
How to Check the Internal Structure of RAR Archives Without Extracting Files
Maybe you’ve found an old RAR archive, or a client has sent you a protected file, and you don’t want to extract anything yet. You just need to understand what’s inside: is the archive healthy, encrypted, or partially damaged? Is it worth investing time into access or recovery, or is it already in bad shape?
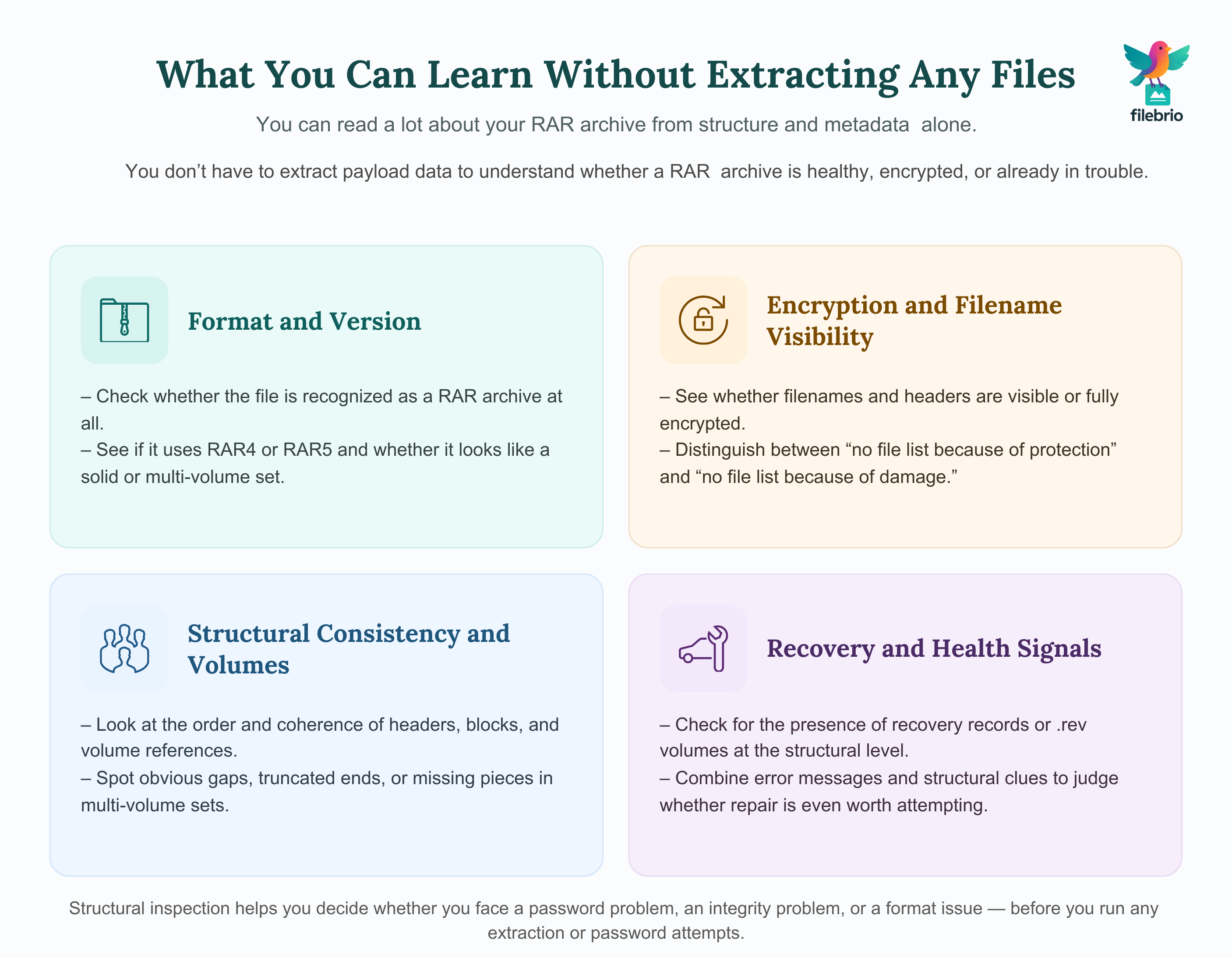
The good news: you can learn a surprising amount about a RAR file without extracting a single byte of payload data. By looking at structure, headers, and metadata, you can often tell whether the issue is password-related, integrity-related, or a format mismatch — and you can do it in a way that’s careful, privacy-first, and respectful of legal boundaries.
This article walks you through how RAR archives are structured, what you can safely inspect, and how those clues help you decide what to do next, especially before you try any kind of password-related action.
🧭 Navigation
Important
The information provided in this article applies exclusively to RAR / WinRAR archives for which you have full, demonstrable ownership or properly documented authorization. If you are not the rightful owner of the data, do not directly control it, or cannot clearly prove permission to access it, you must stop immediately. Attempting to access, recover, or modify data without explicit authorization may violate criminal law, civil statutes, corporate compliance requirements, and privacy regulations in many jurisdictions. You alone are responsible for ensuring that your actions are lawful and properly permitted before proceeding.
📌 TL;DR: Checking RAR Structure Without Extracting
You do not need to extract files from a RAR archive to understand a lot about its condition. Modern RAR/WinRAR archives contain headers, metadata, and structural markers that reveal whether an archive is encrypted, partially damaged, or likely still viable. By focusing on these structural clues instead of rushing directly to extraction, you can protect the remaining data, avoid making corruption worse, and make much better decisions about what to do next.
At a high level, safe RAR inspection means:
- Working only with copies of your archive in a controlled, offline environment.
- Reviewing headers and metadata conceptually to see compression method, format (RAR4 vs RAR5), multi-volume information, and whether headers or filenames are encrypted.
- Checking for structural consistency (do blocks and records appear in a plausible order, are volume references coherent, does the archive end suddenly?).
- Paying attention to error messages and failure patterns instead of guessing blindly what might be wrong.
- Separating password problems from corruption so you don’t waste time on password attempts against an archive that is structurally broken.
Once you understand the internal layout of your archive, you can decide whether it’s more of a password problem, an integrity problem, or simply a format/compatibility issue — and then move on to appropriate, lawful, and privacy-respecting next steps. Throughout the process, keep your focus on archives you own or are authorized to handle, and avoid tools or workflows that upload sensitive data to unknown servers.
🧩 Understanding What “Internal Structure” Means in RAR Archives
When we talk about the “internal structure” of a RAR archive, we are not talking about peeking into file contents. Instead, we mean the layout of control information that describes the archive:
- What RAR format it uses (RAR4 vs RAR5).
- Which blocks and headers appear and in what order.
- Whether filenames, headers, or data are encrypted.
- Whether the archive is part of a multi-volume set.
- Whether recovery records or recovery volumes (.rev) are referenced.
This structural layer is like a table of contents plus some technical labels. It doesn’t expose the plaintext of your data, but it does give you insight into the state of your archive. For example, understanding header and metadata behavior becomes much easier if you’ve already read about how to safely diagnose your locked RAR file ↗️ using early non-destructive checks.
Conceptually, RAR archives are composed of a sequence of blocks. Each block has a type, some flags, and optionally some attached data. Taken together, these blocks describe where volumes start and end, where file data lives, and how recovery-related features are arranged. When you “inspect structure,” you’re effectively reading these labels and checking whether they make sense, without touching the underlying file payload.
🧪 Preparing a Safe Environment Before You Inspect a RAR File
Before you look at any structural details, it’s important to set up an environment that protects both your data and your privacy. Structural inspection is low-risk compared to extraction, but mistakes can still happen if you inspect the wrong file, use untrusted tools, or accidentally modify your only copy.
Good preparatory habits include:
- Work on a copy of the archive. Keep the original in a read-only backup location so it’s always available if something goes wrong.
- Use offline, reputable tools. Avoid any utility that uploads your archive to a remote server. Offline tools are safer for privacy and align with the principles behind reading RAR metadata to understand what went wrong ↗️ locally.
- Make sure storage is healthy. If your RAR is stored on a failing USB drive or noisy network share, copy it to a stable local disk before doing anything else.
- Plan to observe, not modify. Your goal at this stage is to read and interpret structure, not to repair or alter the file.
With this safety mindset, you can inspect your RAR structure confidently, knowing you’re not inadvertently making a fragile situation worse.
🔍 High-Level Ways to Inspect RAR Structure Without Extraction
There are several categories of things you can safely check without extracting any files:
- Format recognition. Confirm whether the file is recognized as a RAR archive at all, and whether it appears to be RAR4 or RAR5.
- Header visibility and flags. You can conceptually review which headers are present, whether they’re marked as encrypted, and how they’re ordered. Articles such as understanding RAR header flags and metadata ↗️ explain why that matters for health checks.
- Filename visibility. If filenames are visible, that suggests headers aren’t fully encrypted; if nothing is visible, filename or header encryption may be active.
- Volume and segment information. For multi-volume archives, structural layout can reveal whether all segments appear to be present.
- Recovery-related metadata. Some archives reference recovery records inside the file, or separate .rev volumes, both of which are part of structure rather than content.
Importantly, these checks can usually be performed in a read-only manner. Your tools may show you “archive maps,” lists of headers, or metadata summaries without ever extracting user files. This is exactly the level you want to stay at when the priority is diagnostics first, actions later.
🧱 Key Elements Inside a RAR Archive: Headers, Blocks, and Metadata
To make sense of what you’re seeing, it helps to know the main building blocks of a RAR archive:
| Element | Role in Structure | What It Tells You |
|---|---|---|
| Main header | Defines basic archive properties and format. | Helps you see whether the file is RAR4 or RAR5 and whether the archive is solid, multi-volume, etc. |
| File headers | Describe individual files stored in the archive. | Indicate file names (if visible), sizes, timestamps, compression, and sometimes encryption flags. |
| Service/extra blocks | Store additional metadata or features. | May reference recovery records, comments, or format-specific features. |
| Data blocks | Contain compressed payload data. | These are typically not inspected directly at this stage; you just verify they appear in consistent locations. |
By reading flags and metadata in these headers, you can infer a lot. For example, you might use conceptual checks like those discussed in simple ways to spot header encryption in your RAR file ↗️ to see whether key structural information is deliberately hidden.
Filename behavior is also important. If you’ve ever looked into RAR filename encryption and its diagnostic limits ↗️, you’ll know that hiding names can be great for privacy but makes structure-based analysis more dependent on metadata and layout instead of obvious filenames.

🧬 Reading Structure to Distinguish Password Issues vs Damage
One of the biggest reasons to inspect structure first is to avoid wasting time on the wrong problem. A locked archive with a missing segment behaves differently from a healthy archive that simply needs the correct password.
Structural clues can help you tell:
- Is the archive recognized cleanly? If tools report that the file is not a RAR archive at all, you might be dealing with a different format or serious corruption. Articles like how to identify whether your RAR file is encrypted or simply corrupted ↗️ can help you interpret mixed symptoms.
- Do headers appear intact? If the main header is present and file headers follow in a plausible sequence, the archive is more likely structurally sound.
- Are errors consistent with password protection? Typical password mismatch messages differ from low-level I/O or truncation errors. You can compare them with the explanations in understanding RAR error messages ↗️.
- Do multi-volume references make sense? If the archive expects “part 3” but never finds it, that’s a structural gap rather than a password issue.
Cross-checking these signals with broader feasibility advice, such as how to confirm whether your RAR archive is still technically recoverable ↗️, helps you decide whether to invest effort or focus on data protection and backups instead.
💼 All-in-One Toolkit for Safe Local RAR Diagnostics
When you’re dealing with decades of personal archives, client deliverables, or sensitive internal data, using multiple random tools for diagnostics can quickly become messy and risky. You want a single, offline, privacy-first toolkit that can inspect structure, analyze headers, and prepare safe recovery workflows without ever uploading your archives.
This is exactly the kind of scenario where a specialized suite like FileBrio Office Suite is designed to help. Instead of juggling separate utilities for file integrity, metadata inspection, format detection, and password feasibility estimation, you can centralize these tasks in one controlled environment. That reduces the chance of copying the wrong file, mixing up versions, or accidentally sending confidential archives to an online service.
| Need | Why It Matters | How an All-in-One Toolkit Helps |
|---|---|---|
| Structure & header overview | Determine quickly whether your archive is usable at all. | Provides high-level maps for RAR4/RAR5, volumes, and recovery records. |
| Privacy-first diagnostics | Archives may contain personal, client, or corporate data. | Keeps all inspection local, with no uploads or background sync. |
| Guided next steps | Helps decide whether the issue is password, corruption, or both. | Integrates with features described in the FileBrio RAR Master features overview ↗️. |
If you’re comparing local diagnostics to cloud-based viewers or “online unlocker” sites, it’s worth reviewing a high-level comparison like offline vs online RAR recovery choices ↗️ so you can keep your structural inspection aligned with strong privacy standards.
________________________
FileBrio RAR Master — part of the FileBrio Office Suite — is a privacy-first, offline Windows toolkit for diagnosing and safely regaining access to your own password-protected RAR / WinRAR archives.
- Local processing only — nothing leaves your PC.
- Smart diagnostics to separate password issues from corruption.
- Owner-verified recovery workflows designed strictly for legitimate use.
Reminder: FileBrio RAR Master may be used only with archives you own or are explicitly authorized to access. It performs all analysis and recovery operations locally on your device, without uploading data anywhere.
________________________
⚙️ How File Type and Archive Design Influence RAR Structure
Even if you never extract files, the types of files stored inside the archive and the way you built it originally still influence its internal structure. Understanding this relationship can make your structural analysis much more accurate.
For example, archives that contain many small text files will have a different layout and compression behavior than archives dominated by large multimedia files. These differences affect the size and distribution of data blocks, and they shape how meaningful certain structural clues are. The deeper reasoning behind this is explored in resources such as how file-type structure affects RAR diagnostics and feasibility analysis ↗️.
Another structural factor is whether you used additional protection features, such as recovery records or .rev volumes. If you see references to recovery information in your structural view, it may align with the concepts described in RAR recovery records and .rev volumes ↗️, which can significantly improve your ability to reconstruct partial damage later on.
🛡️ Privacy-First Practices When Inspecting Encrypted RAR Files
Whenever you’re inspecting the structure of encrypted archives, one of your top priorities should be minimizing exposure of sensitive data. Even if you’re not extracting files, some tools may log details, upload samples, or keep telemetry you don’t want.
Good privacy-first practices include:
- Prefer offline tools and workflows. As a general rule, avoid online viewers and cloud-based services. Their behavior is hard to audit and may conflict with the principles discussed in why offline recovery tools are safer for privacy ↗️.
- Limit who can access your diagnostic environment. If you’re working in a corporate context, structure inspections should happen in a controlled environment with appropriate access controls.
- Be careful with logs and screenshots. Even structural metadata can be sensitive if filenames or paths reveal confidential information.
- Use test/dummy archives for training. If you want to teach others how RAR structure works, it’s better to use non-sensitive samples, much like the approach described in evaluating RAR protection using dummy archives ↗️.
By keeping these practices in mind, you can take advantage of structural diagnostics without compromising confidentiality.

🔐 Secure Offline Solution for Advanced RAR Archive Analysis
As your archives get larger, older, and more complex, manual structural inspection quickly becomes tedious. Multi-volume chains, nested archives, and mixed RAR4/RAR5 collections all require careful handling if you want to avoid mistakes. That’s where a dedicated, offline analysis environment can make a real difference.
FileBrio Office Suite, and specifically its RAR-focused components, are designed to support exactly this: advanced, privacy-first diagnostics for archives you legitimately own. Instead of switching between generic tools, you can keep structural checks, feasibility analysis, and follow-up options under one roof, reducing the risk of misconfigurations or accidental uploads.
- Centralized diagnostics. View archive formats, structural health indicators, and metadata in one place.
- Safer decision-making. Combine structural insights with guidance similar to strengthening RAR archive security while preserving future access ↗️, so you avoid locking yourself out later.
- Trusted download source. Keep your tools up to date from an official channel such as the FileBrio Office Suite download page ↗️ instead of unverified third-party sites.
________________________
FileBrio RAR Master — a secure, offline Windows toolkit for regaining access to your own password-protected RAR / WinRAR archives while keeping all data strictly on your device.
- Offline-only processing — never uploads your archives.
- Smart issue detection — password vs corruption.
- Fast recovery workflow optimized for legitimate ownership.
⬇️ Download FileBrio RAR Master
Reminder: FileBrio RAR Master is intended only for archives you own or are explicitly authorized to access. All operations run locally on your PC.
________________________
🧾 How to Document Your Findings and Prove Legitimate Ownership
Structural inspection is not only about technical insight. In many business or compliance contexts, you also need to prove that you had a legitimate right to work with the archive in the first place and that you handled it responsibly.
Good documentation habits include:
- Recording where the archive came from (project, system, or account) and who requested access.
- Keeping a concise log of structural observations (format, multi-volume status, presence of recovery records, visible vs encrypted headers).
- Noting any steps you took that are consistent with your organization’s information security policies.
- Linking your notes to internal asset inventories or ticket systems.
These habits align well with broader guidance about documenting encrypted archives and password metadata, such as how to store RAR password metadata securely for future you ↗️. Together, structure plus documentation gives you both technical and procedural evidence that you are acting within legitimate boundaries.
🛠️ Protecting Future Archives: Good Habits for Structure & Integrity
Once you’ve gone through the trouble of diagnosing one tricky archive, it’s natural to ask: how do I avoid this situation next time? Many of the most frustrating structural problems are preventable with a few habits and design decisions.
Some practical ideas:
- Use consistent, well-documented workflows. When everyone in a team builds archives the same way, future structural diagnostics become much easier.
- Leverage recovery records and redundancy. As explained in reconstructing missing parts of multi-volume RAR archives ↗️, redundancy and careful volume handling dramatically improve your chances when something goes wrong.
- Protect storage, not just encryption. Following advice similar to preventing RAR data loss on USB drives, HDDs, and cloud storage ↗️ ensures that structural integrity isn’t silently destroyed by flaky hardware.
- Think long-term. Articles such as maintaining long-term access to encrypted RAR archives in enterprises ↗️ emphasize that structural readability and documentation are just as important as strong encryption.
By combining good structure-aware behaviors with sound storage practices, you make it much easier for “future you” (or your future colleagues) to understand what’s going on inside an archive without immediately opening it.
⚖️ Legal Reminder
This article is provided for general informational and educational purposes only. Any examples, scenarios, or references to password recovery, archive security, or related tools (including FileBrio RAR Master or similar software) are intended solely to help you better understand how to protect and manage your own data.
You may only apply any techniques, workflows, or tools described here to files and archives that you fully own or are explicitly and verifiably authorized to access. Attempting to bypass, remove, or recover passwords for third-party data without clear permission may violate criminal law, civil law, or internal company policies in your jurisdiction.
Nothing in this article constitutes legal advice. Laws and regulations differ between countries and organizations, and you are solely responsible for ensuring that your actions comply with all applicable legislation, contracts, and internal policies. If you are unsure whether a particular action is lawful or permitted, consult a qualified legal professional before proceeding.
📚 See Also
- How RAR SFX Installers Handle Passwords and What You Should Expect ↗️
- Using Public Information Responsibly When Creating Security Guidelines ↗️
- Why Searching for “Break RAR Password Online” Leads to Unsafe Options ↗️
- Understanding RAR Decryption Concepts and Safe Ways to Work With Encrypted Files ↗️
- The Risks of Removing RAR Passwords Online — And Safer Offline Methods ↗️