
How to Create Strong Yet Memorable RAR Passwords That You Won’t Lose in the Future
Strong RAR passwords are essential — but memorability is equally important. Many users lock their archives with robust passphrases, only to discover months or years later that they can’t remember them. Because RAR passwords cannot be reset like online accounts, forgetting even one can result in permanent loss of access to your own data. Fortunately, the key to long-term recall isn’t perfect memory: it’s smart design.
This guide shows how to craft strong, memorable passwords based on proven cognitive patterns, so you can secure your RAR archives today without locking out your future self.
🧭 Navigation
⚡ TL;DR — Strong and Memorable RAR Passwords
Creating a strong yet memorable RAR password means balancing security with long-term recall. The best passwords use meaningful personal cues, structured patterns, and safe complexity — without relying on guessable information or unsafe formulas. Memory cues, password themes, and smart metadata storage drastically reduce the risk of lockout.
🧠 Why RAR Passwords Are Easy to Forget
RAR passwords behave very differently from everyday login credentials. Email, banking, and app passwords are typed frequently, reinforcing long-term memory. RAR passwords, however, often protect:
- one-off archive exports
- old project backups
- rarely-accessed sensitive documents
This means they can go untouched for months or years. As discussed in why everyday habits affect your forgotten RAR password ↗️, password recall is heavily dependent on repetition, context, and emotional significance.
🔬 Cognitive factors that cause forgotten RAR passwords
| Factor | Effect on Password Memory |
|---|---|
| Low repetition | Long-term memory never forms; password fades. |
| High security complexity | Hard to reconstruct without strong mental cues. |
| Stress or urgency at creation time | Weak encoding; memory formed under pressure decays quickly. |
| Lack of context reminders | No mental anchor connecting password to its archive. |
Understanding why passwords are forgotten helps you design ones that your future self can reliably recall — without sacrificing cryptographic strength.
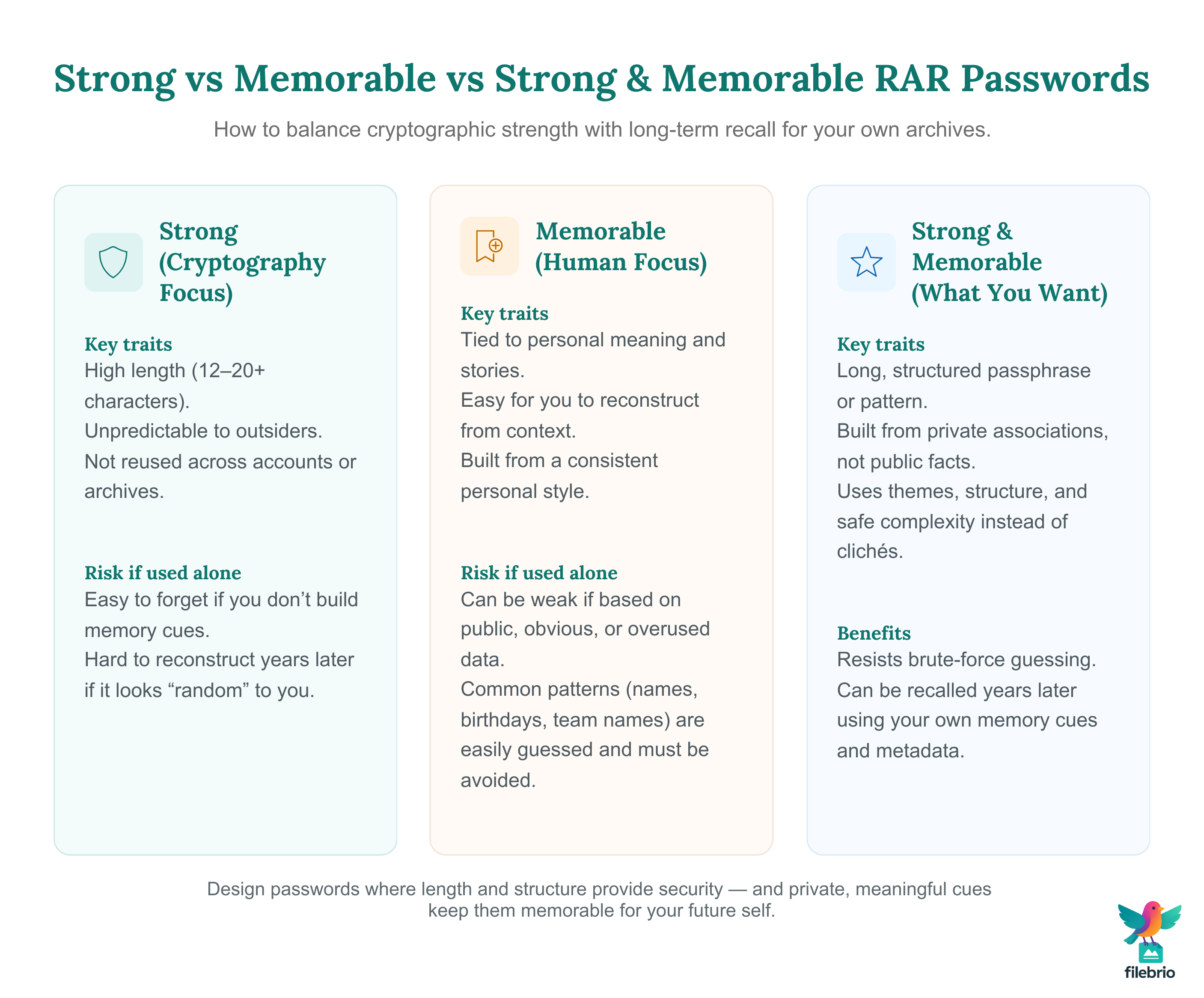
🔐 What Makes a Password Both Strong and Memorable
A strong password is one that resists brute-force guessing. A memorable password is one you can reproduce even after long intervals. It’s surprisingly easy to achieve both, provided you base your password on personal but non-obvious patterns.
According to how length and entropy affect guessing complexity ↗️, password length contributes far more to security than arbitrary symbol usage. This simplifies design: longer memorable structures can outperform short complicated ones.
Characteristics of a strong password
- High length (12–20+ characters)
- Unpredictable to outsiders
- Not based on dictionary words or clichés
- Not reused across accounts or archives
Characteristics of a memorable password
- Meaningful but not guessable
- Derived from private associations
- Built from a consistent personal “style”
- Linked to memory cues you create intentionally
To better understand your natural password tendencies, many users benefit from ways to study patterns behind your RAR password choices ↗️. This helps reveal how your brain intuitively constructs passwords.
🧠 Turn “I’ll Remember This Password” Into a Real Plan
Even when a password is carefully designed, there’s always a quiet worry in the background: “What if I forget this in two years?” It’s one thing to choose a strong, memorable structure — it’s another to be sure that your protected RAR archives will still make sense to you when life, projects, and devices change.
A safer approach is to combine good password habits with a clear view of how your protected archives actually behave:
- See which RAR archives are truly critical and deserve your best password designs
- Understand which ones use RAR4 vs RAR5 so you know where security is already strongest
- Check whether header encryption is enabled before you rely on filenames as memory cues
- Confirm your archives are structurally healthy so you’re not blaming “bad memory” for a damaged file
| What You Usually Experience | What a Structured Overview Gives You |
|---|---|
| “I know I set a strong password, but I’m not sure how risky lockout really is.” | A clear picture of which archives are most important and how they’re protected. |
| “Some RAR files feel opaque — I can’t tell what’s inside or how they’re configured.” | Insight into encryption mode, header behavior, and recovery features without exposing your data. |
| “I don’t know which archives I should revisit or modernize first.” | A way to prioritize where better passwords and updated formats will help most. |
________________________
FileBrio RAR Master — part of the FileBrio Office Suite — is a privacy-first, offline Windows toolkit for diagnosing and safely regaining access to your own password-protected RAR / WinRAR archives.
- Local processing only — nothing leaves your PC.
- Smart diagnostics to separate password issues from corruption.
- Owner-verified recovery workflows designed strictly for legitimate use.
Reminder: FileBrio RAR Master may be used only with archives you own or are explicitly authorized to access. It performs all analysis and recovery operations locally on your device, without uploading data anywhere.
________________________
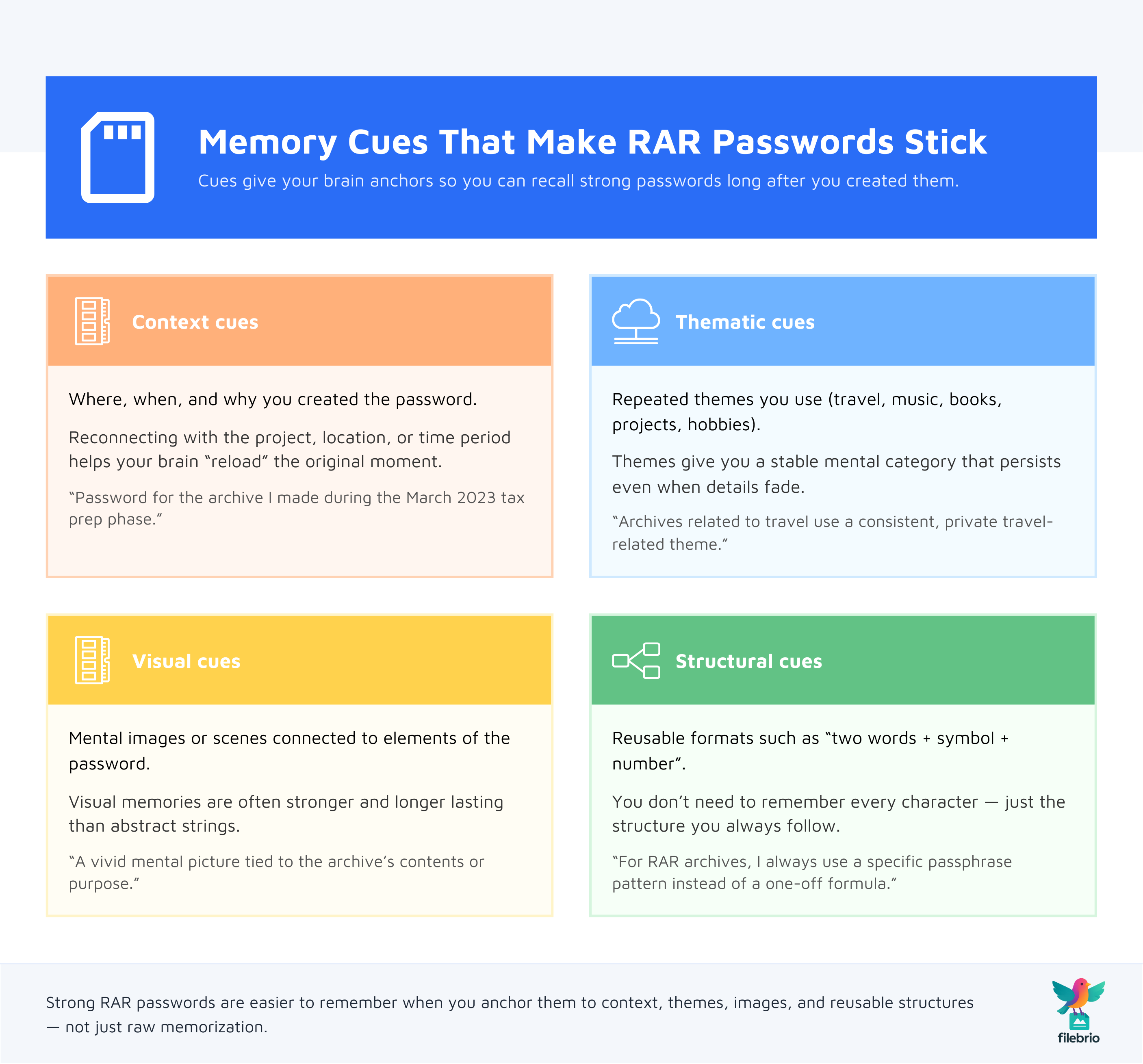
🧩 Using Memory Cues to Build Long-Term Password Retention
Password memory is not just about the password — it’s about the supporting mental cues. Cues help your brain “index” a password, the same way folders help you locate files on a computer.
🔑 Types of memory cues that outperform raw memorization
- Context cues: where, when, and why you created the password.
- Thematic cues: consistent patterns you always use.
- Visual cues: associating a mental image with elements of the password.
- Structural cues: repeating formats like “two words + symbol + number.”
These are the same techniques used in structured ways to reflect on your RAR password ↗️, where users reconstruct forgotten passwords by recovering the cues that shaped them.
Why cues work
Your brain is optimized for remembering stories, not random symbols. Passwords constructed with rich personal meaning — but not obvious meaning — anchor into long-term memory far more reliably than arbitrary strings.
📘 Safe, Structured Approaches to Password Creation
To create strong yet memorable RAR passwords, use a structured pattern with enough entropy to be secure but enough consistency to be memorable.
Recommended structure frameworks
| Framework | Description | Strength | Memorability |
|---|---|---|---|
| Themed passphrase | Four unrelated words following a personal theme. | High | High |
| Story fragment | A sentence fragment encoded into initials + symbols. | High | Medium-high |
| Hybrid pattern | Two meaning-based components plus random segment. | Very high | Medium-high |
| Memory-anchor method | Password tied to a vivid, private mental image. | Medium-high | High |
These patterns maintain randomness while ensuring you can recall them using mental cues, not brute memorization.
Before committing to any structure, many users first review how to safely diagnose your locked RAR file ↗️ to ensure no other issues (like corruption) are present.
🔎 Avoiding Weak Patterns That Feel Memorable but Aren’t Secure
Certain memory-friendly patterns are extremely common — and extremely insecure. Avoiding these is essential, especially when working with RAR archives that may protect sensitive or irreplaceable data.
Patterns to avoid completely
- Birthdays, anniversaries, or familiar dates
- Pet names, partner names, children’s names
- Favorite sports teams or cities
- Reversed dictionary words
- Simple substitutions (e.g., “a → @”, “o → 0”)
These patterns are widely predicted and often appear in low-quality wordlists. As explained in how ethical principles shape wordlists ↗️, attackers exploit these predictable structures — another reason to avoid them entirely.
🔐 A Private, Offline Safety Net When Your Memory Isn’t Perfect
Even with strong, well-designed password habits, there may come a day when a RAR archive feels unfamiliar: the context is fuzzy, the filename doesn’t ring a bell, or you’re no longer sure which pattern you used. In that moment, you need a calm, offline way to understand what’s going on before you make any risky moves.
A dedicated local toolkit can help you:
- Distinguish password issues from corruption so you don’t blame your memory for a damaged file
- Inspect encryption and header settings without exposing sensitive archives to online services
- Check feasibility before you invest time into recovering access to older protected data
- Work only on copies, keeping your original long-term archives untouched and safe
| If You React on Impulse | If You Use an Offline Safety Net |
|---|---|
| Guess passwords blindly and risk confusion or lockout. | See which archives are healthy, encrypted, or damaged before you act. |
| Upload sensitive files to random tools “just to check.” | Keep every inspection and diagnostic step on your own Windows system. |
| Change or repack archives without a clear plan. | Base every decision on structured diagnostics and clear metadata. |
________________________
FileBrio RAR Master — a secure, offline Windows toolkit for regaining access to your own password-protected RAR / WinRAR archives while keeping all data strictly on your device.
- Offline-only processing — never uploads your archives.
- Smart issue detection — password vs corruption.
- Fast recovery workflow optimized for legitimate ownership.
⬇️ Download FileBrio RAR Master
Reminder: FileBrio RAR Master is intended only for archives you own or are explicitly authorized to access. All operations run locally on your PC.
________________________
📂 How to Store Non-Sensitive Password Metadata Safely
You should never store the password itself, but storing structured “memory metadata” is both safe and extremely helpful.
Examples of safe metadata to store
- “Used passphrase structure A-B-C-D”
- “Tied to project phase from March 2023”
- “Derived from theme: travel / music / architecture / etc.”
- “Variant based on my standard memorable pattern”
The metadata does not reveal the password but preserves the cues that help you reconstruct it. See how to safeguard reference info for your RAR passwords ↗️ for safe approaches to metadata storage.
📚 Practical Examples of Strong & Memorable Password Design
The following examples illustrate how to apply structured memory cues without revealing real passwords or unsafe patterns.
Example 1 — The Themed Passphrase
You choose a theme meaningful only to you — for instance, “nonfiction book topics” or “places you visited in 2021.” You convert this theme into a four-word passphrase plus one personal modifier. The result is long, strong, and tied to a memory theme that persists.
Example 2 — Story Fragment Encoding
You take a private, meaningful sentence and encode it using initials and a symbol separator. This creates high entropy but attaches to a narrative you can recall.
Example 3 — Hybrid Pattern
Combine one meaningful cue, one abstract component, and one random—but reproducible—segment, such as a consistent personal formula. The randomness protects security while the structure protects memory.
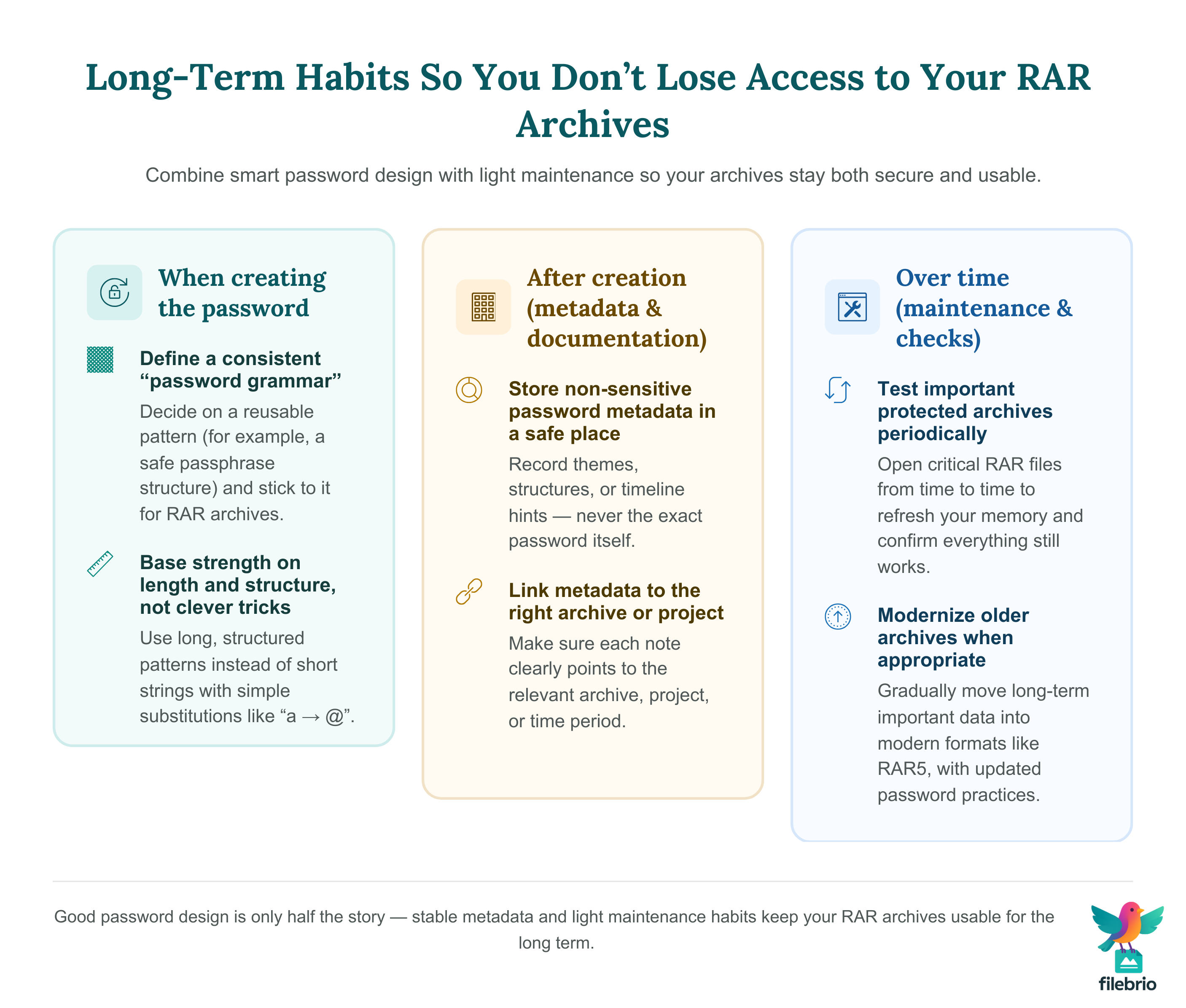
🛡️ Long-Term Habits to Ensure You Never Lose Access
Creation is only half the solution. Long-term access requires ongoing habits.
Essential long-term practices
- Create a consistent password “grammar.”
- Maintain safe metadata about themes or structures.
- Test your protected archives annually.
- Update old archives to modern formats when appropriate (RAR5).
If you’re working with older archives, see why older RAR4 files remain relevant ↗️ to understand compatibility considerations.
With a consistent method and safe anchor cues, password loss becomes extremely unlikely — even after many years.
📜 Legal Reminder
This article is provided for general informational and educational purposes only. Any examples, scenarios, or references to password recovery, archive security, or related tools (including FileBrio RAR Master or similar software) are intended solely to help you better understand how to protect and manage your own data.
You may only apply any techniques, workflows, or tools described here to files and archives that you fully own or are explicitly and verifiably authorized to access. Attempting to bypass, remove, or recover passwords for third-party data without clear permission may violate criminal law, civil law, or internal company policies in your jurisdiction.
Nothing in this article constitutes legal advice. Laws and regulations differ between countries and organizations, and you are solely responsible for ensuring that your actions comply with all applicable legislation, contracts, and internal policies. If you are unsure whether a particular action is lawful or permitted, consult a qualified legal professional before proceeding.
🔗 See Also — Related Guides
- How to Avoid Forgetting RAR Passwords in the Future: Practical Retention Strategies ↗️
- Why Common RAR Passwords Fail: Patterns, Risks, and Security Lessons ↗️
- Understanding Password Encodings in RAR Archives (Unicode, Cyrillic, etc.) ↗️
- How High-Quality Wordlists Are Created: Principles, Ethics, and Safer Alternatives ↗️
- How to Avoid Losing Access to Decade-Old RAR Archives ↗️
- Removing or Changing a RAR/WinRAR Password: What’s Possible When You Own the Archive ↗️
- How to Create Password Policies for RAR Archives in Business Settings ↗️