Using Memory Cues to Analyze Your Password Creation Style (Without Guessing the Password Itself)
When you can’t open a RAR archive you legitimately own, it’s tempting to start hammering random guesses into the password box. But there’s a safer and far more intelligent approach: step back and analyze how you usually create passwords. Instead of trying to “crack” the password, you examine your own habits, mental shortcuts, and memory cues. That analysis won’t magically reveal the exact secret, but it can tell you whether recovery is realistically possible and how you should design passwords in the future so you don’t end up locked out again.
This article focuses on psychology and behavior, not on technical guessing strategies. You’ll learn how your brain builds password patterns, how to use memory cues to sketch a “map” of your password style, and how that map helps you make rational, safe decisions about your own encrypted RAR archives.
🧭 Navigation
⚡ TL;DR — What This Article Helps You Do (And Not Do)
This article does not teach you how to guess or derive a specific password. Instead, it helps you understand your own password creation style using memory cues, behavior patterns, and context. By mapping your habits, you can decide whether recovery of a forgotten RAR password is realistically possible, avoid dangerous or pointless “guessing sprees,” and design future passwords that are both strong and memorable, with safer metadata and documentation.
🧠 Memory Cues vs. Blind Guessing
Most people approach a forgotten password as a random guessing problem: sit at the keyboard, try everything that “feels right,” and hope you trip over the correct combination. From a security and practicality standpoint, that method is usually ineffective and emotionally exhausting.
A safer alternative is to think in terms of memory cues. Memory cues are prompts that help your brain retrieve patterns: where you were, what you were working on, which language you used, whether you added digits at the end, and so on. Instead of “guessing,” you’re building a high-level model of how you typically construct passwords.
If you want to understand why passwords vanish in the first place, it helps to start with behavioral clues linked to your forgotten RAR password ↗️. That guide explains how stress, rare usage, and shifting habits cause even important passwords to fade.
🧩 How Your Brain Builds Password Patterns
Human brains are pattern machines. Even when you think you’re being random, you typically follow unconscious rules. For example:
- Preferring certain starting letters or digits.
- Using a favorite word or theme with variations.
- Repeating structure:
Word + digits + symbol. - Switching between languages or keyboard layouts in a consistent way.
These patterns—your password creation style—emerge over time and across many services, not just RAR archives. The goal of this article is to help you recognize those patterns without ever trying to reverse-engineer a particular password character by character.
| Element | Examples of Style | Why It Matters |
|---|---|---|
| Base words | Pet names, project nicknames, locations, hobbies. | Shows what your brain considers “memorable” without writing secrets down. |
| Modifiers | Year, month, exclamation marks, “+” or “_”. | Reveals how you make passwords feel “strong” in your own mind. |
| Length preference | Short (8–10), medium (12–16), long (20+). | Affects how realistic any future recovery attempt would be. |
| Character set | Letters only, letters + digits, mixed symbols. | Influences overall complexity and guessing difficulty. |
These elements tie directly into security properties such as length and complexity. A separate, high-level explanation in how length impacts protection of your RAR password ↗️ describes why modest changes in length and variety can dramatically increase the number of possible combinations your brain might have chosen.

🧠 A Smarter, Safer Way to Understand Your Locked RAR Archive
When you’re dealing with a forgotten RAR password, it’s easy to feel stuck between two bad options: guessing blindly or doing nothing.
But most of the time, what you actually need is clarity — whether your archive is healthy, partially encrypted, damaged, or fully reliant on the password for access.
FileBrio RAR Master helps you approach the situation calmly and intelligently by giving you offline insight into what your archive is doing behind the scenes — without touching the password or risking further damage.
- 🔍 Identifies whether your archive is locked, corrupted, or misread
- 📁 Shows structural issues without extracting anything
- 🛠️ Separates password problems from archive damage
- 🧩 Understands encrypted headers and how they affect visibility
- 🖥️ Runs 100% offline — nothing is uploaded anywhere
| What You Usually See | What FileBrio Helps You Understand |
|---|---|
| “Wrong password?” | Whether the archive is actually damaged or its headers are encrypted |
| No file list showing | If this is corruption or an encrypted-header design |
| Archive refusing to open | Metadata issues vs. password-related barriers |
Before you waste hours guessing blindly, get a clear, offline picture of what’s actually happening inside your archive:
________________________
FileBrio RAR Master — part of the FileBrio Office Suite — is a privacy-first, offline Windows toolkit for diagnosing and safely regaining access to your own password-protected RAR / WinRAR archives.
- Local processing only — nothing leaves your PC.
- Smart diagnostics to separate password issues from corruption.
- Owner-verified recovery workflows designed strictly for legitimate use.
Reminder: FileBrio RAR Master may be used only with archives you own or are explicitly authorized to access. It performs all analysis and recovery operations locally on your device, without uploading data anywhere.
________________________
🔎 Mapping Your Password Creation Style Safely
To analyze your style without veering into unsafe territory, treat this as an introspective exercise—more like journaling than “cracking.” You’re answering questions about habits, not proposing specific guesses to your archive.
Key areas to explore include:
- Language and alphabet: Do you usually use one language or mix several? Do you rely on Latin characters only, or other scripts as well?
- Capitalization: Do you habitually capitalize the first letter, alternate capitalization, or avoid it?
- Numbers: Are digits usually years, birthdays, milestones, or random sequences?
- Symbols: Do you use them sparingly at the end, or woven into the middle?
A dedicated guide on behavioral clues linked to your forgotten RAR password ↗️ pairs nicely here: it helps you see not just what you choose, but why you felt those choices were “strong” at the time.
Crucially, your goal is to end up with a descriptive profile such as “I usually take a meaningful word, add a year and a symbol, and occasionally replace letters with digits.” That profile is valuable for evaluating feasibility and planning future passwords, even if it never leads you to the exact missing string.
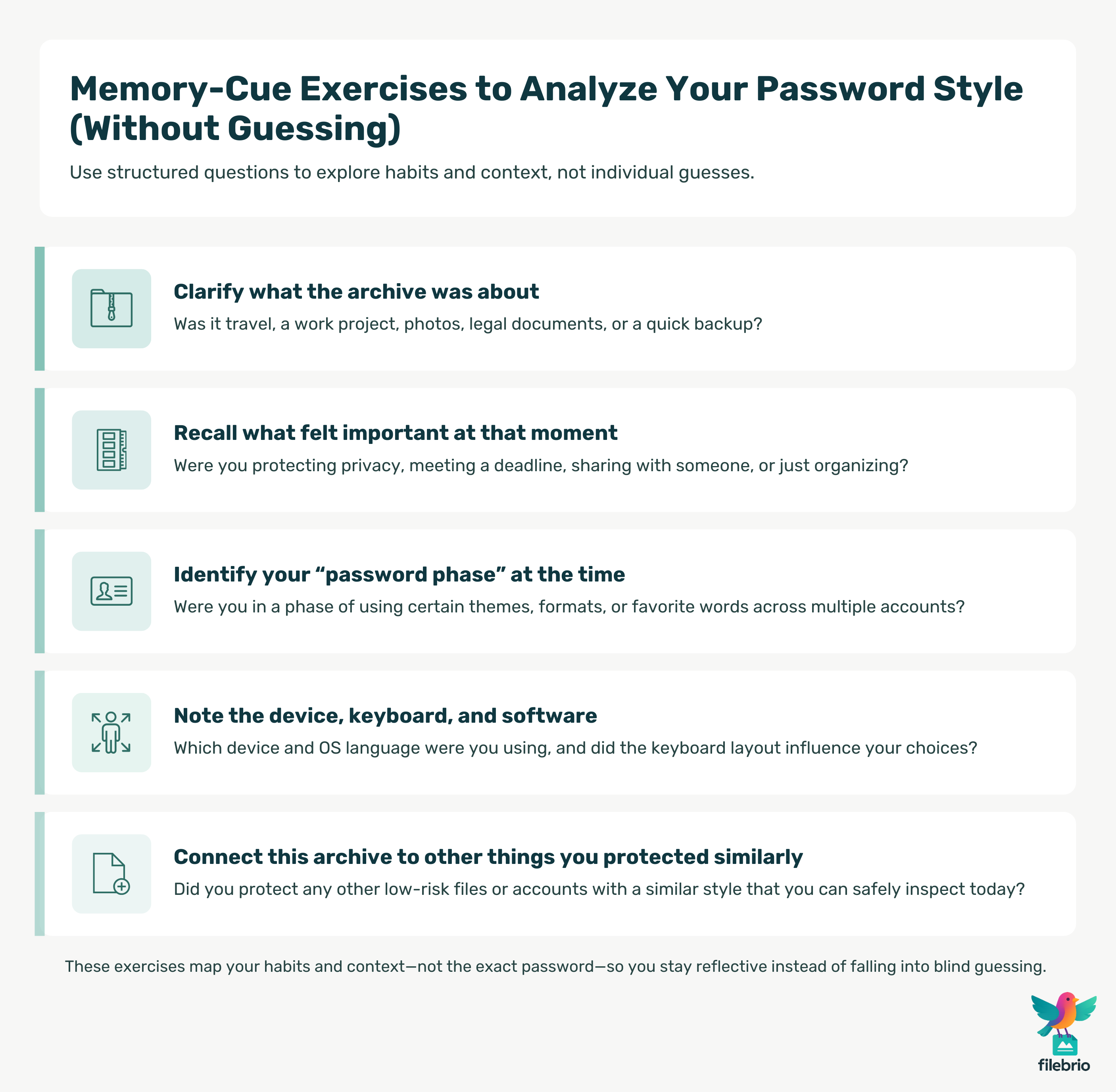
🛠️ Practical Memory-Cue Exercises (Without Guessing the Password)
Exercises in this context mean structured reflection, not entering passwords into tools. You’re working on paper or in a secure notes app, asking questions like:
- “What was this archive about?” Travel? Work project? Photos? Legal documents?
- “What felt important when I created it?” Deadline? Privacy? Sharing with someone?
- “Which password phase was I in?” Did you use certain themes or styles during that time in your life?
- “Which device and software did I use?” The keyboard layout, OS language, and IME can influence choices.
- “What else was I protecting similarly?” Did you use a comparable style on another system or file?
For users who want a deeper, structured approach, ways to rediscover your forgotten RAR password safely ↗️ describes how to rebuild the surrounding context using journaling, timelines, and associated events—without turning it into a brute-force guessing session.
At every step, keep a bright line between understanding patterns and actively trying candidates. The first is introspection; the second can quickly become unproductive and stressful if done without a clear feasibility plan.
🌍 Using Real-Life Examples From Your Digital Life
Your password style doesn’t exist in a vacuum. You can safely study patterns using other accounts or archives—especially low-risk ones—without ever touching the protected RAR file you’re worried about.
| Source | What You Look For | How It Helps |
|---|---|---|
| Old notes or password manager entries (minus the secrets) | Structures you used historically (e.g., two words + digits) | Reveals recurring templates in your mental “password grammar.” |
| Past project folders and archive names | Names, abbreviations, and date formats you favored | Shows how naming habits and password choices align. |
| Low-risk sample archives | Intentional test passwords you can safely review | Helps you observe how your fingers and brain naturally compose new passwords. |
An especially useful practice is to create dummy archives with known passwords and then study them later, as explained in how to test RAR protection with your dummy files ↗️. Doing this periodically shows you how your style evolves over time and how easily you can recall passwords after weeks or months.
When you compare those controlled examples to your current locked archive, you’re no longer guessing blindly—you’re asking whether the archive’s age, purpose, and creation context match any of your known patterns.
🔐 A Private, Offline Path to Understanding Your RAR Archive
Once you’ve explored your memory cues and identified your password style, the next question is simple:
Is recovery realistically possible — and is your archive even intact?
FileBrio RAR Master helps you answer that safely. Instead of guessing, stressing, or risking file damage, you can rely on a fully offline toolkit designed to analyze your archive’s condition, confirm whether corruption is involved, and guide you toward informed, responsible next steps.
- 🧭 Determines if the archive is healthy enough for recovery attempts
- 🧱 Checks for damaged blocks, truncated ends, or missing segments
- 🔐 Detects encrypted-header behavior that hides the file list
- ⚙️ Distinguishes password issues from structural ones
- 🛡️ Ensures every check is done locally for maximum privacy
This gives you a realistic roadmap: whether your memory cues might lead somewhere productive, or whether the archive itself needs repair, reconstruction, or further analysis before anything else.
| Your Reflection | FileBrio’s Offline Insight |
|---|---|
| “I think I created this during a busy project…” | Checks if the archive structure matches that timeline’s naming trends |
| “I don’t remember if it was corrupted or just protected…” | Reveals whether internal blocks are recoverable or intact |
| “Maybe I used a theme…” | Confirms whether encrypted headers are hiding the file list |
Before you make any recovery decisions — get a safe, private assessment of your archive’s real condition:
________________________
FileBrio RAR Master — a secure, offline Windows toolkit for regaining access to your own password-protected RAR / WinRAR archives while keeping all data strictly on your device.
- Offline-only processing — never uploads your archives.
- Smart issue detection — password vs corruption.
- Fast recovery workflow optimized for legitimate ownership.
⬇️ Download FileBrio RAR Master
Reminder: FileBrio RAR Master is intended only for archives you own or are explicitly authorized to access. All operations run locally on your PC.
________________________
📂 Documenting Password Metadata Without Exposing Secrets
Once you’ve mapped your style, the next step is to capture it as metadata—descriptions and hints, not raw passwords. The idea is to give “future you” a safe reference for how your mind worked at the time.
For individuals, a strong starting point is how to organize metadata for your RAR passwords safely ↗️. Instead of writing “Password is X,” you document things like:
- “Always two short words, both in language A.”
- “Year at the end; no leading zeros.”
- “Symbol is never in the middle—always at the end.”
- “Archives for Client Y always use the same theme, but slightly varied.”
In team environments, similar principles apply, but you must also consider access control and role changes. Guidance in how teams can organize shared RAR password metadata ↗️ explains how to keep enough documentation to remain operational without centralizing all secrets in one risky location.
The more you treat your style as an asset to document, the less likely you are to face a total mystery later. Your memory cues become part of a sustainable, privacy-respecting archive management strategy.
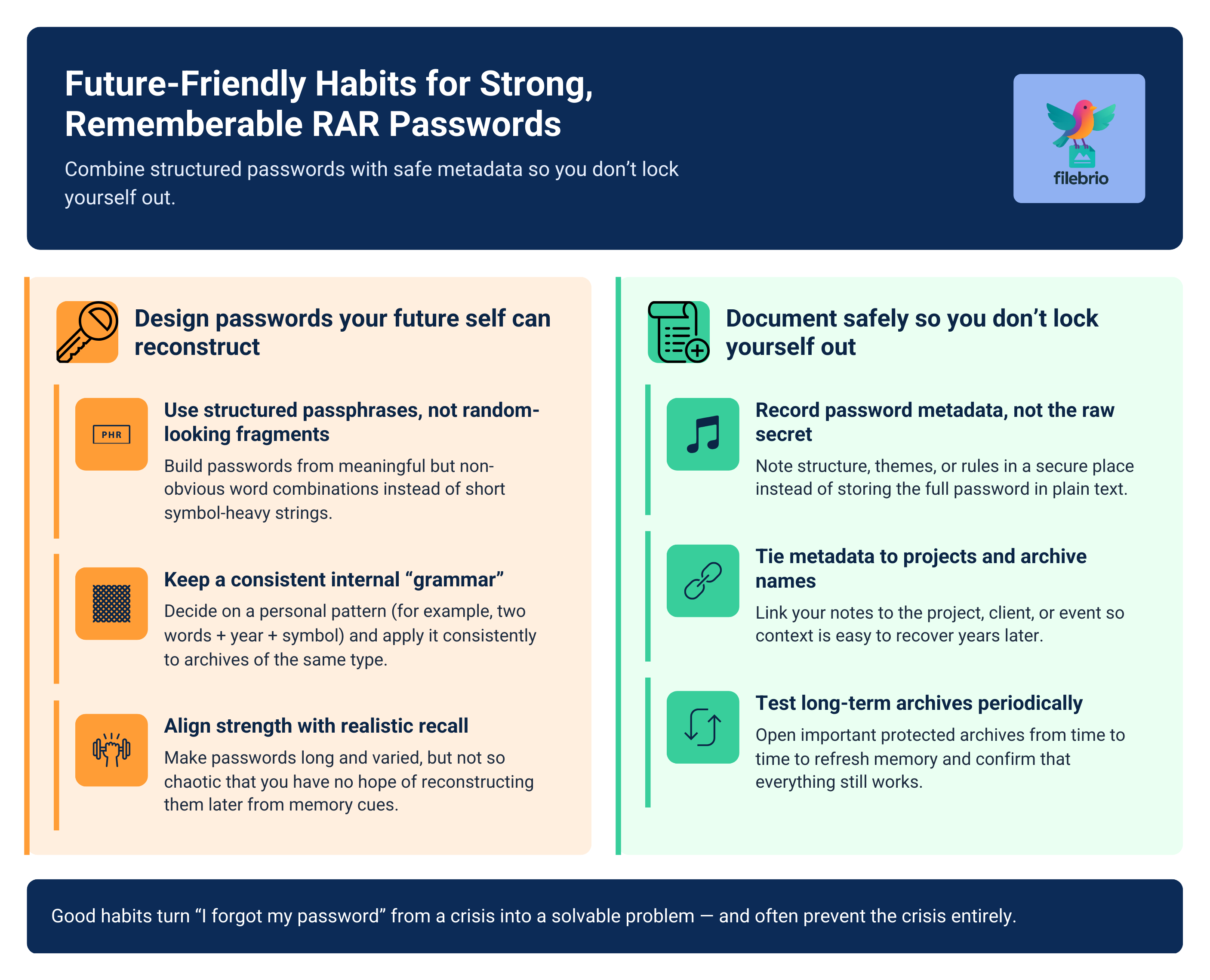
🌱 Designing Future-Friendly RAR Password Habits
Analyzing your existing style is only half of the value. The other half is using what you’ve learned to design better habits going forward—passwords that are both strong and realistically memorable.
Several complementary resources can guide this redesign:
- Balancing strength and recall: practical ways to future-proof your RAR password memory ↗️ show how to build structures that your brain can reliably reconstruct.
- Ensuring long-term access: how to strengthen RAR archive security while preserving future access ↗️ explains how to combine strong encryption with sound processes.
- Protecting against forgetting: ways to retain long-term memory of your RAR passwords ↗️ gives you concrete retention strategies and routines.
- Seeing the bigger security picture: how encryption controls access to your protected RAR contents ↗️ helps you align your habits with the actual security model.
As you refine these habits, remember that the goal isn’t to make passwords “simple” or weak. It’s to make them structured so future you (and authorized collaborators) can work backwards using context and memory cues instead of desperation and guesswork.
📜 Legal Reminder
This article is provided for general informational and educational purposes only. Any examples, scenarios, or references to password recovery, archive security, or related tools (including FileBrio RAR Master or similar software) are intended solely to help you better understand how to protect and manage your own data.
You may only apply any techniques, workflows, or tools described here to files and archives that you fully own or are explicitly and verifiably authorized to access. Attempting to bypass, remove, or recover passwords for third-party data without clear permission may violate criminal law, civil law, or internal company policies in your jurisdiction.
Nothing in this article constitutes legal advice. Laws and regulations differ between countries and organizations, and you are solely responsible for ensuring that your actions comply with all applicable legislation, contracts, and internal policies. If you are unsure whether a particular action is lawful or permitted, consult a qualified legal professional before proceeding.
🔗 See Also — Related Guides
- How to Preserve Helpful Metadata for Future Password Recall ↗️
- How Ethical Wordlists Reflect Real Password Patterns and Habits ↗️
- What People Mean by “Bypass” — And How to Reassess Your Own Password Logic Safely ↗️
- Why “Breaking a Password” Is Misleading — And How to Review Your Creation Habits Responsibly ↗️
- How to Determine What’s Still Reviewable When You Don’t Remember the Password ↗️
- Choosing Safe Local Tools When Analyzing Your Password History ↗️
- How Dummy Archives Help You Explore Your Password Style Without Risk ↗️