
How to Evaluate Safe Options for Regaining Access to a RAR/WinRAR Archive You Own
Few things are as stressful as needing something urgent from a RAR archive you created years ago and suddenly realizing you can’t open it. Maybe WinRAR keeps rejecting your password. Maybe the file throws an error. Or maybe it simply refuses to open and you don’t even know why.
In that moment, it’s easy to panic and search for “quick unlock” tools, random websites, or shortcuts that promise instant access. But blindly trying tools can expose private data, waste time on impossible cases, or even put you in a grey legal zone if ownership is not clearly documented.
The good news: you don’t need guesswork. You can approach the problem systematically — confirming that the archive is really yours, understanding why it fails to open, checking whether recovery is technically feasible, and only then choosing safe, privacy-focused options that stay under your control.
This article takes you through that evaluation process step by step, so you can decide calmly what to do next with a RAR/WinRAR archive you legitimately own.
🧭 Navigation
Important
The information provided in this article applies exclusively to RAR / WinRAR archives for which you have full, demonstrable ownership or properly documented authorization. If you are not the rightful owner of the data, do not directly control it, or cannot clearly prove permission to access it, you must stop immediately. Attempting to access, recover, or modify data without explicit authorization may violate criminal law, civil statutes, corporate compliance requirements, and privacy regulations in many jurisdictions. You alone are responsible for ensuring that your actions are lawful and properly permitted before proceeding.
📌 TL;DR: A Safe Decision Tree for Locked RAR/WinRAR Archives
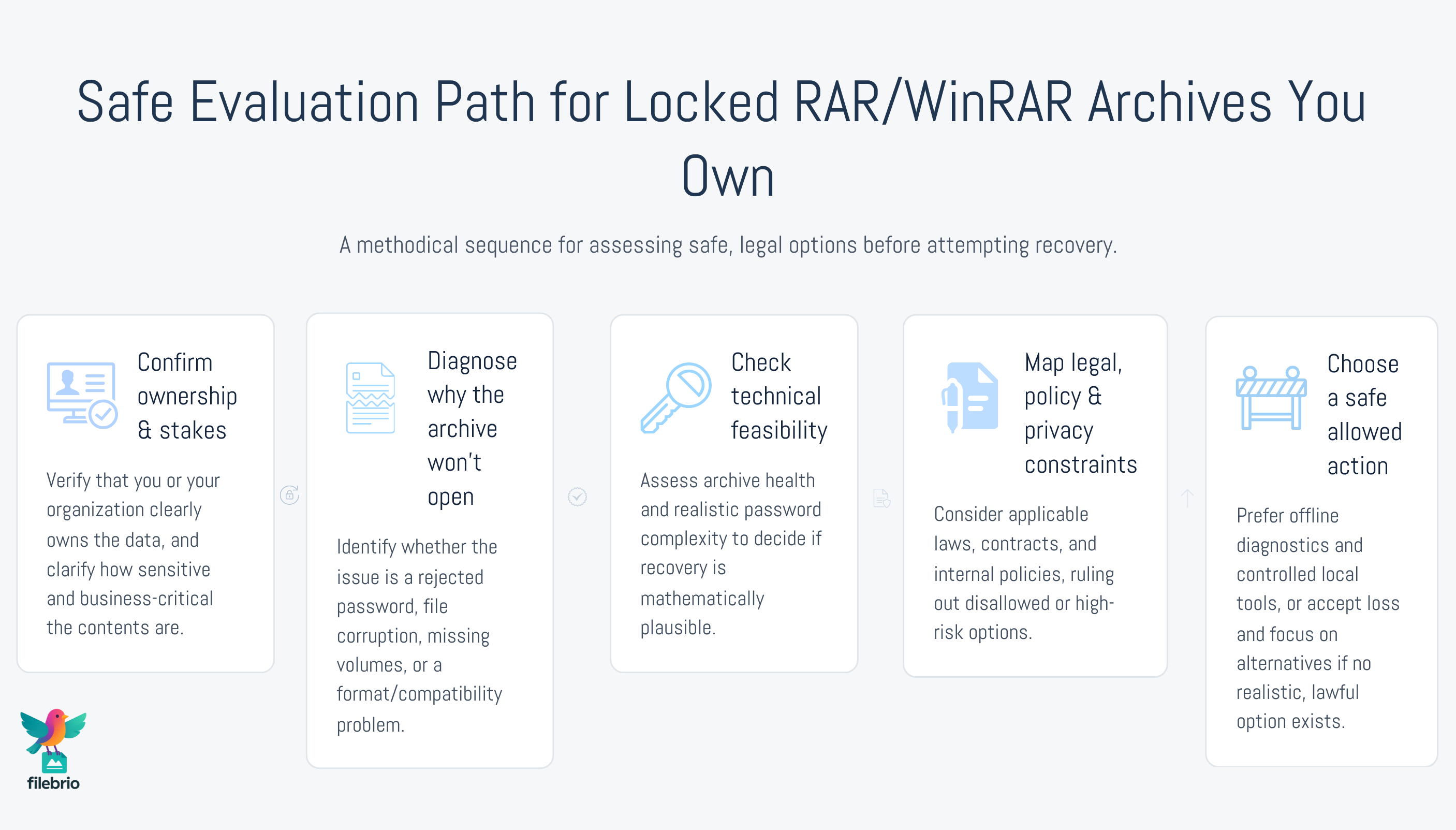
If you’re locked out of a RAR/WinRAR archive you own, don’t start with tools — start with questions. First, confirm that you really have the right to access the contents and that there are no contractual, regulatory, or privacy reasons to stop. Then, analyze why the archive won’t open: is it a forgotten password, file damage, missing volumes, or a format/encoding issue? Each root cause leads to different next steps.
Next, evaluate whether recovery is even technically feasible. RAR encryption has real mathematical limits: for short, simple passwords, local tools may help; for long, random ones, no tool (online or offline) can guarantee success. Structural integrity matters just as much; a heavily corrupted archive might be unrecoverable even if the password is known.
Only after you understand ownership, cause, and feasibility should you choose an action: non-destructive diagnostics, attempts to recall the password, local privacy-focused recovery tools, or — in some cases — accepting that the archive is effectively lost and focusing on backups or alternative sources of the data. Throughout the process, prioritize offline, local methods to avoid leaking sensitive archives to unknown services, and document what you tried so you can improve your workflows and prevent similar emergencies in the future.
🤔 What “Regaining Access” Really Means for a RAR Archive You Own
When people say they want to “regain access” to a RAR archive, they often imagine something like a simple reset: press a button, remove protection, and open the contents. That model works for services with account recovery flows (email, cloud storage, etc.), but it does not match how encrypted archives work.
RAR/WinRAR archives use encryption to tie access directly to the password. There’s no central service holding a spare key for you, and no built-in reset mechanism. As explained in how encryption controls access to your protected RAR contents ↗️, the archive is a self-contained object: if you no longer have the password, you are really asking whether it can be rediscovered or whether another copy of the same data exists elsewhere.
That’s why a safe evaluation process focuses on clarity rather than miracles. You’re asking:
- What is actually blocking access?
- Do I clearly own the data?
- Is there a realistic path to regaining access?
Once those questions are answered, it’s much easier to choose the next step instead of installing random tools in frustration.
🧠 Step 1: Clarify Ownership, Context, and Stakes
Any safe path to regaining access starts with a simple but crucial check: is this archive undeniably yours to work with? That means you either created it, were explicitly entrusted with it, or act on behalf of an organization that clearly controls the data.
Resources like how to verify ownership before accessing your RAR file ↗️ outline practical ways to establish that control — from checking who created the archive and where it’s stored, to reviewing internal documentation and contracts. In corporate environments, you may also need sign-off from information security, legal, or data protection officers.
Alongside ownership, clarify context and stakes:
- What’s inside? (Roughly — never assume; but old project code has different risk than HR records.)
- Who could be impacted? Just you, or clients, colleagues, or customers?
- How critical is the data? Is it nice-to-have, important, or business-critical?
If the stakes are high, it’s worth spending extra time documenting this step. That documentation will be useful later when you consider options under the lens of legal factors when accessing your encrypted RAR files ↗️.
🔍 Step 2: Diagnose Why the Archive Won’t Open
Once ownership is clear, you need to understand what kind of problem you’re facing. “Archive won’t open” can mean several very different things:
- WinRAR prompts for a password, but the ones you try are rejected.
- The archive shows corruption errors, checksum failures, or “unexpected end of archive”.
- The file is not recognized as a RAR archive at all.
A structured approach, like the one described in initial checks when your RAR file won’t open ↗️, helps you separate these scenarios. Complement that with the broader situational view in how to evaluate your situation after losing your RAR password ↗️, which focuses on understanding what changed between the last time the archive was accessible and now.
Key diagnostic questions include:
- Has the file moved between devices or operating systems? (Think path length, filesystem quirks, or transfer errors.)
- Is this a single-volume archive or part of a multi-volume set? Missing parts can block access entirely.
- Do error messages mention passwords, corruption, or format issues? Each points toward different remedies.
For more detailed diagnostic techniques that avoid further damage, see how to safely diagnose your locked RAR file ↗️, which emphasizes non-destructive checks and read-only copies before you try anything else.
🧪 Step 3: Check Technical Feasibility Before You Act
After diagnosing the situation, the next question is simple: is it technically realistic to regain access at all? This depends on two pillars: the health of the archive and the strength of the password.
On the health side, resources like how to verify recoverability of your locked RAR file ↗️ describe how structural checks, size comparisons, and metadata can reveal whether the archive is intact enough to justify further effort. If the file is heavily corrupted, truncated, or missing volumes, even a known password may not restore all data.
On the password side, modern RAR encryption is intentionally resistant to guessing. Articles such as how to judge feasibility of your forgotten RAR password ↗️ and why some RAR archives become impossible to open ↗️ explain that beyond certain entropy thresholds, realistic recovery is no longer possible — no matter what tool or hardware you use.
When evaluating feasibility, ask yourself:
- How long and complex was the likely password? A four-character password built from digits is very different from a long random string.
- Do you remember fragments, patterns, or likely candidates? That can shift feasibility significantly.
- Is there an unencrypted or differently protected copy of the same data? If yes, recovery may not justify the effort.
Understanding these limits up front lets you avoid wasting days or weeks chasing recovery paths that mathematics has effectively closed off.
💼 All-In-One Offline Toolkit for Evaluating Your Options
At this point, you know three things: the archive is yours, you understand the basic failure mode, and you have a rough sense of whether recovery might be possible. Instead of scattering this information across many small utilities, it’s far safer to bring everything into a single, offline evaluation environment.
This is where a dedicated suite like FileBrio RAR Master inside the FileBrio Office Suite becomes valuable. Rather than relying on ad-hoc tools, you can evaluate options in one place, on your own hardware, without sending archives anywhere.
| Evaluation Need | Typical Ad-Hoc Approach | All-In-One Offline Toolkit |
|---|---|---|
| Diagnose why the archive won’t open | Several separate tools, inconsistent views of errors | Centralized diagnostics and status views, aligned with the all-in-one RAR recovery toolkit ↗️ |
| Check structural health and metadata | Manual inspection, risk of accidental modification | Read-oriented inspection workflows and clear health indicators |
| Plan possible recovery steps | Browser searches, unvetted tools, online “unlock” sites | Documented, offline workflows anchored in one trusted application |
Using an integrated toolkit also makes it easier to compare options against your policies and risk appetite, instead of being driven by whichever tool or website you happened to find first.
________________________
FileBrio RAR Master — part of the FileBrio Office Suite — is a privacy-first, offline Windows toolkit for diagnosing and safely regaining access to your own password-protected RAR / WinRAR archives.
- Local processing only — nothing leaves your PC.
- Smart diagnostics to separate password issues from corruption.
- Owner-verified recovery workflows designed strictly for legitimate use.
Reminder: FileBrio RAR Master may be used only with archives you own or are explicitly authorized to access. It performs all analysis and recovery operations locally on your device, without uploading data anywhere.
________________________
⚖️ Step 4: Map Out Legal, Policy, and Privacy Constraints
Technical feasibility is only half of the story. A safe option must also respect legal, contractual, and privacy boundaries. Before you take any active steps, pause and ask how regulations, internal policies, or client agreements might affect what you’re allowed to do.
legal factors when accessing your encrypted RAR files ↗️ explores this from several angles: jurisdictional rules on personal data, sector-specific regulations, and corporate governance. Combined with ethical ways to handle your encrypted RAR files ↗️, it provides a framework for deciding which actions are acceptable and which are off-limits, even if they might be technically possible.
At a minimum, you should consider:
- Data protection laws and confidentiality obligations. Are there restrictions on moving data across borders or into third-party systems?
- Industry-specific rules. For example, legal, medical, or financial records may require strict handling standards.
- Internal policies. Many organizations explicitly forbid uploading sensitive archives to public online services.
Clarity here helps you rule out unsafe “options” early — especially online tools — and focus only on those that keep data within approved boundaries.
🛣️ Step 5: Compare Safe Access Paths from Lowest to Highest Risk
With ownership, diagnostics, feasibility, and legal constraints understood, you can finally compare concrete options. A helpful way to think about this is as a ladder of escalating risk: start with the lowest-risk, highest-control actions and only move upward if absolutely necessary.
A typical ladder might look like this:
- Re-assess the situation and your memory. Use structured reflection techniques (without direct guessing) to recall likely passwords or patterns, as suggested by situational guides like how to evaluate your situation after losing your RAR password ↗️.
- Non-destructive local diagnostics only. Confirm health, encryption, and metadata using safe inspection methods that avoid altering the archive, building on why offline tools keep your encrypted RAR data private ↗️.
- Controlled use of local recovery tools. If technically feasible and legally allowed, consider a privacy-focused RAR password recovery tool ↗️ that runs entirely on your own systems.
- Specialist assistance within your perimeter. In corporate settings, this might mean involving in-house security teams rather than external service providers.
- Accepting loss and focusing on alternatives. If the archive appears mathematically or structurally unrecoverable, shift attention to backups, other data sources, or rebuilding the contents.

Online “instant unlock” services rarely fit into a safe rung on this ladder. They typically combine high privacy risk with uncertain benefit — which is exactly what a careful evaluation process is designed to avoid.
🛡️ Secure Offline Suite for Ongoing RAR Access and Recovery
If you deal with RAR/WinRAR archives regularly — whether as an individual professional or as part of a team — you’ll want something more durable than one-off decisions. A secure offline suite gives you a stable foundation for all future cases, combining diagnostics, feasibility analysis, and responsible recovery inside your own environment.
FileBrio Office Suite, and especially its RAR-focused components, is designed around that idea. Instead of treating each locked archive as an emergency, you can build repeatable workflows that everyone understands and that remain consistent with organizational policies.
- Centralized understanding. Features are organized so users can follow a structured evaluation path rather than jumping between unrelated tools, leveraging the offline vs online RAR recovery comparison ↗️ to reinforce privacy-first habits.
- Controlled, local processing. All operations occur on devices you control, aligning with guidance that emphasizes offline tools and avoiding unnecessary exposure.
- Practical knowledge base. Common questions and pain points can be answered via internal resources and the public RAR user guide and FAQ ↗️, reducing the urge to experiment with untrusted services.
Deploying such a suite from an official channel — for example, by using the FileBrio installer page ↗️ — ensures you have a verified, up-to-date build that can support your workflows over the long term, instead of relying on ad-hoc tools that may disappear or change behavior without warning.
________________________
FileBrio RAR Master — a secure, offline Windows toolkit for regaining access to your own password-protected RAR / WinRAR archives while keeping all data strictly on your device.
- Offline-only processing — never uploads your archives.
- Smart issue detection — password vs corruption.
- Fast recovery workflow optimized for legitimate ownership.
⬇️ Download FileBrio RAR Master
Reminder: FileBrio RAR Master is intended only for archives you own or are explicitly authorized to access. All operations run locally on your PC.
________________________
🧱 Building a Repeatable, Safe Workflow for Future Cases
Once you’ve gone through the evaluation process a few times, patterns emerge. Rather than reinventing it for each new locked archive, convert your approach into a documented workflow that anyone in your role can follow.
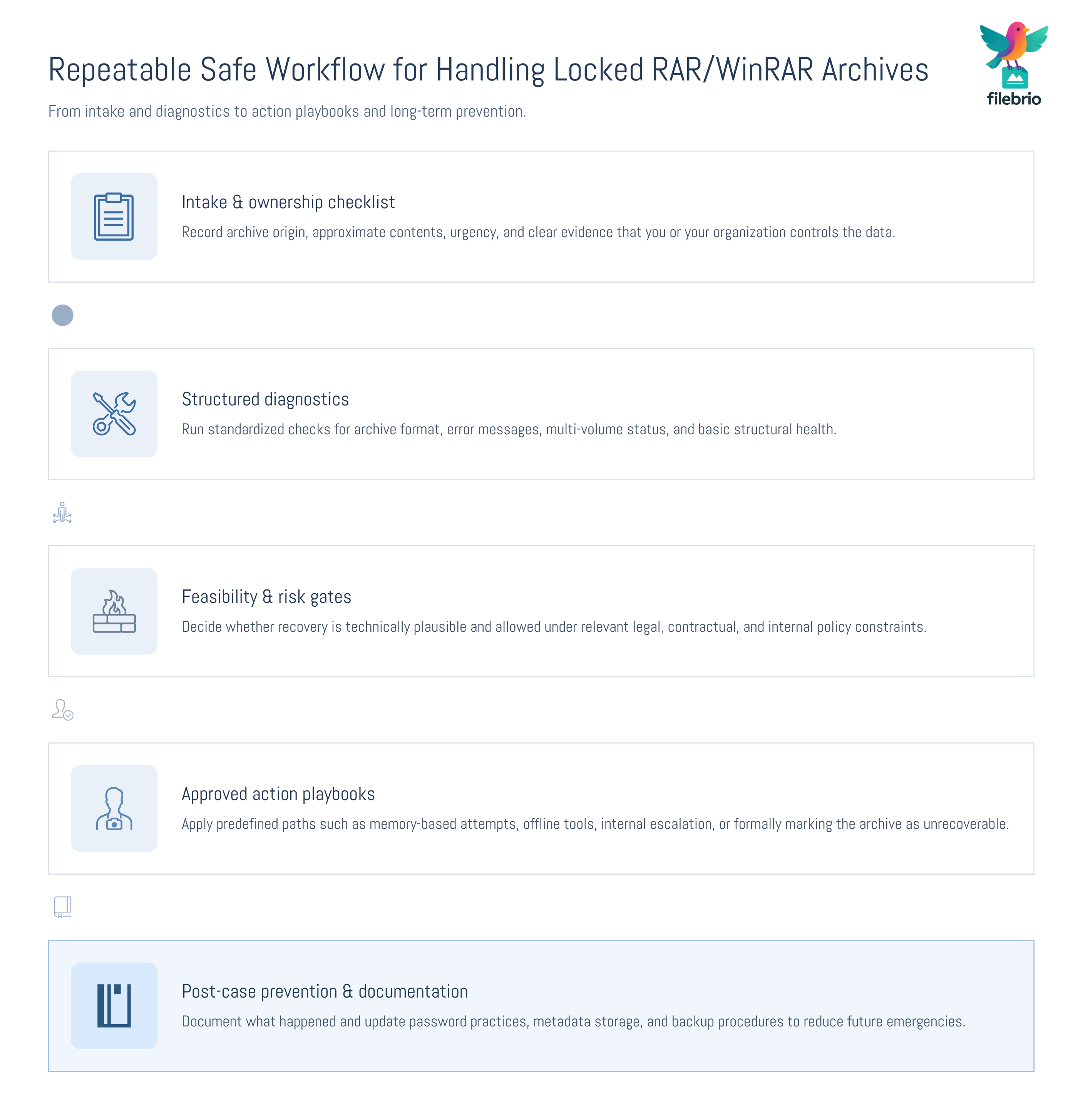
A robust workflow often includes:
- Intake checklist. A simple form capturing archive origin, ownership, approximate contents, and urgency.
- Diagnostic steps. Standardized checks for format, error messages, and structural health, inspired by methods in safe approaches to diagnosing your protected archive ↗️.
- Feasibility decision gates. Criteria based on password complexity and archive condition, aligned with the high-level reasoning in when attempting access to your locked RAR file is viable ↗️.
- Action playbooks. Pre-approved actions for each scenario: memory-based recovery attempts, local tool usage, escalation to internal specialists, or declaring the archive unrecoverable.
These workflows can be scaled from individual use (for example, a freelancer protecting client projects) to team-wide procedures in enterprises. They make decisions more defensible, predictable, and less dependent on one person’s memory of “what we did last time.”
📦 How to Prevent Needing “Emergency Recovery” Next Time
Every locked archive is also a learning opportunity. Once you’ve resolved (or retired) the current case, the most valuable step you can take is to improve your prevention strategy so future archives are easier to work with.
Several topics are especially helpful here:
- Password design. Choose strong but manageable passwords and understand how length and randomness affect security, as explained in how length impacts protection of your RAR password ↗️.
- Metadata and documentation. Store hints, patterns, and recovery-relevant notes securely. how to preserve password metadata for your encrypted RAR files ↗️ offers practical strategies for keeping this information usable over the long term.
- Procedures for high-value archives. For especially important data, define stricter rules for creation, storage, and periodic access checks, so potential issues are discovered while recovery is still realistic.
By translating today’s emergency into tomorrow’s policy — stronger creation habits, better metadata, safer tools — you steadily reduce the chance of finding yourself staring at another locked RAR icon with no idea what to do.
⚖️ Legal Reminder
This article is provided for general informational and educational purposes only. Any examples, scenarios, or references to password recovery, archive security, or related tools (including FileBrio RAR Master or similar software) are intended solely to help you better understand how to protect and manage your own data.
You may only apply any techniques, workflows, or tools described here to files and archives that you fully own or are explicitly and verifiably authorized to access. Attempting to bypass, remove, or recover passwords for third-party data without clear permission may violate criminal law, civil law, or internal company policies in your jurisdiction.
Nothing in this article constitutes legal advice. Laws and regulations differ between countries and organizations, and you are solely responsible for ensuring that your actions comply with all applicable legislation, contracts, and internal policies. If you are unsure whether a particular action is lawful or permitted, consult a qualified legal professional before proceeding.
📚 See Also
- Restoring Access to RAR/WinRAR Archives: Safe and Legal Methods for Handling Your Own Files ↗️
- Opening RAR/WinRAR Archives With or Without a Password: A Practical Guide to Safe Access Options ↗️
- Brute-Forcing a RAR/WinRAR Password? Legal Boundaries, Practical Limits, and Safe Use Cases ↗️
- Removing RAR/WinRAR Passwords Online: Why It’s Unsafe and Secure Offline Alternatives ↗️
- FileBrio RAR Master: Support & Legal (Responsible Use) ↗️
- FileBrio RAR Master: Password Estimation & Time-To-Crack Calculator ↗️
- FileBrio RAR Master: Precautions — Encrypted Headers & When Recovery Is Impossible ↗️