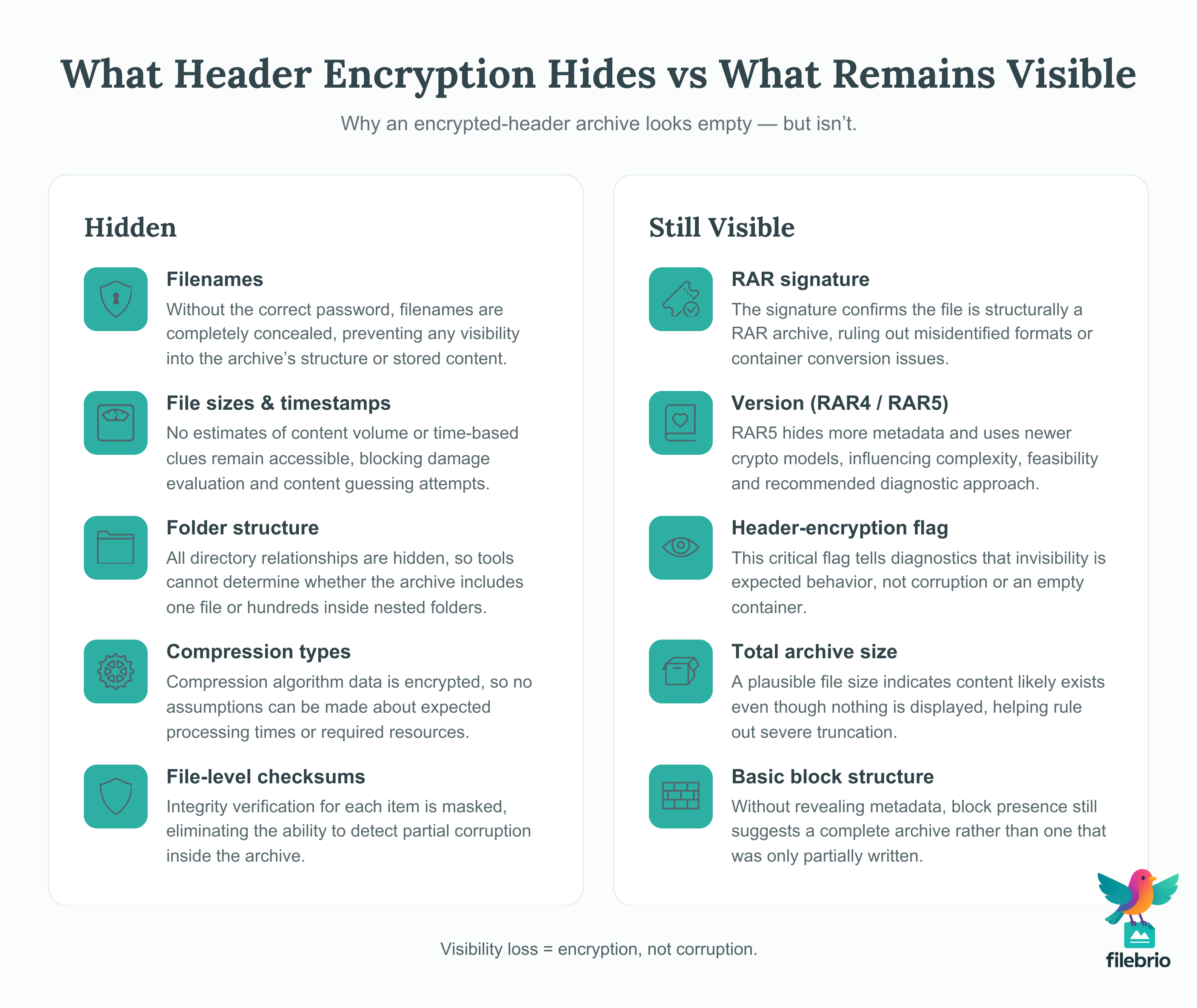
Header encryption hides the archive’s internal structure, file list, and metadata until the correct password is provided. This affects both what you can know about the archive and what remains feasible in terms of recovery. The trick is understanding which clues disappear completely—and which high-level hints remain accessible even when the header is fully locked.
This guide explains how header encryption reshapes recovery feasibility, how to interpret the minimal structural signals that remain visible, and what safe next steps legitimate users can take.
🧭 Navigation
🔍 Introduction
RAR’s header encryption feature is one of its most privacy-protective capabilities. When enabled, it hides the archive’s file list, metadata, sizes, names, and even timestamps. The result is that when you open the archive with the wrong password—or no password—you simply see an empty interface. This can easily lead to confusion: “Is the file broken? Is it corrupted? Is it empty?”
Understanding what header encryption conceals—and what remains detectable—helps you determine whether the file is healthy, whether password access is still feasible, and whether damage has affected the structure in ways that complicate recovery.
⚡ TL;DR — Header Encryption & Recovery Feasibility at a Glance
Header encryption hides your archive’s internal contents completely. Without the correct password, you cannot see filenames, sizes, timestamps, or any of the structural metadata inside the archive.
But the archive still reveals minimal structural clues that indicate whether it’s healthy, how consistent the format is, and whether corruption is likely. These clues are crucial for determining if recovery remains feasible.
📦 What Header Encryption Actually Hides
When header encryption is turned on (a user option during RAR creation), the archive conceals:
- All filenames
- Folder structure
- Compression types
- File sizes and timestamps
- Compression ratios
- Checksums for individual files
The archive effectively acts as a sealed black box. Until the correct password is provided, no tool—local, offline, or cloud-based—can read these internal structures.
This has strong implications for recovery feasibility. Unlike a corruption-only case, where tools can inspect structural metadata, a fully header-encrypted file provides almost nothing to work with.
For example, users analyzing damaged archives often rely on methods found in resources like ways to prevent corruption in your RAR files ↗️ or how to handle your damaged RAR file safely ↗️. But those methods depend on partial visibility of internal metadata—visibility that header encryption removes entirely.
🔐 Why Header Encryption Makes Recovery Harder
Because header encryption removes critical structural insight, recovery feasibility shifts dramatically compared to an ordinary, non-encrypted header archive. In regular archives, you can see filenames, sizes, compression types, and partial checksums, all of which help estimate access feasibility.
With header encryption, these clues disappear. Even foundational diagnostics—like whether a file list exists—become impossible until the password is entered.
For example, determining whether your archive is locked or damaged becomes more complex. Normally, you can rely on strategies similar to those summarized in how to distinguish issues blocking your RAR file ↗️ or how to safely diagnose your locked RAR file ↗️. But with header encryption, those insights are significantly limited.
This doesn’t mean recovery is impossible—it simply means that analysis must shift from inspecting internal metadata to observing external structural clues.
💡 How FileBrio RAR Master Interprets Header Encryption Signals
When a RAR archive shows no filenames, no metadata, no previews, and behaves like a sealed box, it’s difficult to know whether you’re dealing with real header encryption or an archive that’s corrupted, truncated, or partially damaged. This uncertainty is the core pain point: without clarity, it’s easy to take the wrong action and make diagnostics harder or even harm a recoverable archive.
| Common Scenario | Hidden Risk |
|---|---|
| Empty window, no filenames visible | Mistaking header encryption for corruption |
| Instant password prompt before any preview | Assuming the archive is broken or incomplete |
| Archive size looks large but interface shows nothing | False assumption that the file contains no data |
FileBrio RAR Master—part of the FileBrio Office Suite—solves this uncertainty by giving you a controlled, offline, diagnostics-first workspace that reveals the few high-level structural clues that encrypted headers still expose:
- Header-encryption detection: instantly confirms when “no filenames” is an intentional privacy feature, not corruption.
- RAR4 vs RAR5 awareness: evaluates format behavior and metadata visibility limits.
- Block-structure scanning: checks whether the archive is healthy or truncated—without extracting a single file.
- Safe feasibility analysis: helps legitimate users judge whether recovery is realistic before wasting time on wrong strategies.
- Zero-upload privacy: every operation is local—no cloud tools, no exposure risks.
Instead of guessing why your RAR archive reveals nothing, FileBrio RAR Master gives you a clear, offline explanation of what’s happening and what’s realistically possible next.
________________________
FileBrio RAR Master — part of the FileBrio Office Suite — is a privacy-first, offline Windows toolkit for diagnosing and safely regaining access to your own password-protected RAR / WinRAR archives.
- Local processing only — nothing leaves your PC.
- Smart diagnostics to separate password issues from corruption.
- Owner-verified recovery workflows designed strictly for legitimate use.
Reminder: FileBrio RAR Master may be used only with archives you own or are explicitly authorized to access. It performs all analysis and recovery operations locally on your device, without uploading data anywhere.
________________________
🧩 What Clues Still Remain Visible Even With Encrypted Headers
Even though header encryption blocks access to content and metadata, some high-level structural signals remain readable. These include:
- RAR signature (confirming the file is a RAR archive)
- Archive version (RAR4 vs RAR5)
- Presence of main header (but not its decrypted contents)
- Total file size
- Basic block structure (without file-level metadata)
- Flags indicating header encryption
These surviving clues can still be interpreted safely to understand whether the archive is healthy or corrupted.
🔬 How to Interpret the Remaining Clues
Even though header encryption hides visibility, the remaining high-level clues can still guide safe analysis:
- If the signature is intact: The archive is structurally valid.
- If the version is clear: Recovery expectations differ (RAR5 has stronger encryption structures and requires more intensive diagnostics).
- If the header-encryption flag is set: An empty file list means “hidden,” not “corrupted.”
- If the file size is plausible: It suggests the archive has content even though it’s not shown.
- If basic blocks are present: Indicates the file was fully written and is not truncated.
These factors often clarify misunderstandings. Many users incorrectly assume the file is broken when, in fact, the file is simply encrypted at the header level.
To support deeper analysis, consider high-level guidance similar to basic checks for encryption modes in your RAR file ↗️ and how to distinguish encryption from corruption ↗️. These insights apply especially well when header encryption hides internal structures.
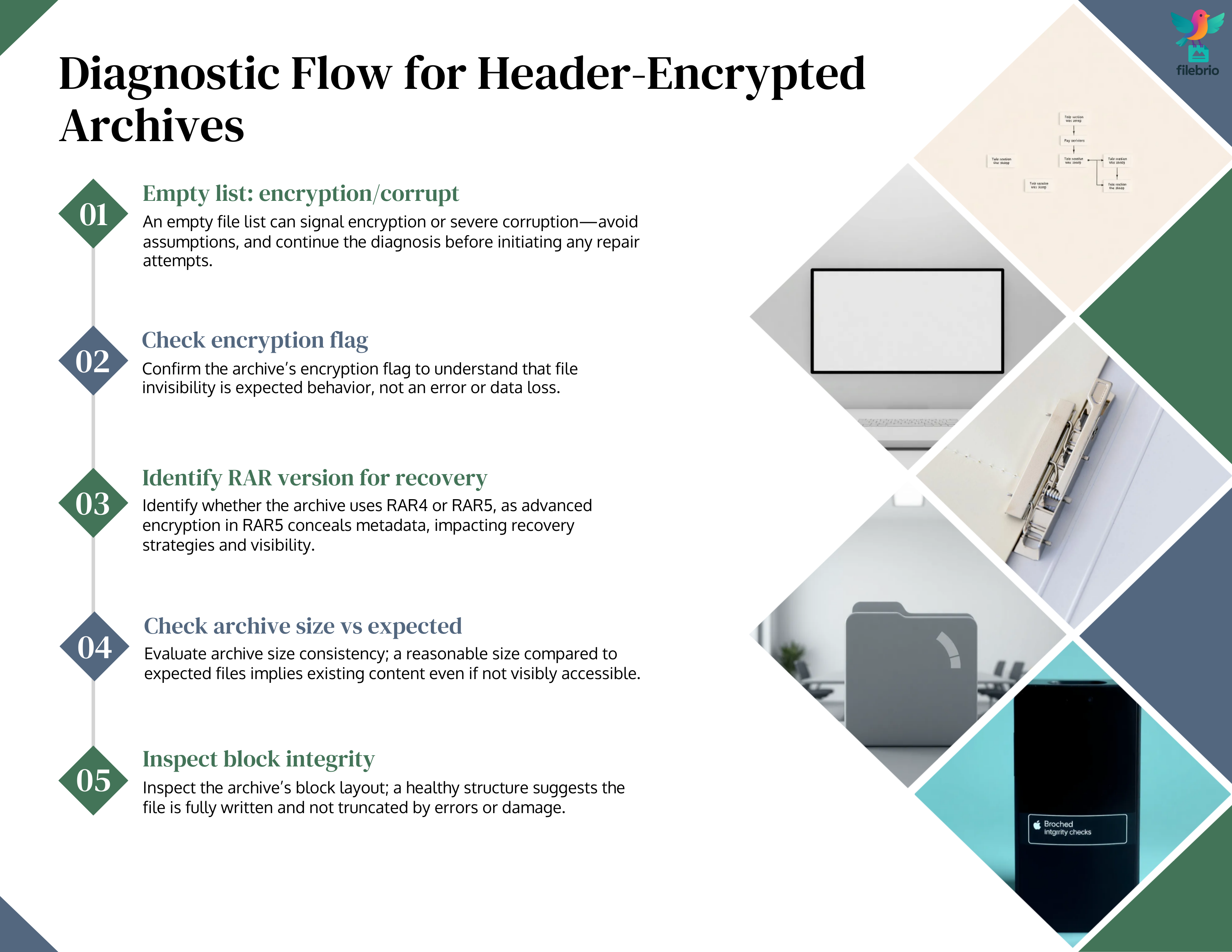
🛠️ Diagnostic Flow: Checking Header Encryption in a Locked Archive
Here is a safe, non-invasive flow for interpreting whether header encryption is active and whether the file appears healthy:
- Observe file list visibility: No filenames = encrypted or extremely damaged.
- Check for header-encryption flags: If present, visibility loss is intentional.
- Look at archive version: RAR5 always hides more metadata by design.
- Confirm structure length: If plausible, the file likely contains data.
- Look for truncation: If the file size is suspiciously small, corruption may be involved.
📊 Tables: Visibility Matrix for Header-Encrypted RAR Archives
Table 1 — Metadata Visibility With vs Without Header Encryption
| Metadata Element | Normal RAR | Header-Encrypted RAR |
|---|---|---|
| Filenames | Visible | Hidden |
| File sizes | Visible | Hidden |
| Timestamps | Visible | Hidden |
| CRC checksums | Visible | Hidden |
| Folder structure | Visible | Hidden |
| Encryption flag | Visible | Visible |
Table 2 — What Each Structural Clue Suggests
| Clue | What It Suggests |
|---|---|
| RAR signature intact | File structurally valid |
| Version identifiable | Archive format stable |
| Header encryption flag set | Empty list is expected |
| Block structure present | File not severely corrupted |
| File size plausible | Likely contains data |
🔐 Secure Offline Solution for Encrypted-Header Archives
Once you confirm that header encryption is active, the next problem appears: how do you analyze the archive safely when no filenames, timestamps, or contents are visible? This lack of visibility tempts many users to upload their archive to online “unlocker” or “preview” sites—yet those services cannot see anything the header encryption hides and simply copy your sensitive archive to remote servers.
| Risky Action | Secure Alternative |
|---|---|
| Uploading the archive to online tools | Keep all analysis inside FileBrio RAR Master, fully offline |
| Running repair tools on the only copy | Non-destructive structure checks before any modification |
| Assuming empty = corrupted | Use header-flag awareness to interpret expected invisibility |
FileBrio RAR Master provides a safe, high-precision diagnostic environment specifically built for header-encrypted RAR archives:
- 100% offline: no servers, no uploads, no exposure of protected data.
- Header-flag intelligence: confirms encryption mode and explains why filenames are hidden.
- Structural health insights: identifies truncation, malformed blocks, or format inconsistencies.
- Version-aware feasibility checks: RAR5’s stronger encryption affects what remains detectable.
- Responsible next-step planning: helps you decide when to focus on password reconstruction vs structural preservation.
For archives where privacy is non-negotiable and header encryption removes almost all visible clues, FileBrio RAR Master offers the safest path to understanding what remains possible—without ever exposing your protected data to the outside world.
________________________
FileBrio RAR Master — a secure, offline Windows toolkit for regaining access to your own password-protected RAR / WinRAR archives while keeping all data strictly on your device.
- Offline-only processing — never uploads your archives.
- Smart issue detection — password vs corruption.
- Fast recovery workflow optimized for legitimate ownership.
⬇️ Download FileBrio RAR Master
Reminder: FileBrio RAR Master is intended only for archives you own or are explicitly authorized to access. All operations run locally on your PC.
________________________
🧱 Hard Cryptographic Limits Imposed by Header Encryption
Header encryption is not a recovery obstacle that can be bypassed through analysis or structural scanning. It is a cryptographic boundary. Until the correct password is provided, no tool—including FileBrio RAR Master—can infer internal metadata or filenames.
These hard limits apply regardless of the archive’s contents, compression formats, or file count. This principle is also described in resources like why your forgotten RAR password cannot be reset ↗️ and how RAR4 and RAR5 secure your protected data ↗️.
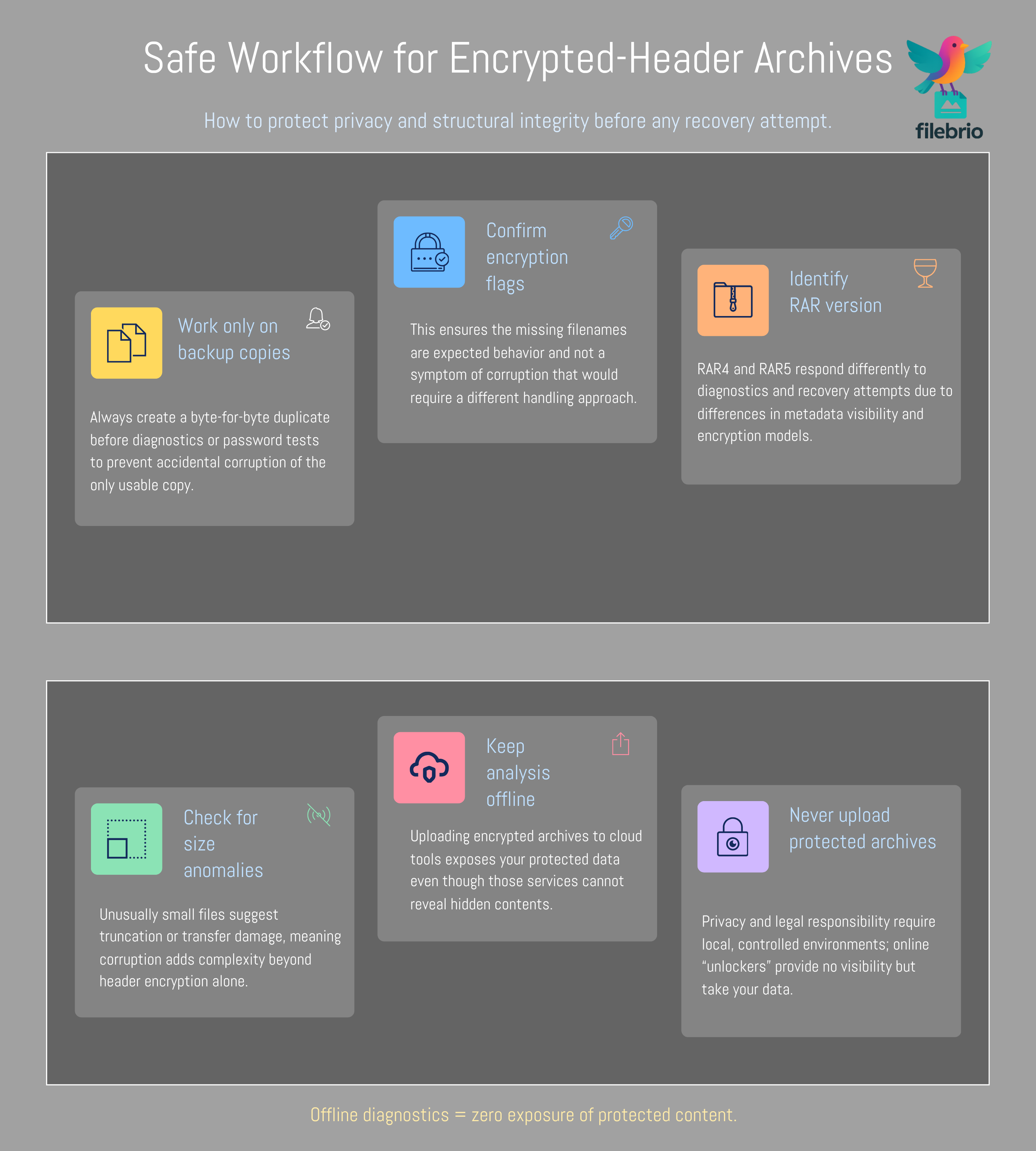
🛡️ Safe Steps to Take Before Any Action
Before taking any steps, legitimate users should avoid modifying the archive. Protective actions include:
- Creating a byte-for-byte backup copy
- Avoiding cloud uploads
- Avoiding repeated extraction attempts that alter timestamps
- Preserving any available metadata outside the archive
This aligns with safe diagnostic practices outlined in initial actions to preserve your damaged RAR data ↗️ and safe approaches to diagnosing your protected archive ↗️.
⚙️ Recommended Safe Workflow for Encrypted-Header Archives
This workflow ensures no further damage while maximizing diagnostic visibility:
- Copy the archive and work only on duplicates.
- Inspect structural clues and detect header encryption flags.
- Determine RAR version to evaluate cryptographic strength.
- Check for file truncation or unusual size anomalies.
- Use offline local tools for privacy, never online viewers.
This general workflow echoes principles from why offline tools keep your encrypted RAR data private ↗️ and steps to check your inaccessible archive safely ↗️.
📘 Realistic Example Cases
Case 1 — Header Encrypted, Archive Healthy
The archive opens with no file list but shows correct signature, version, and healthy block structure. This is a classic example of a secure, header-encrypted archive.
Case 2 — Header Encrypted + Truncated File
File size is unusually small, and structural blocks terminate abruptly. This suggests corruption on top of header encryption.
Case 3 — Corruption Without Header Encryption
Filenames appear but extraction fails. This indicates damage but no header encryption.
🚫 Common Misconceptions About Header-Encrypted Archives
- “The file is empty.” — No, it is hidden.
- “The archive is broken.” — Not necessarily; encryption hides contents.
- “Tools can guess filenames.” — Impossible without the password.
- “Corruption always hides files.” — Only severe damage does; encryption does it by design.
🏁 Summary
Header encryption dramatically alters how RAR archives behave under inspection. It removes visibility, not functionality. Understanding what remains visible helps legitimate users avoid misinterpreting hidden contents as corruption.
⚖️ Legal & Ethical Reminder
This article is provided for general informational and educational purposes only. Any examples, scenarios, or references to password recovery, archive security, or related tools (including FileBrio RAR Master or similar software) are intended solely to help you better understand how to protect and manage your own data.
You may only apply any techniques, workflows, or tools described here to files and archives that you fully own or are explicitly and verifiably authorized to access. Attempting to bypass, remove, or recover passwords for third-party data without clear permission may violate criminal law, civil law, or internal company policies in your jurisdiction.
Nothing in this article constitutes legal advice. Laws and regulations differ between countries and organizations, and you are solely responsible for ensuring that your actions comply with all applicable legislation, contracts, and internal policies. If you are unsure whether a particular action is lawful or permitted, consult a qualified legal professional before proceeding.