
How to Safely Evaluate RAR Protection Using Dummy Archives (Without Risking Real Data)
If you’re curious how strong your RAR protection really is, it’s tempting to experiment directly on real, sensitive archives. That’s also the fastest way to lose data, leak confidential files, or misconfigure security in a way you can’t undo. Dummy archives solve this tension: they let you test behavior, performance, and workflows in a controlled “sandbox” that feels realistic, but contains nothing you would regret losing or exposing.
In this guide, you’ll see how to use non-sensitive dummy archives to understand RAR protection mechanisms, explore practical limits, and build a safe workflow you can later apply to your real data — without touching the actual confidential files until you are fully prepared and confident.
🧭 Navigation
Important
The information provided in this article applies exclusively to RAR / WinRAR archives for which you have full, demonstrable ownership or properly documented authorization. If you are not the rightful owner of the data, do not directly control it, or cannot clearly prove permission to access it, you must stop immediately. Attempting to access, recover, or modify data without explicit authorization may violate criminal law, civil statutes, corporate compliance requirements, and privacy regulations in many jurisdictions. You alone are responsible for ensuring that your actions are lawful and properly permitted before proceeding.
✨ TL;DR — Safe RAR Testing With Dummy Archives
Dummy RAR archives are test archives that contain only harmless, non-sensitive files (for example sample documents, public images, or placeholder text). They are created specifically so you can experiment safely with passwords, formats, and settings without risking private or business-critical data.
Instead of using real confidential archives, you design several dummy RAR files with different passwords, formats (RAR4/RAR5), header-encryption settings, and file sizes. Then you observe how tools behave when opening, listing, or analyzing these samples. This gives you a realistic feel for how encryption, error messages, and performance work — without exposing actual information.
Using dummy archives, you can test:
- How RAR protection behaves when passwords are correct, incorrect, short, long, or complex.
- What different security options mean (e.g., encrypted headers, filename encryption).
- How long operations roughly take on your hardware under safe, controlled conditions.
- Which workflows are safest for diagnosing locked or damaged archives later.
All of this happens completely offline, against files you intentionally created. Once you’re confident in your workflow, you can apply the same procedures to real archives that you legitimately own — with clearer expectations, fewer mistakes, and a much lower risk of data loss or privacy exposure.
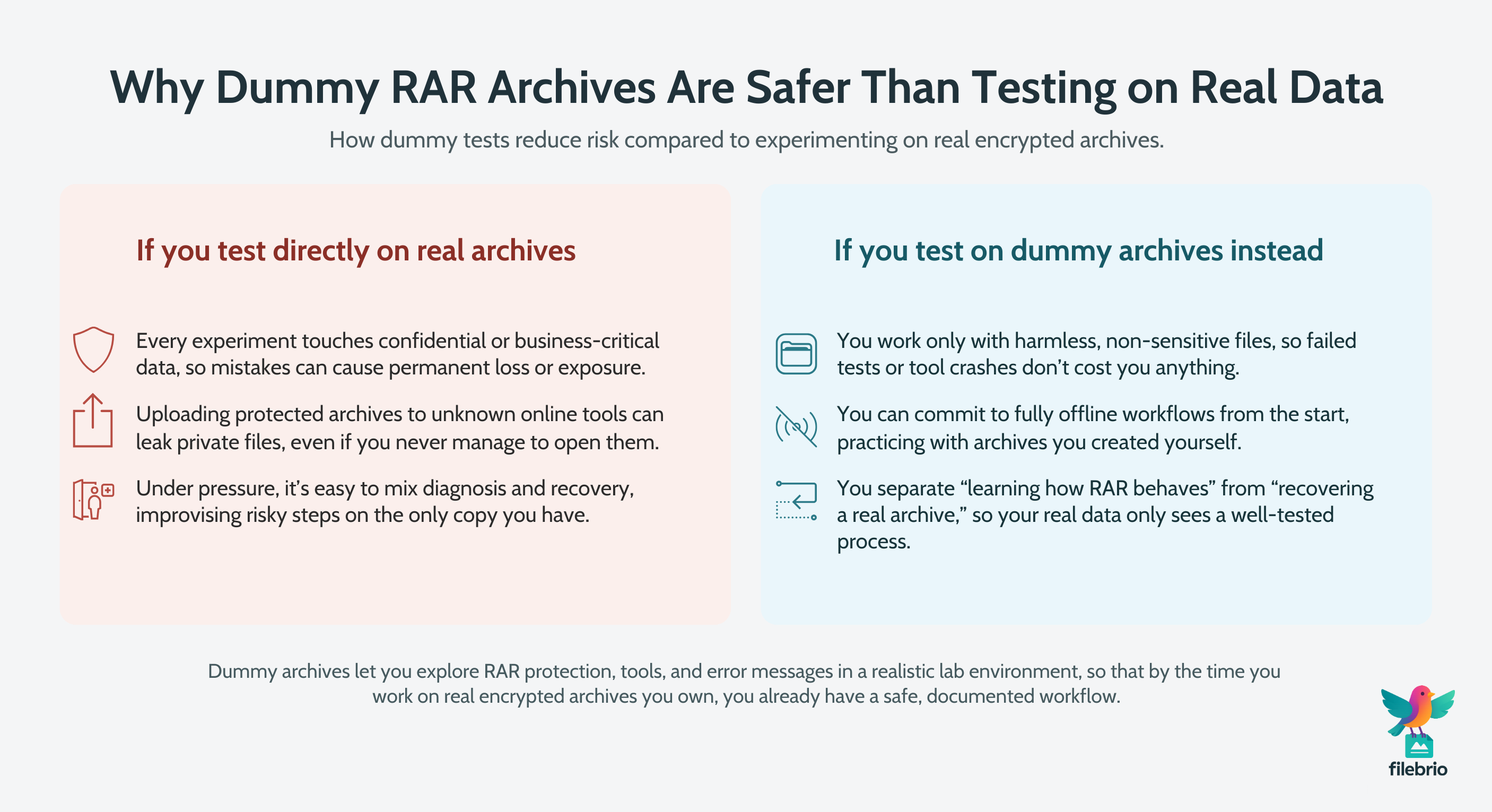
🔐 Why Use Dummy RAR Archives Instead of Real Data?
When people first realize a RAR file is protected by strong encryption, their instinct is often to “test something quickly” on the real archive. That’s understandable, but it blurs two very different goals:
- Understanding how RAR protection works.
- Recovering access to a specific, sensitive archive.
Dummy archives let you separate those goals. Instead of putting your only copy of a confidential project or private backup at risk, you can build a lab of harmless archives and learn in that environment. If something goes wrong, you lose nothing. If a tool behaves unexpectedly, no confidential data is exposed.
There’s another, equally important reason: privacy and legal boundaries. Many users learn the hard way that uploading encrypted RAR files to unknown online services is a serious risk. Those services may store your data, inspect the contents after decryption, or use weak security practices. Offline dummy testing makes it easier to commit to a policy where all serious work happens locally, under your control, on archives that you created yourself.
Finally, dummy archives protect you from “first-step shock.” When you experiment only on real files, every mistake feels critical. With dummy archives, you can calmly explore tools and settings, build confidence, and then move to production archives later with a clear, documented workflow.
🧠 Understanding RAR Protection at a High Level
Before building dummy archives, it helps to understand, at a high level, what you are actually testing.
Modern RAR archives can use strong encryption and key-derivation functions that deliberately slow down guessing attempts. If you’re unfamiliar with this model, you may want to first read about how encryption protects your secured RAR file ↗️ and why RAR passwords cannot be reset like email credentials.
Key ideas:
- Strong encryption: RAR uses modern ciphers designed so that, without the password, the contents should be practically inaccessible.
- Key derivation: The password is processed through multiple rounds of computation so each trial is intentionally expensive, making large-scale guessing harder.
- Encrypted headers: If enabled, even the list of filenames is protected, so you can’t see what’s inside without the correct password.
If you want a deeper conceptual overview of how RAR4 and RAR5 use encryption, how RAR4 and RAR5 secure your protected data ↗️ is a useful companion topic to this article. Dummy archives then become a safe way to see these concepts “in motion” on your own system.
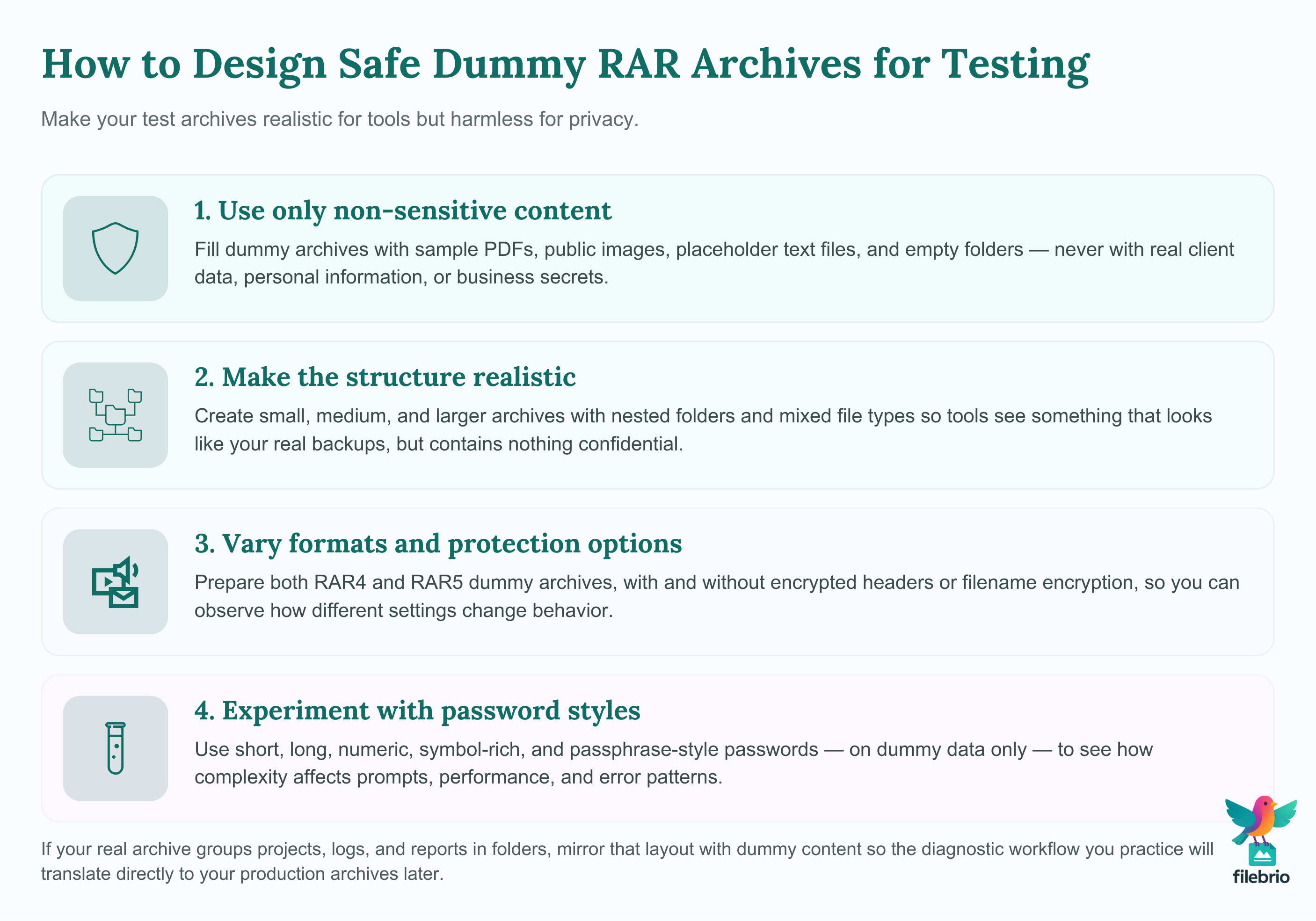
🧪 Designing Safe Dummy Archives for Testing
A well-designed dummy archive feels realistic to your tools, but contains absolutely nothing sensitive. Think of it as a stand-in actor: same stage, same lights, no real risk.
Practical design principles:
- Use only non-sensitive content. Sample PDFs, public images, lorem-ipsum documents, and empty folders are ideal.
- Vary sizes and structures. Create small, medium, and larger archives. Include nested folders, mixed file types, and a variety of names.
- Mix formats. Prepare some RAR4 and some RAR5 archives so you can observe differences in behavior and options.
- Experiment with encryption options. Enable and disable header encryption and filename encryption in different samples.
- Use different password styles. Short, long, purely numeric, mixed case, symbols, and passphrases — all on dummy data only.
You can also design dummy archives that imitate the structure of your real backups. If your production archive contains project folders, logs, and reports, your dummy version might mimic the folder layout with placeholder content. That way, any diagnostic or recovery workflow you practice on the dummy archive will translate more easily to the real one later.
For more nuanced testing that involves file internals, it can be helpful to see how file types influence diagnostics for your RAR archive ↗️, then mirror some of those formats inside your dummy sets.
🧰 All-In-One Toolkit for Safe RAR Testing
Once you have a set of dummy archives, you’ll want a reliable way to analyze them offline: checking formats, header options, error messages, and estimated difficulty — without touching untrusted online tools.
FileBrio RAR Master, as part of the FileBrio Office Suite, is designed for exactly this kind of controlled, privacy-first evaluation. Instead of scattering your tests across multiple utilities, you can centralize your work in one environment and build a repeatable process.
| Goal | How Dummy Archives Help | How FileBrio RAR Master Fits |
|---|---|---|
| Understand RAR protection behavior | Create multiple test archives with different passwords and options. | Use the app capabilities overview in the FileBrio RAR Master features ↗️ page to see which diagnostics and modes apply. |
| Check format and header settings | Compare RAR4 vs RAR5, with and without encrypted headers. | Inspect technical details locally and build a checklist you can later apply to real archives. |
| Estimate feasibility at a high level | Use dummy passwords of known complexity and observe behavior. | Combine results with local estimates and offline analysis, without exposing any private files. |
Because you are working only with safe test data, you are free to explore different settings and see how the toolkit reacts. When you feel comfortable with the workflow, you can download the full suite from the official FileBrio Office Suite download page ↗️ and apply the same carefully tested process to your own archives when appropriate.
________________________
FileBrio RAR Master — part of the FileBrio Office Suite — is a privacy-first, offline Windows toolkit for diagnosing and safely regaining access to your own password-protected RAR / WinRAR archives.
- Local processing only — nothing leaves your PC.
- Smart diagnostics to separate password issues from corruption.
- Owner-verified recovery workflows designed strictly for legitimate use.
Reminder: FileBrio RAR Master may be used only with archives you own or are explicitly authorized to access. It performs all analysis and recovery operations locally on your device, without uploading data anywhere.
________________________
🧷 What You Can Safely Learn From Dummy Archives
Dummy archives cannot magically tell you your real password, but they can reveal a lot about how protection behaves on your system and what to expect when you later work with actual data you own.
Examples of safe insights:
- Error messages and wording. You’ll see typical prompts, warnings, or failure messages for wrong passwords, truncated files, and unsupported formats.
- Impact of different password patterns. By using known test passwords, you can observe which kinds feel slow to process or tricky to type correctly.
- Effect of header encryption. You’ll notice how list views change when filenames and metadata are encrypted versus visible.
- Tool behavior under stress. Larger dummy archives can show whether a tool remains stable and responsive under load.
If you later need to diagnose a real locked archive that you own, you will already be familiar with safe diagnostic patterns such as how to safely diagnose your locked RAR file ↗️, rather than experimenting live on your only copy.
⚖️ Knowing the Limits: What Dummy Tests Can’t Tell You
Dummy archives are powerful learning tools, but they also have clear limitations that you should respect.
First, a dummy archive cannot tell you whether a specific real password will be discoverable or how long it would take in practice. It can only show relative trends, such as “this category of passwords is significantly slower to process” or “this format adds overhead.”
Second, dummy tests cannot override mathematical and cryptographic limits. If your real archive uses very strong encryption combined with a long, random password, then no amount of testing on dummy data will change the fact that exhaustive guessing may be infeasible. For a high-level discussion of these constraints, see how to understand limits on guessing your RAR password ↗️, especially the emphasis on legality and realistic expectations.
Finally, dummy testing is not a substitute for backups, versioning, or sound storage practices. It helps you behave more safely around encrypted archives, but it cannot protect you from hardware failures or accidental deletions. For that, you still need robust backup strategies and careful handling of your actual data.
📊 Interpreting Results: Strength, Entropy, and Time Estimates
Once you start experimenting with dummy archives, you’ll naturally want to interpret what your observations actually mean.
Common questions include:
- “If this dummy password feels slow to process, does that mean my real archive is safe?”
- “How do I translate password length and complexity into realistic expectations?”
- “Can I turn my dummy test results into useful estimates?”
The key is to think in terms of entropy and search space rather than any single speed number. Dummy archives help you understand patterns, but the actual difficulty of accessing a protected archive still depends heavily on its password design and encryption settings.
To support these evaluations, FileBrio includes a high-level estimation tool — you can learn more on the RAR password strength estimator ↗️ page. Combine those conceptual estimates with what you observe when operating on dummy archives and you will have a much clearer picture of what is realistically feasible and what isn’t.
🛡️ Secure Offline Evaluation With FileBrio RAR Master
One of the biggest advantages of dummy archives is that they naturally encourage an offline-first mindset. If you’ve already practiced a fully local workflow on test data, there’s no reason to suddenly upload your real confidential archive to an unknown website later.
FileBrio RAR Master builds on this idea by giving you a structured, offline environment for both testing and later real-world diagnostics. Instead of mixing untrusted tools and ad-hoc scripts, you centralize your work in a single, auditable application.
- Privacy-first: All operations are local. Combined with the rationale in why offline tools keep your encrypted RAR data private ↗️, this helps you avoid exposing archives to external servers.
- Controlled diagnostics: You can focus on safe actions first, as described in what to try before guessing your RAR password ↗️, and apply them to dummy archives until you have a stable procedure.
- Clear technical limits: When you later analyze real archives, you can pair your dummy-based experience with the guidance in limits of RAR decryption ↗️ so you know when recovery is realistically impossible.
Working this way means you are never improvising under pressure. The process you use on a high-value encrypted backup is the same one you practiced repeatedly on dummy archives. When you’re ready to formalize this workflow across your tools, you can again obtain the suite from the official FileBrio Office Suite download section ↗️ and standardize it across your devices.
________________________
FileBrio RAR Master — a secure, offline Windows toolkit for regaining access to your own password-protected RAR / WinRAR archives while keeping all data strictly on your device.
- Offline-only processing — never uploads your archives.
- Smart issue detection — password vs corruption.
- Fast recovery workflow optimized for legitimate ownership.
⬇️ Download FileBrio RAR Master
Reminder: FileBrio RAR Master is intended only for archives you own or are explicitly authorized to access. All operations run locally on your PC.
________________________
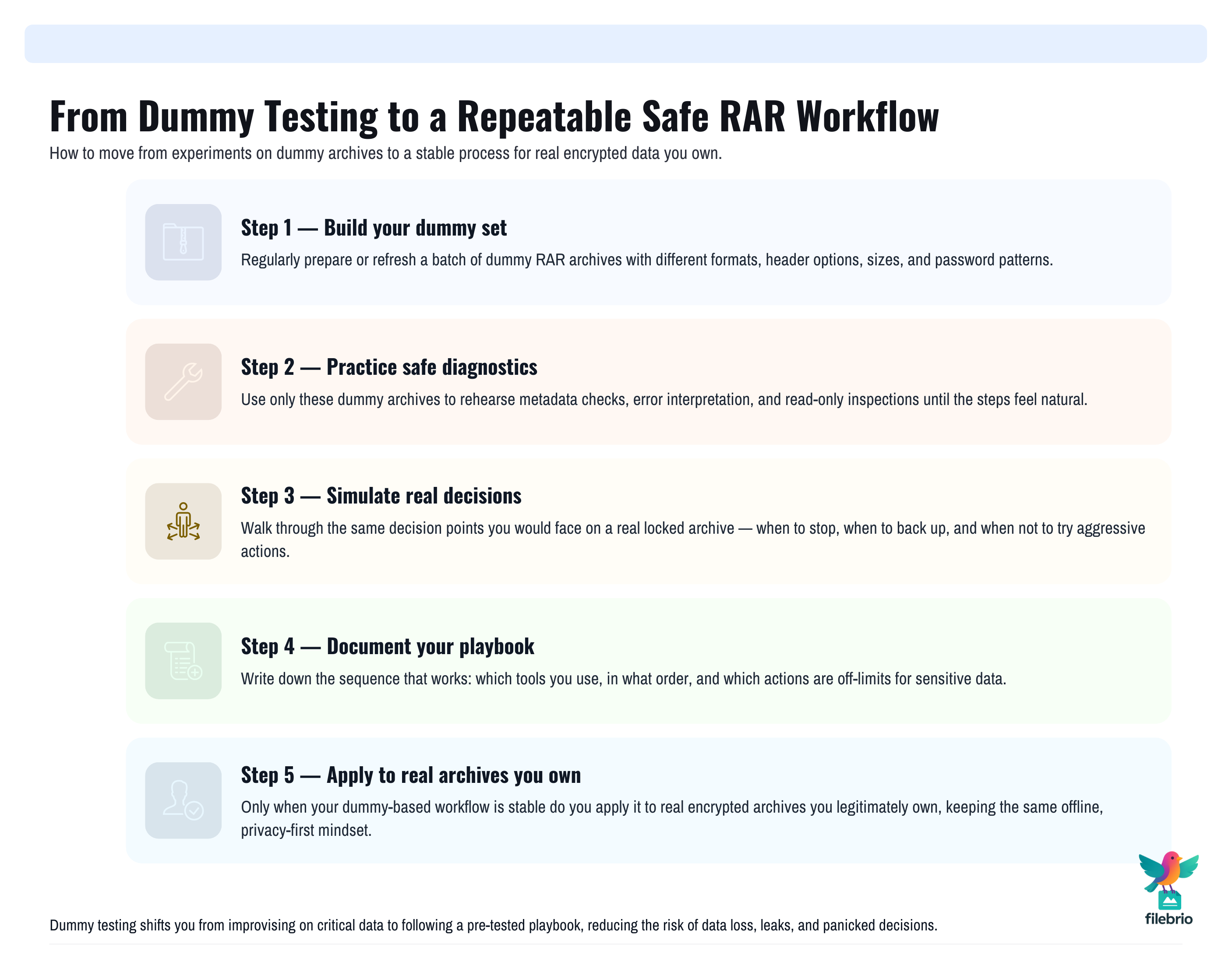
🛠️ Building a Repeatable Safe-Testing Workflow
Dummy archives are most effective when they’re part of a documented, repeatable workflow rather than random one-off experiments. Think in terms of a small “playbook” you can follow each time.
A simple pattern might look like this:
- Prepare or refresh your dummy set. Include RAR4, RAR5, different header options, and a variety of password patterns.
- Run safe diagnostics. Check basic metadata, formats, and error messages to rehearse how to safely diagnose your locked RAR file ↗️ without risking data loss.
- Simulate decision points. Practice the choices you would make before considering any intensive operations, guided by the type of advice in what to review before guessing your RAR password ↗️.
- Record observations. Note which configurations are clearly strong, which are borderline, and which are obviously weak.
- Apply the playbook to real archives you own. Only after you’re comfortable with each step on dummy data do you repeat it on production files.
This repeatability is especially valuable in teams, where you may want colleagues to follow the same safe process. It aligns naturally with broader guidance on how to design a secure workflow for your encrypted files ↗️, ensuring that everyone evaluates protection consistently and responsibly.
🧯 How Dummy Testing Protects You From Common Mistakes
Many data-loss incidents around RAR archives come down to two patterns: rushing under pressure and experimenting directly on the only copy of a critical file. Dummy testing is an antidote to both.
By practicing on non-sensitive archives, you’re far less likely to:
- Delete or overwrite the only copy of a protected archive by accident.
- Run destructive operations on damaged media before you have backups.
- Upload confidential data to untrusted websites “just to see what happens.”
- Misinterpret error messages and take risky steps as a result.
If you recognize any of these behaviors from your own experience, it’s worth reviewing common pitfalls described in mistakes that endanger your protected RAR files ↗️. Then design dummy tests specifically targeted at those weak points so that the risky behavior happens only in a safe sandbox, never with real data.
Because the archives are disposable, you can afford to make mistakes there — and adjust your habits before they impact something you can’t replace.
📁 Long-Term Security: From Dummy Archives to Real-World Policy
Dummy archives are more than a one-time experiment; they can become a regular part of how you design and review your RAR security over time.
For example, you might decide that every time you change your password policies or backup strategy, you will also:
- Create a fresh batch of dummy archives reflecting the new standards.
- Test access, diagnostics, and workflows under the new rules.
- Document what worked well and what needs adjustment.
This practice can feed directly into broader guidance like how to reinforce protection of your encrypted RAR files ↗️, ensuring that any security improvement you make is grounded in hands-on, low-risk testing. It also helps you avoid the trap of making archives so secure that future you — or your team — cannot realistically access them.
For storage and media considerations, you can combine dummy testing with recommendations in ways to prevent losing your RAR data on storage devices ↗️, making sure your real encrypted archives are both well-protected and stored in a way that minimizes corruption and loss.
Over time, this blend of policy and practice gives you a mature, evidence-based approach to RAR security: you don’t guess how safe your configuration is — you test it, safely, using dummy archives designed for exactly that purpose.
⚠️ Legal Reminder
This article is provided for general informational and educational purposes only. Any examples, scenarios, or references to password recovery, archive security, or related tools (including FileBrio RAR Master or similar software) are intended solely to help you better understand how to protect and manage your own data.
You may only apply any techniques, workflows, or tools described here to files and archives that you fully own or are explicitly and verifiably authorized to access. Attempting to bypass, remove, or recover passwords for third-party data without clear permission may violate criminal law, civil law, or internal company policies in your jurisdiction.
Nothing in this article constitutes legal advice. Laws and regulations differ between countries and organizations, and you are solely responsible for ensuring that your actions comply with all applicable legislation, contracts, and internal policies. If you are unsure whether a particular action is lawful or permitted, consult a qualified legal professional before proceeding.
📚 See Also: Further Reading on Safe RAR Use
- How Password Length and Entropy Affect Guessing Complexity ↗️
- RAR Recovery Records and .rev Volumes: How They Help Protect and Restore Data ↗️
- How to Understand Password Guessing Time Estimates (High-Level RAR Examples) ↗️
- How to Strengthen RAR Archive Security While Preserving Future Access ↗️
- Best Practices for Managing Large RAR Archives Safely ↗️
- Restoring Access to RAR/WinRAR Archives: Safe and Legal Methods for Handling Your Own Files ↗️