
How to Determine If a RAR Archive Uses Header Encryption (and Why It Changes What You Can See)
You open a RAR archive and see… nothing. No filenames, no folder structure — just a password prompt and a vague sense that something is “different” from your usual protected files. In many cases, this isn’t corruption at all, but header encryption doing exactly what it was designed to do: hide metadata and contents until the correct password is provided.
If you work with sensitive data, knowing whether an archive uses header encryption is critical. It defines what you (and anyone else) can see without the password, what diagnostics are possible, and how much information leaks to third parties if the file is shared or stolen. This article walks you through how to recognize header encryption in a safe, high-level way — and how to evaluate its implications for visibility and troubleshooting.
Everything here is about your own archives or files you are explicitly authorized to handle. The goal is to help you understand RAR protection, avoid misdiagnosing issues, and build safer workflows — not to access data you do not own.
🧭 Navigation
Important
The information provided in this article applies exclusively to RAR / WinRAR archives for which you have full, demonstrable ownership or properly documented authorization. If you are not the rightful owner of the data, do not directly control it, or cannot clearly prove permission to access it, you must stop immediately. Attempting to access, recover, or modify data without explicit authorization may violate criminal law, civil statutes, corporate compliance requirements, and privacy regulations in many jurisdictions. You alone are responsible for ensuring that your actions are lawful and properly permitted before proceeding.
✨ TL;DR — What Header Encryption Changes
Header encryption in RAR archives protects not just the file contents, but also the metadata that normally appears before decryption: filenames, folder structure, and some structural details. When header encryption is enabled, a tool that opens the archive cannot list contents or show meaningful clues without the correct password.
From a user’s perspective, this means a header-encrypted RAR file may look “empty” or reveal only very limited information, even though the data is still there. That is not a bug — it’s a privacy feature designed to prevent information leakage to anyone who doesn’t have the key.
In practice, you can often tell that header encryption is enabled when:
- The archive prompts for a password before showing any filenames.
- Content lists remain hidden or completely blank without successful decryption.
- Diagnostic tools report encryption on headers or show limited metadata.
Learning to recognize header encryption helps you avoid misdiagnosing a healthy, strongly protected archive as “corrupted” and sets realistic expectations about what diagnostics are possible without the password. Always apply this knowledge only to archives you own or are explicitly authorized to manage.
🔍 Why Header Encryption Matters for Privacy and Diagnostics
Every RAR archive has headers — structural blocks that describe what’s inside: filenames, timestamps, sometimes size information and other metadata. Without header encryption, these details may be visible even if the actual file contents remain protected. That visibility can be convenient for diagnostics, but it also leaks information.
Header encryption changes this balance. When it is enabled, the encryption engine protects not only the data, but also the descriptive layer that would otherwise reveal context about your archive. That’s why, in strongly protected backups, you might see no filenames at all until the password is accepted.
If you are new to RAR security, it can help to first understand how encryption controls access to your protected RAR contents ↗️. Header encryption is essentially a stronger stance on the same idea: if someone shouldn’t see your documents, they also shouldn’t know what those documents are called or how they’re organized.
From a diagnostics point of view, however, this has consequences. With non-encrypted headers, you can often detect which files might be damaged or which parts of the archive are accessible. With encrypted headers, visibility is deliberately reduced, so you need to rely more on high-level metadata and careful, offline analysis instead of expecting a detailed file list.
👁️ Practical Effects: How Header-Encrypted RAR Files Look in Real Life
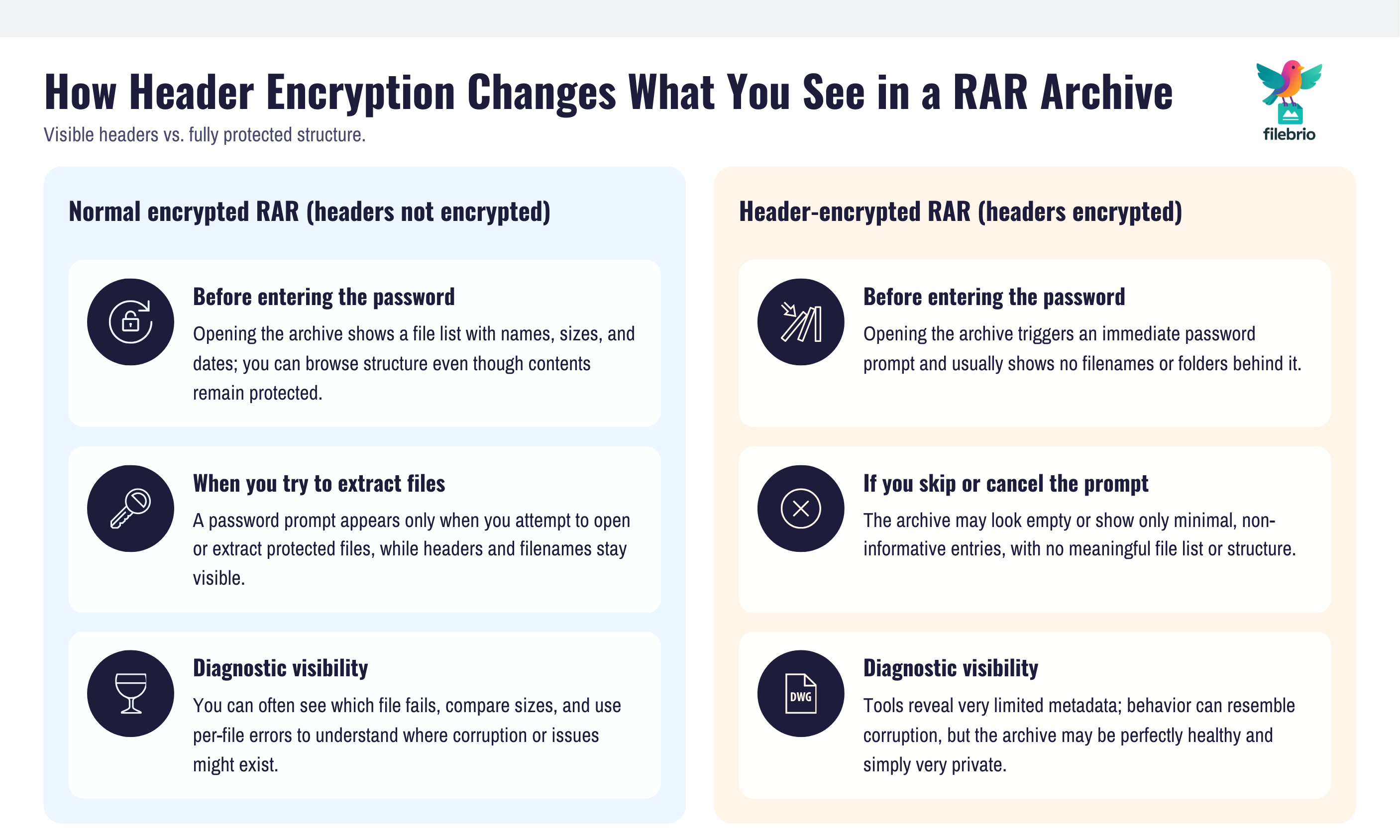
So what does a header-encrypted RAR archive look like in practice, compared to one that only encrypts contents?
In a typical, non-header-encrypted archive, you might:
- Open the archive in a tool and immediately see a list of filenames.
- Get prompted for a password only when you try to extract certain files.
- Be able to view metadata (sizes, dates) without seeing the contents themselves.
In a header-encrypted archive, you’re more likely to experience:
- A password prompt as soon as you try to open the archive.
- No filenames or folder structure displayed until the correct password is entered.
- Limited or no visible metadata about the internal files.
This is closely related to how how encrypted headers hide your protected RAR contents ↗️. The archive is effectively telling you: “I exist and I’m protected, but you don’t get to see any internal structure unless you’re authorized.” It’s important not to confuse this behavior with corruption; a header-encrypted archive may be perfectly healthy, just very private.
In addition, header encryption often goes hand-in-hand with filename protection. When filenames themselves are encrypted, the combination provides strong privacy for both the data and its descriptive labels. For a more focused discussion of this aspect, see how filename encryption hides your protected RAR contents ↗️.
🧪 Safe Manual Checks for Header Encryption
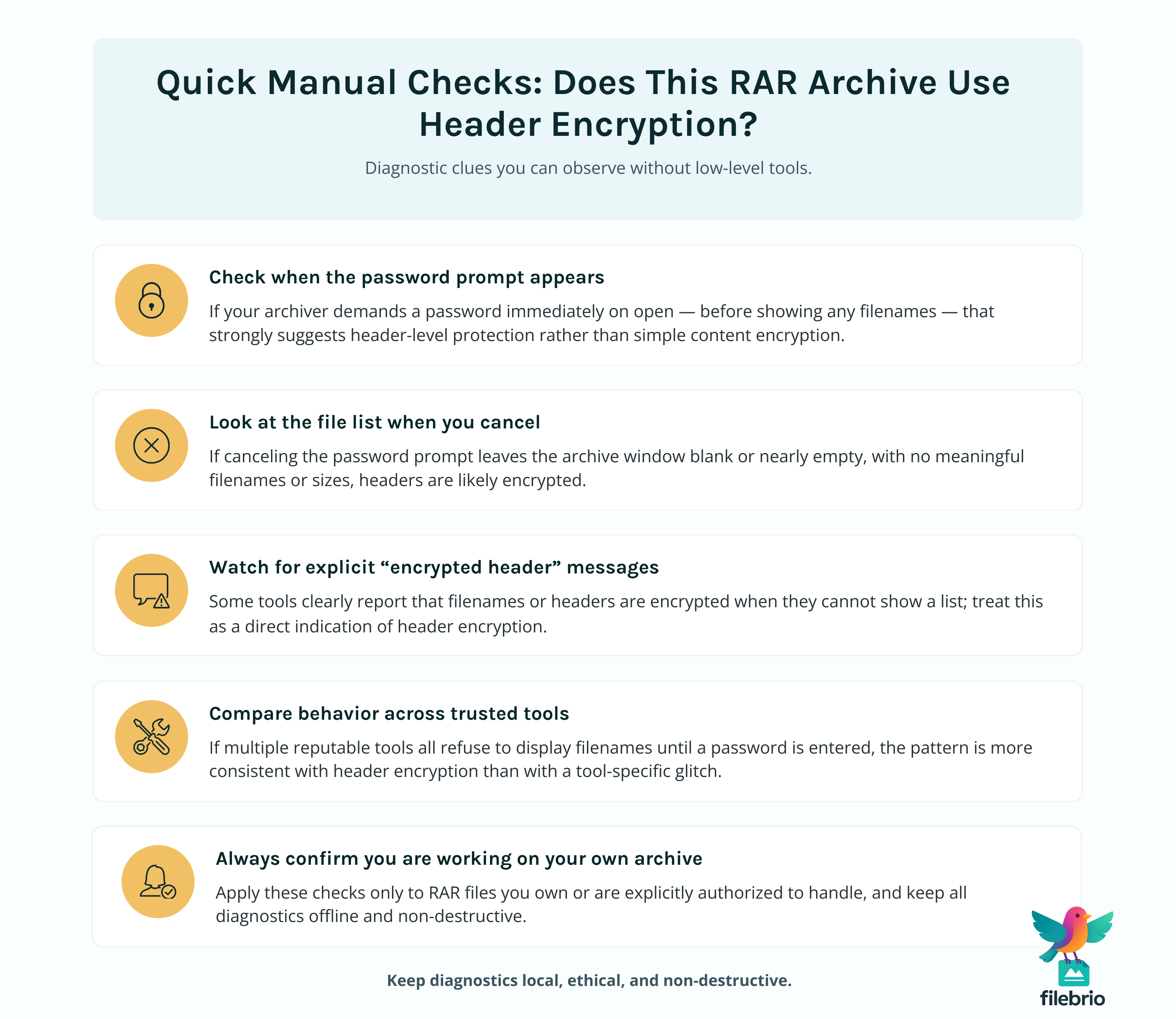
You can often make a basic, high-level judgment about header encryption using careful manual checks — again, only on archives you own or are clearly authorized to handle.
Typical safe indicators include:
- Content listing behavior: If your tool shows a blank file list until a password is accepted, that strongly suggests header-level protection.
- Error messages: Some interfaces explicitly mention that headers or filenames are encrypted when you attempt to open the archive without a password.
- Prompt timing: If the password prompt appears immediately when opening the archive, rather than only at extraction, you’re likely dealing with stronger header protection.
For users who want a more structured approach, steps to confirm header encryption in your locked RAR file ↗️ gives a dedicated framework for interpreting these clues without resorting to risky tools or guessing behavior. The emphasis is always the same: keep everything offline, work only with data you own, and focus on diagnostics rather than aggressive access attempts.
🧰 All-In-One Solution for Safe Header Checks
As your archives and policies become more complex, manually checking each file for header encryption can be time-consuming. You may also want consistent behavior across multiple devices and team members.
This is where a dedicated, privacy-focused toolkit such as FileBrio RAR Master becomes useful. Instead of jumping between various utilities with inconsistent interfaces, you use a single all-in-one RAR recovery toolkit ↗️ that understands RAR4 and RAR5, recognizes header-level protection, and keeps every step local on your own system.
In practice, a structured approach might look like this:
- Use FileBrio RAR Master as the standard environment for viewing archive metadata and encryption modes.
- Record whether headers are encrypted as part of your normal archive-handling documentation.
- Use consistent, offline diagnostics to decide whether further work is justified, before you touch real data.
Because this work involves potentially sensitive archives, you should always obtain tools from the official source. When you’re ready to standardize your workflow, you can get the latest suite from the official FileBrio Office Suite download page ↗️ and deploy the same configuration wherever you need it.
________________________
FileBrio RAR Master — part of the FileBrio Office Suite — is a privacy-first, offline Windows toolkit for diagnosing and safely regaining access to your own password-protected RAR / WinRAR archives.
- Local processing only — nothing leaves your PC.
- Smart diagnostics to separate password issues from corruption.
- Owner-verified recovery workflows designed strictly for legitimate use.
Reminder: FileBrio RAR Master may be used only with archives you own or are explicitly authorized to access. It performs all analysis and recovery operations locally on your device, without uploading data anywhere.
________________________
🧱 Using Dummy Archives to Practice Header Detection
Determining whether header encryption is in use becomes much easier once you have hands-on experience. The safest way to gain that experience is through dummy archives — test RAR files you create yourself with non-sensitive contents.
With dummy archives, you can:
- Create one version with header encryption enabled and another with it disabled.
- Compare how they look in your tools, including timing of password prompts and visibility of filenames.
- Experiment with filename encryption, different formats, and various password patterns without risk.
This mirrors the ideas in how to inspect internal layout of your RAR file safely ↗️, but with a focus on headers. Because the contents are intentionally harmless, you are free to repeat these tests as often as needed to build intuition — and you can share the same dummy archives with colleagues to train them on spotting header encryption quickly.
Once you know what a header-encrypted archive looks like in a safe lab environment, it becomes much easier to recognize the same patterns later when you encounter real, sensitive archives that you legitimately own.
📝 Reading Metadata and Flags for Encryption Hints
Beyond visual cues in the user interface, some tools can expose structured metadata and internal flags that signal whether header encryption is in use. You do not need to reverse engineer anything or run complex scripts — simply reading high-level metadata, when your tools provide it, can be enough.
If you’re interested in going deeper into what these structural details mean, how header flags reflect your RAR file’s health ↗️ is a valuable reference. It explains how internal indicators reflect integrity, structure, and sometimes the protection mode.
On top of flags, generic metadata is also informative. For example, how to read metadata clues in your RAR file ↗️ shows how timestamps, sizes, and archive comments can hint at whether a file is healthy or compromised. When headers are encrypted, some of this information may be hidden by design, and that absence is itself a clue: the archive may be deliberately revealing less detail to protect privacy.
The key is to treat these flags and fields as diagnostic hints, not as tools to circumvent protection. They tell you about format, health, and encryption style, but they do not and should not expose the protected contents themselves without a valid password.
🧮 Combining Header Checks With Broader RAR Diagnostics
Determining whether header encryption is enabled is only one part of understanding what’s going on with a difficult RAR archive. You also need to consider the broader health of the file and whether it is actually locked, damaged, or both.
A safe way to approach this is to integrate header checks into a wider diagnostic workflow like the one described in how to safely diagnose your locked RAR file ↗️. In a combined process, you might:
- Check whether the archive opens and shows filenames (no header encryption).
- Observe if it demands a password immediately with no visible contents (possible header encryption).
- Run high-level integrity checks to detect obvious corruption or truncation.
- Compare behavior across different tools to rule out interface quirks.
You can then interpret your findings alongside broader feasibility questions. While header encryption tightly controls what is visible, recovery feasibility still depends on password strength, archive health, and format details. The more you unify these diagnostics into a single, offline workflow, the less likely you are to misinterpret a healthy, strongly protected archive as “broken” — or to expose it to unnecessary risk by uploading it to untrusted services.
🛡️ Secure Offline Solution for Encrypted Headers
When you do confirm that an archive uses header encryption, your next question is usually: “What, if anything, can I actually do now?” The answer depends heavily on whether you’re operating in a safe, offline environment with good tooling.
Header-encrypted archives are particularly sensitive to privacy risks because all the useful information — filenames, structure, contents — is hidden behind the password. Uploading such archives to untrusted online tools is rarely a good idea. Guidance around why offline recovery is safer ↗️ is especially relevant here: keeping both your analysis and any later recovery attempts local gives you far more control over who can see the archive and how it’s handled.
Using a dedicated offline toolkit like FileBrio RAR Master helps you:
- Evaluate header encryption and archive health without sending data to external servers.
- Apply consistent, policy-driven steps to determine whether further work is justified.
- Document your findings for compliance or audit purposes, particularly in business contexts.
In effect, header encryption becomes one more signal in a carefully controlled, privacy-first diagnostic process — not a reason to panic or rush into risky online services.
________________________
FileBrio RAR Master — a secure, offline Windows toolkit for regaining access to your own password-protected RAR / WinRAR archives while keeping all data strictly on your device.
- Offline-only processing — never uploads your archives.
- Smart issue detection — password vs corruption.
- Fast recovery workflow optimized for legitimate ownership.
⬇️ Download FileBrio RAR Master
Reminder: FileBrio RAR Master is intended only for archives you own or are explicitly authorized to access. All operations run locally on your PC.
________________________
🚫 Understanding the Limits: When Encrypted Headers Block Recovery
It’s important to recognize that header encryption doesn’t just change visibility; it can also shape what’s realistically possible in terms of recovery and diagnostics.
In some scenarios, the combination of strong encryption, a high-entropy password, and fully encrypted headers means that, without the correct password, there is no meaningful way to view or interpret internal contents. High-level guidance such as when RAR recovery isn’t possible ↗️ emphasizes that there are hard mathematical limits beyond which no responsible tool can promise access.
Encrypted headers also reduce the amount of partial information that might otherwise help you understand what went wrong. For example, with visible headers, you might see that certain files are missing or that volume counts don’t match, giving you a path to repair. With encrypted headers, these clues can remain hidden, which is by design. In those cases, your options narrow to:
- Confirming ownership and rights to the archive.
- Ensuring the file is not corrupted or truncated at the container level.
- Accepting that, beyond certain complexity thresholds, safe recovery may not be feasible.
Recognizing these boundaries upfront protects you from unrealistic expectations and from relying on tools or services that promise more than is technically or legally possible.
🔁 Building a Repeatable Header-Check Workflow
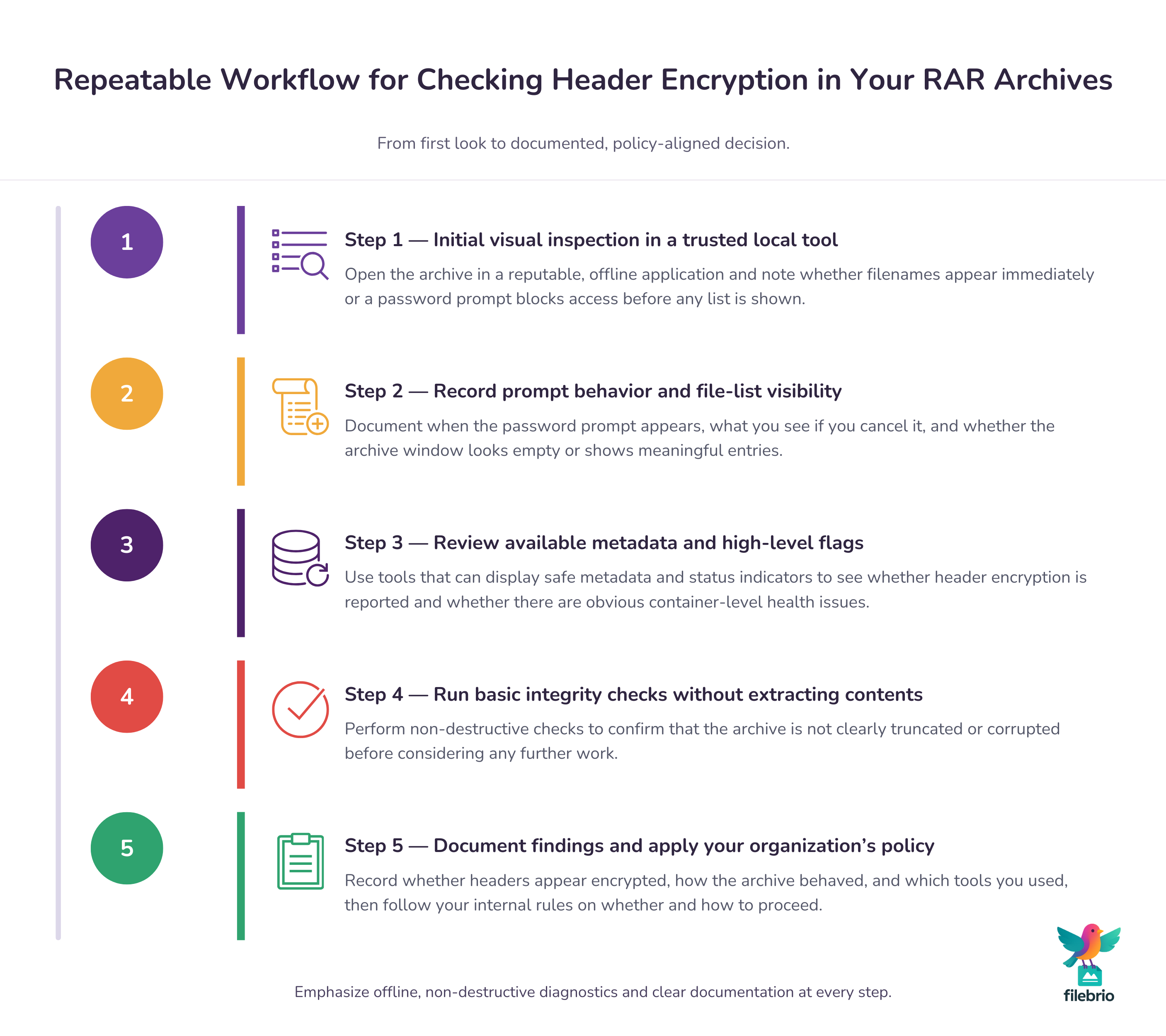
To get the most value from header encryption knowledge, turn it into a repeatable workflow that you can follow whenever you encounter a protected archive you own.
A practical, policy-friendly workflow might include:
- Initial inspection: Open the archive in a trusted local tool to observe whether filenames are visible or hidden behind a password prompt.
- Metadata and flag review: Capture any available high-level metadata and status flags that indicate encryption or health, building on practices from how header encryption shapes your RAR recovery chances ↗️.
- Health and integrity check: Verify that the container itself is not obviously corrupted or truncated before you consider further action.
- Documentation: Log whether headers are encrypted, which tools were used, and what behavior you observed, so you can make consistent decisions later.
- Policy alignment: Apply your organization’s rules about whether and how to proceed, based on encryption level, ownership, and sensitivity.
By repeatedly following the same steps, you reduce the risk of improvising under pressure, avoid exposing sensitive archives to unnecessary tools, and maintain clear records of how each header-encrypted archive was handled.
⚠️ Legal Reminder
This article is provided for general informational and educational purposes only. Any examples, scenarios, or references to password recovery, archive security, or related tools (including FileBrio RAR Master or similar software) are intended solely to help you better understand how to protect and manage your own data.
You may only apply any techniques, workflows, or tools described here to files and archives that you fully own or are explicitly and verifiably authorized to access. Attempting to bypass, remove, or recover passwords for third-party data without clear permission may violate criminal law, civil law, or internal company policies in your jurisdiction.
Nothing in this article constitutes legal advice. Laws and regulations differ between countries and organizations, and you are solely responsible for ensuring that your actions comply with all applicable legislation, contracts, and internal policies. If you are unsure whether a particular action is lawful or permitted, consult a qualified legal professional before proceeding.
📚 See Also: Further Reading on RAR Headers and Security
- Password Handling and Limitations Inside RAR SFX Installers ↗️
- How to Use Publicly Available Information Ethically in Security Planning ↗️
- Why Online “Password Breaking” Claims Are Risky and Misleading ↗️
- A Clear Look at What RAR Decryption Means and How to Work Safely ↗️
- Why Online Password Removal Is Unsafe and What Offline Options Exist ↗️