
How to Ensure You’re Recovering Only RAR Files You Own
When you’re locked out of a RAR archive, stress rises quickly — especially if it contains work documents, personal memories, client materials, or sensitive internal data. In that moment, it’s tempting to jump straight into “recovery mode.” But before anything else, there’s a more important step: confirming beyond doubt that the archive is really yours to access.
Whether you’re an individual trying to retrieve your own encrypted files, or part of a business managing shared protected archives, verifying ownership is not just polite — it’s legally necessary and often organizationally required. This article walks you through responsible ways to confirm legitimacy, avoid ethical risk, and build a secure, documented chain of custody for any encrypted RAR file you attempt to open.
🧭 Navigation
Important
The information provided in this article applies exclusively to RAR / WinRAR archives for which you have full, demonstrable ownership or properly documented authorization. If you are not the rightful owner of the data, do not directly control it, or cannot clearly prove permission to access it, you must stop immediately. Attempting to access, recover, or modify data without explicit authorization may violate criminal law, civil statutes, corporate compliance requirements, and privacy regulations in many jurisdictions. You alone are responsible for ensuring that your actions are lawful and properly permitted before proceeding.
📌 TL;DR — Quick Summary
When accessing an encrypted RAR archive, proving ownership is a non-negotiable first step. Whether you created the archive yourself or are handling materials for your workplace, confirming legitimacy helps avoid legal risks, privacy violations, and accidental access to someone else’s confidential data.
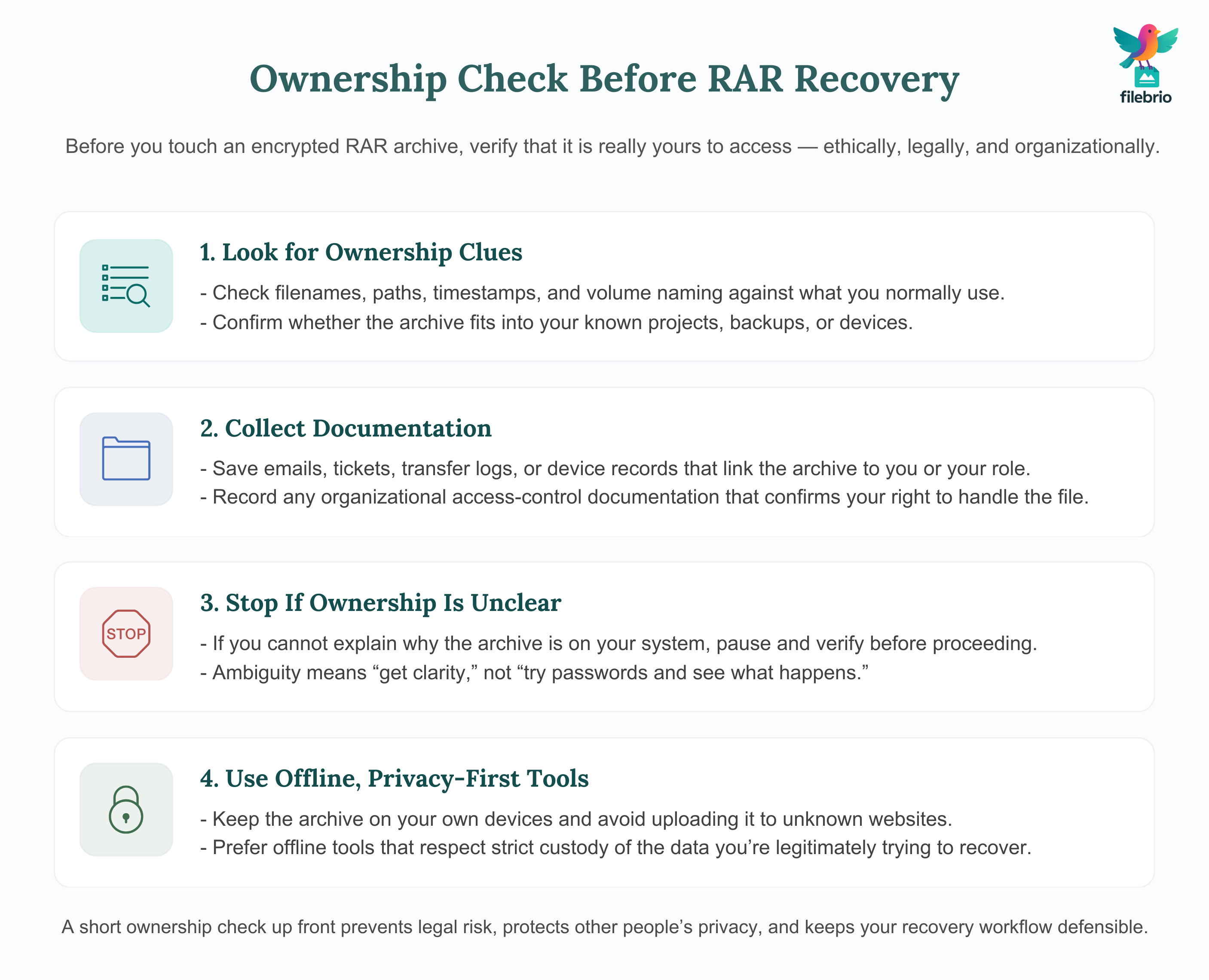
Key principles:
- Ownership checks: Look for clues such as familiar filenames, metadata, file paths, volume naming conventions, or accompanying documents.
- Document your rights: Save emails, tickets, transfer logs, device records, ownership statements, or organizational access-control documentation.
- Stay within ethical lines: Never attempt to open archives you don’t clearly own. Ambiguity means “stop and verify,” not “proceed.”
- Use privacy-first tools: Work offline, avoid uploading sensitive archives to unknown websites, and maintain strict custody of the data.
Remember: You are responsible for ensuring your recovery attempts involve only your own archives. A well-documented, safety-first approach keeps your workflow compliant and protects everyone’s privacy.
⚠️ Why Ownership Verification Matters
Encrypted RAR files are designed to protect sensitive information. The encryption is strong enough that there is no “reset” feature, and attempts to access the archive without authorization may violate laws or internal security policies. That’s why it’s essential to confirm that the archive belongs to you—or that you have appropriate authorization—before attempting any technical recovery.
For example, it’s common for users to inherit folders from older machines, shared network drives, or cloud backups that contain unknown archives. Before acting, the responsible step is to establish whether you have a legitimate right to interact with those files.
If the archive originally belonged to you (e.g., created on your device, stored in your backup structure), ownership is straightforward. But in more complex environments—shared RAR backups, client deliverables, team archives, cross-department folders—you should pause and confirm legitimacy.
Good organizational practice often starts with methods similar to acceptable proof for your encrypted RAR file in business ↗️, where you collect documentation and verify permissions before taking any action.
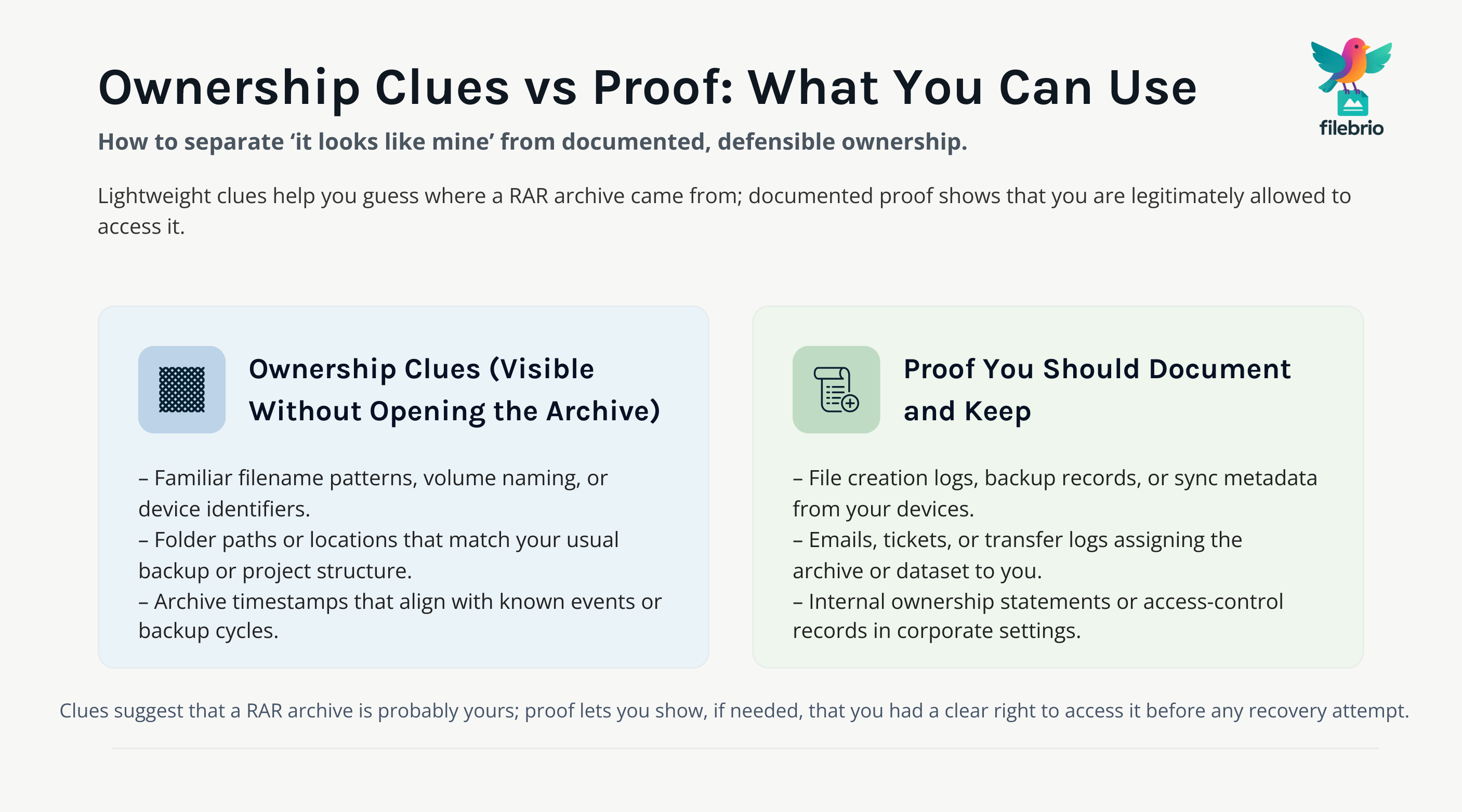
🧩 Identifying Ownership Clues Inside the RAR Structure
Even when you cannot open the archive yet, metadata and non-content clues can reveal important ownership indicators. These checks do not access file contents; they only inspect what is already visible in header fields, naming patterns, and file organization.
Safe, high-level techniques from safe checks for understanding your RAR archive structure ↗️ and how metadata reveals issues in your protected contents ↗️ help you understand:
- File naming conventions — Many users follow consistent patterns for backups, project names, or device identifiers.
- Folder paths in metadata (when unencrypted) — Non-sensitive structural clues can often show where the archive was created.
- Archive timestamps — These may match events, device replacements, or known backup cycles.
- Volume names — Multi-volume sets typically follow user-specific naming patterns.
These clues do not guarantee ownership, but they often reinforce your understanding of the archive’s origin.
📝 Documenting Proof of Ownership
Whether you are an individual working with personal data or an employee handling organizational archives, documentary proof is the clearest—and safest—way to demonstrate ownership.
You can adapt guidelines similar to those in how to document control of your sensitive encrypted files ↗️ to build a safe, auditable trail:
- File creation logs from devices or backup systems.
- Internal tickets confirming your role and authorization.
- Email threads showing that the data was assigned or delivered to you.
- Directory histories showing long-term presence in your user profile or workspace.
- Versioning or sync metadata documenting transfers or device upgrades.
- Signed statements in corporate environments confirming your right to access a dataset.
When ownership is reaffirmed with documentation, recovery becomes not only safe but fully compliant with internal and external requirements.
🧰 All-In-One Solution for Safe RAR Recovery
Ownership verification is only one part of the process; once legitimacy is established, you still need a safe, controlled way to analyze and recover your files. Using separate, untrusted tools can lead to privacy exposure, corrupted archives, or accidental mishandling—especially when the file contains sensitive information.
FileBrio RAR Master provides an all-in-one RAR recovery toolkit ↗️ built for legitimate use cases, making it easier to maintain custody and auditability at every step.
| Challenge | How FileBrio RAR Master Helps |
|---|---|
| Need to inspect metadata before recovery | Offers precise diagnostics without extracting content. |
| Unclear whether you have the right to access the archive | Shows non-sensitive structural clues that may confirm origin. |
| Privacy and confidentiality requirements | All operations happen offline—no uploads, no exposure. |
| Multiple archives across teams or machines | Keeps everything organized in one interface, reducing errors. |
Before beginning recovery work, you can install the suite via the official FileBrio download page ↗️, ensuring you have a trusted and controlled environment.
________________________
FileBrio RAR Master — part of the FileBrio Office Suite — is a privacy-first, offline Windows toolkit for diagnosing and safely regaining access to your own password-protected RAR / WinRAR archives.
- Local processing only — nothing leaves your PC.
- Smart diagnostics to separate password issues from corruption.
- Owner-verified recovery workflows designed strictly for legitimate use.
Reminder: FileBrio RAR Master may be used only with archives you own or are explicitly authorized to access. It performs all analysis and recovery operations locally on your device, without uploading data anywhere.
________________________
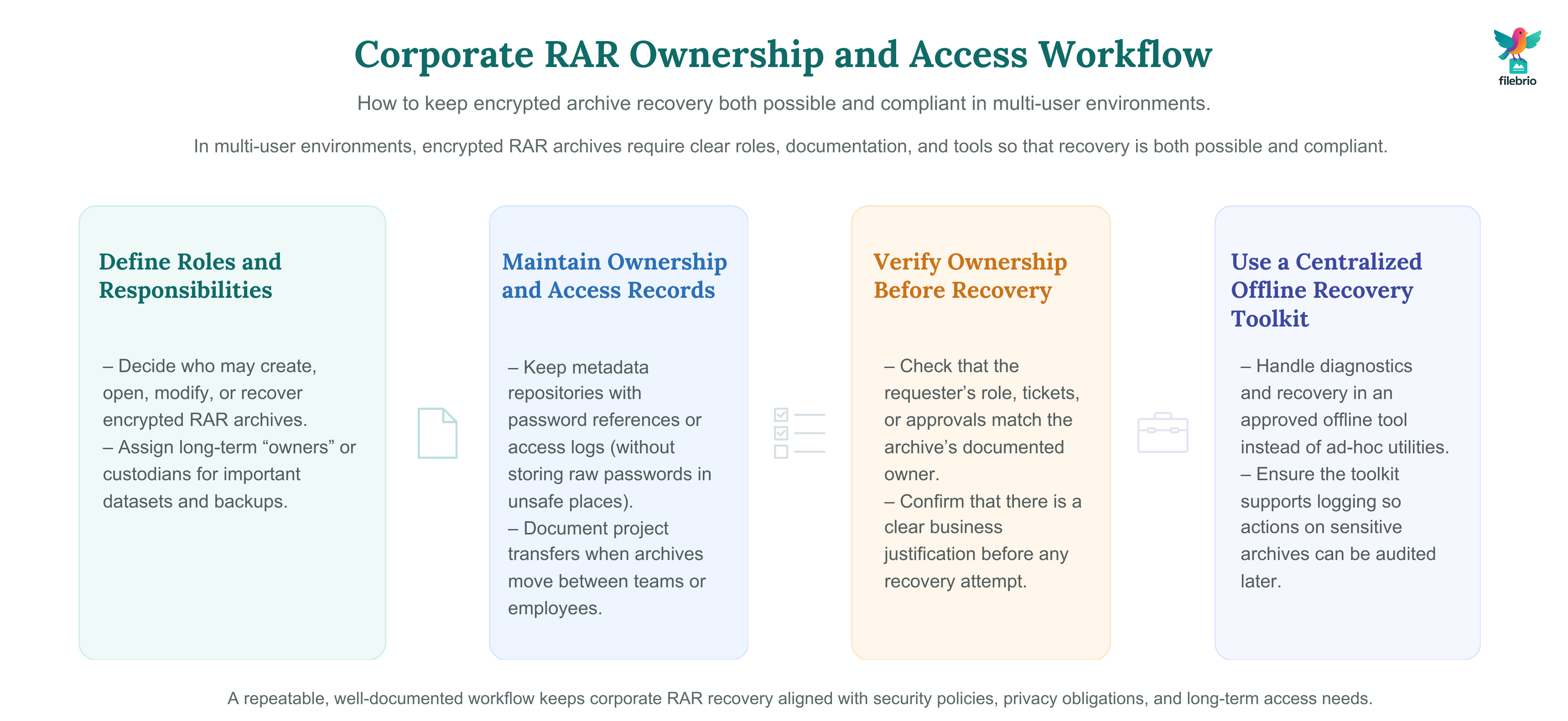
🏢 Ownership in Corporate & Multi-User Environments
In a business setting, verifying ownership is even more important because encrypted archives often contain confidential or regulated data. Departments may share RAR files for years, and without proper documentation, it becomes unclear who is responsible or authorized to access them.
Using principles from ways to safeguard your protected corporate RAR files ↗️ and how teams preserve long-term access to encrypted RAR files ↗️, organizations can establish workflows that preserve both access and compliance:
- Define clear roles for who may open, modify, or handle encrypted archives.
- Maintain metadata repositories that store password references or access logs (without storing actual passwords in unsafe locations).
- Document transfers when projects move between employees or teams.
- Use secure, centralized recovery tools that maintain audit trails.
These practices prevent confusion years later, when the need to open an old RAR archive resurfaces and no one remembers who originally created or secured it.
🛑 How to Avoid Accessing Files That Aren’t Yours
Ambiguity is a warning flag. If you cannot trace where a RAR file came from, who created it, or why it is present on your device, the responsible action is to pause—not proceed.
Here are indicators that mean you should stop and verify:
- The archive appears in an unexpected directory.
- The naming style does not match anything you recognize.
- The timestamp suggests it predates your use of the device.
- The archive resides in a shared or inherited folder.
At this point, you can use ethical ways to handle your encrypted RAR files ↗️ to guide your next steps. Accessing someone else’s encrypted files without authorization—even unintentionally—can create serious legal and privacy issues.
🧯 Technical Safety Tips Before Recovery Attempts
Once ownership is established, technical safety becomes your next priority. A responsible workflow protects your data from additional damage or accidental disclosure.
Before any attempt at access, ensure that you:
- Work only on copies of the archive.
- Isolate the files in a clean workspace.
- Check integrity using non-destructive inspection methods.
- Confirm whether the archive is encrypted or corrupted using simple checks revealing why your RAR file won’t open ↗️.
- Review storage safety guidance such as ways to prevent losing your RAR data on storage devices ↗️.
Safe preparation ensures that even if recovery is not possible, you leave the archive in the best possible condition for future analysis.
🔐 Secure Offline Recovery with FileBrio RAR Master
Once ownership is verified, and once you’re ready to begin legitimate recovery, it’s critical to choose tools that respect your privacy. Uploading encrypted archives to random online services introduces legal, ethical, and practical risks.
It may be helpful to compare offline vs online RAR recovery ↗️ to understand why local tools give you full control. FileBrio RAR Master offers:
- Fully offline operations—nothing leaves your device.
- Integration with responsible use and legal guidelines ↗️ to ensure compliant handling.
- Structured diagnostics that make ownership evaluation easier.
- Access to a high-level password time estimation tool ↗️ to help determine feasibility.
These capabilities make the recovery process safer, more transparent, and fully aligned with best practices for sensitive encrypted data.
________________________
FileBrio RAR Master — a secure, offline Windows toolkit for regaining access to your own password-protected RAR / WinRAR archives while keeping all data strictly on your device.
- Offline-only processing — never uploads your archives.
- Smart issue detection — password vs corruption.
- Fast recovery workflow optimized for legitimate ownership.
⬇️ Download FileBrio RAR Master
Reminder: FileBrio RAR Master is intended only for archives you own or are explicitly authorized to access. All operations run locally on your PC.
________________________
⚖️ Legal Reminder
This article is provided for general informational and educational purposes only. Any examples, scenarios, or references to password recovery, archive security, or related tools (including FileBrio RAR Master or similar software) are intended solely to help you better understand how to protect and manage your own data.
You may only apply any techniques, workflows, or tools described here to files and archives that you fully own or are explicitly and verifiably authorized to access. Attempting to bypass, remove, or recover passwords for third-party data without clear permission may violate criminal law, civil law, or internal company policies in your jurisdiction.
Nothing in this article constitutes legal advice. Laws and regulations differ between countries and organizations, and you are solely responsible for ensuring that your actions comply with all applicable legislation, contracts, and internal policies. If you are unsure whether a particular action is lawful or permitted, consult a qualified legal professional before proceeding.
✅ Summary and Next Steps
Responsible RAR recovery begins long before the first password attempt or diagnostic command. It starts with verifying that the archive is unquestionably yours—or that you have documented authorization to access it. From there, safe evaluation methods, privacy-first tools, well-structured organizational workflows, and careful handling ensure that recovery happens ethically and securely.
If ownership isn’t clear, stop and confirm before proceeding. If it is, work offline, protect your original file, gather metadata clues, and use trusted tools designed for legitimate recovery. By following these principles, you prevent legal and privacy issues, protect your data, and build a recovery workflow that’s both secure and responsible.
📚 See Also
- How to Document Ownership of Sensitive Encrypted Archives ↗️
- Lost Your RAR/WinRAR Password? How to Assess Your Situation Before Taking Action ↗️
- Unlocking Password-Protected RAR/WinRAR Archives: Safe Methods for Legitimate Access ↗️
- Bypass RAR Password: What Users Really Mean and How to Access Your Own Archives Safely ↗️
- Is It Legal to Break a RAR/WinRAR Password? Understanding the Term and Safe Access Options for Your Files ↗️