
How to Check Whether Your RAR Archive Uses Header Encryption (Without Specialized Tools)
You double-click a RAR archive that matters, enter what you think is the right password, and… nothing useful appears. No file list, no friendly preview — just a prompt, an error, or an almost empty window. It’s hard to tell whether the archive is broken, the password is wrong, or something more subtle is going on.
In many cases, this behavior is caused by header encryption: the option that tells RAR to hide not only file contents, but also the file names and other directory information. It’s a powerful privacy feature — but it also removes many of the visual clues that normally help you diagnose what’s happening inside your archive.
This article focuses on one narrow but important question: how can you tell whether a RAR archive uses header encryption, without relying on specialized low-level tools? You’ll learn what to look for in your archiver’s behavior, how to avoid common misinterpretations, and how header encryption affects your expectations about visibility and recovery — always assuming you are working with archives you legitimately own.
🧭 Navigation
⚡ TL;DR — Quick Check for Header Encryption
Header encryption means the archive hides filenames, sizes, and directory information until the correct password is provided. If your RAR archive shows almost no file list, insists on a password before displaying anything useful, and offers no readable filenames even after basic inspection, it probably uses encrypted headers. This behavior is normal and improves privacy — but it also makes diagnostics harder and recovery feasibility more difficult to judge. You can still make high-level checks using visible error messages, archive size, and general structure, but you won’t get the usual per-file clues until the right password is available.
🧠 What Header Encryption Actually Does
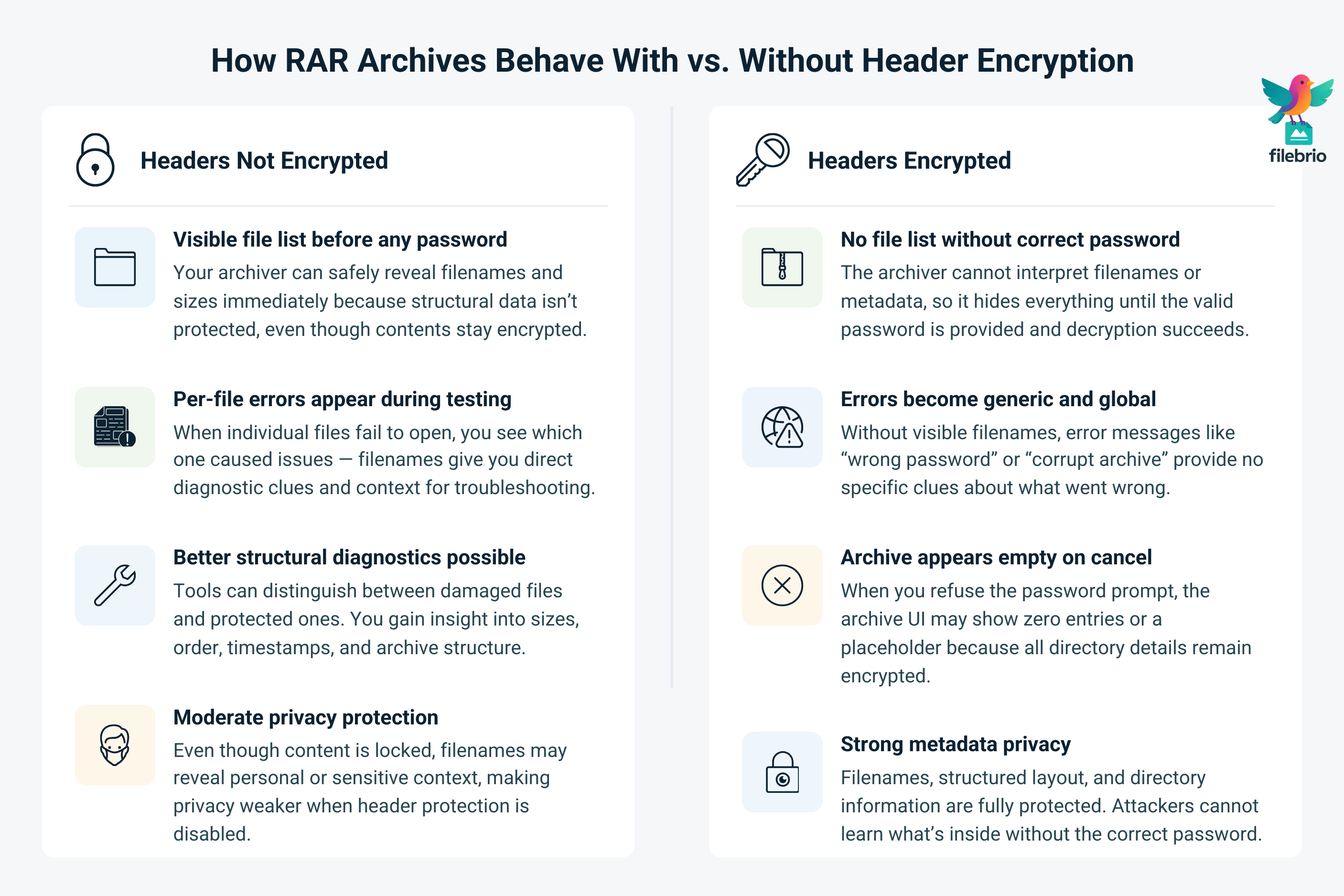
Every RAR archive has structured “directory” information that tells the tool which files exist, where they are stored, and how to decompress them. These structures are known as headers. When headers are not encrypted, your archiver can usually show a file list even if the contents are protected — you see names, sizes, and dates, but can’t open files without a password.
With header encryption enabled, RAR encrypts this directory information as well. Until you provide the correct password, the tool cannot safely interpret filenames or related metadata. The result is that the archive behaves like a “black box”: it may appear almost empty, and you may see only generic prompts or errors.
| Feature | Headers Not Encrypted | Headers Encrypted |
|---|---|---|
| File list before password | Visible (filenames, sizes, timestamps) | Not visible or only meaningless placeholders |
| Ability to see which file fails | Usually yes (per-file errors) | No — errors are global and less specific |
| Privacy of filenames | Moderate (names can leak context) | High (names and structure hidden) |
| Ease of diagnostics without password | Better — more structural clues | Limited — archive looks opaque |
| Risk of casual “snooping” via names | Higher | Lower |
Header encryption is part of RAR’s broader security model. To understand how it interacts with other protection features in RAR4 and RAR5, it helps to look at how RAR4 and RAR5 secure your protected data ↗️, which explains where header protection fits into the overall design.
🔍 Visual Signs Your Archive Uses Header Encryption
You don’t need low-level tools to suspect header encryption. Often, the way your archiver behaves is enough to form a reasonable hypothesis. While every tool’s interface is different, the underlying patterns are similar.
Key Behavioral Clues
- No file list until password: The moment you open the archive, you’re asked for a password and cannot see filenames behind that dialog.
- “Empty” appearance on cancel: If you cancel the password prompt, the archive appears empty or shows no meaningful entries.
- Generic error messages: You may receive “wrong password” or “corrupt archive” errors without per-file details.
These symptoms can overlap with corruption, so it’s helpful to consider them together rather than in isolation. For comparison, another article explains how to tell if your RAR file is locked or damaged ↗️, focusing on differences between encryption and structural faults.
| What You See in Your Archiver | Likely Header State | What It Implies |
|---|---|---|
| File list visible, but extraction asks for password | Headers not encrypted | You get useful diagnostic clues (file names, sizes). |
| Password prompt appears before any file list | Headers may be encrypted | Tool needs password to decode directory structure. |
| After canceling, archive looks empty or has one unclear entry | Headers likely encrypted | Archive hides filenames; tool shows placeholders at best. |
| File list appears but some entries show corruption errors | Headers readable, data may be damaged | Structural damage affects contents, not header visibility. |
| Tool reports “unexpected end of archive” plus no usable file list | Could be both encryption and truncation | Further structure-aware checks are required. |
Remember: behavior is only one piece of the puzzle. You still need to consider archive size, error wording, and context (how the archive was created, whether it was split across volumes, and so on) before drawing conclusions.
🧩All-in-One Solution for Understanding Encrypted RAR Headers
When a RAR archive shows no filenames, keeps asking for a password before revealing anything, or looks almost empty, it’s hard to know whether you’re facing real header encryption or silent damage. That uncertainty is the real pain point: every wrong assumption can push you toward risky experiments on a file that might still be recoverable.
| Typical Situation | Hidden Risk |
|---|---|
| You see a password prompt but no file list. | You can’t tell if it’s header encryption or corruption. |
| The archive looks “almost empty” after canceling the prompt. | You may assume it’s broken and overwrite the only good copy. |
| Different tools show confusing, inconsistent behavior. | You waste time on guesswork instead of structured diagnostics. |
The FileBrio Office Suite — with FileBrio RAR Master at its core — gives you an all-in-one, offline environment to answer these questions safely, without ever uploading your archive:
- Detect header encryption: Understand when filenames and metadata are deliberately hidden, not “missing.”
- Distinguish encryption vs damage: Separate visibility issues from actual structural corruption.
- Format-aware checks: See whether you’re dealing with RAR4 or RAR5 and what that means for diagnostics.
- High-level metadata insights: Inspect size, layout, and structural hints without extracting files.
- One consistent workspace: Stop juggling multiple tools; work in a single, privacy-first interface on your own machine.
Instead of guessing what header encryption is doing to your archive, FileBrio RAR Master helps you see the bigger picture locally and plan safe, realistic next steps.
________________________
FileBrio RAR Master — part of the FileBrio Office Suite — is a privacy-first, offline Windows toolkit for diagnosing and safely regaining access to your own password-protected RAR / WinRAR archives.
- Local processing only — nothing leaves your PC.
- Smart diagnostics to separate password issues from corruption.
- Owner-verified recovery workflows designed strictly for legitimate use.
Reminder: FileBrio RAR Master may be used only with archives you own or are explicitly authorized to access. It performs all analysis and recovery operations locally on your device, without uploading data anywhere.
________________________
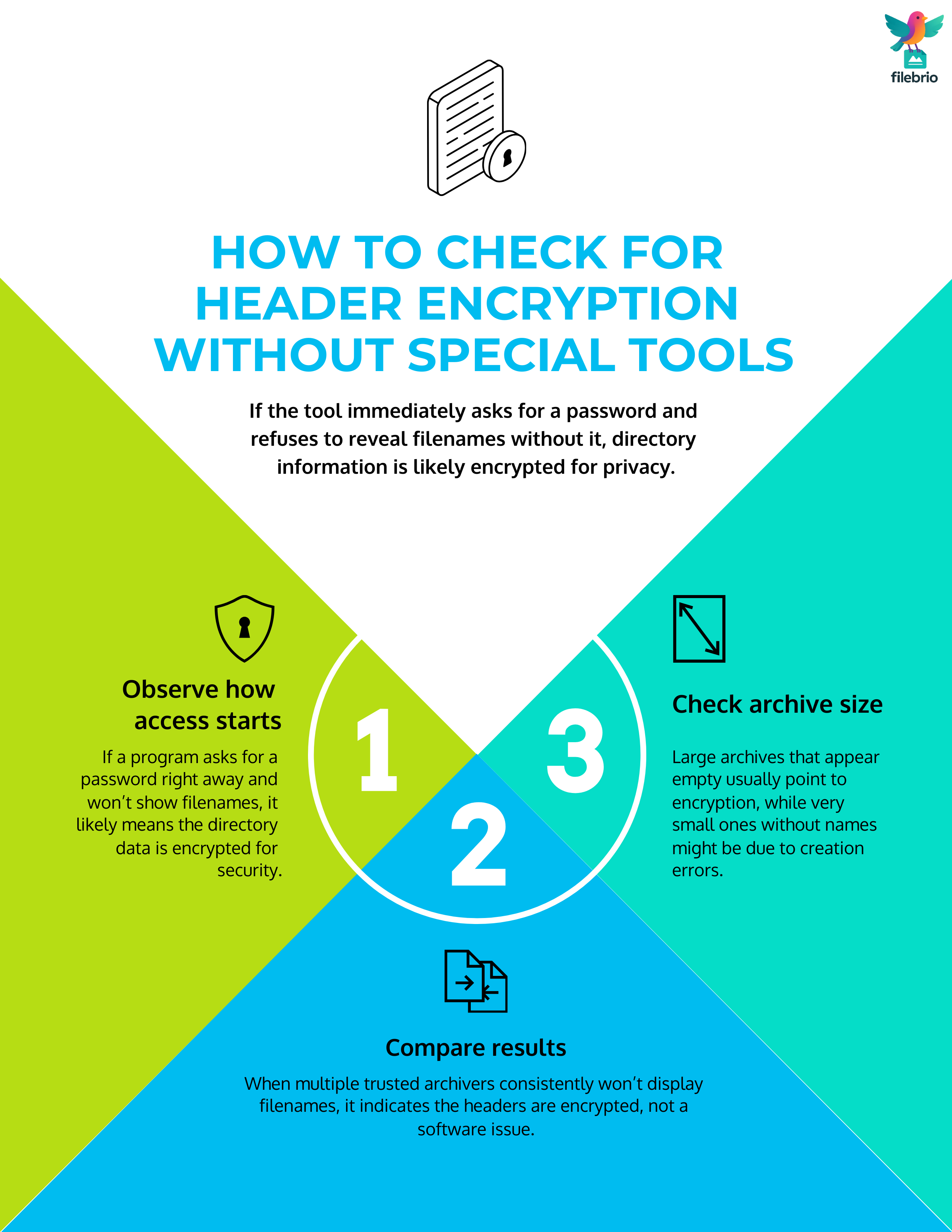
🧪 Simple Ways to Check for Header Encryption Without Extra Tools
Without specialized utilities, you’re essentially relying on what your archiver reveals during everyday actions. The goal is not to “break in,” but to understand which security mode the archive uses so you can set realistic expectations and plan safe next steps.
1. Observe Access Flow Carefully
Open the archive and watch the sequence of events:
- If a detailed file list appears before any password prompt, headers are almost certainly not encrypted.
- If your archiver must ask for a password immediately and will not display filenames otherwise, header encryption is likely active.
- If file names stay unreadable even after you enter what you believe is the correct password, you may be dealing with either wrong credentials or deeper corruption.
When your archive simply “won’t open,” a broader diagnostic approach is helpful. Another guide explains steps to check structure without modifying your protected data ↗️, so you can avoid unnecessary extractions while still gathering clues.
2. Compare Different Tools’ Behavior
Sometimes, using more than one RAR-compatible application (on the same, trusted machine) can clarify what’s going on. If multiple tools all refuse to display filenames until a password is provided, that strengthens the case for header encryption rather than a tool-specific quirk.
| Observation | Interpretation | What to Do Next (High-Level) |
|---|---|---|
| Tool A shows file list, Tool B shows file list | Headers not encrypted | Use visible headers to guide further diagnostics. |
| Tool A and B both show no list until password | Headers likely encrypted | Focus on password recall and feasibility, not previews. |
| Tool A shows names, Tool B fails to read archive | Tool B compatibility/bug issue | Rely on the tool that can clearly read headers. |
| Both tools show severe errors and no meaningful names | Potential corruption plus header protection | Consider non-destructive structure checks and backups. |
For more on using error messages and metadata to understand failures, see how to read metadata clues in your RAR file ↗️, which focuses on what you can safely infer from the limited information available.
3. Consider File Size and Context
Even without technical tools, basic file size and context are informative:
- A multi-gigabyte archive that appears “empty” but still prompts for a password is unlikely to be truly empty; header encryption is a plausible explanation.
- A tiny archive that shows no file list might actually be damaged or miscreated, not intentionally hidden.
- If you remember having enabled options that “hide file names” or “encrypt file list” when creating the archive, that’s a strong hint that header encryption is indeed active.
When you’re unsure whether encryption or damage is to blame, it’s worth revisiting simple checks revealing why your RAR file won’t open ↗️, which walks through common symptoms of both scenarios.
⚙ Technical Background: RAR Formats and Header Flags
From a structural point of view, RAR headers are more than just filenames. They contain flags and metadata that define how the archive behaves, including whether header encryption is enabled. While you might not see these flags directly, understanding that they exist helps make sense of what your tools are doing.
RAR4 vs RAR5 and Header Behavior
RAR4 and RAR5 represent two generations of the format. Both can support header encryption, but RAR5 modernizes many details:
- More robust key derivation and protection of metadata.
- Improved handling of large archives and long file names.
- More explicit flagging of security-related features in headers.
These design choices are part of why RAR5 archives may appear more “opaque” when headers are encrypted — there’s simply less leftover information that can be interpreted without the right key. A broader overview is available in how RAR5 improves protection of your encrypted files ↗️, which explains what stronger RAR5 security means for data access.
Header Flags and What They Can Reveal
Internally, RAR uses flags to indicate whether certain protections are turned on. While a typical end user may not inspect these fields directly, many tools interpret them to decide whether a file list can be shown.
- When a “header encrypted” flag is set, the tool knows not to trust header data without a password.
- When no such flag is set, the tool may safely display filenames even if contents are still protected.
- Other flags might indicate solid compression, recovery records, or multi-volume structures.
If you ever work with software that exposes header details in a readable way, how header flags reflect your RAR file’s health ↗️ can help you interpret those signals responsibly, without going into low-level or attack-focused territory.
Recovery Records, .rev Volumes, and Header Protection
It’s also common for archives with encrypted headers to include recovery records or .rev volumes to guard against damage. While these features don’t remove the need for a correct password, they can improve your chances of restoring structural integrity if corruption occurs later.
To understand how these pieces fit together, you may find it useful to read more about how recovery records safeguard your damaged RAR files ↗️, which explains how redundancy supports archive health when trouble appears.
🔐 Secure Offline Solution for Sensitive, Header-Encrypted Archives
Once you realize that headers are encrypted and filenames are intentionally hidden, the next question is how to investigate safely. Many users are tempted to upload the archive to online “unlocker” or “preview” sites just to see whether anything can be listed — but header encryption means those services cannot see more than your local tools, while still copying your sensitive data to someone else’s server.
| Risky Approach | Safer Offline Alternative |
|---|---|
| Uploading private archives to unknown websites. | Keep all diagnostics inside FileBrio RAR Master on your own device. |
| Trying random tools that rewrite the only copy. | Use read-focused, structure-aware checks before any repair attempts. |
| Guessing blind when filenames are hidden. | Let header-aware analysis confirm what is actually protected and how. |
FileBrio RAR Master, as part of the FileBrio Office Suite, is designed for exactly this privacy-critical scenario:
- 100% offline workflow: No cloud components, no background uploads, no external servers.
- Header-aware diagnostics: Identify when header encryption is active and what that implies for visibility and feasibility.
- Structure and integrity analysis: Review archive size, layout, recovery records, and multi-volume design without risky modifications.
- Format intelligence: Understand how RAR4 vs RAR5, recovery records, and .rev volumes affect your repair and access options.
- Recovery planning, not guesswork: Use clear, high-level insights to decide when password-focused steps make sense and when you should focus on preservation.
For archives that must never leave your environment, FileBrio RAR Master offers a secure, offline path to understanding what header encryption is doing — and how to move forward without compromising privacy.
________________________
FileBrio RAR Master — a secure, offline Windows toolkit for regaining access to your own password-protected RAR / WinRAR archives while keeping all data strictly on your device.
- Offline-only processing — never uploads your archives.
- Smart issue detection — password vs corruption.
- Fast recovery workflow optimized for legitimate ownership.
⬇️ Download FileBrio RAR Master
Reminder: FileBrio RAR Master is intended only for archives you own or are explicitly authorized to access. All operations run locally on your PC.
________________________
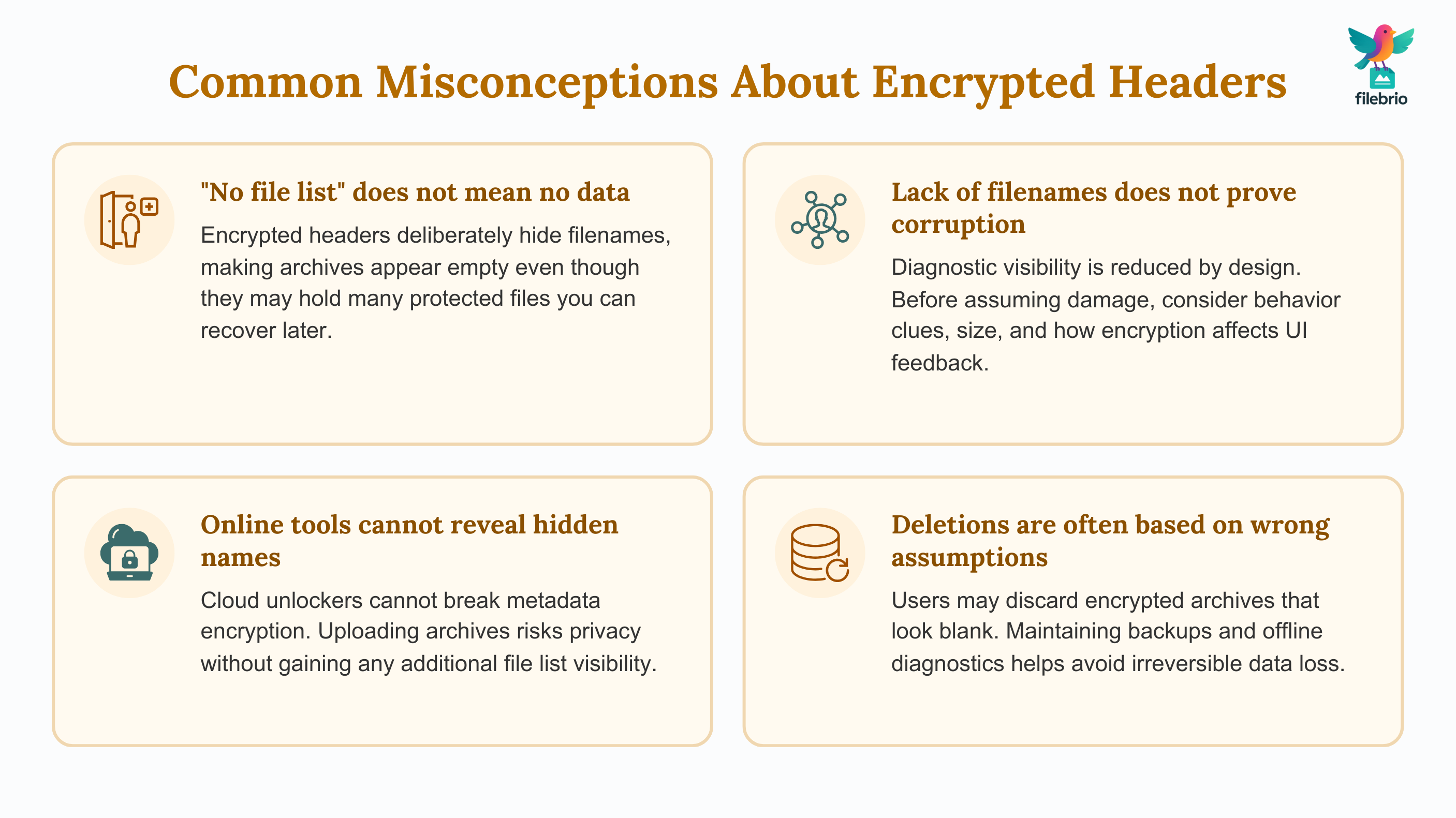
🧰 Common Pitfalls and Misconceptions About Encrypted Headers
Because header encryption changes how archives “look” on the surface, it’s easy to misinterpret the symptoms and draw the wrong conclusions. Here are some common pitfalls to avoid.
“The Archive Must Be Empty — I See No Files”
When headers are encrypted, “no file list” does not mean the archive is empty. It usually means the directory information is hidden until you provide the correct password. Interpreting apparent emptiness as real emptiness can lead to careless deletion of valuable data.
“If It Shows No Names, It Must Be Corrupted”
Corruption is certainly possible, but header encryption alone can explain the absence of a file list. Before you assume damage, look at the full combination of clues: archive size, error wording, whether prompts appear, and how different tools behave.
If your RAR archive really is locked and behaving strangely, it’s wise to follow how to safely diagnose your locked RAR file ↗️, which emphasizes non-destructive checks that avoid making a bad situation worse.
“Online Tools Will Show Me the Hidden File List”
Uploading a sensitive archive to a random website in hopes of “revealing” filenames is almost always a bad idea. Header encryption is designed so that even a remote tool cannot see filenames without the correct password — and now your protected archive has left your control.
Keeping diagnostics local, within your own environment, is one of the safest choices you can make. For an overview of the legal and compliance aspects, see legal factors when accessing your encrypted RAR files ↗️, which focuses on lawful handling of protected data.
📈 Planning Ahead: Passwords, Metadata, and Long-Term Access
Header encryption protects your privacy today, but you also need a plan to ensure future you (or your organization) can still open important archives years from now. That means thinking beyond “Is this protected?” to “Can we still access this in a controlled, documented way?”
Store Password Metadata Safely
Because filenames are hidden, you get fewer reminders about what an archive contains. Without context, it’s easier to misplace or forget the correct password. That’s where well-structured, secure metadata becomes critical — not storing the password itself in plain text, but capturing the kind of cues that help you or your team remember how access was managed.
For practical ideas, you can look at how to organize metadata for your RAR passwords safely ↗️, which covers ways to keep long-term access without exposing secrets.
Balance Strong Security With Future Usability
Header encryption is a strong protection measure, but it should fit into a broader strategy that avoids self-lockout. That strategy includes:
- Using realistic password policies for archives that must stay accessible for many years.
- Avoiding unnecessary duplication of ultra-sensitive, opaque archives.
- Documenting how and why header encryption was enabled for critical sets of files.
Broader strategies for staying safe without losing access are explored in how to reinforce protection of your encrypted RAR files ↗️, which focuses on aligning security settings with long-term needs.
Protect the Archive Itself From Data Loss
Header encryption doesn’t protect against physical damage, bit rot, or failing storage. If the only copy of your archive lives on an old USB stick or unmonitored HDD, you may lose it long before encryption becomes the limiting factor.
Useful habits for storage and backups are discussed in ways to prevent losing your RAR data on storage devices ↗️, which highlights everyday mistakes that can quietly destroy otherwise well-protected archives.
Clarify Ownership and Authorization
Finally, make sure it’s always clear who is allowed to work with a given encrypted archive. This matters both for compliance and for internal clarity — especially in teams and enterprises.
- Document which person or role controls each critical archive.
- Make sure access attempts are consistent with that ownership.
- Keep a record of when and why header encryption is used for especially sensitive sets of files.
Practical guidance on this front can be found in how to verify ownership before accessing your RAR file ↗️, which focuses on making sure your recovery efforts stay firmly within legitimate boundaries.
📜 Legal Reminder
This article is provided for general informational and educational purposes only. Any examples, scenarios, or references to password recovery, archive security, or related tools (including FileBrio RAR Master or similar software) are intended solely to help you better understand how to protect and manage your own data.
You may only apply any techniques, workflows, or tools described here to files and archives that you fully own or are explicitly and verifiably authorized to access. Attempting to bypass, remove, or recover passwords for third-party data without clear permission may violate criminal law, civil law, or internal company policies in your jurisdiction.
Nothing in this article constitutes legal advice. Laws and regulations differ between countries and organizations, and you are solely responsible for ensuring that your actions comply with all applicable legislation, contracts, and internal policies. If you are unsure whether a particular action is lawful or permitted, consult a qualified legal professional before proceeding.
🔗 See Also — Related Guides
- Why Encrypted Headers Make Content Discovery Impossible — and What That Implies for Recovery ↗️
- How RAR Header Encryption Affects Recovery Feasibility and What Clues It Still Reveals ↗️
- How to Determine If a RAR Archive Uses Header Encryption ↗️
- What RAR5 Quick Open Records and Recovery Blocks Do (High-Level Guide) ↗️
- RAR Recovery Records and .rev Volumes: How They Help Protect and Restore Data ↗️
- How to Check the Internal Structure of RAR Archives Without Extracting Files ↗️
- RAR/WinRAR File Passwords Explained: How Encrypted Archives Work and What Access Options You Have ↗️