
Decrypting RAR/WinRAR Passwords Online: Privacy Risks and Better Local Alternatives
It starts innocently: you have a RAR or WinRAR archive you own, but you’ve forgotten the password or can’t tell whether the file is corrupted, mislabeled, or simply protected. A quick search leads you to dozens of websites claiming they can “decrypt your RAR password” instantly. But before uploading anything, you pause — is it actually safe? What happens when you send an encrypted archive containing private or sensitive data to an unknown server?
This article explains the real privacy risks behind online “RAR password decryption” services, why they rarely work in the first place, and how to choose safer, offline tools for evaluating and legitimately recovering access to your own RAR archives without exposing your files.
🧭 Navigation
Important
The information provided in this article applies exclusively to RAR / WinRAR archives for which you have full, demonstrable ownership or properly documented authorization. If you are not the rightful owner of the data, do not directly control it, or cannot clearly prove permission to access it, you must stop immediately. Attempting to access, recover, or modify data without explicit authorization may violate criminal law, civil statutes, corporate compliance requirements, and privacy regulations in many jurisdictions. You alone are responsible for ensuring that your actions are lawful and properly permitted before proceeding.
📌 TL;DR — Why Online RAR Password Tools Are Risky
Online “RAR password decryption” sites are risky because they require uploading your encrypted archive — including all its private data — to unknown third-party servers. You don’t know how long your file will be stored, who can access it, or how it might be reused. Many services also mislead users about their capabilities: they do not “decrypt” anything. Instead, they attempt a few guesses or rely on weak heuristics that only work on trivial passwords.
Meanwhile, real RAR encryption — especially in RAR5 archives — is designed to resist exactly these types of attempts through strong AES-256 encryption, slow key derivation, and optional encrypted headers. Online tools cannot bypass these security foundations. At best, they only succeed against weak, predictable passwords, and at worst, they expose your sensitive files to unknown parties.
Safer alternatives exist: offline, privacy-first software that keeps your archives on your machine, allows structured diagnostics, and lets you responsibly evaluate recovery feasibility without sending data to the cloud. If your archive contains anything personal, confidential, or irreplaceable, never upload it to online “decryption” services — use offline tools instead.
🌐 How Online “Decryption” Tools Actually Work
Sites that advertise “RAR password decryption” give the impression that they can reverse the encryption process or somehow “extract” the password by analyzing uploaded data. In reality, this is not possible. Properly encrypted RAR files — especially RAR5 — use strong cryptography designed to prevent decryption without the exact password.
Online tools typically fall into one of three categories:
- Pattern-based guessers that try short, common passwords and stop after a tiny number of attempts.
- Heuristic validators that check for trivial encryption, incomplete archives, or non-password issues.
- Mislabeled “services” that simply accept your upload without performing meaningful work.
If you want a clearer picture of why encrypted files behave this way, you can review how encryption controls access to your protected RAR contents ↗️, which outlines the principles behind RAR protection and why it resists superficial online analysis.
❌ Why Online Tools Almost Always Fail on Real RAR5 Archives
Modern RAR files — especially RAR5 — use:
- AES-256 encryption
- Slow key derivation (hash strengthening)
- Optional encrypted headers
Together, these features make unauthorized access extraordinarily difficult, even with full local resources. To understand why, see how the RAR5 KDF strengthens your encrypted RAR file ↗️. The deliberate slowdown of each password attempt means that cloud-based guessing — which must serve many users at once — becomes even less practical.
Online services typically fail for at least one of these reasons:
- They cannot test enough passwords per second because RAR5’s KDF is computation-heavy.
- They don’t have access to filenames or metadata if headers are encrypted.
- They rely on simple dictionary lists that are ineffective against strong passwords.
Even legitimate offline tools cannot exceed the cryptographic limits when the password is extremely strong. But offline tools at least operate safely, privately, and transparently.
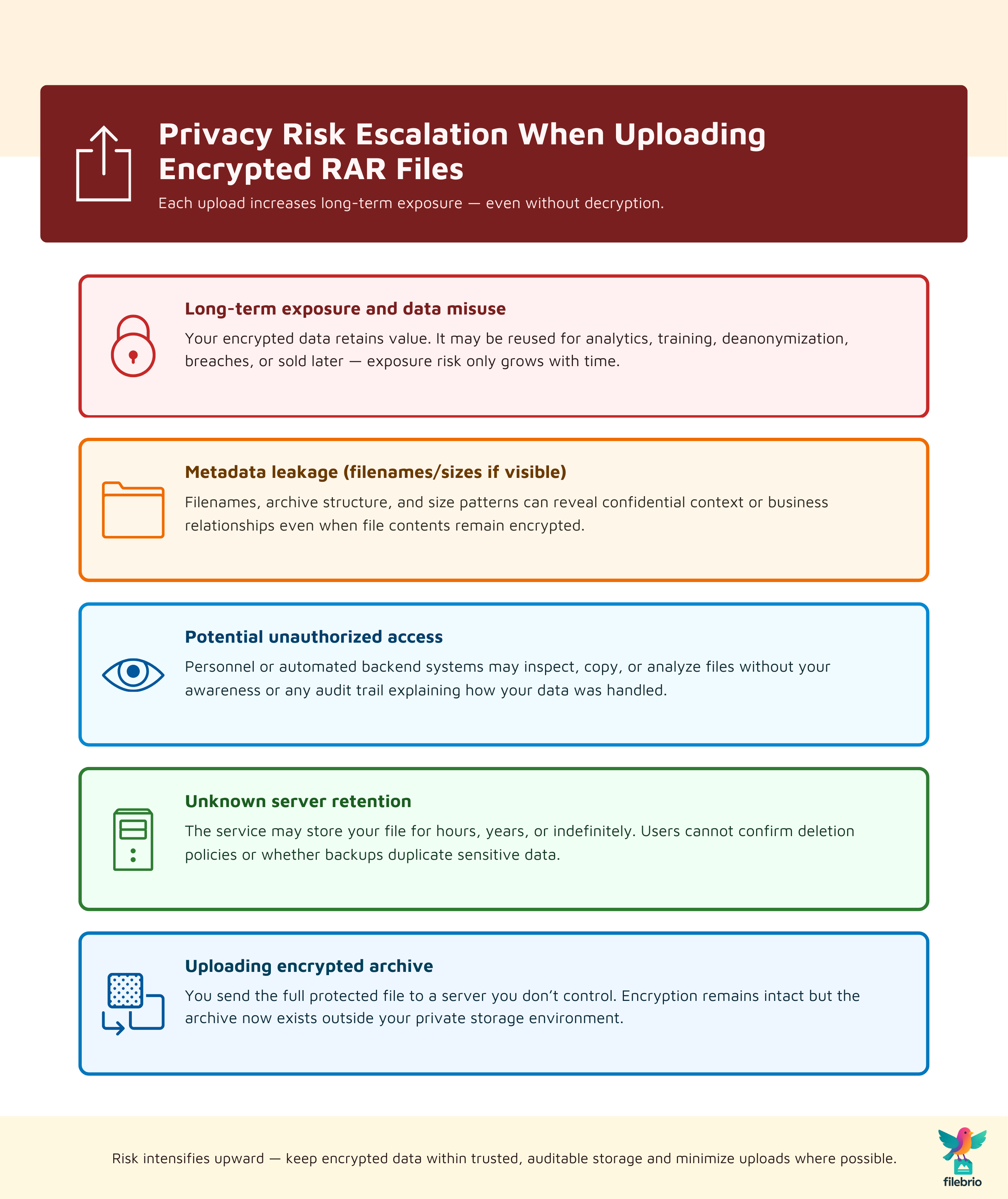
🔓 Privacy & Exposure Risks When Uploading Your Archive
Uploading an encrypted archive to an online tool is not the same as entering a password into a website. An encrypted RAR file still contains:
- your private data, encrypted but intact
- metadata about structure or format (unless headers are encrypted)
- file sizes or volume relationships
Some services keep uploaded archives indefinitely, while others sell aggregated data for training or analytics. Even if the contents remain encrypted, exposure of the archive itself is a privacy event.
To better understand what parts of an archive are visible or hidden depending on settings, review why encrypted headers make content discovery impossible ↗️. When headers are not encrypted, even filenames may leak sensitive context.
🧪 How to Diagnose Your File Before Trying Any Recovery
Before you try any recovery method — online or offline — it is essential to determine why the archive won’t open. Many users assume the password is wrong when the real issue may be:
- file corruption
- format mismatch
- missing volumes
- header encryption making the file appear blank
These distinctions matter. A high-level guide such as how to identify whether your RAR file is encrypted or simply corrupted ↗️ can help you understand the difference before taking any risky steps.
Additionally, consider whether the file is still structurally viable. For this evaluation, see how to confirm whether your RAR archive is still technically recoverable ↗️ — a useful starting point for deciding what action makes sense.
🧰 All-In-One Local Solution for Sensitive RAR Archives
When dealing with files that may contain personal documents, business records, photos, or confidential metadata, local software is by far the safer choice. Online tools demand full trust in unknown servers, but offline tools keep every operation within your own environment.
FileBrio Office Suite provides a unified, privacy-first workspace for working with encrypted RAR and WinRAR archives on your own machine. Its RAR Master module focuses on:
- local-only processing — nothing is uploaded
- structured diagnostics — understand what blocks access
- offline evaluation — test feasibility safely
To explore how the suite handles RAR tasks, see the feature summary for FileBrio RAR Master ↗️.
You can download all FileBrio tools directly from the official installer page ↗️ to avoid unverified sources.
________________________
FileBrio RAR Master — part of the FileBrio Office Suite — is a privacy-first, offline Windows toolkit for diagnosing and safely regaining access to your own password-protected RAR / WinRAR archives.
- Local processing only — nothing leaves your PC.
- Smart diagnostics to separate password issues from corruption.
- Owner-verified recovery workflows designed strictly for legitimate use.
Reminder: FileBrio RAR Master may be used only with archives you own or are explicitly authorized to access. It performs all analysis and recovery operations locally on your device, without uploading data anywhere.
________________________
💽 Why Offline Tools Are Safer and More Reliable
Offline tools offer several critical advantages:
- No data leaves your computer.
- Consistent hardware availability — no shared cloud resources.
- More diagnostic visibility into structure, corruption, and format.
- Safer workflow when dealing with sensitive personal or client files.
For a broad, conceptual comparison of risks, you can read why offline tools keep your encrypted RAR data private ↗️, which explains how local environments reduce exposure.

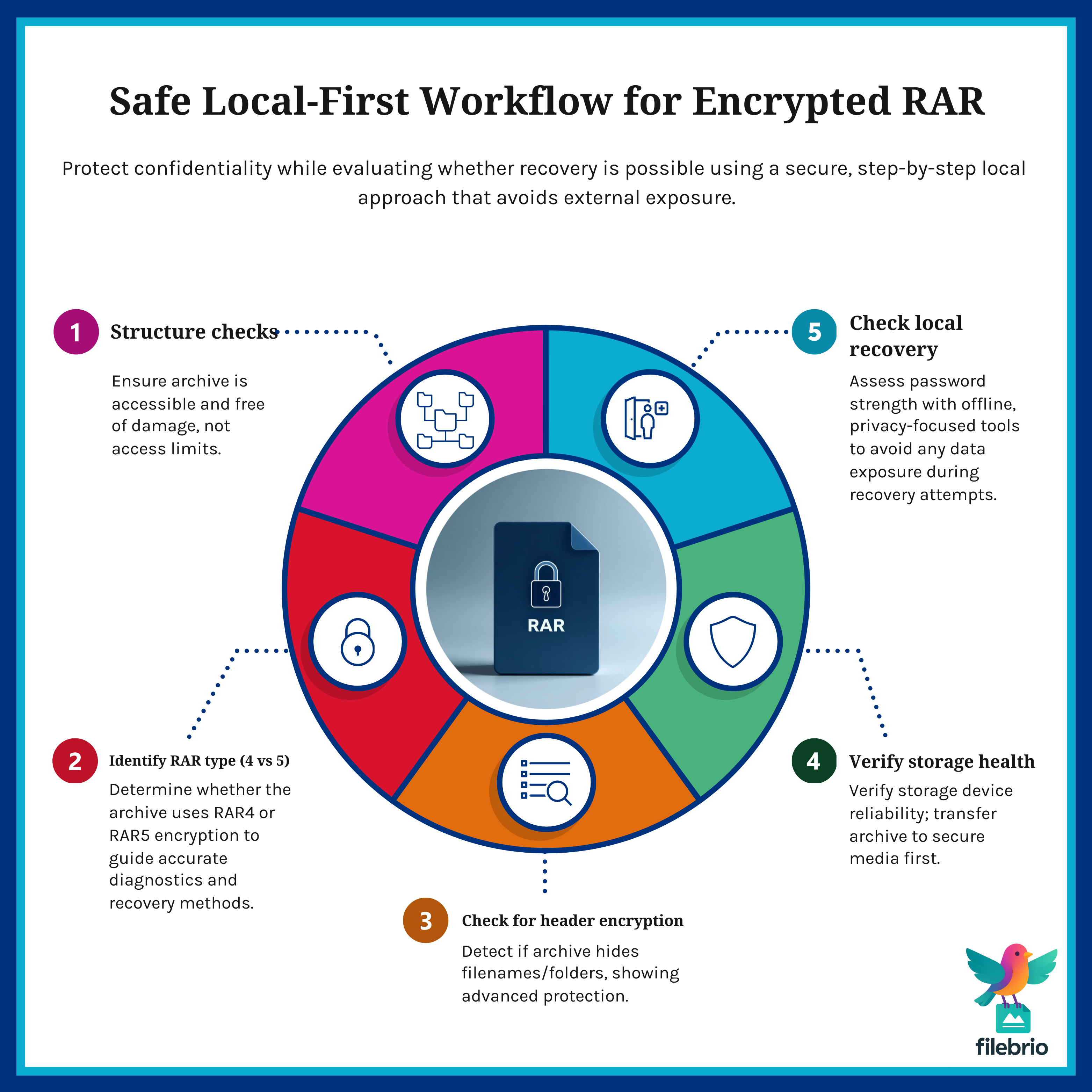
📁 How to Build a Safe Local Workflow for Encrypted Archives
When working with encrypted RAR files, a safe and predictable workflow protects both your data and your long-term access. A typical local-first workflow includes:
- Run basic structure checks — make sure the archive is readable at the file level.
- Identify encryption type — differentiate between RAR4 and RAR5.
- Check for header encryption — filenames and sizes may be hidden.
- Assess physical storage health — avoid diagnosing from failing drives.
- Use safe tools to evaluate feasibility — no cloud uploads.
If your workflow includes multi-user environments, see how teams can preserve long-term access to encrypted RAR archives ↗️ for broader planning strategies.
🛡️ Secure Offline Toolkit for RAR Diagnostics & Recovery
FileBrio RAR Master is specifically built for privacy-first RAR diagnostics and responsible recovery evaluation. Instead of uploading sensitive archives to unknown websites, you can:
- inspect structure locally
- verify format & header encryption
- evaluate feasibility using accurate, offline methods
- detect corruption or missing volumes safely
If you want to understand the conceptual limits of recovery — especially when encrypted headers or strong entropy are involved — review RAR security limitations in encrypted-header scenarios ↗️.
________________________
FileBrio RAR Master — a secure, offline Windows toolkit for regaining access to your own password-protected RAR / WinRAR archives while keeping all data strictly on your device.
- Offline-only processing — never uploads your archives.
- Smart issue detection — password vs corruption.
- Fast recovery workflow optimized for legitimate ownership.
⬇️ Download FileBrio RAR Master
Reminder: FileBrio RAR Master is intended only for archives you own or are explicitly authorized to access. All operations run locally on your PC.
________________________
⚖️ Legal & Ethical Reminder
Only evaluate or attempt recovery on archives you own or have explicit permission to handle. Strong encryption is specifically designed to protect confidentiality, and attempting access without authorization may violate privacy or compliance regulations. Always ensure your actions are legitimate, documented, and aligned with ethical data-handling standards.
This article is provided for general informational and educational purposes only. Any examples, scenarios, or references to password recovery, archive security, or related tools (including FileBrio RAR Master or similar software) are intended solely to help you better understand how to protect and manage your own data.
You may only apply any techniques, workflows, or tools described here to files and archives that you fully own or are explicitly and verifiably authorized to access. Attempting to bypass, remove, or recover passwords for third-party data without clear permission may violate criminal law, civil law, or internal company policies in your jurisdiction.
Nothing in this article constitutes legal advice. Laws and regulations differ between countries and organizations, and you are solely responsible for ensuring that your actions comply with all applicable legislation, contracts, and internal policies. If you are unsure whether a particular action is lawful or permitted, consult a qualified legal professional before proceeding.
🧷 Summary & Action Steps
Online “RAR password decryption” services pose serious risks: privacy exposure, unreliable results, weak security practices, and misleading expectations. They rarely help because RAR5 encryption is intentionally resistant to online guessing and cloud-based shortcuts. By contrast, offline tools give you privacy, transparency, and better diagnostic clarity.
To work safely with your own encrypted archive:
- Never upload sensitive RAR files to online tools.
- Diagnose your archive locally before attempting recovery.
- Use offline, privacy-focused utilities to maintain control.
- Plan for future access by storing password metadata securely.
🔗 See Also: Related High-Level Guides
- Breaking RAR/WinRAR Passwords Online: Why the Search Term Is Misleading and What Safe Methods Actually Exist ↗️
- Why Offline Recovery Tools Are Safer for Privacy ↗️
- Restoring Access to RAR/WinRAR Archives: Safe and Legal Methods for Handling Your Own Files ↗️
- How to Evaluate Safe Options for Regaining Access to a RAR/WinRAR Archive You Own ↗️
- How to Identify Whether Your RAR File Is Encrypted or Simply Corrupted ↗️