How to Confirm Whether Your RAR Archive Is Still Technically Recoverable
Realizing that a RAR archive you own might be “locked forever” is a stressful moment. Maybe WinRAR keeps asking for a password you no longer remember, maybe it shows corruption errors, or maybe nothing opens at all and you are left wondering whether you should invest more effort or accept that the data is gone.
This article walks you through how to evaluate technical recoverability before you waste time, money, or take risky actions. You will learn how to read symptoms, what encryption mode and header settings imply, and how archive structure (volumes, recovery records, media health) affects your chances. The goal is to help you decide whether your own RAR archive is still realistically recoverable — without guesswork and without touching files that are not yours.
🧭 Navigation
📌 TL;DR — Quick Recoverability Checklist
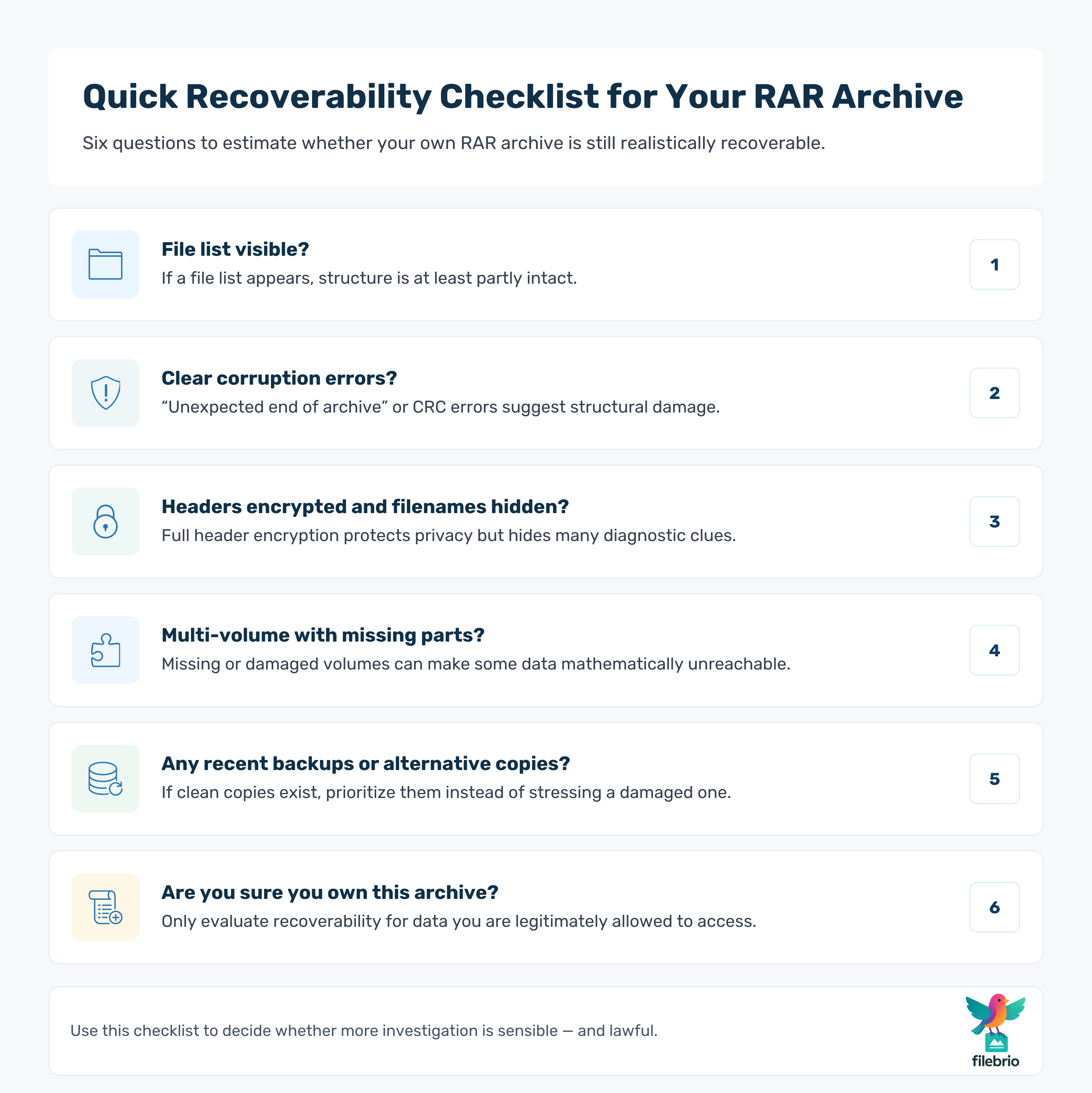
If you only have a few minutes, use this high-level checklist to get an initial feeling for whether your RAR archive is still technically recoverable:
- Does the file open and show a file list? If the file list appears, the archive structure is at least partially intact and the main question is whether the password can be remembered or reconstructed.
- Do you see clear corruption errors? Messages about unexpected end of archive, CRC errors, or truncated volumes suggest structural damage that may limit how much can be recovered.
- Are headers encrypted and filenames hidden? Full header encryption protects privacy but removes many diagnostic clues, making blind guessing riskier and harder to evaluate.
- Is it a multi-volume archive with missing parts? Missing or damaged volumes can make some or all data mathematically unavailable, regardless of password knowledge.
- Do you have recent backups or alternative copies? If other copies open cleanly, focus on those first rather than forcing a badly damaged archive.
- Are you sure you own the archive? Never attempt to access data that is not yours or that you are not authorized to handle.
What follows is a deeper, structured way to confirm whether continued attempts are sensible or whether the archive has reached a point where recovery is no longer realistic.
🔓 Introduction: From Panic to Structured Evaluation
When an important RAR archive stops opening, it is tempting to jump straight into random password attempts or install every “magic tool” you can find online. That reaction is understandable — but technically it is the worst moment to act impulsively. Quick, uninformed decisions can overwrite damaged media, corrupt partial data further, or leak sensitive information to untrustworthy services.
A safer approach is to pause and evaluate your situation first. Other articles in this series show how to perform symptom-based diagnosis and root-cause analysis for unopened archives, for example through ways to diagnose your unopened RAR file issue ↗️. Here, the focus is narrower: once you have a rough idea what is wrong, how do you answer a more precise question:
Is this archive still technically recoverable, or have mathematical or physical limits been reached?
🧠 Understanding the Idea of Technical Recoverability
“Technically recoverable” does not mean “easy” or “fast.” It means that, given enough time and lawful effort, there is still a realistic path to either full or partial data access. That path may involve password reconstruction, leveraging redundancy, using backup volumes, or working with clean copies on different storage.
Several dimensions shape recoverability:
- Cryptographic strength: Modern RAR formats use strong encryption. If the password is extremely long and random, and there are no memory cues, recovery may be mathematically infeasible even if the file itself is healthy.
- Archive integrity: If key structures are missing or corrupted (for example, severe truncation), part of the content may be permanently lost, regardless of password knowledge.
- Header visibility and metadata: When headers are encrypted, you lose many clues about what is inside and how healthy it is. Other articles explain how encrypted headers hide your protected RAR contents ↗️ and how that affects diagnostics.
- Environment and media health: Failing drives, broken USB sticks, and unreliable cloud sync can damage archives beyond practical repair.
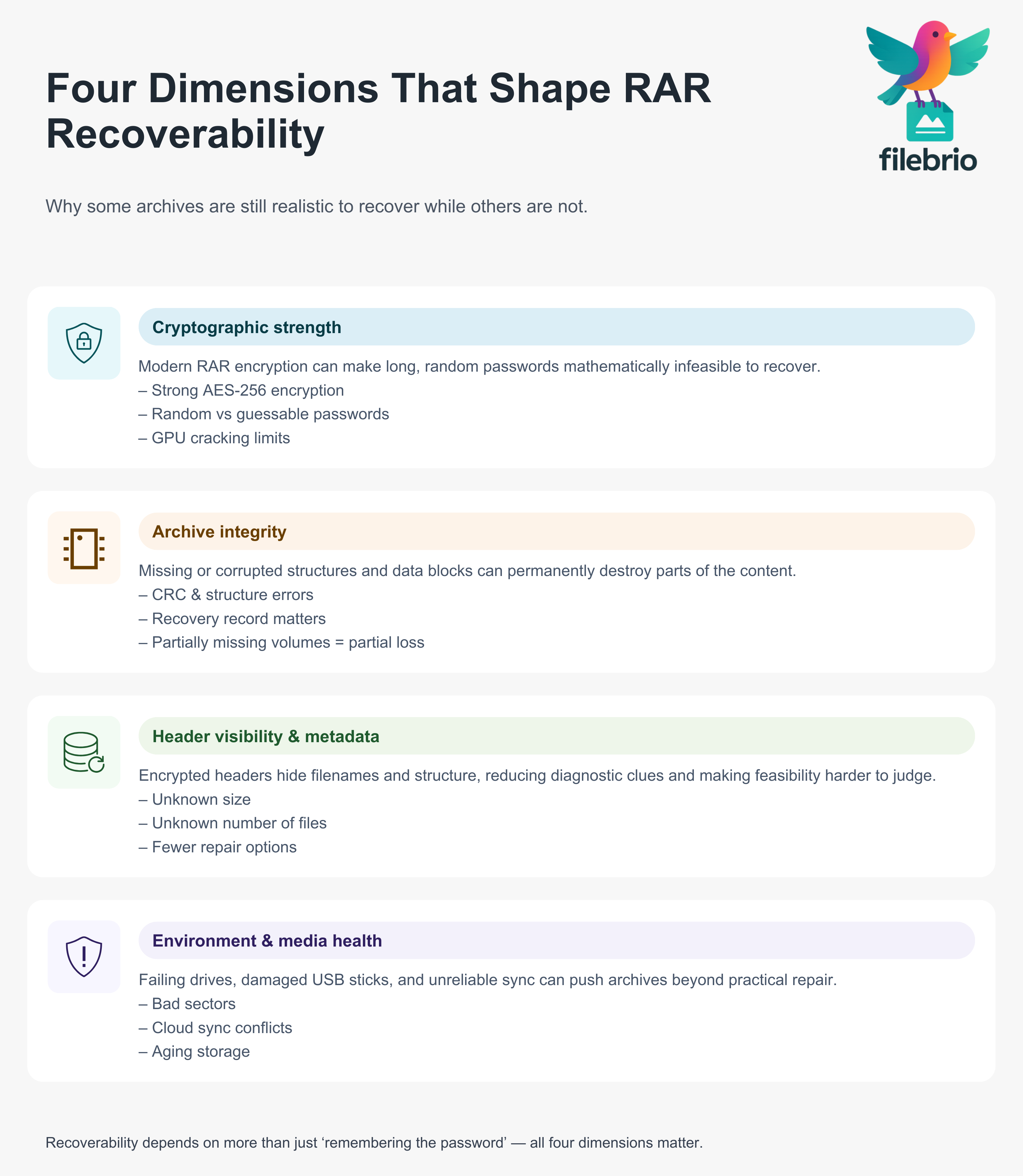
Your job is not to run experiments blindly, but to combine these dimensions into a calm, evidence-based judgment about whether further attempts have a reasonable chance of success.
🎯 Turn “Is This Lost Forever?” Into a Clear Technical Verdict
When a RAR archive refuses to open, it’s easy to spin in circles: is this a strong password doing its job, a damaged file system, or a multi-volume chain that quietly broke years ago?
Before you pour time, money, or hope into recovery, you need a clear, offline verdict on whether the archive is still technically recoverable at all.
FileBrio RAR Master is built to give you that verdict in a calm, structured way:
- 🔍 Shows whether the archive is mainly blocked by encryption, corruption, or format issues
- 📂 Inspects RAR4 and RAR5 structure, headers, and data blocks without forcing risky extraction
- 📦 Detects missing volumes, truncated tails, and damaged sectors that silently kill recoverability
- 🧩 Understands recovery records and
.revvolumes, so you know if redundancy can still help - 🛡️ Works 100% offline on your Windows machine — vital when the archive contains sensitive material
If you’re trying to decide whether there’s a realistic path forward or the archive has crossed a mathematical line, start with a structured, local diagnostic instead of guesswork:
________________________
FileBrio RAR Master — part of the FileBrio Office Suite — is a privacy-first, offline Windows toolkit for diagnosing and safely regaining access to your own password-protected RAR / WinRAR archives.
- Local processing only — nothing leaves your PC.
- Smart diagnostics to separate password issues from corruption.
- Owner-verified recovery workflows designed strictly for legitimate use.
Reminder: FileBrio RAR Master may be used only with archives you own or are explicitly authorized to access. It performs all analysis and recovery operations locally on your device, without uploading data anywhere.
________________________
🔍 Observing How Your RAR Archive Behaves
The first step is to look closely at how your archive behaves in a trustworthy local tool. Focus on what you can see without running risky repairs or aggressive operations.
| Symptom You See | What It Often Suggests | Typical Risk Level |
|---|---|---|
| Prompts for password, then rejects it | Likely wrong or incomplete password, archive itself may be healthy | Low to medium — depends on password complexity |
| Shows file list, but extraction fails with CRC errors | Data blocks are damaged, but structure is visible | Medium — partial recovery may still be possible |
| “Unexpected end of archive” or similar truncation error | Archive is cut off; tail data is missing | Medium to high — depends how much is missing |
| No file list, immediate error | Severe damage or unsupported/incorrect format | High — may indicate unrecoverable structure |
If you are still at the stage of figuring out why the archive will not open at all, you may want to review guidelines for diagnosing your unopenable RAR file ↗️ before you decide on overall feasibility.
🧪 Separating Password Problems from Structural Damage
A technically recoverable archive can still be temporarily “unusable” if you are facing a password issue — but that is very different from structural destruction. Clarifying which category you are in makes a big difference to your options.
- Password barriers: The archive opens and clearly shows a file list, but extraction requires a password you no longer remember. In this case, encryption is doing exactly what it was designed to do. Confirming whether the file is encrypted or corrupted is covered in more detail in how to tell if your RAR file is locked or damaged ↗️.
- Structural damage: The archive throws corruption errors, cannot list contents, or shows only partial lists. Here, feasibility depends on how much of the structural metadata and data blocks survive.
From a recoverability standpoint, a “pure password problem” on an otherwise healthy archive is technically recoverable as long as:
- You are sure you own the archive and have a legitimate right to access it.
- Your historical password habits are not fully random and there are realistic memory cues to revisit.
- There is no evidence of substantial file damage on top of the password barrier.
By contrast, if the file is seriously damaged, recovery may be limited even with the correct password. In such cases, it is important to follow how to safely diagnose your locked RAR file ↗️ without causing further harm.
🔐 What Encryption Mode and Header Settings Tell You
Modern RAR formats use strong cryptography, but the mode of encryption and the header settings change what you can infer about recoverability.
At a high level, you should pay attention to:
- RAR version: RAR4 and especially RAR5 use robust encryption. Understanding their protection models is explained in how RAR4 and RAR5 secure your protected data ↗️.
- Header encryption: If the archive uses header encryption, filenames and some structural details are hidden until the correct password is provided. Basic checks for header protection are described in simple ways to spot header encryption in your RAR file ↗️.
- Visible metadata: When headers are not encrypted, you can often see partial filenames, sizes, date stamps, and other details that help you judge whether the archive structure is intact.
| Header Setting | What You Can See | Recoverability Insight |
|---|---|---|
| Headers not encrypted | Filenames, sizes, some metadata visible without password | Easier to detect damage patterns and estimate which files might be intact |
| Headers encrypted | No filenames or structure visible without password | Privacy is higher, but diagnostics are limited; feasibility is harder to judge from outside |
When headers are encrypted, your ability to confirm recoverability depends heavily on indirect clues, as elaborated in how header encryption shapes your RAR recovery chances ↗️. You may need to rely more on storage health, backup copies, and contextual information about how the archive was created.
🧱 Checking Archive Structure, Volumes, and Recovery Records
Even with a perfect password, a badly damaged archive cannot yield perfect data. That is why structural health is a core part of technical recoverability.
Key structural questions include:
- Is the archive single-volume or multi-volume? Multi-volume sets depend on the presence and order of all required parts. An overview of how multi-volume behavior affects access is given in how passwords behave across your multi-volume RAR set ↗️.
- Are all volumes present and readable? Missing or unreadable parts can make certain files, or entire sections, unrecoverable.
- Were recovery records or .rev volumes created? Features such as recovery records and recovery volumes can significantly improve resilience, as described in how recovery records safeguard your damaged RAR files ↗️.
- What does metadata say about file integrity? Viewing structural hints through metadata can reveal whether corruption is localized or widespread; see how to read metadata clues in your RAR file ↗️ for conceptual guidance.
Another subtle factor is the type of files stored inside. Archives containing large, already-compressed formats (for example, certain media types) may be less tolerant of small errors than archives holding many small text-based files. High-level considerations around this are explored in how file types influence diagnostics for your RAR archive ↗️.
🧪 A Safe Lab for Testing Recoverability Before You Spend Effort
Once you know your archive is maybe recoverable, the next challenge is planning what to do — without smashing the only surviving copy or trusting unknown “online unlockers.” You need a controlled space where you can test integrity, structure, and password feasibility on your own terms.
FileBrio RAR Master acts as that offline lab for your own archives:
- 🧬 Lets you experiment on copies of your archive, keeping the original frozen and untouched
- 📊 Surfaces practical signals: how healthy the structure is, how much data seems intact, and where damage starts
- 🔐 Helps you separate “password still plausible” cases from those that are realistically unopenable
- 📦 Handles encrypted, damaged, and multi-volume RAR/WinRAR archives in one toolkit
- ⚙️ Integrates with your safe workflows for password reconstruction and corruption repair on archives you genuinely own
| Question You Have | What FileBrio Helps You See |
|---|---|
| “Is this just a password problem?” | Whether encryption is the main barrier or damage is also involved |
| “Are missing volumes killing my chances?” | Which parts of a multi-volume set are present, readable, or beyond repair |
| “Is it worth trying recovery at all?” | A realistic picture of integrity, redundancy, and technical limits |
If you want to make a calm, evidence-based decision before investing more energy, run your own archive through a private, offline technical check first:
________________________
FileBrio RAR Master — a secure, offline Windows toolkit for regaining access to your own password-protected RAR / WinRAR archives while keeping all data strictly on your device.
- Offline-only processing — never uploads your archives.
- Smart issue detection — password vs corruption.
- Fast recovery workflow optimized for legitimate ownership.
⬇️ Download FileBrio RAR Master
Reminder: FileBrio RAR Master is intended only for archives you own or are explicitly authorized to access. All operations run locally on your PC.
________________________
⚖️ Interpreting Technical Limits and When Recovery Is Unrealistic
At some point, you may have to decide that further attempts are no longer sensible. This is not just an emotional decision; there are objective signals that the archive has reached or is approaching technical limits.
| Signal | Likely Situation | Recoverability Outlook |
|---|---|---|
| Archive opens, headers visible, password clearly forgotten, very long random-looking credentials | Healthy file, but password space may be enormous | Technically recoverable in theory, but practically infeasible if no memory cues exist |
| Archive heavily truncated, no usable file list, no recovery records or backups | Critical structural data missing | Large parts may be mathematically unrecoverable |
| Multi-volume set with several missing segments | Key volumes lost or overwritten | Only limited partial recovery possible, often for files stored in surviving volumes |
| Strong encryption, very high-entropy password, no patterns from your usual habits | Cryptographic strength doing its job | Recovery may be impossible in realistic time frames, as discussed in why some archives become inaccessible |
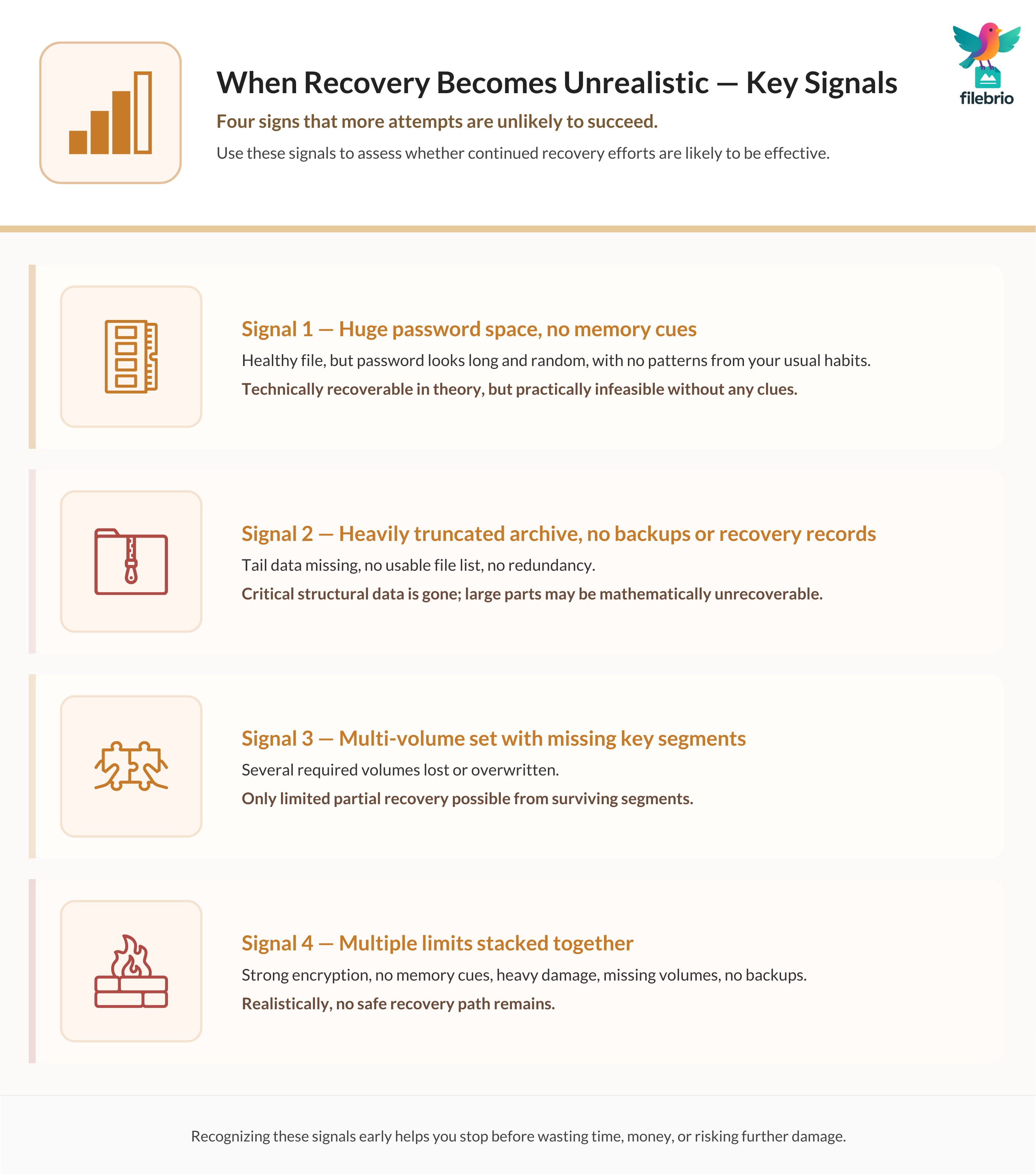
For a deeper conceptual view of why some archives cross the line into “unopenable” territory, see why strong encryption blocks access to your RAR file ↗️. When several limiting factors stack together — strong encryption, no memory cues, heavy damage, missing volumes, no backups — honesty may require accepting that the archive is no longer technically recoverable in any meaningful sense.
Before you reach that conclusion, ensure you have carried out basic, non-destructive checks similar to those described in what to review before guessing your RAR password ↗️, so that your decision is informed rather than rushed.
🛡️ Protecting Your Data While You Investigate
Even if you eventually conclude that an archive is no longer technically recoverable, you should still handle it — and your remaining copies — with care. Investigation itself can put the last good bits of data at risk if done recklessly.
Key protective habits include:
- Work from copies, not originals: Make a bit-level copy of the archive to separate storage and do all your tests on that, while keeping the original untouched.
- Avoid dubious online tools: Uploading a sensitive archive to unknown web services can permanently expose confidential data. A safer discussion of offline methods is available in why offline tools keep your encrypted RAR data private ↗️.
- Preserve surrounding metadata: Notes, filenames, folder context, and timestamps can all help reconstruct how the archive was created, which supports later analysis.
Looking forward, it is wise to strengthen your protection practices without making future access harder than necessary. Conceptual guidance for balancing safety with usability is covered in how to reinforce protection of your encrypted RAR files ↗️.
📂 When to Involve Professionals and How to Prove Ownership
Sometimes you will reach a point where internal tools and your own analysis are not enough. If the data is critical and the archive still seems technically recoverable, you may consider professional help — but this comes with legal and practical responsibilities.
Two aspects matter most:
- Clear ownership and authorization: Before anyone else touches the archive, make sure you can demonstrate that it is genuinely yours or your organization’s. Corporate scenarios are discussed further in ways to document ownership of your encrypted RAR file ↗️.
- Documented chain of custody: Keep a record of where the archive came from, which devices it was stored on, what tools have touched it, and what copies were made. This helps both technically and legally.
In high-sensitivity environments, long-term planning also matters. Organizations need sustainable practices to avoid repeating the same problems years later, as described in how teams can preserve long-term access to encrypted RAR files ↗️. Any external service you involve should operate under clear agreements, respect confidentiality, and comply with relevant laws and internal policies.
⚖️ Legal Reminder
This article is provided for general informational and educational purposes only. Any examples, scenarios, or references to password recovery, archive security, or related tools (including FileBrio RAR Master or similar software) are intended solely to help you better understand how to protect and manage your own data.
You may only apply any techniques, workflows, or tools described here to files and archives that you fully own or are explicitly and verifiably authorized to access. Attempting to bypass, remove, or recover passwords for third-party data without clear permission may violate criminal law, civil law, or internal company policies in your jurisdiction.
Nothing in this article constitutes legal advice. Laws and regulations differ between countries and organizations, and you are solely responsible for ensuring that your actions comply with all applicable legislation, contracts, and internal policies. If you are unsure whether a particular action is lawful or permitted, consult a qualified legal professional before proceeding.
📚 See Also
- How to Interpret RAR Error Messages and What They Reveal About File Health ↗️
- How to Check Whether Your RAR Archive Uses Header Encryption ↗️
- How to Evaluate What’s Still Possible Without the Correct RAR Password ↗️
- Safe Ways to Inspect and Extract Data From RAR Files ↗️
- How RAR SFX Packaging Affects Access and Protection ↗️
- Why Ethical Wordlist Principles Matter When Assessing Password Feasibility ↗️
- How to Use Dummy Archives to Test RAR Behavior and Feasibility Safely ↗️