What to Try Before Considering Any Password Guessing on Your Own RAR File
You have a RAR archive that definitely belongs to you, you’re sure the password is “somewhere in your head,” and yet every attempt fails. It’s tempting to jump straight into aggressive password guessing, install the first “magic unlocker” you find online, or fire up a GPU and hope for the best.
But before you do anything that might waste days of time or risk damaging the only copy of important data, there’s a safer route: a structured sequence of checks that tell you whether guessing even makes sense, how risky it would be, and what you can learn from the archive itself first.
This article walks through those preliminary steps: diagnostics, metadata review, archive health checks, feasibility assessment, and long-term protection. It’s designed only for archives you fully own and have a legitimate right to access. Throughout the guide, we’ll also reference related FileBrio RAR knowledge-base articles so you can dig deeper into specific topics when needed.
🧭 Navigation
Important
The information provided in this article applies exclusively to RAR / WinRAR archives for which you have full, demonstrable ownership or properly documented authorization. If you are not the rightful owner of the data, do not directly control it, or cannot clearly prove permission to access it, you must stop immediately. Attempting to access, recover, or modify data without explicit authorization may violate criminal law, civil statutes, corporate compliance requirements, and privacy regulations in many jurisdictions. You alone are responsible for ensuring that your actions are lawful and properly permitted before proceeding.
📝 TL;DR — Why You Shouldn’t Start With Guessing
Before you type a single guess into your own RAR file, you should know whether guessing is even the right move. Many users assume “wrong password” is the only explanation when a RAR archive won’t open, but in reality the problem might be corruption, a format mismatch, missing volumes, or a subtle issue like keyboard layout or encoding. If you start hammering passwords into a fragile archive, you won’t fix any of those issues—you’ll just burn time and possibly misinterpret what the software is telling you.
A safer approach starts with diagnostics. First, make a copy of the archive and work only on that duplicate. Then run basic checks: confirm that the file extension and tool version match (RAR4 vs RAR5), check that all volumes are present, and carefully read any error messages instead of clicking them away. Next, examine metadata and structural signals: whether the archive is encrypted, whether headers are visible, and whether integrity tests report damage. These clues tell you whether the archive is technically recoverable and whether a password is truly the barrier—or just one symptom.
Only after these checks should you consider whether password guessing makes sense. At that point, focus on feasibility—length, complexity, uniqueness, and your own memory clues—rather than random attempts. In parallel, prefer privacy-safe, offline tools and avoid uploading sensitive archives to unknown websites. Finally, use this situation as a trigger to improve your password hygiene, documentation, and long-term access planning so you won’t be stuck in the same situation again.
🧩 Before You Think About Guessing: Mindset & Scope
The first step is mental, not technical. Password guessing feels like “doing something,” so it’s emotionally attractive when you’re locked out of your own data. But without preparation, guessing is often:
- Inefficient — you may be attacking the wrong problem entirely.
- Risky for privacy — especially if you upload sensitive archives to online services.
- Misleading — repeated failures can make you think “this password is impossible,” when the true issue is corruption or missing parts.
This guide assumes one strict condition: you are working only with RAR/WinRAR archives that you fully own and are legally entitled to access. If the archive was sent to you, belongs to your employer, or comes from a shared environment, you may need formal authorization before attempting any recovery work. For personal archives, you still need to approach recovery responsibly and carefully.
If you’ve recently realized you no longer remember a password you once knew, it can be useful to step back and review safe ways to approach your forgotten RAR password ↗️ before diving into anything more aggressive. That high-level reflection often clarifies whether guessing is even appropriate, or whether you need a different path entirely (for example, finding an older, unencrypted backup).
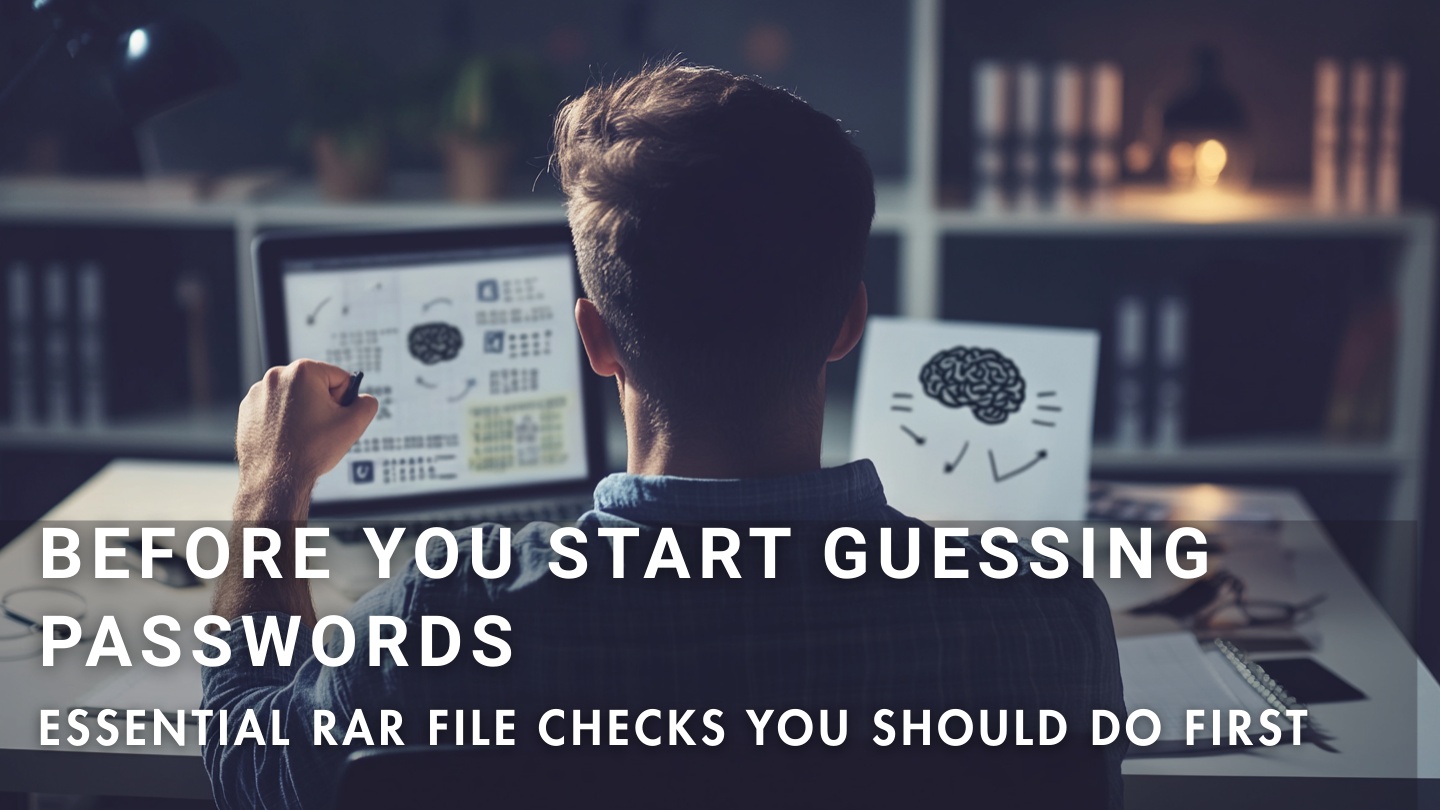
🔍 Step 1: Basic Non-Destructive Checks
Before touching anything else, focus on checks that cannot damage your archive. Your goal is to confirm that the situation is truly “wrong password on a healthy file,” not something else.
1. Work on a copy, never on the only original. Move the original RAR file to a safe location and create a duplicate to experiment on. That copy becomes your “lab sample”; the original remains untouched in case something goes wrong, the disk starts failing, or you later discover better tools.
2. Confirm you’re opening the right file in the right tool. It sounds trivial, but it’s surprisingly common to:
- Try to open a partially downloaded archive.
- Use an older tool that struggles with newer RAR5 features.
- Confuse a similarly named archive (e.g., “backup-final.rar” vs “backup-final-v2.rar”).
Make sure the file is fully copied, the extension is correct, and your software understands both RAR4 and RAR5.
3. Observe behavior when you enter no password at all. If the archive demands a password and immediately fails even when you press OK with an empty field, that’s a different pattern from a file that lets you see filenames but shows errors halfway through extraction. These subtle patterns are covered in more detail in ways to diagnose your unopened RAR file issue ↗️.
4. Re-check keyboard layout and input quirks. If you created the password on a different keyboard layout, with Caps Lock enabled, or using a password manager that auto-filled differently in the past, you may be reproducing the wrong keystrokes now. Small differences in character encoding or layout can make your “correct” password wrong in practice. A careful, slow re-entry is worth more than dozens of rushed guesses.
For a structured overview of non-destructive checks and safe handling principles, see how to safely diagnose your locked RAR file ↗️. Those steps help you avoid taking any action that could worsen corruption or confuse the diagnostic signals the archive is already giving you.
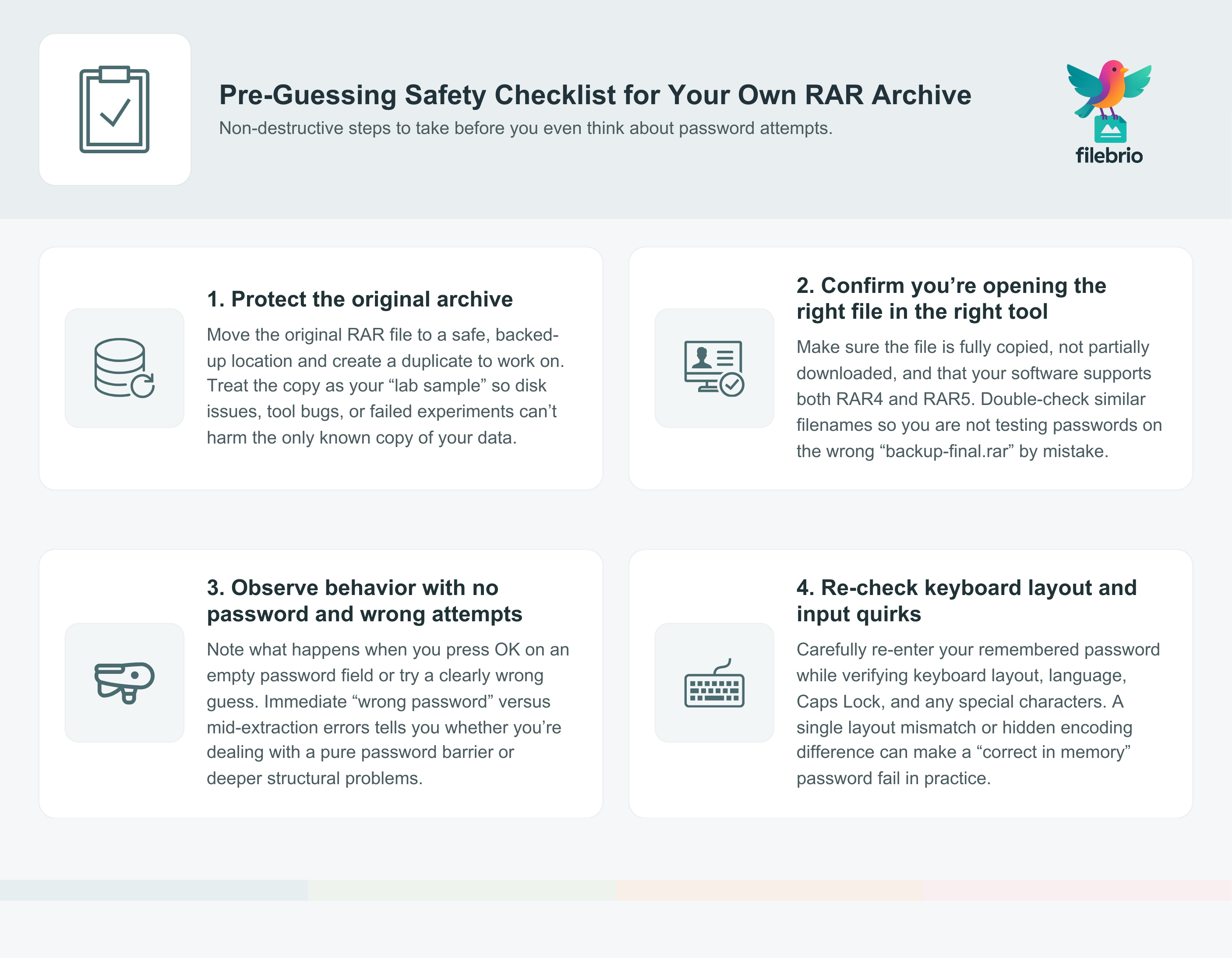
🧾 Step 2: Messages, Metadata, and Context
Once you’ve done the basic checks, shift your attention to the exact feedback the archive and tool are providing. Error messages, header flags, and archive metadata are valuable signals—if you know how to read them.
1. Don’t ignore error messages. Many users instinctively click “OK” on every dialog just to get past it. Instead, read the exact wording, timing, and context of each message. There’s a big difference between:
- “Wrong password” shown immediately after you enter a value, and
- “Unexpected end of archive” or “Checksum error” appearing halfway through extraction.
The first hints at a pure password issue; the second suggests structural damage or missing data. A more detailed breakdown of common messages is available in how to interpret error messages from your RAR file ↗️.
2. Look at archive metadata, not just the UI. Tools that can expose metadata—format version, compression method, flags for encryption, recovery records, and so on—tell you whether the archive is structurally sound. If the metadata looks inconsistent, if sizes are obviously wrong, or if certain headers are missing, password guessing will not fix those deeper issues. To learn what these clues mean, see how to read metadata clues in your RAR file ↗️.
3. Consider the context in which the archive was created. Ask yourself:
- Did you create this archive on a different machine or operating system?
- Did you enable special features like filename or header encryption?
- Have you ever successfully opened this archive before?
These answers affect how you interpret the metadata. For example, an archive you’ve never once opened successfully might have been corrupted at creation time. In that scenario, even a perfect password won’t help. For guidance on deciding whether an archive is still viable at all, review how to verify recoverability of your locked RAR file ↗️.
🧱 Step 3: Validating Archive Structure Safely
At this stage, you want to know whether the archive is internally coherent. That doesn’t mean you have to extract the contents; it means you run tools and tests that examine the archive’s structure from the outside.
1. Inspect the internal layout without extraction. Some tools allow you to analyze the archive’s internal structure—block headers, flags, and basic consistency—without touching the payload data. This can reveal whether the file is truncated, has unexpected gaps, or contains the right number of entries. How to inspect internal layout of your RAR file safely ↗️ explains how these structure-only checks reduce risk while giving you valuable diagnostics.
2. Check for recovery records and .rev volumes. If the archive was created with recovery records, or if you have separate .rev volumes, your situation may be better than it looks. Those features can reconstruct certain types of damage or missing segments, making it worthwhile to repair the archive before you think about password guessing. For a conceptual overview of these mechanisms, see:
- how recovery records safeguard your damaged RAR files ↗️
- how .rev files rebuild missing parts of your RAR archive ↗️
3. Consider quick open records and RAR5 structures. Modern RAR5 archives may include quick open records and recovery blocks that influence how quickly and safely the archive can be scanned. If these structures are missing or inconsistent, the file may be more fragile than you expect. A high-level explanation of these features is given in how quick open records enhance your protected RAR file ↗️.
By the time you’ve reached this point, you should have a clear picture: is the archive structurally sound and clearly password-protected, or does it show signs of corruption, truncation, or missing volumes? Only in the first case is password guessing even on the table as a rational next step.
💼 One Suite to Centralize Safe RAR Diagnostics
By now, you’ve seen how many different pieces of information you should gather before guessing: error messages, header flags, structure checks, recovery records, and more. Doing all of this across multiple tools and command-line utilities can be confusing and error-prone—especially when you’re already stressed about possible data loss.
Instead of juggling separate utilities, many users prefer an integrated toolkit that focuses on offline diagnostics and recovery for their own archives. A consolidated environment makes it easier to:
- Run structural checks and integrity tests on a copy of the archive.
- See format details (RAR4 vs RAR5, encryption flags, recovery records) in one place.
- Evaluate repair options before deciding whether guessing is worthwhile.
- Keep all operations local, on your own machine, without uploading sensitive data.
If you want to understand what an all-in-one toolkit can do in this space, the RAR Master full feature list ↗️ shows how diagnostics, repair options, and responsible recovery capabilities can live together in a privacy-first desktop environment. It also compares favorably to risky web services in terms of control and transparency, as discussed in why offline recovery is safer ↗️.
________________________
FileBrio RAR Master — part of the FileBrio Office Suite — is a privacy-first, offline Windows toolkit for diagnosing and safely regaining access to your own password-protected RAR / WinRAR archives.
- Local processing only — nothing leaves your PC.
- Smart diagnostics to separate password issues from corruption.
- Owner-verified recovery workflows designed strictly for legitimate use.
Reminder: FileBrio RAR Master may be used only with archives you own or are explicitly authorized to access. It performs all analysis and recovery operations locally on your device, without uploading data anywhere.
________________________
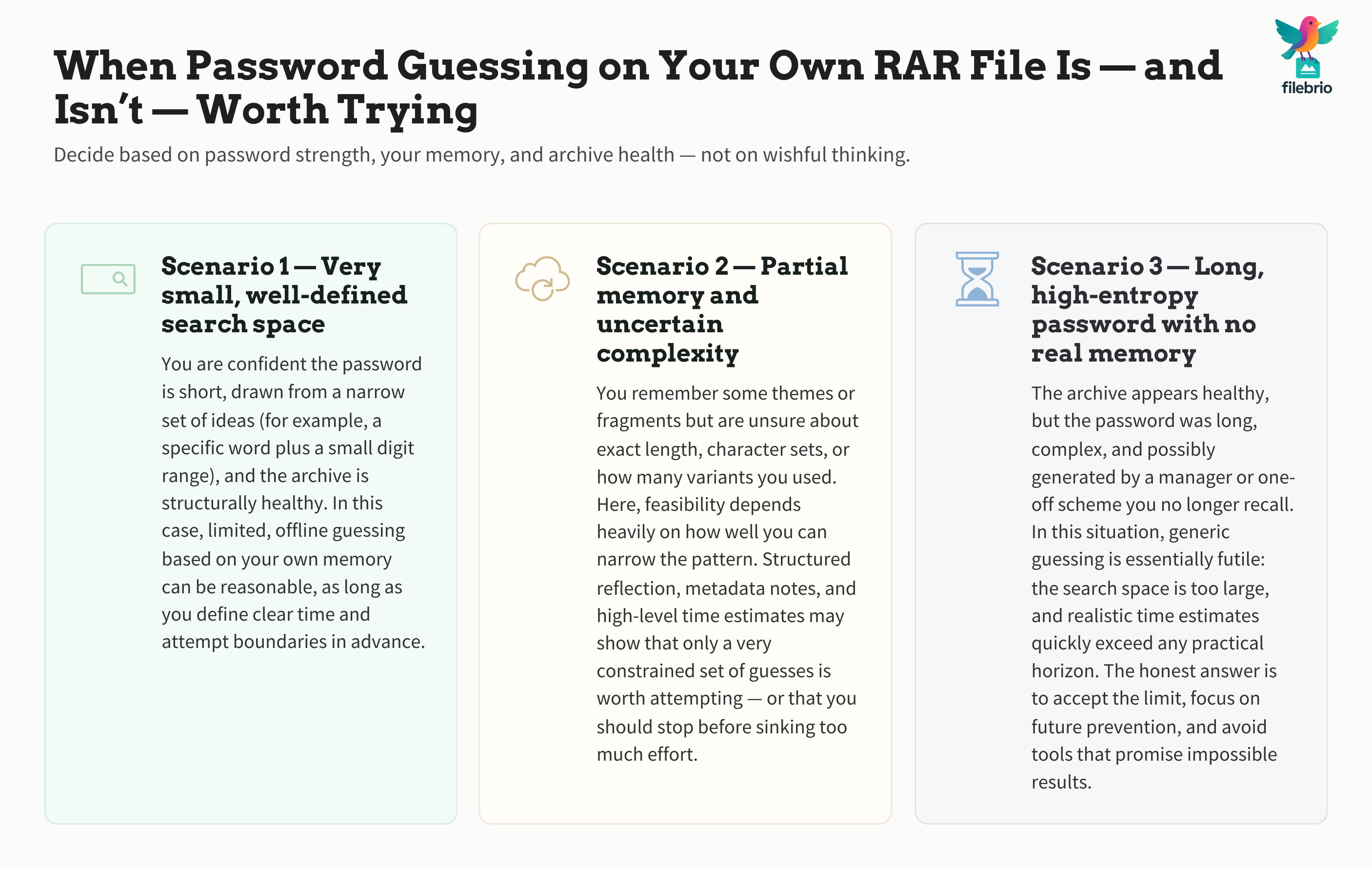
⚙️ Step 4: Evaluate Feasibility Instead of Guessing Blindly
Suppose your diagnostic work shows a healthy, encrypted archive with no structural defects. Now the question becomes: is password guessing actually viable for this file? The answer depends on the password’s length, complexity, and how much real information you still remember about it.
1. Length and entropy matter far more than you think. A short numeric password might be feasible to recover; a long, random string drawn from a password manager is effectively a brick wall. The relationship between length, character set size, and guessing complexity is explained conceptually in how length impacts protection of your RAR password ↗️. The takeaway: once passwords cross certain size and randomness thresholds, generic guessing approaches are no longer realistic.
2. Memory clues vs. total amnesia. There’s a big difference between “I vaguely remember the idea behind this password” and “I have no idea what I used.” In the first case, structured reflection and narrowing the search space might help. In the second, random guessing is almost always futile. For borderline cases, it’s worth reading about how to judge feasibility of your forgotten RAR password ↗️ before you commit time and energy.
3. Work with high-level time estimates, not promises. Rough, high-level estimates of how long certain search spaces would take—at different speeds and hardware capabilities—can help you decide whether a strategy is worth attempting at all. A conceptual guide is available in the article on password strength and time-to-crack estimation ↗️, which focuses on understanding ranges rather than offering unrealistic guarantees.
The key idea is simple: do not start guessing until you’ve convinced yourself that the search space is realistically bounded and that your remaining memory of the password is rich enough to narrow down possibilities. Otherwise, you’ll simply be staring at a progress bar that never brings you closer to an answer.
🛡️ Protect Yourself While You Experiment
If, after all this, you still decide to perform limited password experiments on your own archive, you should do so in a way that protects both your data and your privacy.
1. Always test on a copy. This cannot be repeated enough. Hardware issues, sudden power loss, or software bugs should never threaten your only copy of important data. Keeping the original read-only and working on a duplicate is a simple but powerful safeguard.
2. Avoid online tools for sensitive archives. Uploading an encrypted archive to an unknown website may expose the data to long-term retention or analysis, even if the service claims otherwise. For personal archives containing private documents, photos, or business records, it’s usually much safer to keep everything local. The privacy advantages of local tools are discussed in why offline tools keep your encrypted RAR data private ↗️.
3. Limit the scope and duration of any guessing attempts. If you decide to run a constrained search based on strong prior knowledge (for example, a narrow set of variants of a known phrase), define clear boundaries in advance: how many attempts, how long, and when you will stop. Treat this as an experiment, not a guarantee.
4. Keep a record of what you tried. Note which passwords, variants, and approaches you’ve already tested. This avoids repeating the same attempts and gives you a history you can revisit later if you discover new clues about your original password.
🧪 A Secure Offline Environment for Careful Experiments
Even when you act carefully, coordinating diagnostics, structural checks, and controlled experiments can be overwhelming if you’re switching between multiple tools and interfaces. A dedicated, offline environment can make this process more manageable and less error-prone.
In an ideal workflow, your toolkit should:
- Analyze archive metadata and structure before you touch any password settings.
- Highlight corruption, missing volumes, or header issues early, so you don’t waste time.
- Offer clearly separated modes for diagnostics, repair, and legitimate password recovery work.
- Keep all operations on your own machine, with no background uploads or remote processing.
Having these capabilities in one place helps you make rational decisions about whether to continue, pause, or change direction. And when you’re ready to install such a toolkit, you can get FileBrio RAR Master and related tools from the official download page ↗️, ensuring the software comes from a trusted, verifiable source rather than an unvetted mirror.
________________________
FileBrio RAR Master — a secure, offline Windows toolkit for regaining access to your own password-protected RAR / WinRAR archives while keeping all data strictly on your device.
- Offline-only processing — never uploads your archives.
- Smart issue detection — password vs corruption.
- Fast recovery workflow optimized for legitimate ownership.
⬇️ Download FileBrio RAR Master
Reminder: FileBrio RAR Master is intended only for archives you own or are explicitly authorized to access. All operations run locally on your PC.
________________________
🧬 Long-Term Protection: Avoid Needing Guessing Next Time
Every difficult recovery situation is also an opportunity to improve how you handle encrypted archives in the future. The goal is simple: make your RAR protection strong, but avoid locking yourself out.
1. Use strong yet memorable password strategies. Instead of short, weak passwords, design structures that are long and complex but still tied to stable, personal associations you won’t forget. The article on how to design strong memorable RAR passwords ↗️ explains how to balance security with recall, so you reduce the chance of future lockouts.
2. Store metadata and hints safely. You don’t need to store the password itself in plain text, but you can keep structured hints and context that will help “future you” if you forget details. For personal use, see how to organize metadata for your RAR passwords safely ↗️. This kind of metadata can drastically reduce the need for guessing years later.
3. Strengthen security without destroying future access. Strong encryption is essential, but you can combine it with good backup practices and documented procedures so that you—and only you—can regain access when needed. High-level guidance on this balance is available in how to reinforce protection of your encrypted RAR files while preserving future access ↗️.
4. Build habits that prevent future “forgotten password” emergencies. Recurrent routines, such as updating a secure password manager when you create or change an archive password, can dramatically reduce the risk of being forced into complex recovery efforts later on.
👔 When to Contact Professionals or Your IT/Security Team
There are situations where it’s safer—legally and practically—to bring in additional help instead of acting alone.
1. Corporate or shared archives. If the RAR file belongs to your employer, a client, or a shared project, you may need to prove you’re authorized to access it. In these cases, audit trails and documentation matter. Guidance on this topic is provided in ways to document ownership of your encrypted RAR file in corporate environments ↗️, which can help you work with internal security or compliance teams.
2. Long-term retention and team access. For teams and enterprises, the problem is not just “today’s password” but continued access over years and role changes. Planning for that is covered in how teams can preserve long-term access to encrypted RAR files ↗️.
3. When you need official support and clear legal framing. If you’re unsure whether a particular approach fits within your organization’s policies, or you need clarity about responsible use, your best option is to consult official documentation and support channels that explicitly frame recovery within legal and ethical boundaries. For example, the legal and responsible use policy ↗️ for FileBrio tools outlines how the software is intended to be used and how support can help you stay within appropriate limits.
⚖️ Legal & Ethical Reminder
This article is provided for general informational and educational purposes only. Any examples, scenarios, or references to password recovery, archive security, or related tools (including FileBrio RAR Master or similar software) are intended solely to help you better understand how to protect and manage your own data.
You may only apply any techniques, workflows, or tools described here to files and archives that you fully own or are explicitly and verifiably authorized to access. Attempting to bypass, remove, or recover passwords for third-party data without clear permission may violate criminal law, civil law, or internal company policies in your jurisdiction.
Nothing in this article constitutes legal advice. Laws and regulations differ between countries and organizations, and you are solely responsible for ensuring that your actions comply with all applicable legislation, contracts, and internal policies. If you are unsure whether a particular action is lawful or permitted, consult a qualified legal professional before proceeding.
📚 See Also: Further Reading
- What to Try Before Considering Any Password Guessing on Your Own RAR File ↗️
- How to Diagnose a Locked RAR Archive Without Risking Data Loss ↗️
- How to Confirm Whether Your RAR Archive Is Still Technically Recoverable ↗️
- When It Makes Sense to Attempt Password Recovery — and When the Archive Is Mathematically Unopenable ↗️
- How Password Length and Entropy Affect Guessing Complexity ↗️
- Why Offline Recovery Tools Are Safer for Privacy ↗️
- Forgot Your RAR Password? Practical Ways to Regain Access to Your Own Archive ↗️