GPU Acceleration in Password Analysis: Benefits, Limits, and Safety Considerations
Modern GPUs can perform massive amounts of mathematical operations in parallel, which is why people often hear that “GPUs can try millions of passwords per second.” While this is true in principle, the real situation with encrypted RAR archives—especially RAR5—is far more nuanced. Password-guessing speed depends on format, password length, entropy, device power limits, and safety practices. This article helps legitimate users understand what GPU acceleration can and cannot do when evaluating access to their own encrypted archives.
You’ll learn the real benefits, constraints, and privacy-first practices needed when exploring feasibility—not tactical procedures. This is a conceptual, high-level explanation intended for users checking the feasibility of accessing archives they rightfully own.
🧭 Navigation
Important
The information provided in this article applies exclusively to RAR / WinRAR archives for which you have full, demonstrable ownership or properly documented authorization. If you are not the rightful owner of the data, do not directly control it, or cannot clearly prove permission to access it, you must stop immediately. Attempting to access, recover, or modify data without explicit authorization may violate criminal law, civil statutes, corporate compliance requirements, and privacy regulations in many jurisdictions. You alone are responsible for ensuring that your actions are lawful and properly permitted before proceeding.
⚡ TL;DR — What GPUs Actually Change in RAR Password Guessing
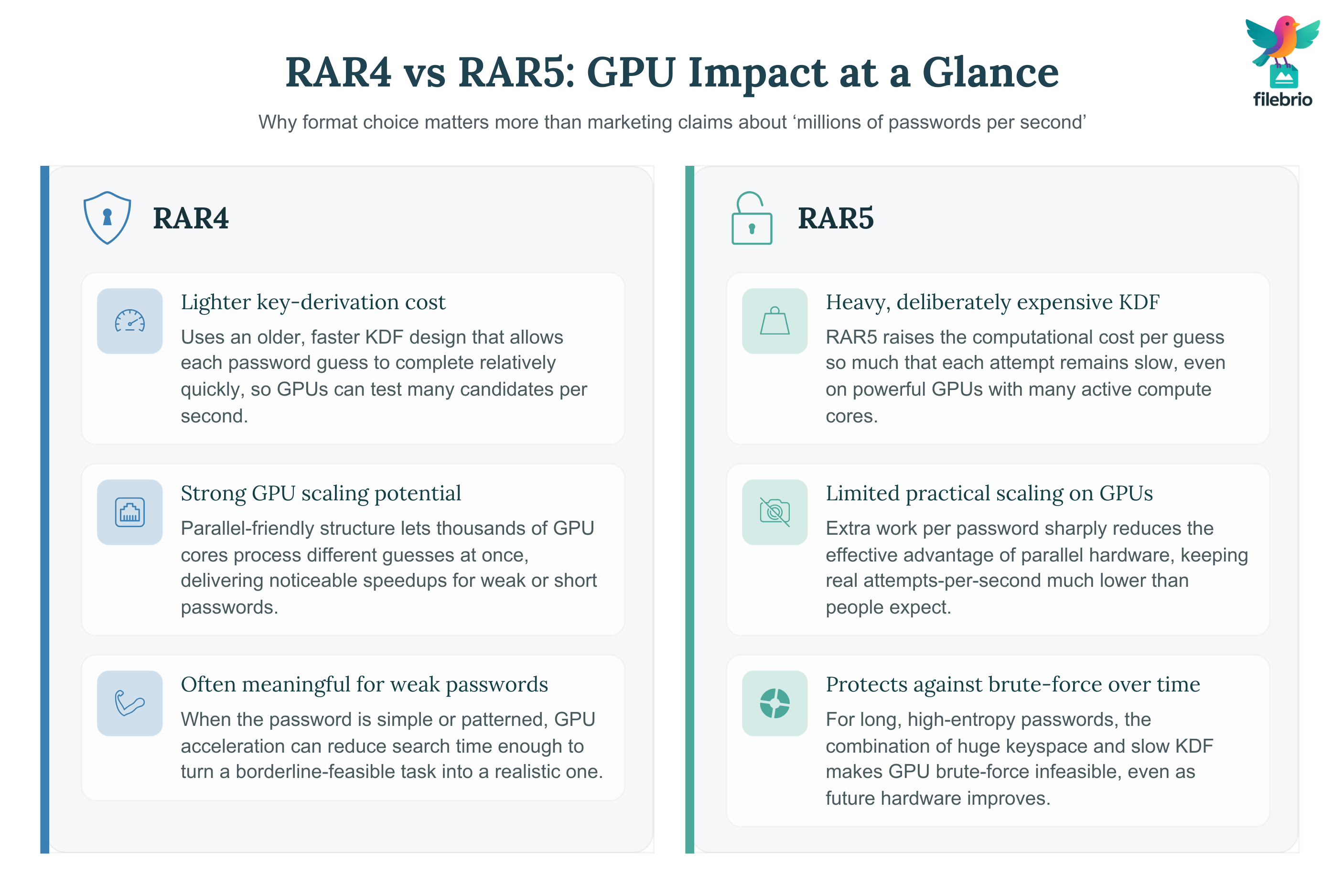
GPUs can dramatically accelerate some types of password-guessing tasks thanks to their massive parallelism, but their benefits apply unevenly to RAR archives. RAR4 uses an older, lighter key-derivation design that scales well on GPUs, so weak or very short passwords may be testable faster. RAR5, however, deliberately uses a much heavier KDF that slows each attempt, sharply reducing the advantage GPUs normally provide. Even powerful GPUs cannot meaningfully help with strong, long, or high-entropy passwords; the search space simply becomes too large for any hardware to handle.
Real feasibility depends on the password’s structure, not just GPU speed. Short, predictable, or pattern-based passwords may fall into small, dense regions of the search space where GPU acceleration is useful. But random, lengthy, or unique passwords remain effectively unreachable—millions of attempts per second do not change that.
For legitimate users evaluating their own encrypted archives, GPU analysis must always be done offline to avoid exposing sensitive data. A privacy-first tool such as FileBrio RAR Master helps determine whether an archive is RAR4 or RAR5, assess feasibility, distinguish encryption from corruption, and estimate realistic recovery boundaries without uploading anything. The key lesson: GPUs can help only under narrow conditions, and they cannot overcome strong cryptography, forgotten long passwords, or the fundamental mathematical limits of protected RAR archives.
🎛️ GPU Acceleration Basics: Why Parallelism Matters
GPUs excel at performing the same mathematical operation many thousands of times in parallel. Password-guessing involves repeatedly running cryptographic functions with different candidate passwords. If an algorithm allows highly parallel work, GPUs can significantly increase the number of candidates processed per second.
GPU acceleration is conceptually beneficial because:
- Thousands of cores: ideal for repeating similar operations at scale.
- High throughput: suited for cryptographic hashing tasks with low memory cost.
- Parallelizable tasks: each password candidate is an independent computation.
But this only works well when the encryption scheme does not intentionally slow down or complicate parallel attempts. RAR5’s improved KDF design does exactly that. A related discussion can be found in RAR5 key-derivation security basics ↗️.
| Factor | Effect on GPU Acceleration |
|---|---|
| Parallelism | More parallel tasks → better GPU scaling. |
| Memory usage | High memory algorithms reduce GPU efficiency. |
| Algorithm design | KDFs like RAR5 intentionally increase per-guess cost. |
🧱 Why RAR4 and RAR5 React Differently to GPU Acceleration
RAR4 and RAR5 both use AES-based encryption, but their key derivation mechanisms differ dramatically. GPU performance depends largely on the cost of each key derivation, not only on the cipher.
| Format | KDF Complexity | GPU Scaling | Practical Result |
|---|---|---|---|
| RAR4 | Older design, quicker per-password test. | Good GPU scaling—large speedups possible. | GPU feasibility often meaningful. |
| RAR5 | More expensive KDF with significantly higher cost. | Reduced GPU scaling. | High complexity quickly becomes infeasible. |
Because RAR5’s KDF is deliberately heavy, it slows down each password attempt, making brute-force attempts exponentially harder. This is by design. Why? Because it protects your data long after hardware improves.
This is also why high-level feasibility guides such as understanding password-guessing time estimates ↗️ are so critical: raw GPU power never guarantees access.
🚀 Practical Speed: What GPUs Improve and What They Don’t
It’s common to hear statements like “a GPU can test millions of passwords per second,” but the real numbers depend on multiple factors. The most important are:
- Archive format (RAR4 vs RAR5)
- Password length and entropy
- GPU model and thermal limits
- Algorithm-specific memory usage
| Scenario | GPU Impact | Explanation |
|---|---|---|
| Short, simple password | High benefit | Low entropy → few candidates → GPU helps. |
| Medium complexity password | Moderate benefit | Parallelism helps, but keyspace grows quickly. |
| Strong, long, random password | Nearly zero practical benefit | Keyspace too large → millions/sec don’t matter. |
Even strong GPU hardware does not meaningfully shrink impossible keyspaces, which is why articles like why some RAR archives become impossible to open ↗️ stress that encryption is working properly when it prevents unauthorized (or forgotten) access.
💼 All-In-One Solution for Evaluating GPU Feasibility on Your Own Archives
Users often run into confusion when trying to understand whether GPU acceleration might help with their own encrypted archive. Typical pain points include:
- Not knowing whether the archive uses RAR4 or RAR5.
- No clear way to interpret GPU feasibility without technical expertise.
- Difficulty distinguishing strong encryption from file corruption.
- All information scattered across multiple tools or online sources.
FileBrio Office Suite—and especially FileBrio RAR Master—addresses these uncertainties by giving you one offline environment to evaluate format, complexity, and realistic expectations without exposing your data.
| Your Question | How FileBrio RAR Master Helps |
|---|---|
| “Does my archive benefit from GPU acceleration?” | Format detection identifies RAR4 vs RAR5 instantly. |
| “Is the archive damaged or just protected?” | Metadata inspection highlights structural errors. |
| “Is recovery feasible at all?” | High-level feasibility estimation explains realistic boundaries. |
| “How do I stay safe during analysis?” | 100% offline workflow prevents data exposure. |
For a deep overview of all capabilities, see the FileBrio RAR Master feature list ↗️.
________________________
FileBrio RAR Master — part of the FileBrio Office Suite — is a privacy-first, offline Windows toolkit for diagnosing and safely regaining access to your own password-protected RAR / WinRAR archives.
- Local processing only — nothing leaves your PC.
- Smart diagnostics to separate password issues from corruption.
- Owner-verified recovery workflows designed strictly for legitimate use.
Reminder: FileBrio RAR Master may be used only with archives you own or are explicitly authorized to access. It performs all analysis and recovery operations locally on your device, without uploading data anywhere.
________________________
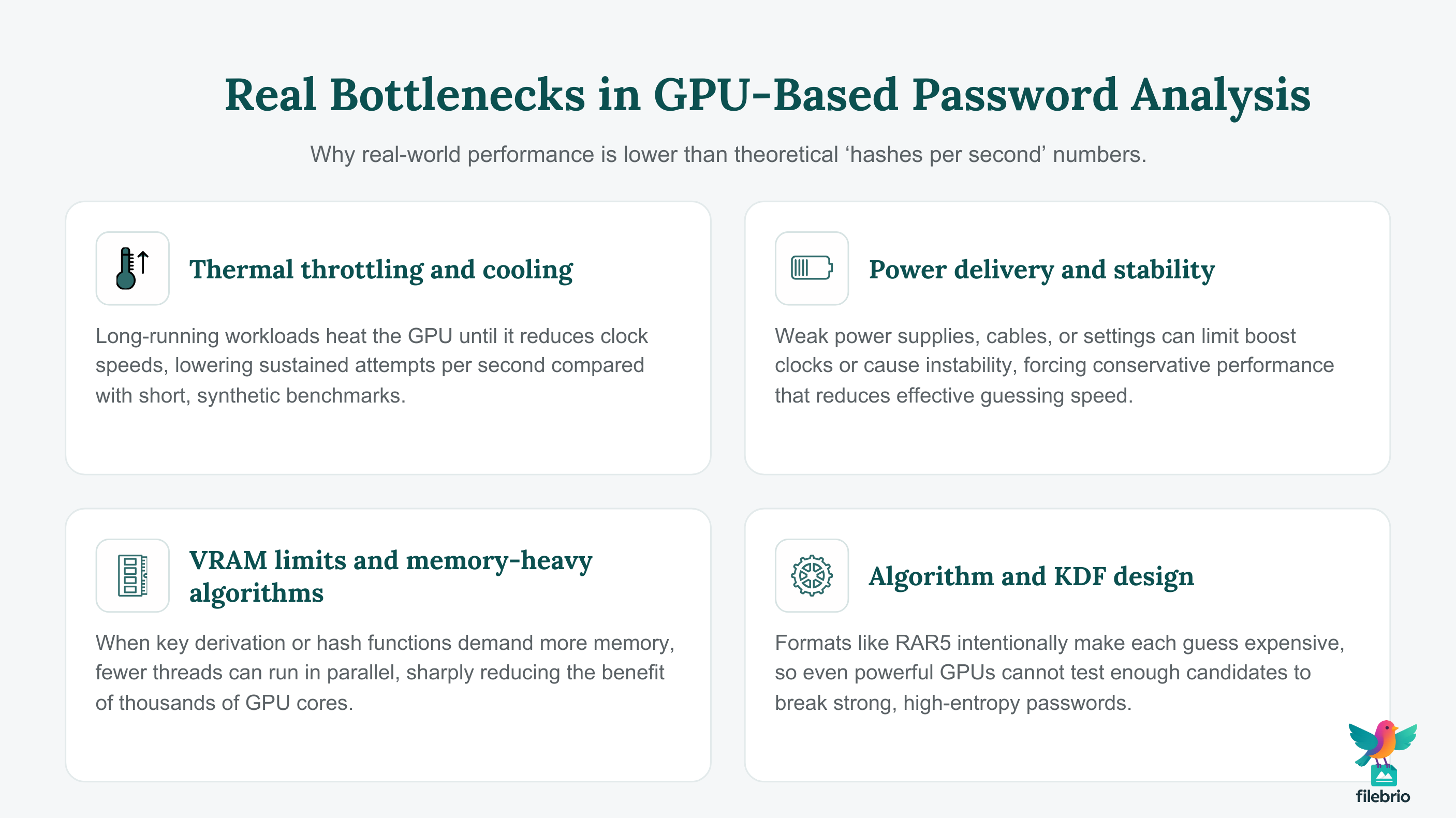
⚙️ Real Bottlenecks: Heat, Power, Memory, and Algorithm Choice
Even powerful GPUs encounter bottlenecks during password-guessing tasks. Understanding these constraints helps set realistic expectations:
- Thermal throttling: GPUs reduce performance when overheating.
- Power delivery: Insufficient power limits sustained performance.
- VRAM constraints: Algorithms with high memory cost run slower on GPUs.
- Algorithm design: RAR5’s heavy KDF is intentionally GPU-resistant.
| Bottleneck | Impact on Speed | Why It Matters |
|---|---|---|
| Thermal throttling | Reduces sustained attempts per second. | Guessing requires long, continuous workloads. |
| High KDF cost (RAR5) | Each attempt is slow, even on GPUs. | Designed to limit brute-force attempts. |
| Large keyspace | Speed improvements become irrelevant. | Strong passwords remain out of reach. |
🔒 Safety and Privacy Considerations for Legitimate Users
Even when using GPU acceleration for your own archives, safety remains essential. Risks emerge not from the concept of GPU computation, but from where and how you attempt to analyze your archive.
- Never upload encrypted archives to unknown online tools.
- Always work offline to maintain confidentiality.
- Use reputable, locally installed software to avoid malware.
- Understand legal boundaries when handling encrypted data.
These principles align with broader guidelines discussed in how to ensure you’re recovering only RAR files you own ↗️ and legal considerations for working with your own encrypted archives ↗️.
🧲 Secure Offline GPU Analysis and High-Level Estimation
For users evaluating their own locked archives, GPU acceleration is only one part of the decision-making process. Equally important is understanding feasibility, time ranges, and realistic expectations—without exposing the archive to external servers or tools.
FileBrio RAR Master provides an integrated offline environment for:
| User Need | FileBrio Capability |
|---|---|
| Determine whether GPU acceleration applies | Format-aware detection of RAR4 vs RAR5. |
| Estimate feasibility in a safe way | High-level recovery estimations based on entropy and KDF. |
| Ensure full privacy | Offline-only workflow, no uploads. |
| Plan next steps responsibly | Built-in safety guidance aligned with cryptographic limits. |
To compare secure offline methods with unsafe online approaches, see the FileBrio offline vs online comparison ↗️. For feasibility estimates, the RAR password time-estimation tool ↗️ offers conceptual guidance before taking any action.
You can obtain the toolkit from the official FileBrio download page ↗️ or review the pricing and licensing page ↗️.
________________________
FileBrio RAR Master — a secure, offline Windows toolkit for regaining access to your own password-protected RAR / WinRAR archives while keeping all data strictly on your device.
- Offline-only processing — never uploads your archives.
- Smart issue detection — password vs corruption.
- Fast recovery workflow optimized for legitimate ownership.
⬇️ Download FileBrio RAR Master
Reminder: FileBrio RAR Master is intended only for archives you own or are explicitly authorized to access. All operations run locally on your PC.
________________________
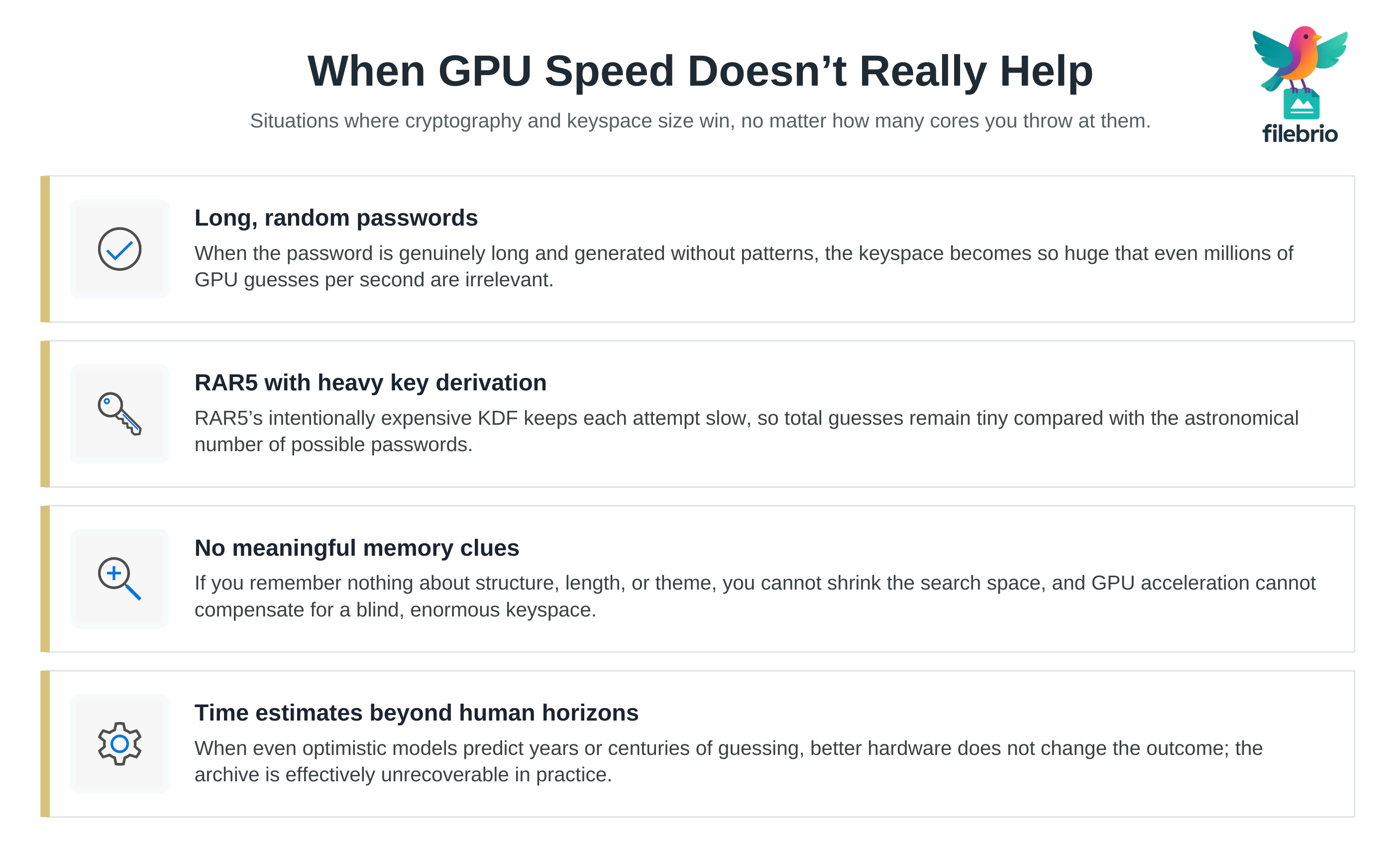
📉 Reality Check: When GPU Speed Doesn’t Meaningfully Help
Even though GPUs are powerful, there are situations where they provide little or no practical benefit:
- The password is long (10+ characters) and random.
- The archive uses RAR5 with strong KDF settings.
- You have no meaningful memory clues to reduce the search space.
- The time estimate exceeds realistic timeframes (months → decades → centuries).
This is exactly why encryption is effective. Articles like RAR file passwords explained ↗️ help clarify how cryptography shapes possible access paths. And when you need a structured evaluation method, how to evaluate safe access options for your own RAR file ↗️ provides a practical, safety-focused framework.
⚖️ Legal Reminder
This article is provided for general informational and educational purposes only. Any examples, scenarios, or references to password recovery, archive security, or related tools (including FileBrio RAR Master or similar software) are intended solely to help you better understand how to protect and manage your own data.
You may only apply any techniques, workflows, or tools described here to files and archives that you fully own or are explicitly and verifiably authorized to access. Attempting to bypass, remove, or recover passwords for third-party data without clear permission may violate criminal law, civil law, or internal company policies in your jurisdiction.
Nothing in this article constitutes legal advice. Laws and regulations differ between countries and organizations, and you are solely responsible for ensuring that your actions comply with all applicable legislation, contracts, and internal policies. If you are unsure whether a particular action is lawful or permitted, consult a qualified legal professional before proceeding.
🧩 See Also: Understanding RAR Protection and Feasibility
- How to Understand Password Guessing Time Estimates ↗️
- Why Some RAR Archives Become Impossible to Open — Security Explained ↗️
- How to Ensure You’re Recovering Only RAR Files You Own ↗️
- How to Strengthen RAR Archive Security While Preserving Future Access ↗️
- RAR Password Estimation & Time-to-Crack Calculator ↗️